Manual Chapter :
Deploying F5 Access for Windows 10
Applies To:
Show Versions
BIG-IP APM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0, 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0, 12.1.4, 12.1.3
Deploying F5 Access for Windows 10
Windows 10 auto-trigger VPN options
You can configure F5 Access for Windows 10 using Intune. In Windows 10, a number of features
were added to auto-trigger VPN so you won’t have to manually connect when VPN is needed to access
necessary resources. There are four different types of auto-trigger rules:
- App trigger
- Name-based trigger
- Always On
Refer to VPN auto-triggered profile options for more
information.
The Name-based trigger does not work for F5 Access VPN.
Configuring Azure active directory
Add/Delete a user
Add/Delete a user
Refer to How to: Add or delete users using Azure Active
Directory for information on adding new users or deleting existing users from the
Azure active directory.
Create a new group
Create a new group
Refer to How to: Create a basic group and add members using Azure
Active Directory for information on creating a basic group using the Azure active
directory portal.
About configuring VPN profile in Azure Intune
Virtual private networks (VPNs) give users secure remote access to the company network.
Devices use a VPN connection profile to initiate a connection with the VPN server.
Creating device configuration profile
Refer to Create a device profile in Microsoft Intune for
information on creating device profile in Microsoft Intune.
Configuring base VPN profile for F5 Access
To create a base VPN profile:
- Sign in to the Azure portal.
- SelectAll services, filter onIntune, and selectMicrosoft Intune.
- Click .
- Type theNameandDescriptionfor the VPN profile.
- From thePlatformlist, selectWindows 10 and later.
- From theProfile typelist, selectVPN.
- Depending on the platform you chose, the settings you can configure are different. Open configured settings.
- ClickBase VPNto open the Base VPN settings.
- Enter the name for this connection. End users see this name when they browse their device for the list of available VPN connections.
- Add/Import one or more VPN servers that devices connect to. When you add a server, you enter the following information:
- Description:Enter a descriptive name for the server, such asF5 VPN server.
- IP address or FQDN:Enter the IP address or fully qualified domain name of the VPN server that devices connect to.
- Default server:Enables this server as the default server that devices use to establish the connection. Set only one server as the default.
- From theConnection typelist, selectF5 Access.
- From theAuthentication methodlist, select how you want the users to authenticate to the VPN server. Using certificates provides enhanced capabilities, such as zero-touch experience, on-demand VPN, and per-app VPN.
- SelectRemember credentials at each logonto cache the authentication credentials.
- EnterCustom XMLcommands that configure the VPN connection.
- ClickOK.The profile is created and appears on the profiles list.
Configuring app trigger for F5 Access
VPN profiles in Windows 10 can be configured to connect automatically on the launch
of F5 Access. To configure App trigger:
- Sign in to the Azure portal.
- SelectAll services, filter onIntune, and selectMicrosoft Intune.
- Click .
- From theAssociate WIP or apps with this VPNlist, selectAssociated apps with this connection.
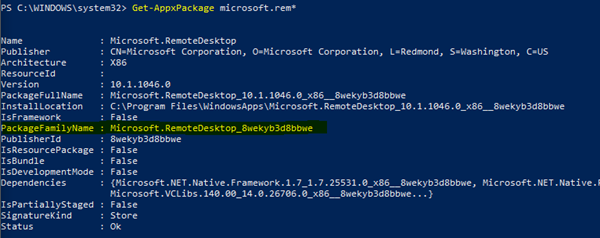
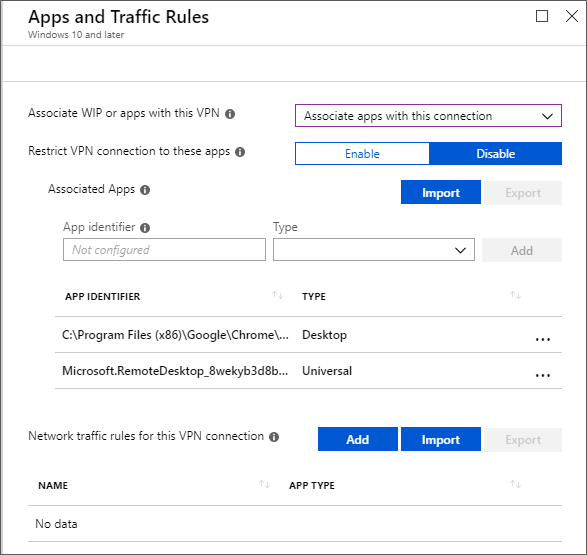
- TheRestrict VPN connection to these appsoption lets you to restrict VPN connection to apps you enter inAssociated Appstable. The apps you enter automatically use the VPN connection. The type of app determines the app identifier. For a universal app, enter the package family name. To get the package family name of an app, use theGet-AppxPackage package_namepowershell command on the client machine. For a desktop app, enter the file path of the app. For example, to start the VPN every time Microsoft Remote Desktop app is launched, useApp identifierasC:\Program Files \WindowsApps\Microsoft.RemoteDesktop.exe.Add associated apps in before enablingRestrict VPN connection to these apps, as the list will become read-only after enabling. Traffic rules for apps will automatically be added to the network traffic rules when you clickEnable.Example of a PowerShell command to get package family name
- TheNetwork traffic rules for this VPN connectionoption is not required to be setup for F5 Access.Apps and Traffic Rules Screen
Configuring Name-based trigger for F5 Access
You can configure a domain name-based rule so that a specific domain name triggers the VPN
connection.
Refer to Name-based trigger for information on configuring
name-based trigger rule.
Always specify the
DnsIPAddress
parameter with an
actual DNS Server IP address. This parameter cannot be overwritten by APM server
configuration.Configuring Always On for F5 Access
The Always On feature in Windows 10 enables the active VPN profile to connect
automatically on the following triggers:
- User sign-in
- Network change
- Device screen on
Assigning a device profile to group
After you create a profile, you can assign the profile to Azure active directory
groups.
Refer to Assign user and device profiles for information on
assigning a device profile in Microsoft Intune.





