Manual Chapter :
Protecting Internal Resources
Per-Request
Applies To:
Show Versions
BIG-IP APM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
Protecting Internal Resources
Per-Request
Overview: Protecting internal resources on a per-request basis
You can use a per-request policy to protect your internal resources and to be more selective
about who accesses them and when. After a user starts a session, a per-request policy makes it
possible to apply additional criteria for access any time the user makes a request. These steps
are for use in a reverse proxy configuration; that is, with APM and LTM set up for web access management.
You cannot use subroutines in macros within per-request policies.
Creating a per-request policy
You must create a per-request policy before you can configure it in the visual
policy editor.
- On the Main tab, click .The Per-Request Policies screen opens.
- ClickCreate.The General Properties screen opens.
- In theNamefield, type a name for the policy and clickFinished.A per-request policy name must be unique among all per-request policy and access profile names.The policy name appears on the Per-Request Policies screen.
Configuring policies to branch by local database user
group
If you plan to look up local database groups
from the per-request policy, you must configure local database-related items in the
access policy and the per-request policy to use the same session variable.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- On a policy branch, click the(+)icon to add an item to the policy.A popup screen displays actions on tabs, such as General Purpose and Authentication, and provides a search field.
- In the search field, typelocal, selectLocal Database, and clickAdd Item.A popup properties screen opens.
- Configure properties for the Local Database action:
- From theLocalDB Instancelist, select a local user database.
- ClickAdd new entryA new line is added to the list of entries with the Action set toReadand other default settings.
- In theDestinationcolumn in theSession Variablefield, type the name of the variable in which to store the user groups retrieved from the local database.In the per-request policy, the default value that the LocalDB Group Lookup item uses issession.localdb.groups. If you enter a differentvalue, note it. You will need it to update the advanced expression in the LocalDB Group Lookup item in the per-request policy.
- In theSourcecolumn from theDB Propertylist, selectgroups.
- ClickSave.The properties screen closes. The policy displays.
This is not a complete access policy, but you can return to it and complete it later. You can close the visual policy editor or leave it open.The access policy includes a Local Database action that can read groups into a session variable. - On the Main tab, click .The Per-Request Policies screen opens.
- In theNamefield, locate the policy that you want to update, then in thePer-Request Policyfield, click theEditlink.The visual policy editor opens in another tab.
- Click the(+)icon anywhere in the per-request policy to add a new item.
- In the search field, typelocal, selectLocalDB Group Lookup, and clickAdd Item.A popup properties screen opens.
- Click the Branch Rules tab.
- Click thechangelink in the entry for the default expression.A popup screen opens.
- If the session variable you typed in the access policy Local Database action wassession.localdb.groups, perform these substeps.
- In theUser is a member offield, removeMY_GROUPand type the name of a group.
- ClickFinished.The popup screen closes.
- ClickSave.The properties screen closes and the policy displays.
- If you typed a session variable other thansession.localdb.groupsin the access policy Local Database action, perform these substeps.
- Click the Advanced tab.In the field, this expression displays.expressionisexpr{ [mcget{session.localdb.groups}]contains"MY_GROUP" }
- In the expression, replacesession.localdb.groupswith the name of the session variable you typed into the Local Database action.
- In the expression, replaceMY_GROUPwith the name of a group that should match a local database group.
- ClickFinished.The popup screen closes.
- ClickSave.The properties screen closes and the policy displays.
This is not a complete per-request access policy, but you can return to it and complete it later.
The access and per-request policies are configured to use the same session variable.
The access policy is configured to support the use of LocalDB Group Lookup in the
per-request policy.
Complete the configuration of the access and
per-request policies.
Categorizing URLs
using custom categories in a per-request policy
These steps apply to a BIG-IP system on which URL categories
are available only by creating them in Access Policy Manager (APM).
Look up the category for a URL request and use it
in
a policy branch rule, or to
assign
a URL filter, and so on.
These steps
provide guidance for adding items to control traffic based on the URL category; they
do not specify a complete per-request policy.
- On the Main tab, click .The Per-Request Policies screen opens.
- In theNamefield, locate the policy that you want to update, then in thePer-Request Policyfield, click theEditlink.The visual policy editor opens in another tab.
- Add aCategory Lookupitem and set its properties:A Category Lookup item triggers event logging for URL requests and provides categories for a URL Filter Assign item.
- From theCategorization Inputlist, select an entry based on the type of traffic to be processed. .
- For HTTP traffic, selectUse HTTP URI (cannot be used for SSL Bypass decisions).
- For SSL-encrypted traffic, selectUse SNI in Client Hello (if SNI is not available, use Subject.CN).
- Use Subject.CN in Server Certis not supported for reverse proxy.
- ForCategory Lookup Type, you can only retain the default settingProcess custom categories only.
- ClickSave.The properties screen closes. The policy displays.
- To add aURL Filter Assignitem, do so anywhere on a branch after a Category Lookup item.A URL filter applies to the categories that a Category Lookup item returns. If the filter specifies theBlockaction for any URL category, URL Filter Assign blocks the request.If URL Filter Assign does not block the request and the filter specifies the confirm action for any URL category, URL Filter Assign takes theConfirmper-request policy branch and the policy exits on the ending for it.
- From theURL Filterlist, select a URL filter.
- To simplify the display in the visual policy editor if the URL filter does not specify confirm actions, select Branch Rules, and clickxon theConfirmentry.
- ClickSave.The properties screen closes and the policy displays.
Now the per-request policy includes
an item
that
looks
up the URL
category.
You can add other items to the policy to control access according to your requirements.
SSL bypass and SSL intercept are not supported when you are protecting internal
resources from incoming requests. They are supported in a forward proxy
configuration.
A per-request policy goes into effect when you add it to a
virtual server.
Configuring a
per-request policy to control access to applications
Access Policy Manager (APM) supports a preset group of application families and
applications. You can configure your own application filters or use one of the filters
that APM provides: block-all, allow-all, and default.
Configure a per-request policy to specify the
logic that determines whether to allow access to the applications or application
families.
This task provides the steps for adding items to control
requests based on the application name or application family or based on an
application filter. It does not specify a complete per-request policy.
- On the Main tab, click .The Per-Request Policies screen opens.
- In theNamefield, locate the policy that you want to update, then in thePer-Request Policyfield, click theEditlink.The visual policy editor opens in another tab.
- Add anApplication Lookupitem to the policy.
- Click the(+)icon anywhere in the per-request policy to add a new item.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- From the General Purpose tab, selectApplication Lookup, and clickAdd Item.A Properties popup screen opens.
- ClickSave.The Properties screen closes. The visual policy editor displays. A single branch, fallback, follows theApplication Lookupitem.
- To branch by application family or application name, add branch rules to theApplication Lookupitem.
- Click the name of the application lookup item.A Properties popup screen displays.
- Click the Branch Rules tab.
- ClickAdd Branch Rule.A new entry withNameandExpressionsettings displays.
- Click thechangelink in the new entry.A popup screen opens.
- Click theAdd Expressionbutton.Settings are displayed.
- ForAgent Sel, selectApplication Lookup.
- ForConditionselectApplication FamilyorApplication Name.
- From the list,Application Family isorApplication Name is, select a family or name.
- ClickAdd Expression.The expression displays.
- Continue adding branches and when you are done, clickFinished.The popup screen closes. The Branch Rules popup screen displays.
- ClickSave.The visual policy editor displays.
Newly created branches follow theApplication Lookupitem. - To apply an application filter to the request, add anApplication Filter Assignitem on a branch somewhere after the Application Lookup item.A Properties popup screen displays.
- From theApplication Filterlist, select an application filter and clickSave.The popup screen closes.
To put the per-request policy into effect, add it
to the virtual server.
To support
application filtering, classification must be enabled on the virtual server.
Configuring a
per-request policy to branch by group or class
Add a group or class lookup to a per-request
policy when you want to branch by user group or class.
The access
policy must be configured to populate session variables for a group or class lookup
to succeed. This task provides the steps for adding items to branch by group or
class. It does not specify a complete per-request policy.
- On the Main tab, click .The Per-Request Policies screen opens.
- In theNamefield, locate the policy that you want to update, then in thePer-Request Policyfield, click theEditlink.The visual policy editor opens in another tab.
- On a policy branch, click the(+)icon to add an item to the policy.The actions you can use for building a per-request policy are displayed on a popup screen with actions on tabs, such as Authentication, Classification, and General Purpose, and a search field.
- On the Authentication tab, select an option:AD Group Lookup,LDAP Group Lookup, orRADIUS Class Lookupto the per-request policy.
- ClickAdd Item.A properties popup screen opens.
- Click the Branch Rules tab.
- To edit an expression, click thechangelink.An additional popup screen opens, displaying the Simple tab.
- Edit the default simple expression to specify a group or class that is used in your environment.In an LDAP Group Lookup item, the default simple expression isUser is a member ofCN=MY_GROUP, CN=USERS, CN=MY_DOMAIN. You can use the simple expression editor to replace the default values.
- ClickFinished.The popup screen closes.
- ClickSave.The popup screen closes. The visual policy editor displays.
A per-request policy goes into effect when you add it to a
virtual server.
Adding a
per-request policy to the virtual server
To add per-request processing to a configuration, associate the
per-request policy with the virtual server.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server.
- In the Access Policy area, from thePer-Request Policylist, select the policy that you configured earlier.
- ClickUpdate.
The per-request policy is now associated with the virtual server.
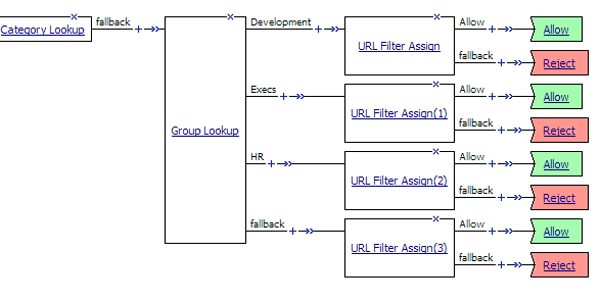
Example policy: URL filter per user
group
Each URL Filter Assign item in this per-request policy example should specify a filter that is
applicable to the user group.
URL filter based on group membership
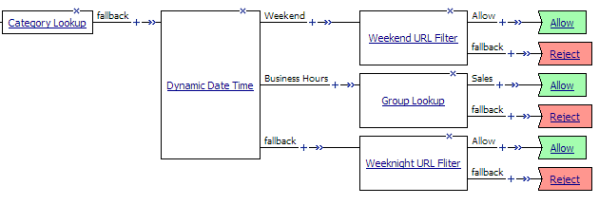
Example policy: Access control by date, time,
and user group
This per-request policy example applies specific URL filters for weekends and weeknights, and
restricts access during work hours based on user group.
Deny or allow access based on date and time and group membership
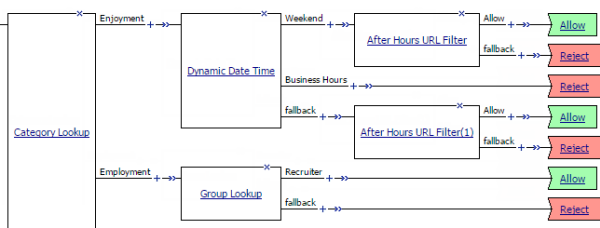
Example policy: User-defined
category-specific access control
In this per-request policy example, only recruiters are allowed to access URLs in the
user-defined category Employment. The policy also restricts access to entertaining videos during
business hours.
Category-specific access restrictions
(using user-defined categories)
Example policy: Application lookup and
filter
Application access control by application family, application name, and application
filter
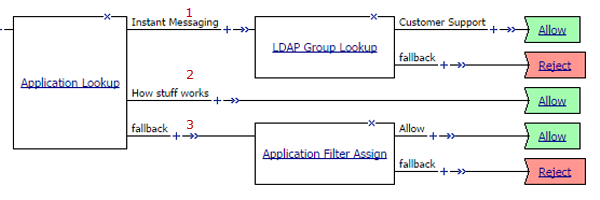
1 | A user-defined branch for the instant messaging application family. |
2 | A user-defined branch for a specific application. |
3 | The default fallback branch, on which an application filter is applied. Application
Filter Assign needs the information provided by Application Lookup. |





