Manual Chapter :
Automatically Synchronizing Application Security Configurations
Applies To:
Show Versions
BIG-IP ASM
- 14.0.0
Automatically Synchronizing Application Security Configurations
Overview: Automatically synchronizing ASM systems
This implementation describes how to set up multiple BIG-IP® systems
running Application Security Manager™ (ASM) so that they automatically
synchronize their security policies and ASM™ configurations. In addition, the
ASM devices can fail over to one another if any of the devices goes offline. For synchronizing
local traffic configuration data, you can manually synchronize that data as needed.
Automatically synchronizing ASM configuration data
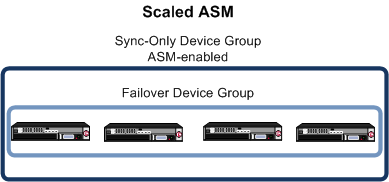
In this case, multiple BIG-IP systems are all processing similar traffic for one or more web
applications behind a router (or load balancer). All systems are running BIG-IP ASM™ and are in the local trust domain. You organize the systems into two device groups:
one Sync-Failover device group for all systems (not ASM-enabled) and one Sync-Only device group
with ASM-enabled for all of the systems. The ASM configurations and web applications are
automatically duplicated on all of the systems. You can manually synchronize the BIG-IP
configuration of the systems in the Sync-Failover device group.
About device
management and synchronizing application security configurations
You can use device management to set up several BIG-IP systems running Application Security Manager (ASM) so that the systems synchronize their security
policies and configurations, and fail over to one another if a system goes offline for any
reason. By using application security synchronization, you can set up application security and
create security policies on one system, and can propagate them to other systems in an
application security device group. In BIG-IP ASM, a
device group
is two or more BIG-IP devices using the same
configuration and providing consistent security policy enforcement. You can set up application security synchronization, for example, behind
an Application Delivery Controller where multiple BIG-IP systems running Application Security
Manager are deployed as members of a pool. The options and security policies on all of the
systems stay in sync regardless of where you update them.
When you set up ASM
synchronization, in addition to security policies, other settings such as custom attack
signatures, logging profiles, SMTP configuration, anti-virus protection, system variables, and
policy templates, are synchronized with all devices in the ASM-enabled device group.
Considerations for application security synchronization
When using device management with Application Security Manager™ (ASM™),
you need to be aware of the following considerations that apply specifically to application
security synchronization.
- A BIG-IP® system with Application Security Manager can be a member of only one ASM-enabled device group.
- All BIG-IP systems in a device group must be running the same version (including hot fix updates) of Application Security Manager (version 11.0 or later).
- The BIG-IP systems in the ASM-enabled device group synchronize application security configuration data and security policies, providing consistent enforcement on all the devices.
- Real Traffic Policy Builder® can run on only one system per security policy. For example, you can set up automatic security policy building on one system that is a member of an ASM-enabled device group, the policy is built on that system and then automatically updated on all of the systems in the device group.
- If using a VIPRION® platform (with multiple blades), it is considered one device, and you need to add only the master blade to the device trust and group.
Performing basic network configuration for synchronization
You need to perform basic networking configuration for each of the BIG-IP systems whose Application Security Manager (ASM)
configurations you want to synchronize.
- Install the same BIG-IP system version (including any hot fixes) on each device.
- Provision LTM and ASM on each device ().
- On each device, create one or more VLANs, depending on your networking configuration ().
- On each device, create a self IP ().When creating the self IP, setTraffic Grouptotraffic-group-local-only (non-floating).
- On each device, create a default gateway, if needed ().
- On each device, configure DNS () and NTP () so they are set to the same time.
- Verify connectivity between the devices (self IP address to self IP address). For example, use this command to ensure communications:ping -Ivlan_interfacedevice_self_IP
- If your company requires special device certificates, install them on each device ( and clickImport).
The basic networking setup is complete for the BIG-IP ASM systems for which you want
to share security policies and configurations.
Next, on each device, specify the IP address to use when synchronizing
configuration objects to the local device:
Specifying an IP address for config sync
Before configuring the config sync address, verify that all devices in the device
group are running the same version of BIG-IP system software.
You perform this task to specify the IP address on the local device that other devices in the
device group will use to synchronize their configuration objects to the local device.
You must perform this task locally on each device in the device group.
- Confirm that you are logged in to the device you want to configure.
- On the Main tab, click .This displays a list of device objects discovered by the local device.
- In the Name column, click the name of the device to which you are currently logged in.
- Near the top of the screen, clickConfigSync.
- From theLocal Addresslist, retain the displayed IP address or select another address from the list.F5 Networks recommends that you use the default value, which is the self IP address for the internal VLAN. This address must be a non-floating (static) self IP address and not a management IP address.If the BIG-IP device you are configuring is accessed using Amazon Web Services, then the internal self IP address that you select must be an internal private IP address that you configured for this EC2 instance as theLocal Address.
- ClickUpdate.
After performing this task, the other devices in the device group can synchronize
their configurations to the local device whenever a sync operation is
initiated.
Establishing device trust
Before you begin this task, verify that:
- Each BIG-IP device that is to be part of the local trust domain has a device certificate installed on it.
- The local device is designated as a certificate signing authority.
You perform this task to establish trust among devices on one or more network segments. Devices
that trust each other constitute the
local trust domain
. A device must
be a member of the local trust domain prior to joining a device group.By default, the BIG-IP software includes a local trust domain with one member, which
is the local device. You can choose any one of the BIG-IP devices slated for a
device group and log into that device to add other devices to the local trust
domain. For example, devices
Bigip_1
,
Bigip_2
, and Bigip_3
each
initially shows only itself as a member of the local trust domain. To configure the
local trust domain to include all three devices, you can simply log into device
Bigip_1
and add devices Bigip_2
and Bigip_3
to the local trust domain; there is no need to
repeat this process on devices Bigip_2
and
Bigip_3
.- On the Main tab, click .
- ClickAdd.
- From theDevice Typelist, selectPeerorSubordinate.
- Type a device IP address, administrator user name, and administrator password for the remote BIG-IP device with which you want to establish trust. The IP address you specify depends on the type of BIG-IP device:
- If the BIG-IP device is an appliance, type a management IP address (IPv4 or IPv6) for the device.
- If the BIG-IP device is a VIPRION device that is not licensed and provisioned for vCMP, type a primary cluster management IP address (IPv4 or IPv6) for the cluster.
- If the BIG-IP device is a VIPRION device that is licensed and provisioned for vCMP, then type a cluster management IP address (IPv4 or IPv6) for the guest.
- If the BIG-IP device is an Amazon Web Services EC2 device, type one of the Private IP addresses created for this EC2 instance.
- ClickRetrieve Device Information.
- Verify that the certificate of the remote device is correct, and then clickDevice Certificate Matches.
- In theNamefield, verify that the name of the remote device is correct.
- ClickAdd Device.
After you perform this task, the local device is now a member of the local trust
domain. Also, the BIG-IP system automatically creates a special Sync-Only device group
for the purpose of synchronizing trust information among the devices in the local trust
domain, on an ongoing basis.
Repeat this task to specify each device that you want to add to the local trust
domain.
Creating a Sync-Failover device group
This task establishes failover capability between two or more BIG-IP
devices. If an active device in a Sync-Failover device group becomes unavailable,
the configuration objects fail over to another member of the device group and
traffic processing is unaffected. You perform this task on any one of the authority
devices within the local trust domain.
Repeat this task for each Sync-Failover device group that you want to create for your network configuration.
- On the Main tab, click .
- On the Device Groups list screen, clickCreate.The New Device Group screen opens.
- In theNamefield, type a name for the device group.
- From theGroup Typelist, selectSync-Failover.
- In theDescriptionfield, type a description of the device group.This setting is optional.
- From theConfigurationlist, selectAdvanced.
- For theMemberssetting, select a host name from theAvailablelist for each BIG-IP device that you want to include in the device group, including the local device. Use the Move button to move the host name to theIncludeslist.TheAvailablelist shows any devices that are members of the device's local trust domain but not currently members of a Sync-Failover device group. A device can be a member of one Sync-Failover group only. Also, for vCMP-provisioned systems on platforms that contain a hardware security module (HSM) supporting FIPS multi-tenancy, the FIPS partitions on the guests in the device group must be identical with respect to the number of SSL cores allocated to the guest's FIPS partition and the maximum number of private SSL keys that the guest can store on the HSM.
- From theSync Typelist:
- SelectAutomatic with Incremental Syncwhen you want the BIG-IP system to automatically sync the most recent BIG-IP configuration changes from a device to the other members of the device group. In this case, the BIG-IP system syncs the configuration data whenever the data changes on any device in the device group.
- SelectManual with Incremental Syncwhen you want to manually initiate a config sync operation. In this case, the BIG-IP system syncs the latest BIG-IP configuration changes from the device you choose to the other members of the device group. We strongly recommend that you perform a config sync operation whenever configuration data changes on one of the devices in the device group.
- SelectManual with Full Syncwhen you want to manually initiate a config sync operation. In this case, the BIG-IP system syncs the full set of BIG-IP configuration data from the device you choose to the other members of the device group. We strongly recommend that you perform a config sync operation whenever configuration data changes on one of the devices in the device group.
- In theMaximum Incremental Sync Size (KB)field, retain the default value of1024, or type a different value.This value specifies the total size of configuration changes that can reside in the incremental sync cache. If the total size of the configuration changes in the cache exceeds the specified value, the BIG-IP system performs a full sync whenever the next config sync operation occurs.
- For theNetwork Failoversetting, select or clear the check box:
- Select the check box if you want device group members to handle failover communications by way of network connectivity. This is the default value and is required for active-active configurations.
- Clear the check box if you want device group members to handle failover communications by way of serial cable (hard-wired) connectivity.
For active-active configurations, you must select network failover, as opposed to serial-cable (hard-wired) connectivity. - In theLink Down Time on Failoverfield, use the default value of0.0, or specify a new value.This setting specifies the amount of time, in seconds, that interfaces for any external VLANs are down when a traffic group fails over and goes to the standby state. Specifying a value other than0.0for this setting causes other vendor switches to use the specified time to learn the MAC address of the newly-active device.This setting is a system-wide setting, and does not apply to this device group only. Specifying a value in this field causes the BIG-IP system to assign this value to the global bigdb variablefailover.standby.linkdowntime.
- ClickFinished.
Syncing the BIG-IP configuration to the device group
Before you sync the configuration, verify that the devices targeted for config sync
are members of a device group and that device trust is established.
This task synchronizes the BIG-IP configuration data from the
local device to the devices in the device group. This synchronization ensures that
devices in the device group operate properly. When
synchronizing self IP addresses, the BIG-IP system synchronizes floating self IP
addresses only.
You perform this task on either of the two
devices, but not both.
- On the Main tab, click .
- In the Device Groups area of the screen, click the arrow next to the name of the relevant device group.The screen expands to show a summary and details of the sync status of the selected device group, as well as a list of the individual devices within the device group.
- In the Devices area of the screen, choose the device that shows a sync status ofChanges Pending.
- In the Sync Options area of the screen, selectPush the selected device configuration to the group.
- ClickSync.The BIG-IP system syncs the configuration data of the selected device to the other members of the device group.
Specifying IP addresses for failover communication
You perform this task to specify the local IP addresses that you want other devices
in the device group to use for continuous health-assessment communication with the local
device. You must perform this task locally on each device in the device group.
The IP addresses that you specify must belong to route domain
0
.- Confirm that you are logged in to the device you want to configure.
- On the Main tab, click .This displays a list of device objects discovered by the local device.
- In the Name column, click the name of the device to which you are currently logged in.
- Near the top of the screen, clickFailover Network.
- ClickAdd.
- From theAddresslist, select an IP address.The unicast IP address you select depends on the type of device:PlatformActionAppliance without vCMPSelect a static self IP address associated with a VLAN on the internal network (preferably VLANHA) and the static management IP address or addresses currently assigned to the device. If the system is configured with both IPv4 and IPv6 management IP addresses, then by default, the system will use either of these addresses for failover communication if needed, for failover communication between devices.Appliance with vCMPSelect a static self IP address associated with a VLAN on the internal network (preferably VLANHA) and the unique management IP address currently assigned to the guest. If a guest is configured with both IPv4 and IPv6 cluster management IP addresses, then by default, the system will use either of these addresses for failover communication if needed, for failover communication between devices.VIPRION without vCMPSelect a static self IP address associated with a VLAN on the internal network (preferably VLANHA). If you choose to select unicast addresses only (and not a multicast address), you must also specify the existing per-slot static management IP address or addresses (IPv4, IPv6, or both) that you previously configured for each slot in the cluster. If you choose to select one or more unicast addresses and a multicast address, then you do not need to select the existing per-slot, static management IP addresses when configuring addresses for failover communication.VIPRION with vCMPOn the vCMP host, select a self IP address that is defined on the guest and associated with a VLAN on the internal network (preferably VLANHA). If you choose to select unicast failover addresses only (and not a multicast address), you must also select the existing per-slot virtual static management IP address or addresses (IPv4, IPv6, or both) that you previously configured for each slot in the guest's virtual cluster. If you choose to select one or more unicast addresses and a multicast address, you do not need to select the existing per-slot virtual static, management IP addresses when configuring addresses for failover communication.Failover addresses should always be static, not floating, IP addresses.
- From thePortlist, select a port number.We recommend using port1026for failover communication.
- To enable the use of a failover multicast address on a VIPRION platform (recommended), then for theUse Failover Multicast Addresssetting, select theEnabledcheck box.
- If you enabledUse Failover Multicast Address, either accept the defaultAddressandPortvalues, or specify values appropriate for the device.If you revise the defaultAddressandPortvalues, but then decide to revert to the default values, clickReset Defaults.
- ClickFinished.
After you perform this task, other devices in the device group can send failover
messages to the local device using the specified IP addresses.
Creating a
Sync-Only device group
You perform this task to create a Sync-Only type
of device group. When you create a Sync-Only device group, the BIG-IP system can then
automatically synchronize configuration data in folders attached to the device group
(such as security policies and acceleration applications) with the other devices in the
group, even when some of those devices reside in another network.
You perform
this task on any one BIG-IP device within the local trust domain; there is no need
to repeat this process on the other devices in the device group.
- On the Main tab, click .
- Find thePartitionlist in the upper right corner of the BIG-IP Configuration utility screen, to the left of theLog outbutton.
- From thePartitionlist, pick partitionCommon.
- On the Device Groups list screen, clickCreate.The New Device Group screen opens.
- Type a name for the device group, select the device group typeSync-Only, and type a description for the device group.
- From theConfigurationlist, selectAdvanced.
- For theMemberssetting, select a host name from theAvailablelist for each BIG-IP device that you want to include in the device group. Use the Move button to move the host name to theIncludeslist.The list shows any devices that are members of the device's local trust domain.
- For theFull Syncsetting, specify whether the system synchronizes the entire configuration during synchronization operations:
- Select the check box when you want all sync operations to be full syncs. In this case, every time a config sync operation occurs, the BIG-IP system synchronizes all configuration data associated with the device group. This setting has a performance impact and is not recommended for most customers.
- Clear the check box when you want all sync operations to be incremental (the default setting). In this case, the BIG-IP system syncs only the changes that are more recent than those on the target device. When you select this option, the BIG-IP system compares the configuration data on each target device with the configuration data on the source device and then syncs the delta of each target-source pair.
If you enable incremental synchronization, the BIG-IP system might occasionally perform a full sync for internal reasons. This is a rare occurrence and no user intervention is required. - In theMaximum Incremental Sync Size (KB)field, retain the default value of1024, or type a different value.This value specifies the total size of configuration changes that can reside in the incremental sync cache. If the total size of the configuration changes in the cache exceeds the specified value, the BIG-IP system performs a full sync whenever the next config sync operation occurs.
- ClickFinished.
You now have a Sync-Only type of device group
containing BIG-IP devices as members.
Enabling ASM synchronization on a device group
You need to have already set up the BIG-IPsystems you want to
synchronize in a device trust and a device group. Application Security
Manager (ASM) must be provisioned on all the systems in the device group.
You can enable ASM synchronization on a device group to
synchronize security policies and configurations on all devices in the device group. You
do this task on one system; for example, the active system in an active-standby
pair.
- On the Main tab, click .The system displays a list of device groups of which this device is a member.
- ForDevice Group, select the device group whose members you want to synchronize.
- ClickSave.
The BIG-IP ASM systems that you want to share security policies
and configurations are part of a device group with ASM synchronization.
Synchronizing an ASM-enabled device group
You need to have set up the BIG-IP
Application Security Manager (ASM) systems you want to synchronize
in a Sync-Failover device group that is ASM-enabled.
You can manually synchronize security policies and configuration of systems in an
ASM-enabled device group.
- On one system in the ASM-enabled failover device group, create an application security policy.Because the two systems are not in sync, you see aChanges Pendingstatus message on the screen.
- Click theChanges Pendingmessage.You can also click .The Overview screen opens.
- In the Device Groups area of the screen, click the arrow next to the name of the relevant device group.The screen expands to show a summary and details of the sync status of the selected device group, as well as a list of the individual devices within the device group.
- In the Devices area of the screen, choose the device that shows a sync status ofChanges Pending.
- In the Sync Options area of the screen, selectPush the selected device configuration to the group.
- ClickSync.The BIG-IP system syncs the configuration data of the selected device to the other members of the device group.
- Verify that the devices are synchronized.For example, log in to another device in the device group and verify that the security policy you created also resides on that system. Click and see if the policy is listed.
Except for static self IP addresses, the entire set of BIG-IP configuration data
including ASM security policies and configuration is replicated on
one or more devices in the ASM-enabled device group. If the active device is not
available, the standby device becomes active and handles traffic.
You can create new security policies or update existing ones on any of the devices
in the group, or update the ASM configuration options. You can manually synchronize
changes you make on one device with the other devices in the ASM-enabled device group.
Implementation result
You have set up multiple BIG-IP® systems running Application Security Manager™ (ASM) so that they automatically synchronize their ASM
security policies and ASM configuration data. In addition, with this implementation, you can
manually synchronize the local traffic
configuration, as needed.
You can create new security policies or update existing ones on any of the devices in the
group, or update the ASM™ configuration options. Any ASM changes you make on
one device are automatically synchronized with the other devices in the ASM-enabled Sync-Only
device group.
If Attack Signatures
Update Mode
is scheduled for automatic update, the
attack signature update settings are synchronized. Each device in the device group updates itself
independently according to the configured schedule. If you manually upload attack signatures or
click Update Signatures
to update from the server, the update is
propagated to all of the devices in the device group.




