Manual Chapter :
Configuring Remote Desktop Access
Applies To:
Show Versions
BIG-IP APM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
Configuring Remote Desktop Access
What are remote desktops?
Remote desktops in Access Policy Manager allow users to access the
following types of internal servers in virtual desktop sessions:
- Microsoft Remote Desktop servers
- Citrix servers
- VMware View Connection servers
Remote desktop resources of type Citrix and VMware View require HTTPS
virtual servers.
You can configure remote desktops by name or by their internal IP addresses, and grant or deny
users the ability to set up their own favorites.
What is Microsoft remote desktop?
Using an Access Policy Manager (APM) RDP type
remote desktop, clients can access a server that runs Microsoft Remote Desktop Services.
Microsoft Remote Desktop servers run the Microsoft Remote Desktop Protocol (RDP) server.
RDP
is a protocol that provides a graphical interface to another computer on a
network. To provide Microsoft RDP connections natively, APM provides these remote
desktop resources:
- APM webtop
- APM webtop provides a Java Client option in the remote desktop configuration. The option supports native connections for Windows, Mac, and Linux clients. When this option is selected, a user on any compatible platform is presented with a simple Java Client interface to the Microsoft RDP server with reduced visual display features.
- APM as a remote desktop gateway
- With proper BIG-IP system configuration, Microsoft RDP clients can use APM as a gateway. The configuration supports Microsoft RDP clients on Windows, Mac, iOS, and Android. When a user types the address or hostname of the gateway into an RDP client and specifies a particularly configured virtual server for it, APM authorizes the client. When the client requests connections to resources on backend servers, APM authorizes the access.
For support information, refer to
BIG-IP APM Client Compatibility Matrix
on AskF5 at http://support.f5.com/
. What is Citrix remote desktop?
Citrix® remote desktops are supported by Citrix XenApp™ and ICA clients. With Access Policy Manager you can configure
clients to access servers using Citrix terminal services. You provide a location from which a
client can download and install a Citrix client for a Citrix ICA connection.
What is VMware View desktop?
VMware View is VMware's virtual desktop infrastructure (VDI) software that runs a View Desktop
on a user's PC from the servers in a data center. You can integrate APM with VMware View
Connection Servers and present View Desktops on dynamic APM webtops. APM authenticates users on a
View Connection Server and displays the View Desktops. Refer to
Presenting a View Desktop
on an APM Webtop
for how to set this up.About ACLs to control access from remote
desktop resources
When you create a remote desktop resource, Access Policy Manager (APM) automatically creates an allow ACL for the IP addresses and ports
specified in the resource. To disallow access to any other IP addresses and ports, you must
create ACLs that deny access to them and assign the ACLs in the per-session policy. F5
recommends that you create an ACL that rejects access to all connections and put it last in
the ACL order.
Configuring an ACL
to reject all connections
You can place an access control list (ACL) that
rejects all connections last in the ACL order to keep users from accessing any host and
port combinations other than those to which they have been explicitly allowed access by
the other ACLs assigned to the policy.
- On the Main tab, click .The User-defined ACLs screen opens.
- ClickCreate.The New ACL screen opens.
- In theNamefield, type a name for the access control list.
- From theTypelist, retain the default valueStatic.
- In theDescriptionfield, add a description of the access control list.
- From theACL Orderlist, selectLastto add the ACL at the last position in the list.
- Click theCreatebutton.The ACL Properties screen displays.
- In the Access Control Entries area, clickAddto add an entry.The New Access Control Entry screen displays.
- From theTypelist, selectL4.
- For theSource IP Address,Source Port(s),Destination IP Address, andDestination Port(s)fields, retain the default valueAny.
- From theActionlist, selectReject.The reject action drops the packet. On TCP flows, it also sends a TCP RST message. On UDP flows, it also sends proper ICMP messages. On other protocols, it drops the packet silently.
- ClickFinished.
To use the ACL, assign it to a session using an
Advanced Resource Assign or ACL Assign action in a per-session policy.
If you assign
this ACL and Network Access or Portal Access resources to the same policy, you might
need to also create and assign ACLs that allow access for Network Access and Portal
Access resources.
Configuring a resource
for Citrix remote desktops
You
can configure BIG-IP APM so users can access Citrix internal srvers in virtual desktop sessions.
Refer to the online help for more information about the parameters you can configure for remote
desktops.
- On the Main tab, click .The Remote Desktops screen opens.
- ClickCreate.The New Resource screen opens.
- In theNamefield, type a name for this desktop resource.
- From theTypelist, selectCitrix.
- In theDescriptionfield, type a description for the new resource.
- For theDestinationsetting, specify an IP address as your destination, and accept or change thePort.
- For theServer Side SSLsetting, select the check box to provide SSL functionality between the BIG-IP system and the resource server.If this option is selected, the system changes the port number from80to443.
- For theAuto Launchoption, select whether to enable auto launch for Citrix.If you selectEnable, the first application runs automatically.
- In theCustom Parametersfield, type one or more lines to specify custom settings.These parameters affect the rendering of certain features for Citrix. A line should contain a section name enclosed in brackets ([ ]) or a name-value pair separated by an equal (=) sign.
- For theEnable SSOsetting, select whether to enable single sign-on to the server.
- ClickFinished.
Configuring a
resource for RDP remote desktop session host
You can configure BIG-IP APM so users can access
Microsoft Remote Desktop internal srvers in virtual desktop sessions. Refer to the
online help for more information about the parameters you can configure for remote
desktops.
- On the Main tab, click .The Remote Desktops screen opens.
- ClickCreate.The New Resource screen opens.
- In theNamefield, type a name for this desktop resource.
- From theTypelist, selectRDP.
- In theDescriptionfield, type a description for the new resource.
- For theServer Type, selectRemote Desktop Session Host.
- For theClient Type, selectNative.Nativeis the only client type recommended because theJavaandActiveXoptions are deprecated.
- For theDestinationsetting, specify an IP address as your destination, and accept or change thePort.
- In theCustom Parametersfield, type one or more lines to specify custom settings.These parameters affect the rendering of certain features for RDP. For Microsoft RDP, a line should inclue a name, type, and a value, with a colon as a separator, shown in the examples below:
- screen mode id:i:1
- use multimon:i:0
- desktopwidth:i:1440
- desktopheight:i:900
- session bpp:i:32
- ForEnable SSO, select whether to enable single sign-on to the server.
- ClickFinished.
You have now configured an RDP resource for a remote desktop session host.
Configuring a
resource for RDP remote desktop web access
You can configure BIG-IP APM so users can access
Microsoft Remote Desktop internal srvers in virtual desktop sessions. Refer to the
online help for more information about the parameters you can configure for remote
desktops.
- On the Main tab, click .The Remote Desktops screen opens.
- ClickCreate.The New Resource screen opens.
- In theNamefield, type a name for this desktop resource.
- From theTypelist, selectRDP.
- In theDescriptionfield, type a description for the new resource.
- ForServer Type, selectRemote Desktop Web Access.
- For theClient Type, selectNative.Nativeis the only client type recommended because theJavaandActiveXoptions are deprecated.
- For theDestinationsetting, specify an IP address as your destination , and accept or change thePort.
- In theCustom Parametersfield, type one or more lines to specify custom settings.These parameters affect the rendering of certain features for RDP. For Microsoft RDP, a line should inclue a name, type, and a value, with a colon as a separator, shown in the examples below:
- screen mode id:i:1
- use multimon:i:0
- desktopwidth:i:1440
- desktopheight:i:900
- session bpp:i:32
- ForEnable SSO, selectEnable.
- ClickFinished.
You have now configured an RDP resource for APM webtop.
Configuring an access
policy to include a remote desktop
This
procedure is applicable if you want to configure Access Policy Manager for Citrix or Microsoft
RDP terminal services.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- Click the name of the access profile for which you want to edit the access policy.The properties screen opens for the profile you want to edit.
- On the menu bar, clickAccess Policy.
- In the General Properties area, click theEdit Access Policy for Profilelink.profile_nameThe visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- On the Assignment tab, select theAdvanced Resource Assignagent, and then clickAdd Item.The Resource Assignment screen opens.
- Click theAdd/Deletelink below the entry.The screen changes to display resources on multiple tabs.
- On the Remote Desktop tab, select the remote desktop that you configured previously.
- On the Static ACL tab, select an ACL that rejects all connections.Adding an ACL that is last in order and rejects all connections keeps users from accessing any host and port combinations other than those to which they have been explicitly allowed access by the other ACLs assigned to the policy.
- On the Webtop tab, select a full webtop.
- Select any other resources that you want to assign to the policy.If you assign a Network Access resource to the policy, be sure to also assign an ACL that allows access to the resources that you want users to have. Otherwise, the ACL that rejects all connections blocks access.If you assign a Portal Access resource to the policy, be sure to also assign an ACL that allows access to all parts of the web sites specified in the start URI or hosted content fields of the Portal Access configuration. Otherwise, the ACL that rejects all connections blocks access.
- ClickUpdate.
- ClickSave.
Your
remote desktop is assigned to the session along with system-defined (allow) and user-defined
(deny) ACLs.
To
complete the process, you must apply the access policy, and associate the access policy and
connectivity profile with a virtual server so users can launch the remote desktop session.
To ensure that logging is configured to meet your
requirements, verify the log settings for the access profile.
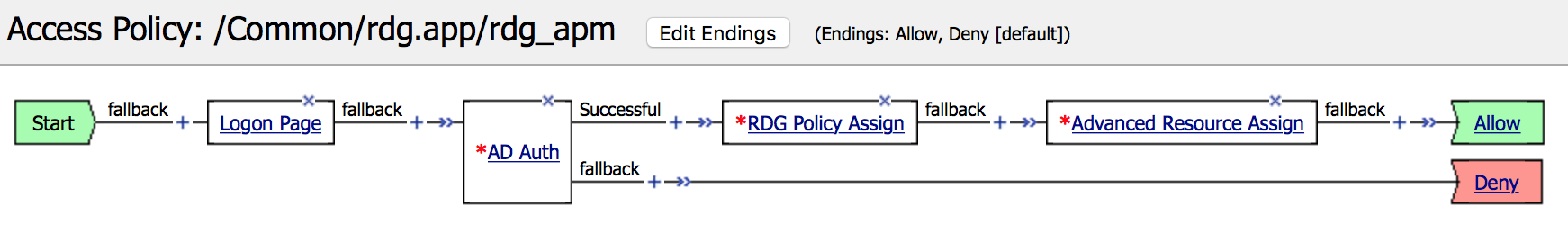
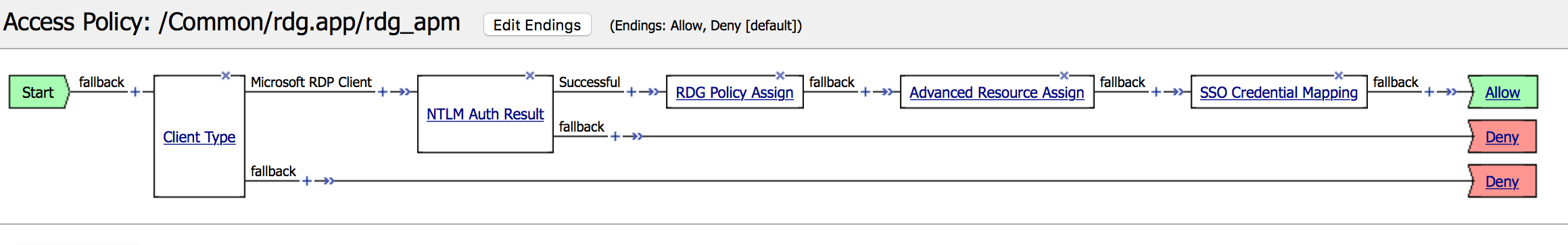
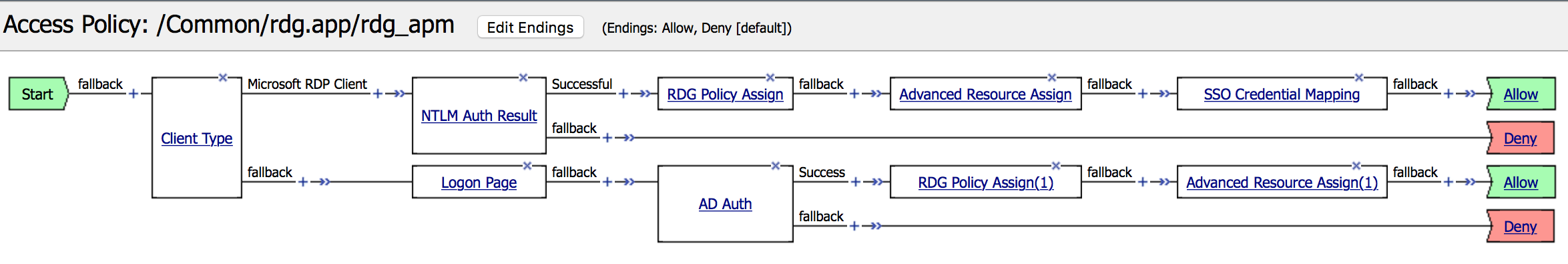
Sample access policies for Native RDP client and APM webtop
These sample access policies are a reference for configuring RDP for APM webtop, a standalone
client, or both.
Access policy for an APM webtop
Access policy for a standalone client
Access policy for both an APM Webtop and a standalone client
Attaching an access
policy to a virtual server for remote desktops
When
creating a virtual server for an access policy, specify an IP address for a single host as the
destination address.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- For theDestination Address/Masksetting, confirm that theHostbutton is selected, and type the IP address in CIDR format.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.The IP address you type must be available and not in the loopback network.
- If using Citrix or VMware View remote desktops, set theService Portto443and select anSSL Profile (Client).Remote desktop resources of type Citrix and VMware View require HTTPS virtual servers. You can still usehttpfor the HTTP Profile.
- For theHTTP Profile (Client)setting, verify that the default HTTP profile,http, is selected.
- In the Access Policy area, from theAccess Profilelist, select the access profile that you configured earlier.
- If you are using a connectivity profile, from theConnectivity Profilelist, select the connectivity profile.
- If you are creating a virtual server to use with portal access resources in addition to remote desktops, from theRewrite Profilelist, select the defaultrewriteprofile, or another rewrite profile you created.
- If you want to provide connections to allow Java rewriting for portal access or support a per-app VPN connection that is configured on a mobile device, select theApplication Tunnels (Java & Per-App VPN)check box.You must enable this setting to make socket connections from a patched Java applet. If your applet does not require socket connections, or only uses HTTP to request resources, this setting is not required.
- If you want to provide native integration with an OAM server for authentication and authorization, select theOAM Supportcheck box.You must have an OAM server configured in order to enable OAM support.
- ClickUpdate.
The
access policy is now associated with the virtual server.
Verifying log settings for the access profile
Confirm that the correct log settings are selected
for the access profile to ensure that events are logged as you intend.
Log settings
are configured in the area of the product. They enable and disable logging for access
system and URL request filtering events. Log settings also specify log publishers
that send log messages to specified destinations.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- Click the name of the access profile that you want to edit.The properties screen opens.
- On the menu bar, clickLogs.The access profile log settings display.
- Move log settings between theAvailableandSelectedlists.You can assign up to three log settings that enable access system logging to an access profile. You can assign additional log settings to an access profile provided that they enable logging for URl request logging only.Logging is disabled when theSelectedlist is empty.
- ClickUpdate.
An access profile is in effect when it is assigned to a virtual server.





