Manual Chapter :
Manipulating HTTPS Traffic by Using a
Third-Party Device
Applies To:
Show Versions
BIG-IP AAM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
BIG-IP APM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
BIG-IP Analytics
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
BIG-IP Link Controller
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
BIG-IP LTM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
BIG-IP PEM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
BIG-IP AFM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
BIG-IP DNS
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
BIG-IP ASM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0
Manipulating HTTPS Traffic by Using a
Third-Party Device
Overview: Manipulating HTTPS traffic by using
a third-party device
You can configure a BIG-IP® device to manage HTTPS traffic by using a
third-party device that can intercept and modify the traffic, as necessary. This configuration
provides SSL decryption, manipulation, and re-encryption while appearing relatively transparent
at layer 2.
When you configure a virtual server to use the Transparent Nexthop control, traffic matching
the virtual server is sent to the specified interface and the layer 2 addressing on the ingress
packet is preserved. Configuring the Transparent Nexthop to specify the VLAN that is configured
with the inspection device eliminates the need to configure a pool, NAT, SNAT, or other load
balancing functionality to the inspection device.
Transparent Nexthop functionality requires a
license that supports that functionality. If the Transparent Nexthop control does not appear on
the New Virtual Server screen, contact your F5 Networks support
representative to acquire the necessary license.
The basic process used in this configuration is as follows:
- A client sends an HTTPS request to a server by means of the BIG-IP device.
- The BIG-IP device intercepts the request, decrypts it, and forwards the request as cleartext to the inspection device.
- The inspection device receives and, as necessary, modifies the cleartext request.
- The inspection device forwards the cleartext request to the server by means of the BIG-IP device.
- The BIG-IP device re-encrypts the cleartext request and sends the ciphertext request to the server.
- The server sends a response to the client by means of the BIG-IP device.
- The BIG-IP device receives the response, decrypts it, and forwards the response as cleartext to the inspection device.
- The inspection device receives and, as necessary, modifies the cleartext response.
- The inspection device forwards the cleartext response to the client by means of the BIG-IP device.
- The BIG-IP device re-encrypts the cleartext response and sends the ciphertext response to the client.
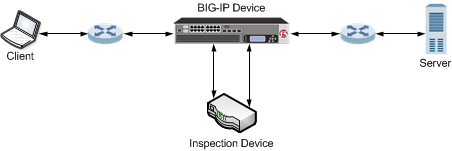
The following illustration shows an example of a BIG-IP device that manages HTTPS traffic
modified by a third-party device.
An example configuration of a BIG-IP device
managing HTTPS traffic modified by a third-party device.
Task
summary for manipulating HTTPS traffic thru third-party
devices
Complete these tasks to configure a BIG-IP® device to manage HTTPS traffic
by using a third-party device that can intercept and modify the traffic, as necessary.
Creating a VLAN
VLANs
represent a logical collection of
hosts that can share network resources, regardless of their physical location
on the network. You create a VLAN to associate physical interfaces with that
VLAN.- On the Main tab, click .The VLAN List screen opens.
- ClickCreate.The New VLAN screen opens.
- In theNamefield, type a unique name for the VLAN.
- In theTagfield, type a numeric tag, between 1-4094, for the VLAN, or leave the field blank if you want the BIG-IP system to automatically assign a VLAN tag.The VLAN tag identifies the traffic from hosts in the associated VLAN.
- If you want to use Q-in-Q (double) tagging, use theCustomer Tagsetting to perform the following two steps. If you do not see theCustomer Tagsetting, your hardware platform does not support Q-in-Q tagging and you can skip this step.
- From theCustomer Taglist, selectSpecify.
- Type a numeric tag, from 1-4094, for the VLAN.
The customer tag specifies the inner tag of any frame passing through the VLAN. - For theInterfacessetting,
- From theInterfacelist, select an interface number.
- From theTagginglist, selectUntagged.
- ClickAdd.
- For theHardware SYN Cookiesetting, select or clear the check box.When you enable this setting, the BIG-IP system triggers hardware SYN cookie protection for this VLAN.Enabling this setting causes additional settings to appear. These settings appear on specific BIG-IP platforms only.
- For theSyncache Thresholdsetting, retain the default value or change it to suit your needs.TheSyncache Thresholdvalue represents the number of outstanding SYN flood packets on the VLAN that will trigger the hardware SYN cookie protection feature.When theHardware SYN Cookiesetting is enabled, the BIG-IP system triggers SYN cookie protection in either of these cases, whichever occurs first:
- The number of TCP half-open connections defined in the LTM settingGlobal SYN Check Thresholdis reached.
- The number of SYN flood packets defined in thisSyncache Thresholdsetting is reached.
- For theSYN Flood Rate Limitsetting, retain the default value or change it to suit your needs.TheSYN Flood Rate Limitvalue represents the maximum number of SYN flood packets per second received on this VLAN before the BIG-IP system triggers hardware SYN cookie protection for the VLAN.
- ClickFinished.The screen refreshes, and displays the new VLAN in the list.
Creating a custom Client SSL profile
You create a custom Client SSL profile when you want the BIG-IP system to terminate client-side SSL traffic for the purpose of:
- Authenticating and decrypting ingress client-side SSL traffic
- Re-encrypting egress client-side traffic
- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Client SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- Selectclientsslin theParent Profilelist.
- Select theProxy SSLcheck box (the rest of the UI will collapse following this setting).
- Optionally, select theProxy SSL Passthroughcheck box.This option is often not needed. Review the Knowledge Center article K13385: Overview of the Proxy SSL feature for guidelines on when to enable this setting and its implications.
- Configure theCertificate Key Chain.TheCertificateandKeyunder ClientSSL profile are not used inProxy SSL(since the client and the server will eventually verify each other). F5 recommends leaving the default F5 cert/key pair.
- ClickFinished.
Creating a custom Server SSL profile
Create a custom server SSL profile to support SSL forward proxy.
- On the Main tab, click .The Server SSL profile list screen opens.
- ClickCreate.The New Server SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- ForParent Profile, retain the default selection,serverssl.
- Select theProxy SSLcheck box (the rest of the UI will collapse following this setting).
- Optionally, select theProxy SSL Passthroughcheck box.This option is often not needed. Review the Knowledge Center article K13385: Overview of the Proxy SSL feature for guidelines on when to enable this setting and its implications.
- Configure theCertificateandKeyusing the identical Certificate and Key details configured on the server.Import the details to the BIG-IP system prior to configuringProxy SSL.
- ClickFinished.
The custom Server SSL profile is now listed in the SSL Server profile list.
Task
summary for manipulating HTTPS traffic thru third-party
devices
Complete these tasks to configure a BIG-IP® device to manage HTTPS traffic
by using a third-party device that can intercept and modify the traffic, as necessary.
Creating a virtual server to manage
clientside HTTPS traffic
You can specify a virtual server
that manages clientside HTTPS traffic sent to a third-party device to manipulate
traffic.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- From theTypelist, selectStandard.
- For theDestination Address/Masksetting, confirm that theHostbutton is selected, and type the IP address in CIDR format.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.The IP address you type must be available and not in the loopback network.
- For theService Portsetting, type443in the field, or selectHTTPSfrom the list.
- From theProtocol Profile (Client)list, selectsplitsession-default-tcp.
- From theConfigurationlist, selectAdvanced.
- From theHTTP Profilelist, selecthttp.
- For theSSL Profile (Client)setting, from theAvailablelist, select a Client SSL profile, and using the Move button, move the name to theSelectedlist.
- From theVLAN and Tunnel Trafficlist, selectEnablerd on.
- For theVLANs and Tunnelssetting, move the clientside VLAN to theSelectedlist.
- From theTransparent Nexthoplist, select the VLAN that you created for the inspection device.
- ClickFinished.
The clientside HTTPS virtual server
appears in the Virtual Server List screen.
Creating a virtual server to manage
serverside traffic
You can specify a virtual server
that manages serverside traffic sent from a third-party device to manipulate traffic.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- From theTypelist, selectStandard.
- For theDestination Address/Masksetting, confirm that theHostbutton is selected, and type the IP address in CIDR format.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.The IP address you type must be available and not in the loopback network.
- For theService Portsetting, type80in the field, or selectHTTPfrom the list.
- From theConfigurationlist, selectAdvanced.
- From theProtocol Profile (Server)list, selectsplitsession-default-tcp.
- From theHTTP Profilelist, selecthttp.
- For theSSL Profile (Server)setting, from theAvailablelist, select a Server SSL profile, and using the Move button, move the name to theSelectedlist.
- From theVLAN and Tunnel Trafficlist, selectEnabled on.
- For theVLANs and Tunnelssetting, move the VLAN that you created for the inspection device to theSelectedlist.
- From theTransparent Nexthoplist, select the serverside VLAN.
- ClickFinished.
The serverside HTTPS virtual server
appears in the Virtual Server List screen.
Creating a VLAN group
VLAN groups consolidate Layer 2 traffic from two or
more separate VLANs.
- On the Main tab, click .The VLAN Groups list screen opens.
- From the VLAN Groups menu, choose List.
- ClickCreate.The New VLAN Group screen opens.
- In the General Properties area, in theVLAN Groupfield, type a unique name for the VLAN group.
- For theVLANssetting, from theAvailablefield select theinternalandexternalVLAN names, and click<<to move the VLAN names to theMembersfield.
- ClickFinished.





