Manual Chapter :
BIG-IP System Federation for SP-Initiated Connections
Applies To:
Show Versions
BIG-IP APM
- 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
BIG-IP System Federation for SP-Initiated Connections
Overview: Federating BIG-IP systems for SAML SSO (without an SSO portal)
In a federation of BIG-IP® systems, one BIG-IP system acts as a SAML
Identity Provider (IdP) and other BIG-IP systems act as SAML service providers (SPs).
This configuration supports:
- Only those connections that initiate at a service provider.
- Only service providers that accept assertions with similar subject type, attributes, and security settings.
About SAML IdP discovery
On a BIG-IP® system that you use as a SAML service provider (SP), you can
bind an SP service to one or more SAML Identity Provider (IdP) connectors (each of which
specifies an external IdP). When you bind an SP service to multiple IdP connectors, Access Policy Manager chooses the correct IdP connector at run time through a
filtering and matching process called IdP discovery.
Scenario
You might bind multiple IdP connectors to an SP service on the BIG-IP system when you must
provide services to different businesses and universities, each of which specifies an IdP to
identify their users. When the user's information arrives at the SP service on the BIG-IP
system, the SP service identifies the correct IdP and redirects the user to authenticate against
that IdP before the SP service provides access to the service.
The SP service performs IdP discovery for a user only when the user initiates connection
from an SP.
Session variables and the typical access policy for BIG-IP system as SP
On a BIG-IP system configured as an SP, the typical access policy presents a logon page to the
user. The Logon Page action populates session variables. You can customize the Logon Page action
and affect session variable values. A SAML Auth action follows the logon page.
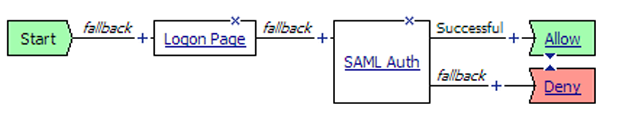
A SAML Auth action specifies an SP service. An SP service is an AAA service that requests
authentication from an external IdP (specified in an IdP connector).
Session variables and SAML IdP discovery
Among multiple IdP connectors, the BIG-IP system must discover the correct external IdP with
which to authenticate a user. For IdP discovery to work, you must specify matching criteria, a
session variable name and value, for each IdP connector.
For example, users of a service might go to a particular landing page. When you bind the IdP
connector, for the external IdP that serves those users, to the SP service, select the
%{session.server.landinguri}
session variable and supply a landing path
value, such as, /south*
. For users going to URLs such as
https://sp-service/southwest
and
https://sp-service/southeast
, the SP service selects the same IdP to
authenticate them.Logon Page action customization
These are some common customization examples for the Logon Page action.
Setting the value of session.logon.last.domain variable to the domain name only
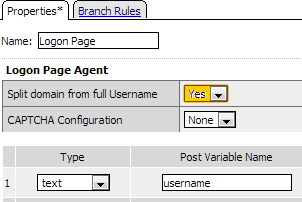
Yes
for Split domain from full
Username
. The Logon Page agent takes the user name, such as joe@office.com, that was
entered and creates the following session variables with these values.
Session Variable | Value |
|---|---|
%{session.logon.last.username} | joe |
%{session.logon.last.domain} | office.com |
%{session.logon.last.logonname} | joe@office.com |
Obtaining and email address as the username
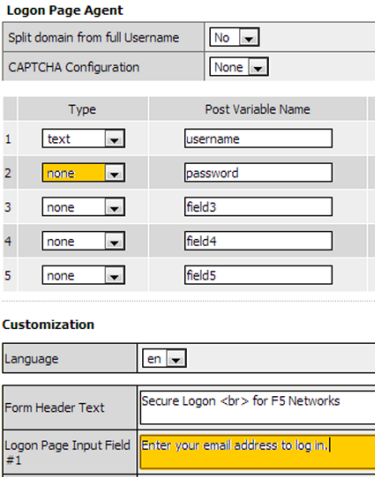
Type
, select none
from the list. About local IdP
service
A
SAML IdP service
is a type of single
sign-on (SSO) authentication service in Access Policy
Manager (APM). When you use a BIG-IP system as a SAML identity provider (IdP), a SAML IdP service
provides SSO authentication for external SAML service providers (SPs). You must bind a SAML IdP
service to SAML SP connectors, each of which specifies an external SP. APM responds to
authentication requests from the service providers and produces assertions for them.About SP connectors
A SAML service provider connector (an SP connector) specifies how a BIG-IP® system, configured as a SAML Identity Provider (IdP), connects with an external
service provider.
What are the available ways I can configure a SAML SP connector?
You can use one or more of these methods to configure SAML service provider (SP) connectors in
Access Policy Manager.
- From metadata - Obtain a metadata file from the vendor and import it into Access Policy Manager. The advantage to this method is that the vendor provides the majority of all required data, including certificates. You can complete the configuration by simply typing a unique name for the SP connector, a very few additional required fields, and browsing to and importing the file. Access Policy Manager then configures the SP connector.
- From template - Use templates that Access Policy Manager provides for some vendors; for example, Google. The advantages to this method are that:
- Most required data is included in the template
- Additional required data is minimal. You can obtain it and certificates from the vendor
- Custom - Obtain information from the vendor and type the settings into the Configuration utility. To use this method, you must also obtain certificates from the vendor and import them into the BIG-IP® system. Use this method when a metadata file or a template for an SP connector is not available.
About local SP
service
A SAML SP service is a type of AAA
service in Access Policy Manager (APM ). It requests authentication from an external SAML Identity
Provider (IdP) that is specified on APM in a SAML IdP connector. (You bind a SAML service
provider (SP) service to one or more SAML IdP connectors.) APM requests authentication from an
IdP and consumes assertions from it to allow access to resources behind APM.
About IdP
connectors
An IdP connector specifies how a BIG-IP system, configured as a SAML service provider (SP), connects with an external SAML
identity provider (IdP).
About methods for
configuring SAML IdP connectors in APM
You can use one or more of these methods to configure SAML identity
provider (IdP) connectors in Access Policy Manager
(APM).
- From metadata - Obtain a metadata file from the vendor and import it into APM. The advantage to this method is that the vendor provides all required data, including the certificate. You can complete the configuration by simply typing a unique name for the identity provider, and browsing to and importing the file. APM imports the certificate to the BIG-IP system and configures the SAML IdP connector.
- From template - Use templates that APM provides for some vendors. The advantages to this method are that:
- Most required data is included in the template. (Note that the certificate is not included.)
- Additional required data is minimal and is available from the vendor.
- Custom - Research the identity provider requirements and type all settings into the Configuration utility. Use this method when a metadata file or a template for an identity provider is not available. APM configures the SAML IdP connector. You must obtain a certificate from the vendor and import it into the BIG-IP system.
- IdP Automation - Provide files with cumulative IdP metadata on remote systems, then configure BIG-IP IdP automation to poll the files periodically and create IdP connectors and bind them to a specific service provider (SP) service.
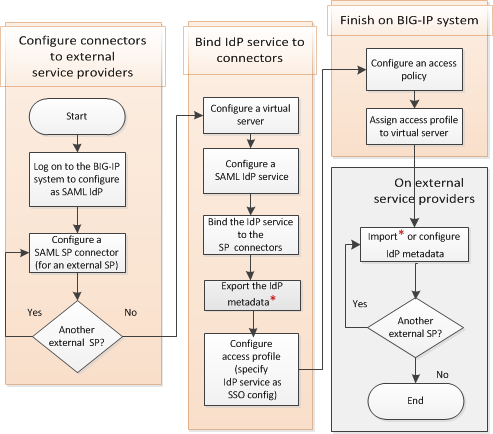
Task summary
for SAML federation without portal
Setting up SAML federation for BIG-IP® systems involves three major activities:
- First, you set up one BIG-IP system as a SAML identity provider (IdP) system
- Next, you set up one or more BIG-IP systems as a SAML service provider (SP)
- Last, you go back to the IdP system and set up connectivity to the SP systems
Flowchart: BIG-IP system federation configuration
This flowchart illustrates the process for configuring BIG-IP® systems
in federation without providing an SSO portal.
Setting up a BIG-IP system as a SAML IdP
You log in to the BIG-IP system that you have selected to act
as the SAML Identity Provider (IdP) so that you can configure elements that are required
for SAML federation.
- Log on to the BIG-IP system that you have selected to act as the SAML IdP in a SAML federation of BIG-IP systems.
Creating a virtual server for a BIG-IP (as SAML IdP) system
Before you start this task, configure a client SSL profile and a server SSL profile
if you are going to create an SSL virtual server.
Access Policy Manager supports using a non-SSL virtual server for the BIG-IP® system configured as a SAML Identity Provider (IdP).
However, we recommend using an SSL virtual server for security reasons. The
following procedures include steps that are required for configuring an SSL virtual
server, such as selecting client and server SSL profiles, and setting the service
port to HTTPS.
Specify a host virtual server to use as the SAML IdP.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- For theDestination Address/Masksetting, confirm that theHostbutton is selected, and type the IP address in CIDR format.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.The IP address you type must be available and not in the loopback network.
- In theService Portfield, type443or selectHTTPSfrom the list.
- For theHTTP Profile (Client)setting, verify that the default HTTP profile,http, is selected.
- For theSSL Profile (Client)setting, from theAvailablelist, select the name of the Client SSL profile you previously created and move the name to theSelectedlist.
- For theSSL Profile (Server)setting, from theAvailablelist, select the name of the Server SSL profile you previously created and move the name to theSelectedlist.
- ClickFinished.
The virtual server for the BIG-IP system configured as an IdP now appears on the
Virtual Server List. The virtual server destination is available for use in one or more
SAML IdP service configurations.
Configuring an
artifact resolution service
Before you configure the artifact resolution service (ARS), you need to have configured
a virtual server. That virtual server can be the same as the one used for the SAML
Identity Provider (IdP), or you can create an additional virtual server.
F5
highly recommends that the virtual server definition include a server SSL
profile.
You configure an ARS so that a BIG-IP system that
is configured as a SAML IdP can provide SAML artifacts in place of assertions. With ARS,
the BIG-IP system can receive Artifact Resolve Requests (ARRQ) from service providers,
and provide Artifact Resolve Responses (ARRP) for them.
- On the Main tab, click .
- ClickCreate.The Create New SAML Artifact Resolution Service popup screen opens, showing general settings.
- In theNamefield, type a name for the artifact resolution service.
- In theDescriptionfield, type a new description.
- ClickService Settings.
- From theVirtual Serverlist, select the virtual server that you created previously.ARS listens on the IP address and port configured on the virtual server.
- In theArtifact Validity (Seconds)field, type the number of seconds for which the artifact remains valid. The default is 60 seconds.The BIG-IP system deletes the artifact if the number of seconds exceeds the artifact validity number.
- For theSend Methodsetting, select the binding to use to send the artifact, eitherPOSTorRedirect.
- In theHostfield, type the host name defined for the virtual server, for examplears.siterequest.com.
- In thePortfield, type the port number defined in the virtual server. The default is443.
- ClickSecurity Settings.
- To require that artifact resolution messages from an SP be signed, select theSign Artifact Resolution Requestcheck box.
- To use HTTP Basic authentication for artifact resolution request messages, in theUser Namefield, type a name for the artifact resolution service request and in thePasswordfield, type a password.These credentials must be present in all Artifact Resolve Requests sent to this ARS.
- ClickOK.The popup screen closes, leaving the Artifact Resolution Services list screen open.
The Artifact Resolution Service is ready for use.
Configuring a SAML
IdP service
Configure a SAML Identity Provider (IdP) service
for the BIG-IP system, configured as a SAML IdP, to provide authentication service for
SAML service providers (SPs).
Configure this
IdP service to meet the requirements of all SAML service providers that you bind
with it.
- On the Main tab, click .The Local IdP Services screen opens.
- ClickCreate.The Create New IdP Service popup screen displays.
- In theIdP Service Namefield, type a unique name for the SAML IdP service.The maximum length of a single sign-on configuration, such as the SAML IdP service, is 225 characters, including the partition name.
- In theIdP Entity IDfield, type a unique identifier for the IdP (this BIG-IP system).Typically, the ID is a URI that points to the BIG-IP virtual server that is going to act as a SAML IdP. If the entity ID is not a valid URL, theHostfield is required.For example, typehttps://siterequest.com/idp, where the path points to the virtual server you use for BIG-IP system as a SAML IdP.
- If theIdP Entity IDfield does not contain a valid URI, you must provide one in the IdP Name Settings area:
- From theSchemelist selecthttpsorhttp.
- In theHostfield, type a host name.For example, typesiterequest.comin theHostfield.
- From theLog Settinglist, select one of the following options:
- Select an existing APM log setting.
- ClickCreateto create a new log setting.
- If you selectSAML Profileson the left pane, theWeb Browser SSOcheck box is selected by default.At least one profile must be selected.
- To specify that this IdP use an artifact resolution service, clickEndpoint Settingson the left pane and select a service from theArtifact Resolution Servicelist.
- On the left pane, selectAssertion Settingsand complete the settings that display:
- From theAssertion Subject Typelist, select the type of subject for the IdP to authenticate.
- From theAssertion Subject Valuelist, select the name of a session variable.This variable,%{session.logon.last.username}, is generally applicable. Some session variables are applicable depending on the type of authentication that you use for your site.
- In theAuthentication Context Class Referencefield, select a URI reference.The URI reference identifies an authentication context class that describes an authentication context declaration.
- In theAssertion Validity (in seconds)field, type the number of seconds for which the assertion is valid.
- To encrypt the subject, select theEnable encryption of Subjectcheck box.TheEncryption Strengthlist becomes available.
- From theEncryption Strengthlist, select a value.Supported values are AES128, AES192, and AES256.
- On the left pane, selectSAML Attributes, and for each attribute that you want to include in the attribute statement, repeat these substeps.
- ClickAdd.A Create New SAML Attribute popup screen displays.
- In theNamefield, type a unique name for the attribute.Usually, the name is a fixed string, but it can be a session variable.
- To add a value to the attribute, clickAdd, type a value in theValue(s)field, and clickUpdateto complete the addition.You can use a session variable for the value.This example shows using a fixed string for the name and a session variable for the value. Name:user_telephonenumberand value:%{session.ad.last.attr.telephoneNumber}.You can repeat this step to add multiple values for an attribute.
- To encrypt the values, select theEncryptcheck box and select a value from theTypelist.Supported values for type are AES128, AES192, and AES256.
- ClickOK.The Create New SAML Attribute popup screen closes.
- ClickSecurity Settingsfrom the left pane.
- From theSigning Keylist, select the key from the BIG-IP system store.Noneis selected by default.
- From theSigning Certificatelist, select the certificate from the BIG-IP system store.When selected, the IdP (the BIG-IP system) publishes this certificate to the service provider so the service provider can verify the assertion.Noneis selected by default.
- ClickOK.The popup screen closes. The new IdP service appears on the list.
Access Policy Manager (APM) creates a SAML IdP service. It is available to bind to SAML
SP connectors. This service works with external service providers that share the same
requirements for assertion settings and SAML attribute settings.
Exporting SAML IdP metadata from APM
You need to convey the SAML Identity Provider (IdP) metadata from Access Policy Manager (APM) to the external service
providers that use the SAML IdP service. Exporting the IdP metadata for a SAML IdP
service to a file provides you with the information that you need to do this.
- On the Main tab, click .The Local IdP Services screen opens.
- Select a SAML IdP service from the table and clickExport Metadata.A popup screen opens, withNoselected on theSign Metadatalist.
- For APM to sign the metadata, perform these steps:
- From theSign Metadatalist, selectYes.
- From theSigning Keylist, select a key.APM uses the key to sign the metadata.
- From theSignature Verification Certificatelist, select a certificate.APM exports the certificate to the metadata file. The system on which you import the metadata file can use the certificate to verify the metadata signature.
- SelectOK.APM downloads an XML file.
An XML file that contains IdP metadata is available.
Setting up a BIG-IP system as a SAML service provider system
You log in once to each BIG-IP system that you have selected
to act as a SAML service provider so that you can configure the elements on it that are
required for federation with other BIG-IP systems, one of which functions as an SAML
IdP.
- Log on to a BIG-IP system that you have selected to act as a SAML SP in a federation of BIG-IP systems.
Configuring an IdP
connector from IdP metadata
Locate the SAML IdP metadata file that you exported from the BIG-IP system (as IdP). If
the metadata file is signed, obtain the certificate also; import it into the BIG-IP
system store on this device.
Import IdP metadata to create a SAML IdP connector
on this BIG-IP system. The SAML IdP connector enables this BIG-IP system to connect and
exchange information with the external BIG-IP system that acts as the IdP in the SAML
federation.
- On the menu bar, expandSAML Service Providerand clickExternal IdP Connectors.The External IdP Connectors screen displays.
- Select .The Create New SAML IdP Connector screen opens.
- In theSelect Filefield, browse to and select the metadata file for the IdP.
- In theIdentity Provider Namefield, type a unique name for the IdP.
- If the metadata is signed, select a certificate from theSelect Signing Certificatelist.
- ClickOK.The file is uploaded, the SAML IdP connector is created, and the screen closes.
The SAML IdP connector is displayed on the SAML IdP Connectors list.
Creating a virtual server for a BIG-IP (as SAML SP) system
Before you start this task, configure a client SSL profile and a
server SSL profile.
Access Policy Manager
supports using a non-SSL virtual server for the BIG-IP system
(as SP). However, we highly recommend using an SSL virtual server for security
reasons. The following procedure includes steps that are required for configuring an
SSL virtual server. These are: selecting client and server SSL profiles and setting
the service port to HTTPS.
Specify a host virtual server to use as the SAML SP.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- For theDestination Address/Masksetting, confirm that theHostbutton is selected, and type the IP address in CIDR format.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.The IP address you type must be available and not in the loopback network.
- In theService Portfield, type443or selectHTTPSfrom the list.
- For theHTTP Profile (Client)setting, verify that the default HTTP profile,http, is selected.
- For theSSL Profile (Client)setting, from theAvailablelist, select the name of the Client SSL profile you previously created and move the name to theSelectedlist.
- For theSSL Profile (Server)setting, from theAvailablelist, select the name of the Server SSL profile you previously created and move the name to theSelectedlist.
- ClickFinished.
The virtual server for the BIG-IP system configured as an SP now appears on the
Virtual Server List. The virtual server destination is available for use in a SAML SP
service configuration.
Configuring a SAML
SP service for federation
Configure a SAML service provider (SP) service for
Access Policy Manager to provide AAA authentication, requesting authentication and
receiving assertions from a SAML IdP.
- On the Main tab, click .The Local SP Services screen displays.
- ClickCreate.The Create New SAML SP Service screen opens.
- In theNamefield, type a unique name for the SAML SP service.
- In theEntity IDfield, type a unique identifier for the service provider.Typically entity ID is a URI that points to the BIG-IP virtual server that is going to act as SAML SP. If the entity ID is not a valid URL, theHostfield is required.For example, typehttps://bigip-sp, wherehttps:/bigip-sppoints to the virtual server you use for BIG-IP system as a SAML service provider.
- If theEntity IDfield does not contain a valid URI, in the SP Name Settings area from theSchemelist, selecthttpsorhttpand in theHostfield, type a host name.For example, typesiterequest.comin theHostfield.
- In theRelay Statefield, type a scheme, host, and path.This is a path is where this BIG-IP system redirects users after they are authenticated.
- For this service provider to request an artifact instead of an assertion from the IdP, from the left pane selectEndpoint Settingsand, from theAssertion Consumer Service Bindinglist, selectArtifact.POSTis the default setting.
- From the left pane, selectSecurity Settings.The screen displays the applicable settings.
- If you want this BIG-IP system to send signed authentication requests to the SAML IdP, selectSigned Authentication Request. Then select a key and a certificate from those in the BIG-IP system store from theMessage Signing Private KeyandMessage Signing Certificatelists.
- If this BIG-IP system requires signed assertions from the SAML IdP, ensure that theWant Signed Assertioncheck box remains selected.
- If this BIG-IP system requires encrypted assertions from the SAML IdP, selectWant Encrypted Assertion. Then select a key and a certificate from those in the BIG-IP system store from theAssertion Decryption Private KeyandAssertion Decryption Certificatelists.The BIG-IP system uses the private key and certificate to decrypt the assertion.
- To configure additional service provider attributes, from the left pane clickAdvanced.The screen displays the applicable settings.
- To force users to authenticate again even when they have an SSO session at the identity provider, select theForce Authenticationcheck box.This setting is for use when the external IdP supports a force authentication flag.
- To allow the external IdP, when processing requests from this BIG-IP system as SP, to create a new identifier to represent the principal, select theAllow Name-Identifier Creationcheck box.
- To specify the type of identifier information to use, select a URI reference from theName-Identifier Policy Formatlist.For example, if a Service Provider (SP) initiates SSO by sending anAuthnRequestto the IdP with formaturn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress, then the IdP response should contain the subject identity in email format.
- To specify that the assertion subject's identifier be returned in the namespace of an SP other than the requester, or in the namespace of a SAML affiliation group of SPs, type a value in theSP Name-Identifier Qualifierfield.
- ClickOK.The screen closes.
APM creates the SAML SP service. It is available to bind to SAML IdP connectors and to
export to a metadata file.
Binding the BIG-IP system (as IdP) with the SP service on this
device
Bind the SAML SP service for this device (BIG-IP
system) to the SAML IdP connector for the external BIG-IP system that acts as the IdP,
so that this device requests authentication service from the IdP.
- On the Main tab, click .The Local SP Services screen displays.
- Select a SAML SP service from the list.
- ClickBind/Unbind IdP Connectors.A pop-up screen displays a list of any IdP connectors that are associated with this SP service.
- ClickAdd New Row.
- Select the SAML IdP connector for the BIG-IP system that acts as the IdP in the federation.Because you are binding only one IdP connector to the SP service, you do not need to fill in theMatching SourceandMatching Valuefields.
- ClickUpdate.The configuration is not saved until you clickOK.
- ClickOK.APM saves the configuration. The screen closes.
The SAML IdP connector that you selected is bound to the SAML SP service.
Exporting SAML SP metadata from APM
You need to convey the SP metadata from APM to the external SAML IdP that provides
authentication service to this SP. Exporting the SAML SP metadata to a file provides you
with the information that you need to do this.
- On the Main tab, click .The Local SP Services screen displays.
- Select an SP service from the list and clickExport Metadata.A popup window opens, displayingNoon theSign Metadatalist.
- For APM to sign the metadata, perform these steps:
- From theSign Metadatalist, selectYes.
- From theSigning Keylist, select a key.APM uses the key to sign the metadata.
- From theSignature Verification Certificatelist, select a certificate.APM exports the certificate to the metadata file. The system on which you import the metadata file can use the certificate to verify the metadata signature.
- SelectOK.APM downloads an XML file.
You must either import the XML file on the IdP system or use the information in the
XML file to configure SP metadata on the IdP system .
Configuring an
access policy to authenticate with an external SAML IdP
Before you start this task, configure
an access profile.
When you use this BIG-IP system as a
SAML service provider (SP), configure an access policy to direct users to an
external SAML Identity Provider (IdP) for authentication.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- On the Authentication tab, selectSAML Authand click theAdd Itembutton.The SAML Auth properties window opens.
- In the SAML Authentication SP area from theAAA Serverlist, select a SAML SP service and clickSave.The Access Policy window displays.
- Add any additional actions that you require to complete the policy.
- Change the Successful rule branch fromDenytoAllow, and then click theSavebutton.
- At the top of the window, click theApply Access Policylink to apply and activate your changes to this access policy.
- Click theClosebutton to close the visual policy editor.
You have an access policy that uses
SAML authentication against an external SAML IdP and further qualifies the
resources that a user can access.
Simple access policy to authenticate users
against an external SAML IdP
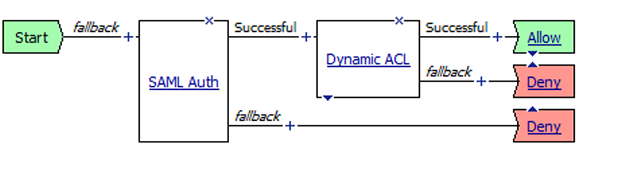
To apply this access policy to network
traffic, add the access profile to a virtual server.
To ensure that logging is configured to meet your
requirements, verify the log settings for the access profile.
Verifying log settings for the access profile
Confirm that the correct log settings are selected
for the access profile to ensure that events are logged as you intend.
Log settings
are configured in the area of the product. They enable and disable logging for access
system and URL request filtering events. Log settings also specify log publishers
that send log messages to specified destinations.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- Click the name of the access profile that you want to edit.The properties screen opens.
- On the menu bar, clickLogs.The access profile log settings display.
- Move log settings between theAvailableandSelectedlists.You can assign up to three log settings that enable access system logging to an access profile. You can assign additional log settings to an access profile provided that they enable logging for URl request logging only.Logging is disabled when theSelectedlist is empty.
- ClickUpdate.
An access profile is in effect when it is assigned to a virtual server.
Adding the access profile to the virtual server
You associate the access profile with the virtual server so that the system can apply the profile to incoming traffic.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- In the Access Policy area, from theAccess Profilelist, select the access profile that you configured earlier.
- ClickUpdateto save the changes.
Setting up connectivity from the IdP system to the SP systems
You log in to the BIG-IP system that you configured as the
SAML Identity Provider (IdP) so that you can set up connectivity to the BIG-IP systems
you configured as SAML service providers (SPs).
- Log on to the BIG-IP system that you have selected to act as the SAML IdP in a SAML federation of BIG-IP systems.
Configuring SAML SP
connectors from SAML SP metadata files
Import SP metadata into this BIG-IP system from
each BIG-IP system that is configured as an SP to create SP connectors in this system
that you can use to create a federation of BIG-IP systems.
- On the Main tab, click .A list of SAML SP connectors displays.
- SelectThe Create New SAML Service Provider window opens.
- In theSelect Filefield, browse to and select the metadata file for the service provider.
- In theService Provider Namefield, type a unique name for the service provider.
- If the metadata is signed, select the certificate from theSelect Signing Certificatelist.
- ClickOK.The file is uploaded, the SAML SP connector is created, and the window closes.
The SAML SP connector is displayed on the External SP Connectors list.
Binding IdP service and SP connectors for federation
Select a SAML Identity Provider (IdP) service and
the SAML service provider (SP) connectors that use the service so that this BIG-IP
system can provide authentication (SAML IdP service) to external SAML service providers.
- On the Main tab, click .The Local IdP Services screen opens.
- Select a SAML IdP service from the list.A SAML IdP service provides authentication service.
- ClickBind/Unbind SP Connectors.The screen displays a list of available SAML SP connectors.
- Select the SAML SP connectors for the external BIG-IP systems that are configured as SPs and that you want to use this service.
- ClickOK.The screen closes.
The SAML IdP service is bound to the external SAML service providers specified in the
SAML SP connectors.
Creating an access profile associated with the SAML IdP service
Use this procedure when this BIG-IP system, as a SAML Identity Provider (IdP),
supports service provider-initiated connections only.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- ClickCreate.The New Profile screen opens.
- In theNamefield, type a name for the access profile.A access profile name must be unique among all access profile and any per-request policy names.
- In the SSO Across Authentication Domains (Single Domain mode) area, from theSSO Configurationlist, select the name of the local SAML IdP service.
- In the Language Settings area, add and remove accepted languages, and set the default language.A browser uses the highest priority accepted language. If no browser language matches the accepted languages list, the browser uses the default language.
- ClickFinished.
The access profile displays in the Access Profiles
List. Default-log-setting is assigned to the access profile.
Verifying log settings for the access profile
Confirm that the correct log settings are selected
for the access profile to ensure that events are logged as you intend.
Log settings
are configured in the area of the product. They enable and disable logging for access
system and URL request filtering events. Log settings also specify log publishers
that send log messages to specified destinations.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- Click the name of the access profile that you want to edit.The properties screen opens.
- On the menu bar, clickLogs.The access profile log settings display.
- Move log settings between theAvailableandSelectedlists.You can assign up to three log settings that enable access system logging to an access profile. You can assign additional log settings to an access profile provided that they enable logging for URl request logging only.Logging is disabled when theSelectedlist is empty.
- ClickUpdate.
An access profile is in effect when it is assigned to a virtual server.
Configuring an
access policy to provide authentication from the local IdP
Configure an access policy so that this BIG-IP
system, as a SAML Identity Provider (IdP) can provide authentication for SAML service
providers.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- On the Logon tab, selectLogon Pageand click theAdd Itembutton.The Logon Page Agent properties screen opens.
- Make any changes that you require to the logon page properties and clickSave.The properties screen closes and the policy displays.
- Add one or more authentication checks on the fallback branch after theLogon Pageaction.Select the authentication checks that are appropriate for application access at your site.
- Add any other branches and actions that you need to complete the policy.
- Change the Successful rule branch fromDenytoAllow, and then click theSavebutton.
- Click theApply Access Policylink to apply and activate the changes to the policy.
- Click theClosebutton to close the visual policy editor.
You have an access policy that presents a logon page and authenticates the user..
Access policy
to provide authentication for SAML service providers when this BIG-IP system is the
IdP
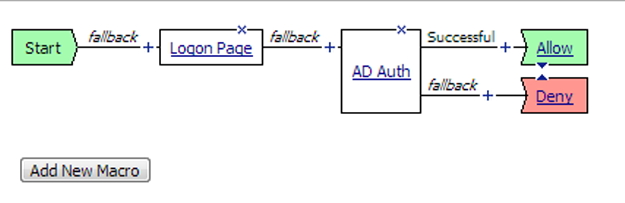
To apply this access policy to network
traffic, add the access profile to a virtual server.
To ensure that logging is configured to meet your
requirements, verify the log settings for the access profile.
Adding the access profile to the virtual server
You associate the access profile with the virtual server so that the system can apply the profile to incoming traffic.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- In the Access Policy area, from theAccess Profilelist, select the access profile that you configured earlier.
- ClickUpdateto save the changes.





