Manual Chapter :
Securing Client-Side SMTP Traffic
Applies To:
Show Versions
BIG-IP AAM
- 14.0.1, 14.0.0
BIG-IP APM
- 14.0.1, 14.0.0
BIG-IP Analytics
- 14.0.1, 14.0.0
BIG-IP Link Controller
- 14.0.1, 14.0.0
BIG-IP LTM
- 14.0.1, 14.0.0
BIG-IP PEM
- 14.0.1, 14.0.0
BIG-IP AFM
- 14.0.1, 14.0.0
BIG-IP DNS
- 14.0.1, 14.0.0
BIG-IP ASM
- 14.0.1, 14.0.0
Securing Client-Side SMTP Traffic
Overview: Securing client-side SMTP traffic
You can add SSL encryption to SMTP traffic quickly and easily, by configuring an SMTPS profile
on the BIG-IP® system.
SMTPS
is a method for securing Simple Mail Transport Protocol
(SMTP) connections at the transport layer.Normally, SMTP traffic between SMTP servers and clients is unencrypted. This creates a privacy
issue because SMTP traffic often passes through routers that the servers and clients do not
trust, resulting in a third party potentially changing the communications between the server and
client. Also, two SMTP systems do not normally authenticate each other. A more secure SMTP server might
only allow communications from other known SMTP systems, or the server might act differently with
unknown systems.
To mitigate these problems, the BIG-IP system includes an SMTPS profile that you can configure.
When you configure an SMTPS profile, you can activate support for the industry-standard STARTTLS
extension to the SMTP protocol, by instructing the BIG-IP system to either allow, disallow, or
require STARTTLS activation for SMTP traffic. The STARTTLS extension effectively upgrades a
plain-text connection to an encrypted connection on the same port, instead of using a separate
port for encrypted communication.
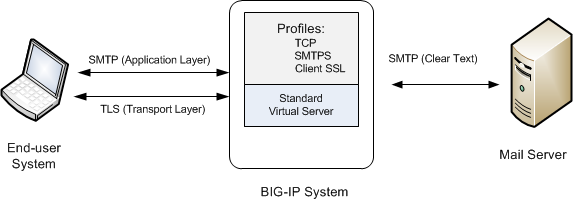
This illustration shows a basic configuration of a BIG-IP system that uses SMTPS to secure SMTP traffic between the BIG-IP system and an SMTP mail server.
Sample BIG-IP configuration for SMTP traffic with STARTTLS activation
Task summary
for securing client-side SMTP traffic
To configure the BIG-IP ®system to process Simple Mail Transport Protocol
(SMTP) traffic with SSL functionality, you perform a few basic tasks.
Creating an SMTPS profile
This task specifies that STARTTLS authentication and encryption should be required
for all client-side Simple Mail Transport Protocol (SMTP) traffic. When you require
STARTTLS for SMTP traffic, the BIG-IP system effectively upgrades
SMTP connections to include SSL, on the same SMTP port.
- On the Main tab, click .The SMTPS profile list screen opens.
- ClickCreate.The New SMTPS Profile screen opens.
- In theNamefield, type a unique name for the profile.
- Select theCustomcheck box.
- From theSTARTTLS Activation Modelist, selectRequire.
- ClickFinished.
The BIG-IP system is now required to activate STARTTLS for all client-side SMTP traffic.
Create a Client SSL profile
You create a Client SSL profile when you want the BIG-IP system to
authenticate and decrypt/encrypt client-side application traffic.
- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Client SSL Profile screen opens.
- Configure all profile settings as needed.
- ClickFinished.
After creating the Client SSL profile and assigning the profile to a virtual server,
the BIG-IP system can apply SSL security to the type of application traffic for which
the virtual server is configured to listen.
Creating a virtual server and load-balancing pool
You use this task to create a virtual server, as
well as a default pool of Simple Mail Transport Protocol (SMTP) servers. The virtual
server listens for and applies the configured STARTTLS activation to client-side SMTP
application traffic. The virtual server then forwards the SMTP traffic on to the
specified server pool.
Using this task, you assign an SMTPS profile to the virtual server instead of an SMTP profile. You must also assign a Client SSL profile.
- On the Main tab, clickThe Virtual Server List screen opens.
- Click theCreatebutton.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- In theDestination Address/Maskfield, type an address, as appropriate for your network.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.
- In theService Portfield, type25or selectSMTPfrom the list.
- From theConfigurationlist, selectBasic.
- For theSSL Profile (Client)setting, in theAvailablebox, select a profile name, and using the Move button, move the name to theSelectedbox.
- From theSMTPS Profilelist, select the SMTPS profile that you previously created.
- In the Resources area of the screen, for theDefault Poolsetting, click theCreate (+)button.The New Pool screen opens.
- In theNamefield, type a unique name for the pool.
- In the Resources area, for theNew Memberssetting, select the type of new member you are adding, then type the information in the appropriate fields, and clickAddto add as many pool members as you need.
- ClickFinishedto create the pool.The screen refreshes, and reopens the New Virtual Server screen. The new pool name appears in theDefault Poollist.
- ClickFinished.
After performing this task, the virtual server
applies the custom SMTPS and Client SSL profiles to incoming SMTP traffic.
Implementation result
After you have created an SMTPS profile and a Client SSL profile and assigned them to a virtual server, the BIG-IP system listens for client-side SMTP traffic on port 25. The BIG-IP system then activates the STARTTLS method for that traffic, to provide SSL security on that same port, before forwarding the traffic on to the specified server pool.





