Manual Chapter :
APM as an Active Directory Federation
Services (AD FS) Proxy
Applies To:
Show Versions
BIG-IP APM
- 14.0.1, 14.0.0
APM as an Active Directory Federation
Services (AD FS) Proxy
About APM support for AD FS proxy
Access Policy Manager (APM®) follows the Microsoft
specification
[MS-ADFSPIP]: Active Directory Federation Services and Proxy Integration
Protocol
so that APM can replace Microsoft Web Application Proxy (WAP) in the role of
AD FS proxy. This includes enabling APM to be configured for client and device certificate
authentication to AD FS. On top of that, APM can secure browser access to AD FS with an access
policy.AD FS versions that
APM supports as an AD FS proxy
Access Policy Manager (APM®) can act as an AD FS proxy for AD FS versions 3.0 (on
Windows Server 2012 R2) and 4.0 (on Windows Server 2016).
Overview: Configuring APM as an AD FS
proxy
You can register Access Policy Manager (APM) with
Microsoft Active Directory Federation Services (AD FS) as an AD FS proxy. Your remote users then
go through APM before reaching the AD FS server or AD FS farm.
Configuring a pool
of AD FS servers
You configure a pool with an AD FS server or
with members of an AD FS farm for use with Access Policy Manager (APM) as an AD FS
proxy.
- On the Main tab, click .The Pools list screen opens.
- ClickCreate.The New Pool screen opens.
- In theNamefield, type a name for the pool.Names must begin with a letter, and can contain only letters, numbers, and the underscore (_) character.The pool name is limited to 63 characters.
- In the Resources area in theNew Memberssetting, add an ADFS server or add the ADFS servers for the ADFS farm that you want to include in the pool:
- Type an IP address in theAddressfield, or select a node address from theNode List.
- In theService Portfield, type443, which is the default; otherwise, type the port number configured for the ADFS server.
- ClickAdd.
- ClickFinished.
Create a Client SSL profile
You create a Client SSL profile when you want the BIG-IP system to
authenticate and decrypt/encrypt client-side application traffic.
- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Client SSL Profile screen opens.
- Configure all profile settings as needed.
- ClickFinished.
After creating the Client SSL profile and assigning the profile to a virtual server,
the BIG-IP system can apply SSL security to the type of application traffic for which
the virtual server is configured to listen.
Configuring a
server SSL profile for AD FS proxy
To complete this task, you need to know the
FQDN for the AD FS server.
You configure a server SSL profile for use in
a configuration where Access Policy Manager (APM) acts as an AD FS proxy.
When you enable trust between a virtual server and
an AD FS server, APM generates a certificate of trust and a key and attaches them to
the server SSL profile used on the virtual server. If you use a server SSL profile
that already has a certificate attached to it, this action will detach the existing
certificate and attach a newly generated self-signed certificate to the profile. The
previously attached certificate is not deleted from the BIG-IP
system.
- On the Main tab, click .The Server SSL profile list screen opens.
- ClickCreate.
- In theNamefield, type a unique name for the profile.
- From theConfigurationlist, selectAdvanced.
- Select theCustomcheck box.The settings become available for change.
- InServer Name, type the FQDN for the AD FS server.
- ClickFinished.
Configuring a virtual server for AD FS proxy
To complete this task, you need to know the service port used on your AD FS server. The
default port is 443, but yours might be different.
You configure a virtual server for AD FS proxy to
process traffic going to an AD FS server or AD FS farm.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- In theDestination Address/Maskfield, type the IP address that you want to use for the virtual server.For external users, the FQDN for the AD FS server should resolve into this IP address.
- ForService Port, type the port number that's used on the AD FS server.
- From theHTTP Profile (Client)list, select a previously-created HTTP/2 profile for client-side traffic.
- For theSSL Profile (Client)setting, move the client SSL profile you configured previously to theAvailablelist.
- For theSSL Profile (Server)setting, move the server SSL profile you configured previously to theAvailablelist.
- In the Access Policy area, forADFS Proxy, select theEnabledcheck box.
- In the Resources area, from theDefault Poollist, select the name of the pool that you created previously.
- ClickFinished.The virtual server list displays.
Registering APM as an AD FS proxy
To complete this task, you must know
the username and password for a local administrator account on the AD FS
server.
You establish trust between a virtual server and
an AD FS server so that your remote users can go through Access Policy Manager (APM)
before reaching the AD FS server or AD FS farm.
If using redundant
systems where the main system failed, trust cannot be established from the standby
system; it fails with the error
Failed to establish ADFS trust
relationship on the virtual server /Common/adfs_vs: Can't connect to
ADFS
.- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- Scroll to the Access Policy area.
- ForADFS Proxy:
- If theEnabledcheck box is cleared, select it.
- Click theEstablish Trustbutton.
- In theUsernameandPasswordfields, type the credentials of a local administrator account on the AD FS server.APM uses the credentials while establishing trust, but does not store them.The AD FS server dictates the format for the user name.
- InCertificate Name, type a name.APM generates a self-signed certificate with this name, while establishing trust.
- ClickOK.
On success, a trust certificate name and expiration details display; otherwise, the message that APM receives from the AD FS server displays.
On success, APM adds the newly
generated trust certificate and key to the server SSL profile for this virtual server.
Any previously attached certificate and key are detached from the server SSL profile,
but remain on the system. APM periodically renews the trust certificate.
Overview: Using alternate port for client
certificate authentication (AD FS 3.0 or 4.0)
On an AD FS server, client certificate authentication enables a user to authenticate using, for
example, a smart card. If your AD FS server (version 3.0 or 4.0) is configured to support client
certificate authentication using an alternate port, you can use this implementation to enable an
Access Policy Manager (APM) AD FS proxy to provide
the same support.
If you have not already done so, configure APM as an AD FS proxy.
Configuring a
client SSL profile
You configure a client SSL profile with
Client Certificate
set to require
to support client certificate
authentication in some cases.- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Server SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- Next to Client Authentication, select theCustomcheck box.The settings become available.
- FromClient Certificatelist, selectrequire.
- Configure other profile settings as needed.
- ClickFinished.
Configuring a virtual server for client certificate authentication with AD FS
proxy
Before you start this task, gather
this information:
- The service port that the AD FS server uses for certificate authentication. By default, it's 49443, but yours could be different.
- The server SSL profile name and the pool name used by the virtual server that is already configured to serve as the AD FS proxy.
You configure a virtual server to
support client certificate authentication on the AD FS proxy when the AD FS server
provides this support using an alternate port.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- In theDestination Address/Maskfield, type the IP address that you want to use for the virtual server.For external users, the FQDN for AD FS should resolve into this IP address.
- ForService Port, type the port number that's used for certificate authentication on the AD FS server.
- From theHTTP Profile (Client)list, select a previously-created HTTP/2 profile for client-side traffic.
- For theSSL Profile (Client)setting, move the client SSL profile you recently configured to theSelectedlist.
- For theSSL Profile (Server)setting, select the name of the server SSL profile that's used on the AD FS proxy virtual server and move it to theSelectedlist.
- In the Access Policy area, forADFS Proxy, select theEnabledcheck box.You do not need to establish trust between this virtual server and the ADFS server. This virtual server uses the trust certificate that was generated on the other AD FS proxy-enabled virtual server.
- In the Resources area, from theDefault Poollist, select the name of the pool that's used on the AD FS proxy virtual server.
- ClickFinished.
Overview: Using alternate hostname for client
certificate authentication (AD FS 4.0)
On an AD FS server, client certificate authentication enables a user to authenticate using, for
example, a smart card. If your AD FS server (version 4.0) is configured to support client
certificate authentication using an alternate hostname, you can use this implementation to enable
an Access Policy Manager (APM) AD FS proxy to provide
the same support.
If you have not already done so, configure APM as an AD FS proxy.
Creating a client
SSL profile for client certificate authentication on the AD FS proxy
When the external AD FS server supports client
certificate authentication using an alternate hostname, you can configure a client SSL
profile to support client certificate authentication on Access Policy Manager (APM) as
an AD FS proxy.
- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Client SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- From theConfigurationlist, selectAdvanced.
- Select theCustomcheck box.
- In theServer Namefield, typecertauth.ADFSFQDNwhereADFSFQDNis the FQDN for the AD FS server.
- Next to Client Authentication, select theCustomcheck box.The settings become available.
- FromClient Certificatelist, selectrequire.
- Configure other profile settings as needed.
- ClickFinished.
Adding a client SSL profile to the AD FS
proxy
You add a client SSL profile to the
virtual server that is configured as the AD FS proxy to support client certificate
authentication.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- For theSSL Profile (Client)setting, from theAvailablelist, select the name of the custom Client SSL profile you previously created, and move it to theSelectedlist.
- ClickFinished.
Overview: Configuring APM to support AD F5
device registration (Workplace Join)
You can configure Access Policy Manager (APM®) to
proxy device certificate authentication for devices that have already registered with AD FS for
Microsoft Workplace Join.
Task summary
Importing a certificate from AD FS
Before you start this task, you must
have the MS-Organization-Access certificate exported from the AD FS server. The
certificate is located in the
AdfsTrustedDevices
folder of Local
Computer certificate storage.You import the
MS-Organization-Access certificate to the BIG-IP system to support
device registration through the AD FS proxy.
- On the Main tab, click .The SSL Certificate List screen opens.
- Click theImportbutton.
- From theImport Typelist, selectCertificate.
- For theCertificate Namesetting:
- If you are importing a new certificate, selectCreate Newand type a unique name in the field.
- If you are replacing an existing certificate, selectOverwrite Existingand select a certificate name from the list.
- For theCertificate Sourcesetting, selectUpload Fileand browse to select the certificate you obtained from the vendor.
- ClickImport.
Updating the client SSL profile for the AD
FS proxy
Before you start this task, you need
to know the name of the client SSL profile used on the virtual server that processes
traffic as the AD FS proxy.
You update the client SSL profile to
enable device certificate authentication through the AD FS proxy.
- On the Main tab, click .The Client SSL profile list screen opens.
- Click the name of the profile that you want to modify.
- Next to Client Authentication, select theCustomcheck box.The settings become available.
- ForClient Certificate, select the default valueignore.
- ForTrusted Certificate AuthoritiesandAdvertised Certificate Authorities, select the previously imported "MS-Organization-Access" certificate.
- ClickUpdate.
Creating a server
SSL profile for AD FS device registration
To enable device registration through Access
Policy Manager (APM) to AD FS (version 3.0), you need an additional server SSL profile
with the settings specified in these steps.
You only need
to create a server SSL profile for ADFS 3.0 on Windows Server 2012 R2.
- On the Main tab, click .The Server SSL profile list screen opens.
- ClickCreate.The New Server SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- From theConfigurationlist, selectAdvanced.
- Select theCustomcheck box.
- In theServer Namefield, typeenterpriseregistration.domainnamewheredomainnameis the domain name for the AD FS server.By default, theDefault SSL Profile for SNIcheck box is cleared. Be sure to leave it that way.
- ClickFinished.
You need the name of this server SSL profile to
configure the iRule that's specified in a subsequent step.
Overview: Supporting device registration
through the proxy to AD FS 3.0
On an AD FS server, device registration enables Microsoft Workplace Join. If you have AD FS
version 3.0, you can use this implementation to enable Access Policy Manager (APM®) to support device registration.
If you have not already done so, configure APM as an AD FS proxy. Then complete these
tasks.
Task summary
Creating a client SSL profile for AD FS
device registration
To enable device registration
through Access Policy Manager (APM) to AD FS
(version 3.0), you need an additional client SSL profile with the settings specified in
these steps.
- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Client SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- From theConfigurationlist, selectAdvanced.
- Select theCustomcheck box.
- In theServer Namefield, typeenterpriseregistration.domainnamewheredomainnameis the domain name for the AD FS server.By default, theDefault SSL Profile for SNIcheck box is cleared. Be sure to leave it that way.
- Next to Client Authentication, select theCustomcheck box.The settings become available.
- FromClient Certificatelist, selectignore.
- ClickFinished.
Creating an iRule
to support AD FS device registration
You configure this iRule to support device
registration to AD FS version 3.0 through the AD FS proxy.
- On the Main tab, click .The iRule List screen opens, displaying any existing iRules.
- ClickCreate.The New iRule screen opens.
- In theNamefield, type a unique name for the iRule.The full path name of the iRule cannot exceed 255 characters.
- In theDefinitionfield, type this text, making sure to replaceenterprisereg-serversslwith the name of the server SSL profile you created previously.when HTTP_REQUEST { set useEnterpriseRegProfile [expr { [string tolower [HTTP::host]] starts_with "enterpriseregistration." }] } when SERVER_CONNECTED { if { $useEnterpriseRegProfile == 1 } { SSL::profileenterprisereg-serverssl} }For complete and detailed information about iRules syntax, see the F5 DevCentral web sitehttp://devcentral.f5.com.
- ClickFinished.The new iRule appears in the list of iRules on the system.
Updating a virtual server for AD FS
device registration
You add more SSL profiles and an
iRule to the virtual server that has established trust with AD FS version 3.0 to support
device registration through the AD FS proxy.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- For theSSL Profile (Client)setting, from theAvailablelist, select the name of the custom Client SSL profile you previously created, and move it to theSelectedlist.
- For theSSL Profile (Server)setting, from theAvailablelist, select the name of the custom Server SSL profile you previously created, and move it to theSelectedlist.
- ClickFinished.
- Once again, click the name of the virtual server.
- On the menu bar, clickResources.
- In the iRules area, click theManagebutton.
- For theiRulesetting, move the iRule that you configured previously to theEnabledlist.
- ClickFinished.
Overview: Securing browser access to AD FS
with an access policy
To secure browser access to AD FS with an access policy, complete these tasks.
If you have not already
configured Access Policy Manager (APM®) as an AD FS
proxy, do so before you continue.
Configuring forms
client-initiated SSO for AD FS
To support this configuration, make sure that the
Extranet
zone setting is configured
to Forms Authentication
only
on the AD FS server.You create a forms client-initiated SSO
configuration with these settings when you want to secure browser access through Access
Policy Manager (APM) as an AD FS proxy.
- On the Main tab, click .The Forms - Client Initiated screen opens.
- ClickCreate.A Create New Forms-Client Initiated Configuration popup screen opens.
- InSSO Configuration Name, type a name.
- On the left, clickForm Settings.New settings display on the right.
- ClickCreate.Another popup screen, Create New Form Definition, opens.
- InForm Name, type a name.
- On the left, clickRequest Detectionand on the right inRequest URI, type/adfs/ls.
- On the left, clickForm Identification.
- On the right, fromIdentify Form by, selectID Attribute.
- InForm ID, typeloginForm.
- On the left, clickForm Parameters.You'll create two form parameters.
- On the right, clickCreate.
- ForForm Parameter Name, typePassword.The user interface might attempt to replacePasswordwithpassword; do not allow this. Case is important.
- ForForm Parameter Value, type%{session.sso.token.last.password}.
- ForSecure, selectYes.
- ClickOK.
- On the right, clickCreate.
- ForForm Parameter Name, typeUserName.The user interface might attempt to replaceUserNamewithusername; do not allow this. Case is important.
- ForForm Parameter Value, type%{session.sso.token.last.username}.
- ForSecure, retain the default value,No.
- ClickOK.
- On the left, clickLogon Detection.
- FromDetect Login by, selectPresence of Cookie.
- InCookie Name, typeMSISAuth.
- ClickOK.The Create New Form Definition popup screen closes.
- ClickOK.The Create New Form-Client Initiated Configuration popup screen closes. The new SSO configuration displays in the list.
Configuring an
access profile for the AD FS proxy
You create an access profile so that you can add
an SSO configuration to the AD FS proxy.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- ClickCreate.The New Profile screen opens.
- In theNamefield, type a name for the access profile.An access profile name must be unique among all per-session profile and per-request policy names.
- FromProfile Type, selectAll.
- Scroll to the SSO Across Authentication Domains (Single Domain mode) area.
- FromSSO Configuration, select the SSO configuration that you created previously.
- ClickFinished.
Configuring an
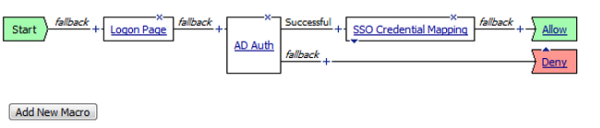
access policy for AD FS
To use an access policy to secure browser access
through the AD FS proxy, you configure an access policy that authenticates users and
supports SSO for them.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- On a policy branch, click the(+)icon to add an item to the policy.A popup screen displays actions on tabs, such as General Purpose and Authentication, and provides a search field.
- Add a Logon Page to the policy.
- Click the(+)icon anywhere in the policy to add a new action item.
- On the Logon tab, selectLogon Pageand click theAdd Itembutton.The Logon Page Agent properties screen opens.
- ClickSave.The properties screen closes. The policy displays.
- Add Active Directory authentication to the policy.
- On a policy branch, click the plus symbol(+)to add an item to the policy.
- On the Authentication tab, selectAD Authand clickAdd Item.A properties screen opens.
- FromServer, select an Active Directory server to use for authentication.
- ClickSave.The properties screen closes. The policy displays.
- Add SSO Credential Mapping to the policy.
- On a policy branch, click the plus symbol(+)to add an item to the policy.
- On the Assignment tab, selectSSO Credential Mappingand clickAdd Item.
- ClickSave.The properties screen closes. The policy displays.
- Click theApply Access Policylink to apply and activate the changes to the policy.
To put the SSO configuration and the access policy
into effect, add the access profile to the virtual server that established trust with AD
FS and functions as the AD FS proxy.
Adding the access
profile to the virtual server
You associate the access profile with the virtual
server so that Access Policy Manager can apply the profile to incoming traffic.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- In the Access Policy area, from theAccess Profilelist, select the access profile that you configured earlier.
- ClickUpdateto save the changes.
Your access policy is now associated with the virtual server.





