Manual Chapter :
Sample Service Function Chaining Network Topologies
Applies To:
Show Versions
BIG-IP LTM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
BIG-IP PEM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
Sample Service Function Chaining Network Topologies
Sample Service Function Chaining Network Topologies
In a general service function chaining (SFC) topology, two
service functions (SFs) of different types are attached to a service function forwarder
(SFF).
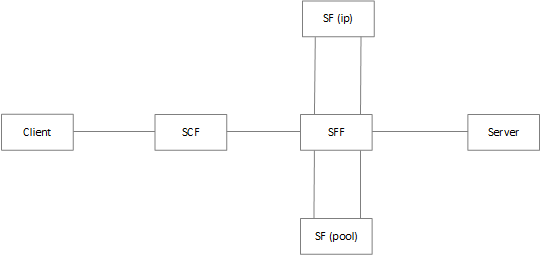
There are two types of topologies for
these types of SFs:
- Network service header (NSH)-unaware SFs of typeIPandPoolon an external network.
- NSH-aware SFs of typeIPandPoolon an external network, and an NSH-aware SF of typeVirtualon an internal network.
Network service header-unaware service functions
With network service header (NSH)-unaware service functions
(SFs), data forwarded to the SF does not contain NSH encapsulation.
Before configuring NSH-unaware SFs, you must create an ingress and an
egress VLAN.
NSH-unaware service function of type IP
One type of network service header (NSH)-unaware service
function (SF) that you can configure is an SF of type
IP
.In this topology, the SF is on the
external network.
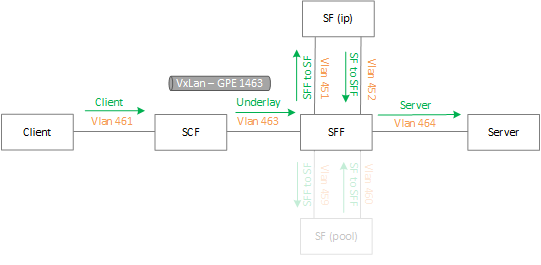
Use this sytax to create this
topology:
tmsh create net sfc sf <SF NAME> {nsh-aware disabled ip-address <IP ADDRESS> ingress-interface <INGRESS VLAN> egress-interface <EGRESS VLAN>}
For example:
tmsh create net sfc sf sf1_non_nsh_ip {nsh-aware disabled ip-address <ip1> ingress- interface <VLAN 452> egress-interface <VLAN 451>}
NSH-unaware service function of type Pool
One type of network service header (NSH)-unaware service
function (SF) that you can configure is an SF of type
Pool
.In this topology, the SF is on the external network.
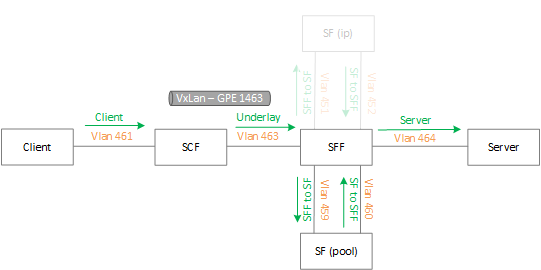
Use this sytax to create this
topology:
tmsh create net sfc sf <SF NAME>_non_nsh_pool {nsh-aware disabled pool-name <POOL NAME> ingress-interface <INGRESS VLAN> egress-interface <EGRESS VLAN>}
For
example:
tmsh create net sfc sf sf1_non_nsh_pool {nsh-aware disabled pool-name <pool1> ingress-interface <vlan 460> egress-interface <vlan 459>}
NSH-aware service functions
With network service header (NSH)-aware service functions
(SFs), the SF receives and acts on data in the NSH encapsulation.
Before configuring NSH-aware SFs, you must create VXLAN-GPE tunnels.
NSH-aware service function of type IP
One type of network service header (NSH)-aware service
function (SF) that you can configure is an SF of type
IP
.In this topology, the SF is on the
external network.
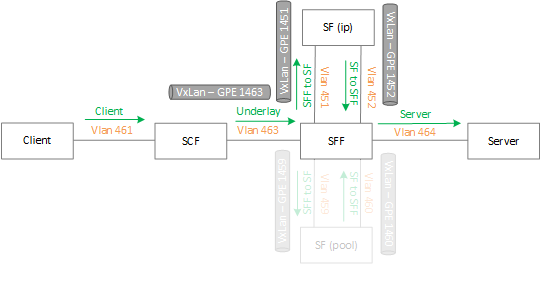
Use this sytax to create this
topology:
tmsh create net sfc sf <SF NAME> {nsh-aware enabled ip-address <IP ADDRESS > ingress-interface <INGRESS TUNNEL > egress-interface <EGRESS TUNNEL>}
For
example:
tmsh create net sfc sf sf1_nsh_ip {nsh-aware enabled ip-address <ip1> ingress-interface <VXLAN GPE TUNNEL 1452> egress-interface <VXLAN GPE TUNNEL 1451>}
NSH-aware service function of type Pool
One type of network service header (NSH)-aware service
function (SF) that you can configure is an SF of type
Pool
.In this topology, the SF is on the external network.
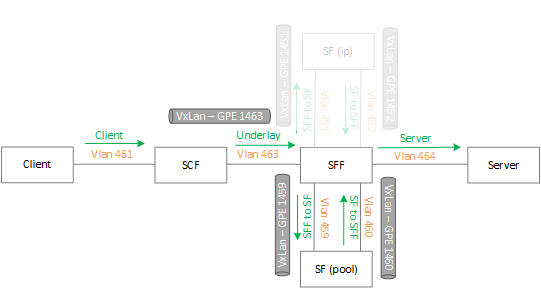
Use this sytax to create
this
topology:
tmsh create net sfc sf <SF NAME> {nsh-aware enabled pool-name <POOL NAME> ingress- interface <INGRESS TUNNEL> egress-interface <EGRESS TUNNEL>}
For
example:
tmsh create net sfc sf sf1_nsh_pool {nsh-aware enabled pool-name <pool1 > ingress- interface <vxlan gpe tunnel 1460> egress-interface <vxlan gpe tunnel 1459>}
NSH-aware service function of type Virtual
One type of network service header (NSH)-aware service
function (SF) that you can configure is an SF of type
Virtual
.Before configuring NSH-aware SFs, you must create a separate virtual server
to use as the SF. F5 recommends that you create dedicated/dummy VLANs for this
virtual server that are separate from the other VLANs. Because this SF resides
inside the service function forwarder (SFF), the SF is
encapsulation-aware.
In this topology, the SF is a virtual server on the
internal network.
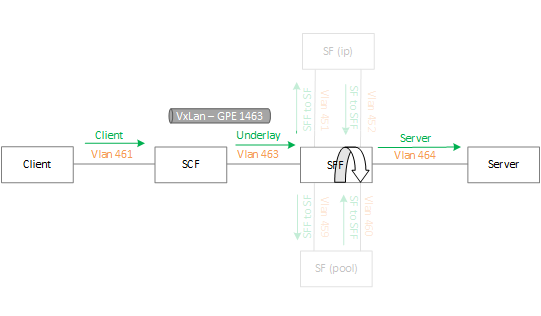
Use this sytax to create this
topology:
tmsh create ltm virtual <VS NAME > destination any:any ip-forward vlans-enabled vlans add { VLAN NAME }
tmsh create net sfc sf <SF NAME > virtual-name <VS NAME>
For
example:
tmsh create ltm virtual virtual1_v4 destination any:any ip-forward vlans-enabled vlans add { virtual1 }
tmsh create net sfc sf sf_nsh_virtual virtual-name virtual1_v4





