Manual Chapter :
Using APM as an OAuth 2.0 Authorization Server
Applies To:
Show Versions
BIG-IP APM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
Using APM as an OAuth 2.0 Authorization Server
Overview: Configuring APM as an OAuth 2.0
authorization server
You can configure a BIG-IP® system with Access Policy Manager (APM) to act as an OAuth authorization server. OAuth
client applications and resource servers can register to have APM authorize requests.
Task summary
Registering a client application for OAuth services
For a client application to obtain
OAuth tokens and OAuth authorization codes from the BIG-IP system,
you must register it with Access Policy Manager (APM).
- On the Main tab, click .The Client Application screen opens.
- ClickCreate.
- In theNamefield, type a name for the object.
- In theApplication Namefield, type the application name.
- In the Customization Settings for English area in theCaptionfield, type a caption.APM displays this caption as the name of the application on an Authorization screen if you choose to display one.
- In the Security Settings area, forAuthentication Type, select one of the options:
- None- This is typically used in conjunction with the Implicit grant type, which does not use a secret or a certificate. For grant types other thanImplicit, the other options provide better security.
- Secret- This is the default setting. If this is selected, APM generates this secret for the client and you can request that APM regenerate the secret.
- Certificate- Uses the client certificate. If this is selected, theClient Certificate Distinguished Namefield displays.
- If theClient Certificate Distinguished Namefield displays, leave it blank or type a name.If you leave it blank, APM accepts any valid client certificate. If you specify a name, APM accepts only the specific valid client certificate with the specified Distinguished Name.This is a sample Distinguished Name for the client certificate:emailAddress=w.smith@f5.com,CN=OAuth AS Project Client2 Cert,OU=Product Development,O=F5 Networks,ST=CA,C=US
- ForScope, select one or more and move them to theSelectedfield.
- FromGrant Type, select one or more of the options:
- Authorization Code / Hybrid- The client must authenticate with the authorization server (APM) to get a token.
- Implicit- The client gets a token from the authorization server (APM) without authenticating to it. (Refresh tokens are not available with this grant type.)
- Resource Owner Password Credentials- The client goes directly to the authorization server and uses the resource owner credentials to obtain a token.
- ForRedirect URI(s)(if displayed), type a fully qualified URI, clickAdd, and repeat as needed.Redirect URI(s) form a list of URIs to which the OAuth authorization server can redirect the resource owner’s user agent after authorization is obtained for an authorization code or implicit grant type.
- ForSupport OpenID Connect, select Enabled to select OpenID Connect support.Client applications retreive an ID token and an access token.
- To apply the token management settings from an OAuth profile, perform these substeps:
- In the Token Management Configuration area, retain selection of theEnabledcheck box.The token management configuration settings in an OAuth profile apply to client applications assigned to that profile except when this setting is disabled.
- Skip to step 13.
- To manage tokens in a manner that is distinct for this client application, perform these substeps:
- In the Token Management Configuration area, clear theEnabledcheck box.Additional fields display.
- Update any of the additional fields.
- ClickFinished.
APM generates a client ID for the
application. If the
Authentication Type
is set to
Secret
, APM generates a secret. The application displays on
the Client Application screen.Registering a resource server for OAuth services
For Access Policy
Manager (APM) as an OAuth authorization server to accept
token introspection requests from a resource server for token validation, you must
register the resource server with APM.
- On the Main tab, click .The Resource Server screen displays.
- ClickCreate.
- In theNamefield, type a name for the object.
- ForAuthentication Type, select one of these:
- None- This option requires no authentication when the resource server sends a token introspect request to the OAuth authorization server to get the token validated.
- Secret- For this option, APM generates this secret and you can request that APM regenerate the secret.
- Certificate- This is the default setting. If this is selected,Resource Server Certificate Distinguished Namefield displays.
- IfResource Server Certificate Distinguished Namedisplays, leave it blank or type a name.If you leave it blank, APM accepts any valid client certificate. If you specify a name, APM accepts only the specific valid client certificate with the specified Distinguished Name.This is a sample Distinguished Name for the client certificate:emailAddress=w.smith@f5.com,CN=OAuth AS Project Client2 Cert,OU=Product Development,O=F5 Networks,ST=CA,C=US
- ClickFinished.
The new resource server displays on
the list.
Configuring OAuth
scopes of access for client apps
When Access Policy Manager (APM) acts as an OAuth
authorization server, you must configure scopes of access. (A
scope
specifies a string, and optionally, a value, that
represents a resource.)- On the Main tab, click .The Scope screen opens.
- ClickCreate.
- In theNamefield, type a name for the object.
- In theScope Namefield, type a name for the scope.
- In theScope Valuefield, type a value for the scope.
- In the Customization Settings for English area, in theCaptionfield, type a caption.
- In theDetailed Descriptionfield, type a description of the access that the client application needs.If you choose to display an Authorization screen, APM displays the contents of this field on it; or, if this field is blank, APM displays the contents of theCaptionfield.Here are some examples:Access your profileorUpdate your tasks, projects, and workspace.
- ClickFinished.
Configuring JWT claims
You can configure the claims that you want to
include in the JSON Web Tokens (JWTs). (A
claim
specifies a string, and optionally, a value, that represents a resource.) This is only
required if you plan to specify claims in your JWTs.- On the Main tab, select .
- ClickCreate.
- In theNamefield, type a name for the configuration.
- FromClaim Type, select the required claim type from the list. Available options areString,Number,Boolean, orCustom.
- In theClaim Namefield, type a name for the claim.
- In theClaim Valuefield, type a value for the claim depending on its type.Claim TypeValue can beStringEnter ASCII characters or session variable in the Claim Value field. Do not encapsulate the provided claim value in the escaped quotes (\").NumberEnter a valid number or a session variable in the Claim Value field.BooleanEntertrue,false, or a session variable in the Claim Value field.CustomSelect this option when the claim value is a JSON value type array, object, or null in the Claim Value field.When the Claim Type is set to Custom, you can use both Object (array, null) or String (claim type String is recommended) in the claim value. Ensure the string value is encapsulated in the escaped quotes (\"). For example, if an array contains strings, number, boolean, and null, encapsulate only the string values in quotes within the array. Claim Value = [\"example\", \"Strings\", 5, true, null].Note:For BIG-IP versions 14.1.4.2 or lower, you do not need to encapsulate the string value in escaped quotes for the Custom claim type.
- ClickSave.The newly created claim displays on the list.
You associate claims with tokens an OAuth
bearer SSO configuration.
Configuring JSON web keys (JWKs)
A JSON web key configuration specifies a
cryptographic JSON web key (JWK). You configure JWKs for the system to use to sign the
JSON web tokens that it issues. For example, you use JWK key configurations when setting
up OAuth bearer single sign-on.
- On the Main tab, select .The Key Configuration screen opens.
- ClickCreate.
- In theNamefield, type a name.
- InID, type the ID.
- ForType, selectRSA,Octet, orElliptic Curve.Additional parameters display for the type that you select.
- ForSigning Algorithm, select any one.
- For theOctettype, you only need to configure one additional setting:
- InShared Secret, type the secret.To maximize the security of the algorithm, use enough characters so that the resulting key size matches the block size for the signing algorithm: forHS256, 32 characters; forHS384, 48 characters; forHS512, 64 characters.
- ClickSave.The newly created JWK displays on the list.
- For theRSAorElliptic Curvekey types, configure the settings in the Certificates areas:
- ForCertificate File, select a certificate.Do not select the default certificate when the BIG-IP system is on a chassis platform or is included in an HA pair. F5 strongly discourages the use of the default certificate in a JWK in any configuration.
- ForCertificate Key, select one.Do not use the default key when the BIG-IP system is on a chassis platform or is included in an HA pair. F5 strongly discourages the use of the default key in a JWK in any configuration.
- ForKey Passphrase, type a passphrase.
- ForCertificate Chain, select one.If this field is filled in, values for the parameters are auto-generated.
- ClickSave.The newly created JWK configuration displays in the list.
Managing storage
for opaque tokens
You create database instances to store the opaque
tokens that Access Policy Manager (APM) grants and then stores for the tokens'
lifetimes.
APM provides one default database instance,
oauthdb
. Additional instances
enable you to group tokens.- On the Main tab, click .The Database Instance screen opens.
- ClickCreate.
- In theNamefield, type a name for the object.
- In the Purge Schedule Settings area, select a frequency from theFrequencylist and specify a time in theSchedule Atfield.Schedule the database purge for a time when the BIG-IP system is least used to prevent any possible performance issues.Purging removes expired access tokens, refresh tokens, authorization codes, and associated entries from the instance. For the purpose of purging, an access token is considered expired when it passes the date when it expires; (expiry is based on theAccess Token Lifetimesetting).Expired access tokens are not removed when theReuse Access Tokensetting is enabled (in the corresponding OAuth profile) and a refresh token has been issued and the refresh token is not expired.Revoked access tokens are purged after they expire.
- To save this database instance, clickFinished.
Database instances are available for selection in
an OAuth profile.
Creating an OAuth profile
You configure an OAuth profile to
specify the client applications, resource servers, token types, and authorization server
endpoints that apply to the traffic that goes through a particular virtual
server.
- On the Main tab, click .The OAuth Profile screen opens.
- ClickCreate.
- In theNamefield, type a name for the object.
- ForClient Application, select from the available clients and move them to theSelectedlist.
- ForResource Server, select from the available servers and move them to theSelectedlist.
- ClickFinished.
You have created an OAuth profile that supports the client apps and resource servers
you selected; it supports opaque tokens and is configured to store them in the default
database instance.
You can update the types of tokens (JSON web token and opaque token) provided
through this OAuth profile and update token management settings for either type of
token.
Enabling or disabling opaque tokens and
JSON web tokens
Before you begin this task, you must
create an OAuth profile.
You configure the OAuth profile so
that the OAuth authorization server can issue opaque tokens, JSON web tokens (JWT), or
both, for the traffic that goes through a particular virtual server.
- On the Main tab, click .The OAuth Profile screen opens.
- Click the name of the OAuth profile you want to edit.
- In the Token Management Configuration area, select theCustomcheck box.Settings become available.
- To update support for opaque tokens, locate theSupport Opaque Tokencheck box; then select it to enable opaque tokens or clear it to disable them.When the check box is selected, settings for opaque tokens display, and when it is cleared the settings are hidden.
- To update support for JSON web tokens, locate theSupport JWT Tokencheck box; then select it to enable JWT tokens or clear it to disable them.When the check box is selected, settings for JWT tokens display, and when it is cleared the settings are hidden.
- ClickUpdate.
If the OAuth profile supports both opaque tokens and JWTs, for an OAuth client to
get a JWT, its request to the authorization server must include this parameter and
value:
token_content_type=jwt
.Configuring opaque token settings in an OAuth profile
Before you start, configure an OAuth profile. By default, an OAuth profile enables
opaque tokens and supplies default token management settings for them.
You might want to store opaque tokens in a
non-default database instance or change the access token lifetime.
- On the Main tab, click .The OAuth Profile screen opens.
- Click the name of the OAuth profile you want to edit.
- In the Token Management Configuration area, select theCustomcheck box.Settings become available.
- From theDatabase Instancelist, you can retain the default,oauthdb, or select another database instance.
- To update endpoints:
- In the Authorization Server Endpoints area, select theCustomcheck box.Settings become available.
- Change values in any of these fields:Authorization Endpoint,Token Issuance Endpoint,Token Revocation Endpoint, andToken Introspection Endpoint.
- ClickUpdate.
Configuring support
for JWTs in an OAuth profile
Before you start, configure an OAuth profile, configure JSON web keys (JWK), and
configure claims.
You can configure JWKs in the area of the product.
So that Access Policy Manager (APM) will generate
JSON web tokens (JWTs) for the traffic on a specific virtual server, you configure these
settings in the OAuth profile.
- On the Main tab, click .The OAuth Profile screen opens.
- Click the name of the OAuth profile you want to edit.
- In the Token Management Configuration area, select theCustomcheck box.Settings become available.
- If theSupport JWT Tokenscheck box is cleared, select it.Additional settings display.
- InIssuer, type the URL for the issuer.For example, typehttps://big-ip-server.comwherebig-ip-serveris the name of your server.
- InSubject, retain the default value,%{session.assigned.uuid}, or type a subject for the JWT.The session variablesession.assigned.uuidcontains the UUID that APM assigns to the session after the access policy completes.
- ForPrimary Key, select a JWK from the list.Key rotation is a manual process. The administrator should keep track of the certificate expiration for the primary key and assign rotation keys as needed.
- To specifyRotation Keys, select one or more JWKs and move them to theSelectedlist.
- To specify audience claims, in theAudiencefield, type a string and clickAdd. Repeat this step as needed.
- To specify claims, forClaimsmove claims to theSelectedlist.
- InJWT Refresh Token Encryption Secret, type a string.If theJWT Generate Refresh Tokensetting is enabled, after you set this secret do not change it. Changing the secret automatically invalidates all the issued refresh tokens.F5 recommends that you write the secret down and store it in a safe place in case you ever need to rebuild the OAuth profile.
- To update endpoints, in the Authorization Server Endpoints area select theCustomcheck box.Settings become available.
- To update the OpenID Connect discovery endpoint, inOpenID Connect Configuration Endpointtype the URI where clients can find the OpenID Connect provider configuration document.
- To update the JSON Web Key Set endpoint, inJWKS Endpoint, type the URI where clients can locate the public signing keys for the APM OAuth authorization server.
- ClickUpdate.
If the OAuth profile supports both opaque tokens
and JSON web tokens (JWT), for an OAuth client to get a JWT, its request to the
authorization server must include this parameter and value:
token_content_type=jwt
.About key rotation for JWTs
Access Policy Manager (APM) does not support
automatic rotation of signing keys for JSON web tokens (JWTs). To configure signing keys, an
administrator selects a primary key in the OAuth profile for authorization server
configurations, and optionally, can specify rotation keys. To determine when to update the
primary key and when to add or to update rotation keys, an administrator might consider
factors such as when the certificates in the keys expire, and how long JWTs that use a
particular key remain valid.
Creating an access profile for F5 as an
OAuth authorization server
You create an access profile to
provide the access policy configuration for a virtual server that establishes a secured
session. Configure an access profile like this for traffic to Access
Policy Manager (APM) as an OAuth authorization
server.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- ClickCreate.The New Profile screen opens.
- In theNamefield, type a name for the access profile.A access profile name must be unique among all access profile and any per-request policy names.
- From theProfile Typelist, selectAllorLTM-APM.
- Scroll down to the Configurations area.
- From theOAuth Profilelist, select the OAuth profile you configured earlier.
- In the Language Settings area, add and remove accepted languages, and set the default language.A browser uses the highest priority accepted language. If no browser language matches the accepted languages list, the browser uses the default language.If you want to translate text into other languages (as you can in Access Policy Customization), make sure to select the languages that you want to display here.
- ClickFinished.
The access profile displays in the Access Profiles
List. Default-log-setting is assigned to the access profile.
When you create a virtual server to
process traffic from OAuth version 2.0 clients and resource servers, assign this access
profile to it.
Sample policy: Logon, authenticate, and
authorize
Access policy for APM as an OAuth authorization server
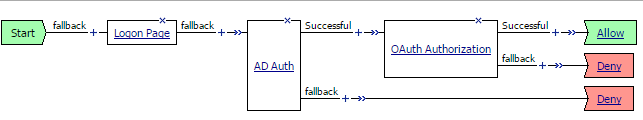
The Logon Page and OAuth Authorization agents are required in the access policy for Access Policy Manager (APM) to act as an OAuth
authorization server. An authentication agent, such as AD Auth, is optional; if included in a
policy, an authentication agent should be placed after the Logon Page and before the OAuth
Authorization agent.
About OAuth Authorization
When Access Policy Manager (APM) is configured to
act as an OAuth authorization server, an OAuth Authorization agent must be present in the access
policy.
The OAuth Authorization agent provides these elements and options.
- Prompt for Authorization
- Enabled- Displays the OAuth Authorization page. The page requests authorization for the client application to access a list of scopes and presents the options to allow or to deny access.
- Disabled- Does not display the OAuth Authorization page.
- Subject
- Type the name of a subject claim (for JSON web tokens).
- Audience
- Specifies the audiences for the claims (for JSON web tokens).
- Scope / Claim Assign
- Specifies the scopes or the claims for which authorization is requested. If no scopes or claims are specified here, the ones configured in APM for the client application are used.
- Customization
- Customize the messages that display on the OAuth authorization page whenPrompt for Authorizationis set toEnabled:
- Authorize MessageSpecifies the initial wording for the prompt.
- Scope MessageSpecifies the wording that precedes the list of scopes that are specified in the Scope / Claim Assign area of this screen.
- Allow MessageProvides the label for the button that allows access.
- Deny MessageProvides the label for the button that denies access.
Configuring an
access policy for F5 as an OAuth authorization server
You configure an access policy so that, as OAuth
authorization server, Access Policy Manager (APM) can identify and authorize client
applications to access resources.
The policy items in these steps are necessary to
process traffic sent to F5 (APM) as an authorization server. You can add these items
to a branch of an existing policy or add them to a new policy.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- On the Logon tab, selectLogon Pageand click theAdd Itembutton.The Logon Page Agent properties screen opens.
- ClickSave.The properties screen closes and the policy displays.
- On a policy branch, click the(+)icon to add an item to the policy.
- On the Authentication tab, selectOAuth Authorizationand clickAdd Item.You must include anOAuth Authorizationitem in the policy for it to work.A Properties popup screen opens.
- If you do not want to prompt for authorization, in the OAuth Authorization area, from thePrompt for Authorizationlist, selectDisabled.
- In theSubjectfield, type the subject.This is the subject of a JSON web token (JWT).
- In the Audience area, for each audience that you want to support for JWT:
- ClickAdd new entry.A numbered entry displays.
- Type an audience name in the new field.
- In the Scope / Claim Assign area, add entries to assign scopes, claims, or both:Assign these whether or not you plan to prompt for authorization.
- ClickAdd new entry.A numbered entry displays withExpressionandClaimandScopeproperties.
- To specify a prerequisite for the scopes and claims, clickchangeand configure an expression.A prerequisite is not mandatory.For example, use an expression to verify that the user has passed an LDAP query for membership in a group. Or verify that the user has passed Active Directory authentication.
- To add claims and scopes, clickAdd/Delete; (this opens a popup screen with Scope and Claim tabs); on one or both tabs, select entries and clickUpdate(this closes the popup screen).
- ClickSave.The properties screen closes and the policy displays.
- Add any additional access policy items you require to complete the access policy.On the branch of the access policy with OAuth Authorization, do not also assign connectivity resources (as you can with various resource assign access policy items). Doing so causes a validation error on the Allow ending.
- Change the ending fromDenytoAllowon any access policy branch on which you want to grant access.
- Click theApply Access Policylink to apply and activate the changes to the policy.
Creating a client
SSL profile for certificate inspection
Before you start this task, import the CA certificate for VMware View Horizon server to
the BIG-IP system certificate store.
You create a custom client SSL profile to request
an SSL certificate from the client at the start of the session. This enables a Client
Cert Inspection item in an access policy to check whether a valid certificate was
presented.
- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Server SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- From theParent Profilelist, selectclientssl.The default settings for the profile specify a 10-second SSL handshake timeout. Some users with smart cards cannot authenticate within that time. You can increase the timeout if this is the case at your site.
- From theConfigurationlist, selectAdvanced.
- If you have VMware View clients on Mac OS X, disable TLS 1.2 in the Options List area:
- In theAvailable Optionslist, selectNo TLS 1.2.
- ClickEnable.
- If you change the values for theCache Sizeor theCache Timeoutsetting, do not specify a value of zero (0) for either setting.When these values are 0, the client must supply a PIN on each browser page refresh.
- Scroll down toHandshake Timeoutand select theCustomcheck box.Additional settings become available.
- To limit the timeout to a number of seconds, selectSpecifyfrom the list, and type the required number in thesecondsfield.In the list, the valueIndefinitespecifies that the system continue trying to establish a connection for an unlimited time. If you selectIndefinite, thesecondsfield is no longer available.
- Scroll down to the Client Authentication area.
- Next to Client Authentication, select theCustomcheck box.The settings become available.
- From theClient Certificatelist, selectrequest.Do not selectrequire.
- From theTrusted Certificate AuthoritiesandAdvertised Certificate Authorities, select the certificates you imported previously.
- ClickFinished.
Creating a virtual server for OAuth authorization server traffic
You create a virtual server to
process traffic for Access Policy Manager (APM) configured as an OAuth authorization server.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theService Portfield, type443or selectHTTPSfrom the list.
- From theHTTP Profilelist, selecthttp.
- For theSSL Profile (Client)setting, move the client SSL profile you created earlier to theSelectedlist.
- Scroll down to the Access Profile area.
- From theAccess Profilelist, select the access profile you created earlier.
- ClickFinished.
The HTTPS virtual server appears in the Virtual Server List screen.





