Manual Chapter :
Creating a Simple Security Policy
Applies To:
Show Versions
BIG-IP ASM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
Creating a Simple Security Policy
Types of security policies
You can create several types of security policies. It is a good idea to understand
your options before you begin.
Security policy type |
Description |
|---|---|
Automatic security policy |
Create a security policy for a web application by having the system
examine traffic and create the policy based on statistical analysis of
the traffic and the intended behavior of the application. The system
stabilizes and enforces the security policy when it processes sufficient
traffic over a period of time. You have the option of modifying the
policy manually, as well, to speed up policy creation. |
Manual security policy |
Use rapid deployment or an application-ready security policy
(pre-configured template) to develop a security policy so you can
develop a policy manually. The system creates a basic security policy
that you can review and fine-tune. When the security policy includes all
the protections that you need, and does not produce any false positives,
you can enforce the security policy. |
Security policy integrated with vulnerability assessment tool |
Create a security policy based on integrating the output from a
vulnerability assessment tool, such as WhiteHat Sentinel, IBM
AppScan, Trustwave App
Scanner (Cenzic), Qualys, Quotium
Seeker, HP WebInspect, or a generic scanner if using another
tool. Based on the results from an imported vulnerability report, Application Security Manager creates a policy that
automatically mitigates the vulnerabilities on your web site. You can
also review and fine-tune the policy. When the security policy includes
all the protections that you need and does not produce any false
positives, you can enforce the security policy. |
Parent security policy |
Create a security policy that can form the basis of other related
security policies. This is useful if you have several similar
applications for which you want to create security policies. Selected
settings in the parent policy are inherited by child policies that you
create. By adjusting the parent policy, the child policies are changed
as well. |
Child security policy |
Create a security policy that is based on a parent security policy.
When you create a child policy, the values for the settings are
inherited from the parent. You can edit some of the settings and others
can only be changed in the parent policy. |
Template security policy |
Use a template to populate the attributes of a new policy. The template is only used when creating the policy - a security policy is always created based on a user-defined or system-supplied template. Unlike parent policies, the templates do not affect the policy after it is created. If you modify a template, policies created from them in the past are not affected. |
Preparing to create a security policy
Before you create and deploy a security policy, you should have an understanding of the
application you are trying to protect and why you are trying to protect it. By defining your
security problem, you will have an easier time creating and enforcing your security policy.
Some of the questions you might consider before you start are:
- How strict a policy do you want to create? Fundamental or comprehensive?
- How many applications do you want ASM to protect? If protecting multiple applications, how similar are they?
- Do you want to develop one policy for multiple applications, or are the applications different enough that you want to create separate policies for them?
- Are there a basic set of features that you want to control from a parent policy? Multiple policies can inherit settings from a parent policy.
- How much traffic and what types of traffic do the applications handle? HTTP, HTTPS, or both?
- Do the applications have lots of parameters and URLs associated with them? Or are they simple?
A strict, application-specific security policy can potentially take more time and effort to
maintain, especially in light of application changes. A generic policy requires less maintenance,
even when applied to multiple applications. Some situations will require more extensive tuning of
the security policy while in other cases a simple policy will provide effective protection from
attacks.
Overview: Creating a simple security
policy
You can use the Application Security Manager™ (ASM) to help you build a
security policy that is tailored to your environment. ASM can build a policy
automatically, or you can do it manually. The policy building tool is called the Real Traffic Policy Builder® (referred to simply as the Policy
Builder). The Policy Builder adds suggestions for strengthening a security policy based
on settings that you configure, and the characteristics of the traffic going to and from
the web application that the system is protecting. If using automatic learning, the
system implements the learning suggestions and automatically builds the policy when
sufficient traffic and time has passed. If using manual learning, you can review the
suggestions and develop the policy adding the policy elements and features you want.
Here we take you through the steps of creating a simple security policy to introduce you
to ASM.
Task summary
Creating a simple security policy
Before you can create a security
policy, you must perform the minimal system configuration tasks required according to
the needs of your networking environment.
You can use Application Security Manager to create a robust, yet simple, security policy
that is tailored to protect your web application. This is the easiest way to create a
security policy.
- On the Main tab, click .The Policies List screen opens.
- ClickCreate New Policy.You only see this button when no policy is selected.
- In thePolicy Namefield, type a name for the policy.
- LeavePolicy Type, set toSecurity.
- ForPolicy Template, selectFundamental.
- ForVirtual Server, clickConfigure new virtual serverto specify where to direct application requests.
- ForWhat type of protocol does your application use?, selectHTTP,HTTPS, or both.
- In theVirtual Server Namefield, type a unique name.
- In theHTTP/HTTPS Virtual Server Destinationfield, type the address in IPv4 (10.0.0.1) or IPv6 (2001:ed8:77b5:2:10:10:100:42/64) format, and specify the service port.If you want multiple IP addresses to be directed here, use theNetworksetting.
- In theHTTP/HTTPS Pool Membersetting, specify the addresses of the back-end application servers.
- If you have chosen HTTPS protocol, in theSSL Profile (Client)field, select clientssl to enable theHTTP/2 Profile (Client)field.
- If you have chose HTTPS protocol, in theSSL Profile (Server)field, select serverssl to enable theHTTP/2 Profile (Server)field.
- From theLogging Profilelist, select a profile such asLog illegal requeststo determine which events are logged on the system.
- In the upper right corner, clickAdvanced.You can use default values for the Advanced settings but it's a good idea to take a look at them.
- If you selectedFundamentalorComprehensivefor thePolicy Template,Learning Modeis set toAutomaticandEnforcement Modeis set toBlocking.If you need to change these values, set application language to a value other thanAuto detect.
- If you know theApplication Language, select it or useUnicode (utf-8).
- To add specific protections (enforcing additional attack signatures) to the policy, forServer Technologies, select the technologies that apply to the back-end application servers.
- You can configure trusted IP addresses that you want the security policy to consider safe.
- ClickCreate Policyto create the security policy.
ASM creates a
security policy that immediately starts protecting your application. The enforcement
mode of the security policy is set to Blocking. Traffic that is considered to be an
attack such as traffic that is not compliant with HTTP protocol, has malformed payloads,
uses evasion techniques, performs web scraping, contains sensitive information or
illegal values is blocked. Other potential violations are reported but not
blocked.
The system examines the traffic to the web application making suggestions
for more specifically building the security policy. The Policy Builder selectively
learns new entities like file types, parameters, and cookies used in requests to the
application. When ASM processes sufficient traffic, it automatically adds the
entities to the security policy, and enforces them.
The system applies a basic
set of attack signatures to the security policy and puts them in staging (by
default, for 7 days). If you specified server technologies, additional attack
signatures are included. ASM reports common attacks discovered by comparison to the
signatures but does not block these attacks until the staging period is over and
they are enforced. That gives you a chance to be sure that these are actual attacks
and not legitimate requests.
This is a good point at
which send some traffic to test that you can access the application being protected
by the security policy and check that traffic is being processed correctly by the
BIG-IP system. Send the traffic to the virtual server
destination address.
How the security policy is built
When you create a security policy, you have a basic security policy that immediately starts
to protect your web application. The Real Traffic Policy Builder®
starts examining the application traffic, and fine-tunes the security policy using the
guidelines you configured.
The Policy Builder builds the security policy as follows:
- Adds policy elements and updates their attributes when ASM sees enough traffic from various users
- Examines application content and creates XML or JSON profiles as needed (if the policy includes JSON/XML payload detection)
- Configures attack signatures in the security policy
- Stabilizes the security policy when sufficient sessions over a period of time include the same elements
- Includes new elements if the site changes
The Policy Builder automatically discovers and populates the security policy with the policy
elements (such as file types, URLs, parameters, and cookies). On the Traffic Learning
screen, you can monitor general policy building progress, review learning suggestions
and deal with those you must handle manually, and see the number of elements that have
been included in the policy.
Automatic policy building characteristics
If you create a security policy with the Learning Mode set to Automatic, the Real Traffic Policy Builder® does automatic policy building. This
is how it works:
- The security policy starts out loose, allowing most traffic, then the Policy Builder adds policy elements based on evaluating the traffic.
- By examining the traffic, the Policy Builder makes learning suggestions that you can review on the Traffic Learning screen to see the suggested additions to the security policy. You can select and examine each suggestion if you want to learn more about it. If using automatic policy building, you can still change the policy manually, or leave it up to the system to make the changes.
- The system sets the enforcement mode of the security policy toBlocking. Traffic with obvious violations is blocked right away.
- The system holds attack signatures in staging for 7 days (by default, you can adjust the length of staging): the system checks, but does not block traffic during the staging period. If a request causes an attack signature violation, the system disables the attack signature for the particular element (parameter, JSON or XML profile, or security policy). After the staging period is over, the Policy Builder removes attack signatures from staging if enough traffic from different sessions and different IP addresses was processed. The security policy enforces the enabled signatures and blocks traffic that causes a signature violation.
- The system enforces elements in the security policy when it has processed sufficient traffic and sessions over enough time, from different IP addresses, to determine the legitimacy of the file types, URLs, parameters, cookies, methods, and so on.
- After a while, the security policy stabilizes.
- If the web site for the application changes, the Policy Builder initially loosens the security policy then adds policy elements to the security policy, updates the attributes of policy elements, puts the added elements in staging, and enforces the new elements when traffic and time thresholds are met.
This is generally how the system automatically builds security policies. You can always
control the way the security policy works by making changes manually and configuring
additional layers of security based on the unique needs of your environment. Also, you
have the option of changing the learning mode to
Manual
.Reviewing learning
suggestions
Before you can see learning suggestions on the system, it needs to have had some
traffic sent to it.
After you create a security policy and begin sending traffic to
the application, the system provides learning suggestions concerning additions to
the security policy based on the traffic it sees. For example, you can have users or
testers browse the web application. By analyzing the traffic to and from the
application, Application Security Manager generates learning suggestions or ways to
fine-tune the security policy to better suit the traffic and secure the
application.
This task is primarily for building a security policy manually. If you are using
the automatic learning mode, this task applies to resolving suggestions that require
manual intervention, or for speeding up the enforcement of policy elements.
- On the Main tab, click .The Traffic Learning screen opens, and lists suggestions based on traffic patterns and violations that the system has detected.
- Take a look at the Traffic Learning screen to get familiar with it.With no suggestions selected, the right pane displays sections that facilitate the reviewer decision-making process. These include graphical charts that summarize policy activity, a summary of top violations inReduce Potential False-positive Alerts, an enforcement readiness summary and a summary of suggestions to add new entity or delete an obsolete entity.
- To change the order in which the suggestions are listed, or refine what is included in the list, use the filters at the top of the column. Click the search icon to see basic and advanced filters.
- Review the learning suggestions as follows.
- Select a learning suggestion.Information is displayed about the action the system will take if you accept the suggestion, and what caused the suggestion.
- Select a suggestion to learn more about what caused it by looking at the action, the number of samples it is based on, the violations caused and their violation ratings, and if available, by examining samples of the requests that caused the suggestion.
- Select a request to view data about the request on the right, including any violations it generated, the contents of the request itself, and the response (if any).By examining the requests that caused a suggestion, you can determine whether it should be accepted.
- To add comments about the suggestion and the cause, click the Add Comment icon
 to the right
of the suggestion commands, and type the comments.
to the right
of the suggestion commands, and type the comments.
- Decide how to respond to the suggestion. You can start with the suggestions that have the highest learning scores, or those which you know to be valid for the application. These are the options.OptionWhat happensAccept SuggestionThe system modifies the policy by taking the suggested action, such as adding an entity that is legitimate. If the entity that triggered the suggestion can be placed in staging (file types, URLs, parameters, cookies, or redirection domains), clickingAccept Suggestiondisplays a second option,Accept suggestionand enable staging on Matched <<entity>>. Click this option to accept the suggestion and place the matched entity in staging.Delete SuggestionThe system removes the learning suggestion, but the suggestion reoccurs if new requests cause it. The learning score of the suggestion starts over from zero in that case.Ignore SuggestionThe system does not change the policy and stops showing this suggestion on the Traffic Learning screen now and in the future. You can view ignored suggestions by filtering by status ignored.If you are working in automatic learning mode, when the learning score reaches 100%, the system can accept most of the suggestions if you selected theLearning Mode Auto-apply Policy, or you can accept suggestions manually at any time. If you are using manual learning, when the learning score reaches 100% (or before that if you know the suggestions are valid), you need to accept the suggestions manually.If you know that a suggestion is valid, you can accept it at any time even before the learning score reaches 100%. The ones that reach 100% have met all the conditions so that they are probably legitimate entities.
- To put the security policy changes into effect immediately, clickApply Policy.
By default, a security policy is put into an enforcement readiness period for seven
days. During that time, you can examine learning suggestions and adjust the security
policy making sure that users can access the application. The security policy then
includes elements unique to your web application.
It is a good idea to periodically review the
learning suggestions on the Traffic Learning screen to determine whether the violations
are legitimate and caused by an attack, or if they are false positives that indicate a
need to update the security policy. Typically, a wide recurrence of violations at some
place in the policy (with a low violation rating and a high learning score) indicates
that they might be false positives, and hence the policy should be changed so that they
will not be triggered anymore. If the violations seem to indicate true attacks (for
example, they have a high violation rating), the policy should stay as is, and you can
review the violations that it triggered.
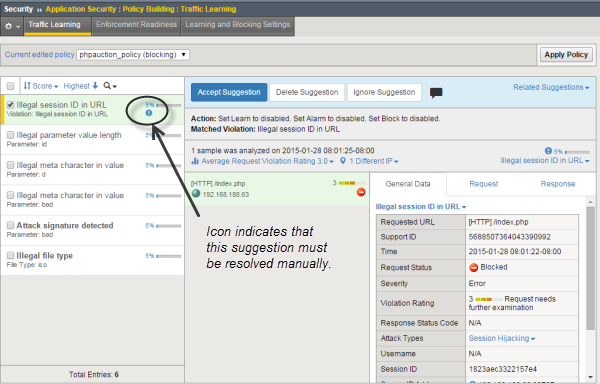
Learning suggestions you must handle manually
Some learning suggestions must be resolved manually even if you are using the Automatic Learning
Mode to create a security policy. Suggestions typically require manual intervention if they may
have a large impact on the policy or involve changing an attribute that was manually and
deliberately set in the policy, such as a disallowed geolocation or a session ID in a URL. In
these cases, the system does not change the policy unless you accept the suggestion manually.
You can easily see the suggestions that you need to resolve manually because they are marked
with an icon on the Traffic Learning screen as shown in the figure. You can also use the advanced
filter to view the suggestions the have Learning Mode set to Manual, and this would list the
suggestions you need to resolve.
Suggestions that must be resolved manually
If you are using the Manual Learning Mode, you must resolve all of the suggestions
manually.
Reviewing outstanding security policy tasks
You can display a security policy summary including a list of action items. To
simplify your work, the system reminds you of required or recommended actions, such as,
outstanding configuration and maintenance tasks, and provides links to setup and
reporting screens.
- On the Main tab, click .The Action Items screen opens.
- Examine the Action Items screen for information about recommended tasks that you need to complete.
- Review the Suggested Action Items area, which lists system tasks and security policy tasks that should be completed. For example, you can update attack signatures if new ones are available.
- Click the links to go to the screen where you can perform the recommended action items.
- Click any security policy task link to open the Summary screen, where you can view and resolve the tasks for that security policy.
- In the Quick Links area, clickPolicies Summary.The Policies Summary opens and shows a summary of all the active security policies on the system.
- In the Policy Details area, click the links to display details about a security policy.
- Click the Policy Name to view or edit policy properties.
- Click a security policy row (not on the policy name) to view Suggested Action Items, Quick Links, and how Policy Builder is operating for that security policy (whether automatically, manually, or disabled).
- Click a number in the File Types, URLs, Parameters, Cookies, or Redirection Domains column of a security policy to see details about these policy elements.
- Click the Real Traffic Policy Builder column to view the learning suggestions for the policy.
If you keep an eye on the summary screens, the system lists the tasks that you
should complete to ensure that the security policy is configured completely.
About additional
application security protections
The Application Security
Manager™ provides additional security protections for a security policy. Some of
these protections are automatically enabled depending on the type of security policy you
create.
Feature |
Description and Location |
|---|---|
DoS attack prevention |
Prevents Denial of Service (DoS) attacks based
on latency and/or transaction rates (also using behavioral analysis,
geolocation, CAPTCHA challenge, heavy URL detection, proactive web
scraping detection, and blacklisting). Click . You create a DoS profile with Application Security
enabled to configure Layer 7 DoS protection. |
Brute force prevention |
Stops attempts to break in to secured areas of
a web application by trying exhaustive, systematic, login combinations.
Click . |
IP Intelligence |
Logs and blocks attacks from IP addresses that
are in the IP Intelligence Database and are considered to have a bad
reputation. Click . |
Web scraping detection |
Mitigates web scraping (web data extraction)
on web sites by attempting to determine whether a web client source is
human. Click . |
Geolocation enforcement |
Lets you specify countries from which users
can and cannot access the web application. To set geolocation
restrictions, click . |
CSRF protection |
Prevents cross-site request forgery (CSRF)
where a user is forced to perform unwanted actions on a web application
where the user is currently authenticated. Click . |
Sensitive data masking |
Protects sensitive data in responses such as a
credit card number, U.S. Social Security number, or custom pattern.
Click . Create sensitive parameters if needed (they are also
masked); click . As an additional protection, set the Mask Credit Card Numbers in
Request Log option in the policy properties. |
Anti-virus protection |
Configures the system as an Internet Content
Adaptation Protocol (ICAP) client so that an external ICAP server can
inspect HTTP file uploads for viruses before releasing the content to
the web server. To set up the ICAP server, click . |





