Manual Chapter :
Overview: F5 Access for Android
Applies To:
Show Versions
BIG-IP APM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0, 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0, 12.1.4, 12.1.3
Overview: F5 Access for Android
Android
F5 Access and mobile devices
F5 Access for mobile devices provides full network access through
BIG-IP®
Access Policy Manager®
. With network access, users can run
applications such as RDP, SSH, Citrix, VMware View, and other enterprise applications on their
mobile devices. For information about how to use F5 Access on your device, refer to the
F5 Access for
.Android
User GuideF5 Access features include:
- Support for F5 Access on Chrome OS
- N-factor authentication (at least two input fields, password and passcode) support
- User name and password, client certificate, and RSA SecurID support
- Support for RSA SecurID software tokens
- Multiple input field support
- Credential caching support
- Support for biometric authentication, PIN, pattern, or device password to make a connection, when using cached credentials
- Support for checking information from client devices
- Support for roaming between cellular and WiFi networks
- Landing URI support
- Logging support to report issues
- Support for certificate-only authentication
- Support client certificate for DTLS tunnels and SSL tunnels
- Per-app VPN support for Android 5.0 and later
- Always-On mode for Android 7.0 and later for devices managed by an MDM
- Support for VPN tunnel on IPv6 single stack
- Support for APM VPN Proxy
About SAML support
F5 Access for
mobile devices
provides the following SAML support:- Service provider-initiated access only, for example, APM acting as the service provider (SP)
- Web Logon mode only
When you use F5 Access as a client performing the SP-initiated access, F5 Access first connects
to BIG-IP®
Access Policy Manager® (APM®). Because there is no
assertion, APM redirects the client to the IdP. The IdP then authenticates the user and redirects
F5 Access back to the SP with an assertion. APM then accepts the assertion and establishes a VPN
connection. You can then access back-end resources through F5 Access.
You can configure a BIG-IP system by configuring APM as an SP. The access policy associated
with the configuration assigns a SAML AAA resource followed by a Network Access Resource. For
more information about SAML configurations, refer to the
BIG-IP®
Access Policy Manager®: SAML Configuration
guide.About supported authentication types
F5 Access for
Android
provides these authentication types:Authentication type |
Description |
|---|---|
Regular Logon |
Provides the following two options:
|
Certificate-only |
Provides a certificate-only authentication without a username and password by adding a
certificate in the configuration while leaving the username field empty. |
Web Logon |
Provides the following three options:
|
About establishing VPN connections
You can use F5 Access to establish a VPN tunnel connection.
About pre-logon checks supported for Android
devices
Android
devicesAccess Policy Manager® can check
unique identifying information from
an
Android
device. The supported
session variables, which become populated with the Android
device information, are gathered automatically, and can easily be combined
with an LDAP or AD query to implement white-listing in a custom action to improve access
context. This information allows the Access Policy Manager to perform pre-logon sequence
checks and operations based on information about the connecting device. Using such
information, the Access Policy Manager can perform the following tasks: - Deny access if theAndroidversion is less than the required level.
- Log UDID information.
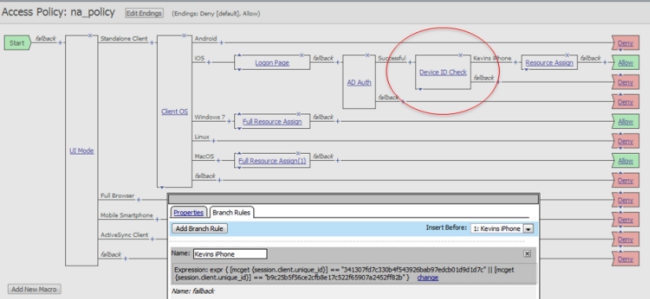
This example displays an access policy with a custom
action of Device ID Check to check the device's UDID.
Example of a custom action for checking device's UDID
About network integration on Android devices
Android
devicesAccess Policy Manager® provides web application-level security to
prevent malware attacks. As an administrator, you can enforce all web access through a secured
gateway, as well as bypass secure gateways for internal resources. This is especially helpful,
for example, when you have clients using corporate tablets, smartphones, or other mobile
devices to browse the web.






