Manual Chapter :
Overview: Access Policies for F5 Access
Applies To:
Show Versions
BIG-IP APM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0, 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
Overview: Access Policies for F5 Access
About access policy branches for F5 Access
You can configure separate access policy branches for F5 Access.
F5 Access does not support client-side checks; however, you
can configure an access policy that provides network access for macOS clients by using any of
these methods:
- Create an access policy usingClient-Side Capability. This provides a branch for clients that do not support client-side checks. Assign authentication and a network access resource to this branch.
- Use an existing access policy with client-side checks. The macOS client will fail to the fallback branch of the first client-side check, if the logon mode is native. If the logon mode is Web Logon, user interaction is required to proceed with the fallback branch. Assign authentication and a network access resource to the fallback branch.
- Add aClient OSAccess Policy item, and assign authentication and resources to themacOSbranch.
F5 Access for macOS is detected with the following access
policy items:
Access policy item |
Value |
|---|---|
Client Type |
F5 Access |
Client OS |
MacOS |
Configuring an access policy for F5 Access for macOS
Configure an access policy to identify and allow access to macOS devices.
- On the Main tab, click .The Access Profiles List screen opens
- ClickCreate.The New Profile screen opens.
- In theNamefield, type a name for the access profile.An access profile name must be unique among all access profile and any per-request policy names.
- From theProfile Typelist, selectSSL-VPN.Additional settings display.
- From the Profile Scope list, retain the default value or select another.
- Profile:Gives a user access only to resources that are behind the same access profile. This is the default value.
- Virtual Server:Gives a user access only to resources that are behind the same virtual server.
- Global:Gives a user access to resources behind any access profile that has global scope.
- In the Language Settings area, add and remove accepted languages, and set the default language.A browser uses the highest priority accepted language. If no browser language matches the accepted languages list, the browser uses the default language.
- ClickFinished.
- Click the name of the access profile for which you want to edit the access policy.The properties screen opens for the profile you want to edit.
- Click theAccess Policytab.
- In the General Properties area, click theEdit Access Policy for Profileprofile_namelink.The visual policy editor opens the access policy in a separate screen.
- ClickAdd Item.The screen is not active while the visual policy editor creates the action. The screen closes and a Properties screen displays.
- Click the Endpoint Security (Server-Side) tab, and select Client OS.
- ClickSave.
- On the MacOS branch, clickAdd Item.
- Click the Endpoint Security (Server-Side) tab, and select Client Type.
- ClickSave.
- On the F5 Access branch, add the authentication and resource actions you require. For example, add a Logon Page, Client Certificate, and Resource Assign actions.
- When you have finished configuring the access policy, clickApply Access Policy.
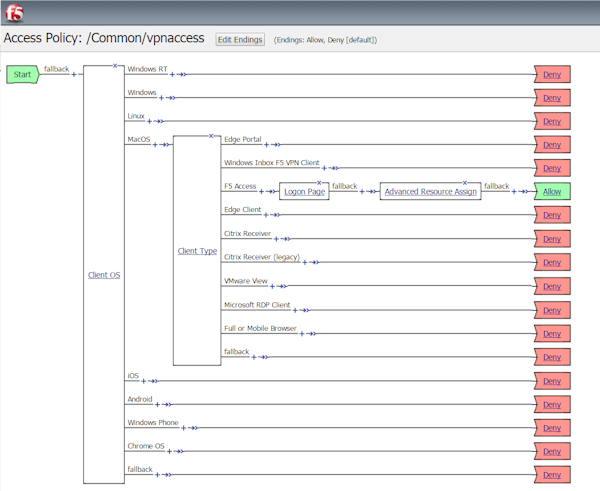
Completed access policy configuration
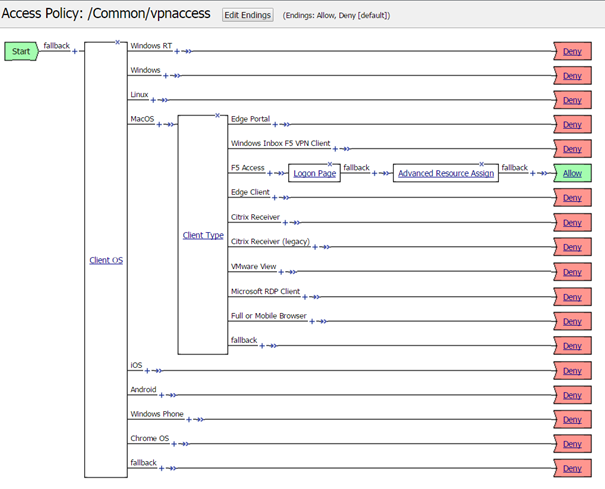
Example of basic access policy that supports F5 Access
You can configure an access policy branch to direct
macOS
device users to F5 Access, and direct non-F5 Access device users to a fallback
branch. This example displays a simple access policy.