Manual Chapter :
HTTP Protocol Security
Applies To:
Show Versions
BIG-IP AFM
- 21.1.0 , 17.1.3, 14.1.3, 14.1.2, 14.1.0
HTTP Protocol Security
Overview: Securing HTTP traffic
You can secure HTTP traffic by using a default configuration or by customizing the
configuration. You can adjust the following security checks in an HTTP security profile:
- HTTP protocol compliance validation
- Evasion technique detection
- Length checking to help avoid buffer overflow attacks
- HTTP method validation
- Inclusion or exclusion of certain files by type
- Mandatory header enforcement
You can also specify how you want the system to respond when it encounters a violation. If the
system detects a violation and you enabled the Block flag, instead of forwarding the request, the
system can either send a blocking response page or redirect the client to a different
location.
Creating an HTTP virtual server to use with HTTP protocol security
When you enable protocol security for an HTTP virtual server, the system scans any
incoming HTTP traffic for vulnerabilities before the traffic reaches the HTTP servers.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- For theDestination Address/Masksetting, confirm that theHostbutton is selected, and type the IP address in CIDR format.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.The IP address you type must be available and not in the loopback network.
- In theService Portfield, type80(for HTTP) or443(for HTTPS), or selectHTTPorHTTPSfrom the list.
- In the Configuration area, for theHTTP Profilesetting, select the default profile,http.
- From theSource Address Translationlist, selectAuto Map.
- For theDefault Poolsetting, either select an existing pool from the list, or click the Create (+) button and create a new pool.
- ClickFinished.
The HTTP virtual server appears in the Virtual Servers list.
Attaching an HTTP
protocol security profile to a virtual server
The easiest method for adding HTTP protocol security to your HTTP
virtual server is to use the system default profile. You do this by configuring a
virtual server with the
HTTP
profile
http
, and then associating
the default HTTP protocol security profile http_security
with the virtual
server.- On the Main tab, click .The Virtual Server List screen opens.
- In theNamecolumn, click the virtual server you previously created.The Properties screen for the virtual server opens.
- On the menu bar, from the Security menu, choose Policies.
- From theProtocol Securitylist, selectEnabled.
- From theProfilelist, selecthttp_security.This configures the virtual server with the default HTTP protocol security profile.
- ClickUpdate.
You now have a virtual server configured so that HTTP protocol checks are performed on
the traffic that the HTTP virtual server receives.
Review violation statistics for security profiles
You can view statistics and transaction information for each security profile that triggers security violations.
- On the Main tab, click and clickHTTP,DNS, orSIP.The appropriate statistics screen opens listing all violations for that protocol, with the number of occurrences.
- Type a Support ID, if you have one, to filter the violations and view one in particular.
- Click a violation's hyperlink to see details about the requests causing the violation.On the Statistics screen, in the left column, you can review information regarding the traffic volume for each security profile configured.
Overview: Creating a custom HTTP security profile
This implementation describes how to set up the BIG-IP® system to perform
security checks on your HTTP virtual server traffic customized to the needs of your environment.
Custom configuration of HTTP security and traffic management requires creating an HTTP security
profile, and fine tuning this profile so it protects HTTP traffic the way you want. Once you have
all HTTP settings specified, you create a virtual server, attach the custom HTTP security
profile, and add a default pool to handle the HTTP traffic.
Task summary
Creating a custom HTTP profile
An HTTP profile defines the way that you want the BIG-IPsystem to manage HTTP traffic.
Other HTTP profile types
(HTTP Compression and Web Acceleration) enable you to configure compression and
cache settings, as required. Use of these profile types is
optional.
- On the Main tab, click .The HTTP profile list screen opens.
- ClickCreate.The New HTTP Profile screen opens.
- In theNamefield, type a unique name for the profile.
- From theParent Profilelist, selecthttp.
- Select theCustomcheck box.
- Modify the settings, as required.
- ClickFinished.
The custom HTTP profile now appears in the HTTP profile list screen.
Creating a security profile for HTTP traffic
Before performing this procedure, verify that you have installed and provisioned BIG-IP
Advanced Firewall Manager (AFM) on the BIG-IP system.
An
HTTP security
profile
specifies security checks that apply to HTTP traffic, and that you
want the BIG-IP system to enforce. In the security profile, you can also configure
remote logging and trusted XFF headers. - On the Main tab, click .The Security Profiles: HTTP screen opens.
- Click theCreatebutton.The New HTTP Security Profile screen opens.
- In theProfile Namefield, type a unique name for the profile.
- If you want the security profile to be case-sensitive, leave theProfile is case sensitivecheck box selected. Otherwise, clear the check box.You cannot change this setting after you create the security profile.
- Modify the blocking policy settings by clickingHTTP Protocol ChecksandRequest Checks, selecting the appropriate options, and enabling theBlockorAlarmoptions as needed.If you do not enable eitherAlarmorBlockfor a protocol check, the system does not perform the corresponding security verification.
- Alarm: The system logs any requests that trigger the security profile violation.
- Block: The system blocks any requests that trigger the security profile violation.
- AlarmandBlock: The system both logs and blocks any requests that trigger the security profile violation.
- If you want to configure the blocking response page, clickBlocking Page.
- ClickCreate.The screen refreshes, and you see the new security profile in the list.
The BIG-IP system automatically
assigns this service profile to HTTP traffic that a designated virtual server
receives.
Configuring an HTTP
virtual server with an HTTP security profile
You can configure a local traffic virtual server
and a default pool for your network's HTTP servers. When the virtual server receives
HTTP traffic, an HTTP security profile can scan for security vulnerabilities, and load
balance traffic that passes the scan.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- In theDestination Address/Maskfield, type an address, as appropriate for your network.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.
- In theService Portfield, type443or selectHTTPSfrom the list.
- From theHTTP Profilelist, select thehttpprofile .
- From theSource Address Translationlist, selectAuto Map.
- In the Resources area of the screen, for theDefault Poolsetting, click theCreate (+)button.The New Pool screen opens.
- In theNamefield, type a unique name for the pool.
- In the Resources area, for theNew Memberssetting, select the type of new member you are adding, then type the information in the appropriate fields, and clickAddto add as many pool members as you need.
- ClickFinishedto create the pool.The screen refreshes, and reopens the New Virtual Server screen. The new pool name appears in theDefault Poollist.
- ClickFinishedto create the virtual server.The screen refreshes, and you see the new virtual server in the list.
- In the Name column, click the name of the relevant virtual server.This displays the properties of the virtual server.
- On the menu bar, from the Security menu, choose Policies.
- From theProtocol Securitylist, selectEnabled.
- From theProtocol Security Profilelist, select your custom HTTP security profile.
- ClickUpdateto save the changes.
Review violation statistics for security profiles
You can view statistics and transaction information for each security profile that triggers security violations.
- On the Main tab, click and clickHTTP,DNS, orSIP.The appropriate statistics screen opens listing all violations for that protocol, with the number of occurrences.
- Type a Support ID, if you have one, to filter the violations and view one in particular.
- Click a violation's hyperlink to see details about the requests causing the violation.On the Statistics screen, in the left column, you can review information regarding the traffic volume for each security profile configured.
Overview: Increasing HTTP traffic security
The HTTP security profile consists of many different security checks for the various components
of HTTP traffic. This implementation shows you how to fine-tune your HTTP security profile as
required by your environment. The custom checks are described under the assumption that you have
already created a custom HTTP security profile but have no other prerequisite or special order.
You need configure only the custom checks that you are interested in.
You can achieve a greater level of security when you configure the system to perform the following checks:
- HTTP Protocol Checks that are related to RFC compliance and actions to take resulting from a violation
- Request Checks, such as length, allowable HTTP request methods, inclusion or exclusion of file types, and custom headers that must occur in every request
- Blocking Page configuration which describes the page to display in the event of a blocked request when a violation is encountered
About RFC compliance and validation checks
When the BIG-IP® system receives an HTTP request from a client, the first
validation check that the system performs is to ensure that it is RFC protocol compliant. If the
request passes the compliance checks, the system applies the security profile to the request. So
that your system fully validates RFC compliance, keep the following HTTP Protocol Checks enabled
(they are enabled by default):
- Several Content-Length headers: This security check fails when the incoming request contains more than one content-length header.
- Null in request: This security check fails when the incoming request contains a null character.
- Unparsable request content: This security check fails when the Advanced Firewall Manager™ is unable to parse the incoming request.
Modifying HTTP protocol compliance checks
We recommend that you retain the default properties
for the HTTP protocol security checks. This task allows you to take additional
precautions such as enabling the Block flag for the HTTP Protocol Checks setting, even
if you enable only the Alarm flag for the other security checks. When you do this, the
system blocks all requests that are not compliant with HTTP protocol standards, and
performs additional security checks only on valid HTTP traffic.
- On the Main tab, click .The Security Profiles: HTTP screen opens.
- In the HTTP Security Profiles area, in the Profile Name column, click the name of the security profile that you are modifying.The HTTP Profile Properties screen opens.
- On the HTTP Protocol Checks tab, for theHTTP Protocol Checkssetting, select the check boxes for the protocol checks that you want the system to validate.
- SelectAlarmorBlockto indicate how you want the system to respond to a triggered violation.The default setting isAlarm.
- Alarm: The system logs any requests that trigger the violation.
- Block: The system blocks any requests that trigger the violation.
- AlarmandBlock: The system both logs and blocks any requests that trigger the violation.
- ClickUpdateto retain changes.
The BIG-IP system is now enabled for compliance checks on all
valid HTTP traffic.
About evasion
techniques checks
Advanced Firewall Manager can
examine HTTP requests for methods of application attack that are designed to avoid detection.
When found, these coding methods, called
evasion techniques
,
trigger the Evasion technique detected violation. By creating HTTP security profiles, you can
detect evasion techniques, such as:- Directory traversal, for example,a/b/../cturns intoa/c
- Multiple decoding passes
- Multiple backslash characters in a URI, for example,\\servername
- Bare byte decoding (higher than ASCII-127) in a URI
- Apache whitespace characters(0x09, 0x0b, or 0x0c)
- Bad unescape
By default, the system logs requests that contain evasion techniques. You
can also block requests that include evasion techniques.
Configuring HTTP
protocol evasion techniques blocking policy
You can use HTTP security profiles to detect, log,
alarm, and block evasion techniques detected in HTTP traffic.
- On the Main tab, click .The Security Profiles: HTTP screen opens.
- In the HTTP Security Profiles area, in the Profile Name column, click the name of the security profile that you are modifying.The HTTP Profile Properties screen opens.
- On the HTTP Protocol Checks tab, for theEvasion Techniques Checkssetting, select or clear theAlarmorBlockcheck boxes, as required.OptionDescriptionAlarmThe system logs any requests that trigger the violation. This is the default setting.BlockThe system blocks any requests that trigger the violation.AlarmandBlockThe system both logs and blocks any requests that trigger the violation.
- ClickUpdateto retain changes.
About the types of HTTP request checks
By creating HTTP security profiles, you can perform several types of checks on HTTP requests to
ensure that the requests are well-formed and protocol-compliant.
- Length checks
- Specify valid maximum lengths for request components to help prevent buffer overflow attacks.
- Method checks
- Specify which HTTP methods the system allows in requests.
- File type checks
- Specify which file types users can or cannot access.
- Mandatory headers
- Specify custom headers that must occur in every request.
- Null in request
- This security check fails when the incoming request contains a null character.
- Unparsable request content
- This security check fails when the system is unable to parse the incoming request.
Configuring length
checks for HTTP traffic
Before performing this procedure, verify that you have installed and provisioned BIG-IP
Advanced Firewall Manager (AFM) on the BIG-IP system.
You can specify valid maximum lengths for request
components in HTTP security profiles to prevent buffer overflow attacks. You can set
maximum lengths for URLs, query strings, POST data, and the entire request.
- On the Main tab, click .The Security Profiles: HTTP screen opens.
- In the Profile Name column, click the name of the security profile for which you want to configure length checking.The Profile Properties screen opens.
- Click the Request Checks tab.
- For each option of theLength Checkssetting, specifyAnyto allow any length or clickLengthand specify the maximum length you want to allow.
- SelectAlarmorBlock, to indicate how you want the system to respond to a triggered violation.The default setting isAlarm.
- Alarm: The system logs any requests that trigger the violation.
- Block: The system blocks any requests that trigger the violation.
- AlarmandBlock: The system both logs and blocks any requests that trigger the violation.
- For theRequest Length Exceeds Defined Buffer Sizesetting, select or clearAlarmandBlock, as needed.
- Alarm: The system logs any requests that are longer than allowed by thelong_request_buffer_sizeinternal parameter (the default is 10,000,000 bytes).
- BlockThe system blocks any requests that are longer than allowed by thelong_request_buffer_sizeinternal parameter (the default is 10,000,000 bytes).
- AlarmandBlockThe system both logs and blocks any requests that trigger the violation.
- ClickUpdateto retain changes.
Specifying which HTTP methods to allow
Before performing this procedure, verify that you have installed and provisioned BIG-IP
Advanced Firewall Manager (AFM) on the BIG-IP system.
The HTTP security profile accepts certain HTTP methods by default. The default
allowed methods are GET, HEAD, and POST. The system treats any incoming HTTP request
that includes an HTTP method other than the allowed methods as a violating request.
Later, you can decide how to handle each violation.
- On the Main tab, click .The Security Profiles: HTTP screen opens.
- In the Profile Name column, click the name of the security profile for which you want to modify allowable HTTP methods.The Profile Properties screen opens.
- Click the Request Checks tab.
- For theMethodssetting, specify which HTTP methods to allow:The default allowed methods are GET, HEAD, and POST.
- From theAvailablelist, select the methods you want to allow in a request and move them to theAllowedlist.
- To add a new method to theAvailablelist: type the name in theMethodfield, clickAddto add it to the list, and move it to theAllowedlist.
- SelectAlarmorBlock, to indicate how you want the system to respond to a triggered violation.The default setting isAlarm.
- Alarm: The system logs any requests that trigger the violation.
- Block: The system blocks any requests that trigger the violation.
- AlarmandBlock: The system both logs and blocks any requests that trigger the violation.
- ClickUpdateto retain changes.
Including or excluding files by type in HTTP security profiles
Before performing this procedure, verify that you have installed and provisioned BIG-IP
Advanced Firewall Manager (AFM) on the BIG-IP system.
By default, an HTTP security profile permits all file types in a request. For
tighter security, you can create a list that specifies either all file types you want to
allow, or a list specifying all the file types you do not want allowed.
- On the Main tab, click .The Security Profiles: HTTP screen opens.
- In the Profile Name column, click the name of the security profile you want to update.The Profile Properties screen opens.
- Click the Request Checks tab.
- For theFile Typessetting, specify whether you want to create a list of allowed or disallowed file types, and which files you want in the list.
- To create a list of file types that are permitted in requests, selectDefine Allowed.
- To create a list of file types not permitted, selectDefine Disallowed.
- Select file types from theAvailablelist, and move them to theAllowedorDisallowedlist.
- To add a new file type, type the name in theFile Typefield, clickAddto add it to theAvailablelist, and then move it to theAllowedorDisallowedlist.
If the profile is case-sensitive, the file types are case-sensitive. For example,jspandJSPwill be treated as separate file types. - SelectAlarmorBlock, to indicate how you want the system to respond to a triggered violation.The default setting isAlarm.
- Alarm: The system logs any requests that trigger the violation.
- Block: The system blocks any requests that trigger the violation.
- AlarmandBlock: The system both logs and blocks any requests that trigger the violation.
The page you configure is displayed every time one of the security checks set to
Block
is violated.Configuring a
mandatory header for an HTTP security profile
Before performing this procedure, verify that you have installed and provisioned BIG-IP
Advanced Firewall Manager (AFM) on the BIG-IP system.
When the BIG-IP system is managing an application
that uses custom headers that must occur in every request, you can specify mandatory
HTTP headers in the security profile. The system verifies that all requests contain
those headers. If a request does not contain the mandatory header, the system issues the
Mandatory HTTP header is missing violation, and takes the action that you configure:
Alarm, Block, or both.
- On the Main tab, click .The Security Profiles: HTTP screen opens.
- In the Profile Name column, click the name of the security profile for which you want to configure a Mandatory Header alarm.The Profile Properties screen opens.
- Click the Request Checks tab.
- For theMandatory Headerssetting, specify the header that must be in the request:
- In theHeaderfield, type the name of the mandatory header, and click theAddbutton to add it to theAvailablelist.
- Move the new mandatory header from theAvailablelist to theMandatorylist.
- Select or clear theAlarmorBlockcheck boxes as required.
OptionDescriptionAlarmThe system logs any responses that trigger theMandatory HTTP header is missingviolation. This is the default setting.BlockThe system blocks any requests that trigger theMandatory HTTP header is missingviolation.AlarmandBlockThe system both logs and blocks any requests that trigger theMandatory HTTP header is missingviolation. - ClickUpdateto retain changes.
All HTTP requests are checked for the mandatory headers you have selected.
Configuring the
blocking response page for HTTP security profiles
If your HTTP security profile is set up to block
requests that violate one or more of the security checks, the system displays a page,
called the blocking response page, on the client's screen. The default blocking response
page states that the request was rejected, and provides a support ID. You can also
configure the system to redirect the client to a specific web site instead of displaying
the blocking response page.
- On the Main tab, click .The Security Profiles: HTTP screen opens.
- In the Profile Name column, click the name of the security profile for which you want to configure a blocking page.The Profile Properties screen opens.
- Click the Blocking Page tab.
- For theResponse Typesetting, select one of the options:
- Default Response: Specifies that the system returns the system-supplied blocking response page. Though you cannot edit the HTML code on the default blocking page, you can copy it into a custom response and edit it.
- Custom Response: Specifies that the system returns a response page that you design or upload.
- Redirect URL: Specifies that the system redirects the client to the specified URL.
- SOAP Fault: Specifies that the system displays a blocking page in standard SOAP fault message format. Though you cannot edit the SOAP fault code, you can copy it into a custom response and edit it.
The settings on the screen change depending on the selection that you make for the Response Type setting. - If you selected theCustom Responseoption, you can either create a new response or upload an HTML file.
- To create a custom response, make the changes you want to the default responses for theResponse HeaderandResponse Bodysettings using HTTP syntax for the content, and clickUpload.
- To upload an HTML file for the response body, navigate to an existing HTML response page, and clickUpload.
- If you selectedRedirect URL, type the full path of the web page to which the system should redirect the client in theRedirect URLfield.
- ClickUpdateto retain changes.
The system displays the response page when a violation occurs on any of the security
checks set to
Block
.Overview: Configuring Local Protocol Security Event Logging
You can configure the BIG-IP® system to log detailed information about
protocol security events and store those logs locally.
The BIG-IP Advanced Firewall Manager™ (AFM) must be
licensed and provisioned and DNS Services must be licensed before you can configure Protocol
Security event logging.
Creating a local Protocol Security Logging profile
Create a custom Logging profile to log BIG-IP system network firewall events
locally on the BIG-IP system.
- On the Main tab, click .The Logging Profiles list screen opens.
- ClickCreate.The Create New Logging Profile screen opens.
- In theProfile Namefield, type a unique name for the profile.
- Select theProtocol Securitycheck box.
- In the HTTP, FTP, and SMTP Security area, from thePublisherlist, selectlocal-db-publisher.
- In the DNS Security area, from thePublisherlist, selectlocal-db-publisher.
- Select theLog Dropped Requestscheck box, to enable the BIG-IP system to log dropped DNS requests.
- Select theLog Filtered Dropped Requestscheck box, to enable the BIG-IP system to log DNS requests dropped due to DNS query/header-opcode filtering.The system does not log DNS requests that are dropped due to errors in the way the system processes DNS packets.
- Select theLog Malformed Requestscheck box to enable the BIG-IP system to log malformed DNS requests.
- Select theLog Rejected Requestscheck box to enable the BIG-IP system to log rejected DNS requests.
- Select theLog Malicious Requestscheck box to enable the BIG-IP system to log malicious DNS requests.
- ClickFinished.
Assign this custom protocol security Logging profile to a virtual server.
Configuring a virtual server for Protocol Security event
logging
Ensure that at least one Log Publisher exists on the BIG-IP system.
Assign a custom Protocol Security Logging profile
to a virtual server when you want the BIG-IP system to log Protocol Security events on
the traffic the virtual server processes.
This task
applies only to systems provisioned at a minimum level (or higher) for
Local Traffic (LTM)
. You can
check the provisioning level on the screen. - On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- On the menu bar, click .The screen displays policy settings for the virtual server.
- In theLog Profilesetting, selectEnabled. Then, select one or more profiles, and move them from theAvailablelist to theSelectedlist.
- ClickUpdateto save the changes.
Viewing Protocol Security event logs locally on the BIG-IP system
Ensure that the BIG-IP system is configured to log the types
of events you want to view, and to store the log messages locally on the BIG-IP
system.
When the BIG-IP system is configured to log events locally, you can view those
events using the Configuration utility.
- On the Main tab, click .The Protocol Security event log displays.
- To search for specific events, clickCustom Search. Drag the event data that you want to search for from the Event Log table into the Custom Search table, and then clickSearch.
Disabling logging
Disable event logging when you need to suspend logging for a period of time or you
no longer want the BIG-IP system to log specific events.
Logging is enabled by adding log settings to the access profile.
- To clear log settings from access profiles, on the Main tab, click .
- Click the name of the access profile.Access profile properties display.
- On the menu bar, clickLogs.
- Move log settings from theSelectedlist to theAvailablelist.
- ClickUpdate.
Logging is disabled for the access profile.
Implementation result
You now have an implementation in which the BIG-IP® system logs
specific Protocol Security events locally.
Overview: Logging
remote protocol security events
You can configure the BIG-IP® system
to log information about Protocol Security events and send the log messages to remote
high-speed log servers.
The Advanced Firewall Manager™ (AFM™) must be
licensed and provisioned before you can configure Protocol Security event logging.
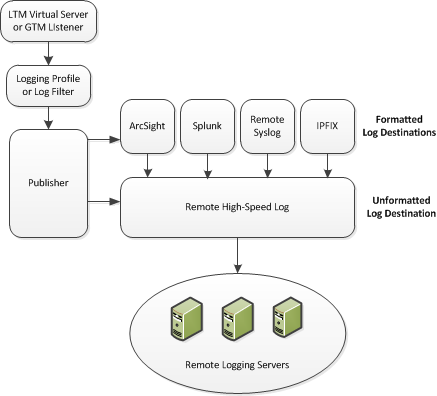
This illustration shows the association of the configuration objects for remote high-speed logging.
Association of remote high-speed logging configuration objects
Task summary
Perform these tasks to configure Protocol Security event logging on the
BIG-IP® system. Enabling remote high-speed logging impacts BIG-IP
system performance.
About the configuration objects of remote protocol security event logging
When configuring remote high-speed logging of Protocol Security events, it is helpful to understand the
objects you need to create and why, as described here:
Object | Reason | Applies to |
|---|---|---|
Pool of remote log servers | Create a pool of remote log servers to which the BIG-IP system
can send log messages. | Creating a pool of remote logging servers. |
Destination (unformatted) | Create a log destination of Remote High-Speed Log type that specifies a pool of remote log servers. | Creating a remote high-speed log destination. |
Destination (formatted) | If your remote log servers are the ArcSight, Splunk, IPFIX, or Remote Syslog type, create an additional log destination to format the logs in the required format and forward the logs to a remote high-speed log destination. | Creating a formatted remote high-speed log destination. |
Publisher | Create a log publisher to send logs to a set of specified log destinations. | Creating a publisher. |
DNS Logging profile | Create a custom DNS Logging profile to define the data you want the BIG-IP system to include in the DNS logs and associate a log publisher with the profile. | Creating a custom Protocol Security logging profile. |
Protected object (virtual server) | Associate a custom DNS profile with a protected object to define
how the BIG-IP system logs the DNS traffic that the protected object processes. | Configuring a protected object for Protocol Security event
logging. |
Creating a pool of remote logging servers
Before creating a pool of log servers, gather the IP addresses of the servers that
you want to include in the pool. Ensure that the remote log servers are configured to
listen to and receive log messages from the BIG-IP
system.
Create a pool of remote log servers to which the BIG-IP system can send log
messages.
- On the Main tab, click .The Pool List screen opens.
- ClickCreate.The New Pool screen opens.
- In theNamefield, type a unique name for the pool.
- Using theNew Memberssetting, add the IP address for each remote logging server that you want to include in the pool:
- Type an IP address in theAddressfield, or select a node address from theNode List.
- Type a service number in theService Portfield, or select a service name from the list.Typical remote logging servers require port514.
- ClickAdd.
- ClickFinished.
Creating a remote high-speed log destination
Before creating a remote high-speed log destination, ensure that at least one pool
of remote log servers exists on the BIG-IP system.
Create a log destination of the
Remote High-Speed Log
type to
specify that log messages are sent to a pool of remote log servers.- On the Main tab, click .The Log Destinations screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this destination.
- From theTypelist, selectRemote High-Speed Log.If you use log servers such as Remote Syslog, Splunk, or ArcSight, which require data be sent to the servers in a specific format, you must create an additional log destination of the required type, and associate it with a log destination of theRemote High-Speed Logtype. With this configuration, the BIG-IP system can send data to the servers in the required format.The BIG-IP system is configured to send an unformatted string of text to the log servers.
- From thePool Namelist, select the pool of remote log servers to which you want the BIG-IP system to send log messages.
- From theProtocollist, select the protocol used by the high-speed logging pool members.
- ClickFinished.
Creating a formatted remote high-speed log destination
Ensure that at least one remote high-speed log destination exists on the BIG-IP system.
Create a formatted logging destination to specify that log messages are sent to a
pool of remote log servers, such as Remote Syslog, Splunk, or IPFIX servers.
- On the Main tab, click .The Log Destinations screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this destination.
- From theTypelist, select a formatted logging destination, such asRemote Syslog,Splunk, orIPFIX.The Splunk format is a predefined format of key value pairs.The BIG-IP system is configured to send a formatted string of text to the log servers.
- If you selectedRemote Syslog, then from theSyslog Formatlist select a format for the logs, and then from theHigh-Speed Log Destinationlist, select the destination that points to a pool of remote Syslog servers to which you want the BIG-IP system to send log messages.For logs coming from Access Policy Manager (APM), only the BSD Syslog format is supported.
- If you selectedSplunkorIPFIX, then from theForward Tolist, select the destination that points to a pool of high-speed log servers to which you want the BIG-IP system to send log messages.
- ClickFinished.
Creating a publisher
Ensure that at least one destination associated with a pool of remote log servers
exists on the BIG-IP system.
Create a publisher to specify where the BIG-IP system sends log messages for
specific resources.
- On the Main tab, click .The Log Publishers screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this publisher.
- For theDestinationssetting, select a destination from theAvailablelist, and click<<to move the destination to theSelectedlist.If you are using a formatted destination, select the destination that matches your log servers, such as Remote Syslog, Splunk, or ArcSight.
- ClickFinished.
Creating a custom
Protocol Security logging profile
Create a logging profile to log Protocol Security events for the traffic handled by
the protected object to which the profile is assigned.
You can configure
logging profiles for HTTP and DNS security events on Advanced
Firewall Manager, and FTP and SMTP security events on Application Security Manager.
- On the Main tab, click .The Logging Profiles list screen opens.
- ClickCreate.The Create New Logging Profile screen opens.
- Select theProtocol Securitycheck box.
- In the HTTP, FTP, and SMTP Security area, from thePublisherlist, select the publisher that the BIG-IP system uses to log HTTP, FTP, and SMTP Security events.
- In the DNS Security area, from thePublisherlist, select the publisher that the BIG-IP system uses to log DNS Security events.
- Select theLog Dropped Requestscheck box, to enable the BIG-IP system to log dropped DNS requests.
- Select theLog Filtered Dropped Requestscheck box, to enable the BIG-IP system to log DNS requests dropped due to DNS query/header-opcode filtering.The system does not log DNS requests that are dropped due to errors in the way the system processes DNS packets.
- Select theLog Malformed Requestscheck box to enable the BIG-IP system to log malformed DNS requests.
- Select theLog Rejected Requestscheck box to enable the BIG-IP system to log rejected DNS requests.
- Select theLog Malicious Requestscheck box to enable the BIG-IP system to log malicious DNS requests.
- From theStorage Formatlist, select how the BIG-IP system formats the log.OptionDescriptionNoneSpecifies the default format type in which the BIG-IP system logs messages to a remote Syslog server, for example:"management_ip_address","bigip_hostname","context_type","context_name","src_ip","dest_ip","src_port","dest_port","vlan","protocol","route_domain","acl_rule_name","action","drop_reasonField-ListAllows you to:
- Select, from a list, the fields to be included in the log.
- Specify the order the fields display in the log.
- Specify the delimiter that separates the content in the log. The default delimiter is the comma character.
User-DefinedAllows you to:- Select, from a list, the fields to be included in the log.
- Cut and paste, in a string of text, the order the fields display in the log.
- ClickFinished.
Assign this custom Protocol Security Logging profile to a protected object.
Logging DoS events for a protected object
Ensure that at least one log publisher exists on the BIG-IP system.
Assign a custom logging profile to a
protected object when you want the system to log DoS events for the traffic the
protected object processes.
- On the Main tab, click .
- Click the name of the protected object for which you want to log DoS events.The Properties pane opens on the right.
- In the Network & General area, forLogging Profiles, move the logging profile to assign from the Available list into the Selected list.This assigns the logging profile to the protected object.
- ClickSave.
The system logs DoS
events for the protected object.
You can review DoS
event logs at and select the type of DoS event log to view.





