Manual Chapter :
Policies for APM as a Secure Web
Gateway
Applies To:
Show Versions
BIG-IP APM
- 15.0.1, 15.0.0
Policies for APM as a Secure Web
Gateway
Overview: Controlling forward proxy traffic
with APM
On a BIG-IP system with Access Policy Manager (APM®), you can configure per-request policies to control forward proxy access
with user-defined URL categories and filters that you have configured.
Task summary
You must have created an explicit or a transparent forward proxy configuration.
Task list
Configuring an
access policy for forward proxy with SWG
You configure an access policy to support explicit
forward proxy or transparent forward proxy. If you plan to use branching by group or
class attribute in your per-request policy, you add items to the access policy to
populate that information. You can also add access policy items to collect credentials
and to authenticate a user or add access policy items to identify the user
transparently.
If you include authentication in your access policy and the
first site that a user accesses uses HTTP instead of secure HTTP, passwords are
passed as clear text. To prevent this from happening, F5 recommends using Kerberos
or NTLM authentication.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- If you specified an NTLM Auth configuration in the access profile, verify that authentication succeeded.
- On the Authentication tab, selectNTLM Auth Result.
- ClickAdd Item.A properties popup screen opens.
- ClickSave.The properties screen closes. The policy displays.
- To add Kerberos authentication to an access policy for forward proxy, addHTTP 407 Response(for explicit forward proxy) orHTTP 401 Response(for transparent forward proxy); then follow it with these actions in order:Variable Assign, andKerberos Auth.This example usesHTTP 407 Response. You can replace it withHTTP 401 Response.In a transparent forward proxy configuration, APM does not support Kerberos request-based authentication
- On a policy branch, click the plus symbol(+)to add an item to the policy.
- On the Logon tab, selectHTTP 407 Responseand clickAdd Item.A properties screen opens.
- From theHTTP Auth Levellist, selectnegotiateand clickSave.The properties screen closes.
- Click the(+)icon on thenegotiatebranch.A popup screen opens.
- On the Assignment tab, selectVariable Assignand clickAdd Item.For Kerberos authentication to work correctly with forward proxy, you must assign the domain name for the proxy virtual server to a session variable.
- ClickAdd new entry.Anemptyentry appears in the Assignment table.
- Click thechangelink in the new entry.A popup screen opens.
- In the left pane, retain the selection ofCustom Variableand type this variable name:session.server.network.name.
- In the right pane, in place ofCustom Variable, selectTextand type the domain name for the proxy virtual server.
- ClickFinished.The popup screen closes.
- ClickSave.The properties screen closes. The policy displays.
- On a policy branch, click the plus symbol(+)to add an item to the policy.
- On the Authentication tab, selectKerberos Authand clickAdd Item.A properties screen opens.
- From theAAA Serverlist, select an existing server.
- From theRequest Based Authlist, selectDisabled.
- ClickSave.The properties screen closes and the policy displays.
TheMax Logon Attempts Allowedsetting specifies attempts by an external client without a Kerberos ticket to authenticate on forward proxy. - To identify a user transparently using information provided by a Secure Web Gateway (SWG) user identification agent, perform these steps:For this step of the access policy to succeed, you must have installed and configured either the F5 DC Agent or the F5 Logon Agent. Either agent is supported on a BIG-IP system with an SWG subscription only.
- On a policy branch, click the plus symbol(+)to add an item to the policy.
- From the Authentication tab, selectTransparent Identity Importand clickAdd Item.The transparent identity import access policy item searches the database in the IF-MAP server for the client source IP address. By default, this access policy item has two branches: associated and fallback.A properties screen opens.
- ClickSave.The visual policy editor opens.
- Add any additional access policy items to the fallback or associated branches.For example, you might add Kerberos authentication on the fallback branch.
- To supply LDAP group information for use in the per-request policy, add an LDAP Query item anywhere in the policy and configure its properties:
- From theServerlist, select an AAA LDAP server.An LDAP Query uses SSL connections when you select an LDAP AAA server that is configured for LDAPS.
- Specify theSearchDN, andSearchFiltersettings.SearchDN is the base DN from which the search is done.
- ClickSave.
This item populates thesession.ldap.last.attr.memberOfsession variable. - To supply Active Directory groups for use in the per-request policy, add an AD Query item anywhere in the policy and configure its properties:
- From theServerlist, select an AAA AD server.
- Select theFetch Primary Groupcheck box.The value of the primary user group populates thesession.ad.last.attr.primaryGroupIDsession variable.
- ClickSave.
- To supply RADIUS class attributes for use in the per-request policy, add a RADIUS Auth item anywhere in the policy and configure its properties:
- From theServerlist, select an AAA RADIUS server.
- ClickSave.
This item populates thesession.radius.last.attr.classsession variable. - Click theApply Access Policylink to apply and activate the changes to the policy.
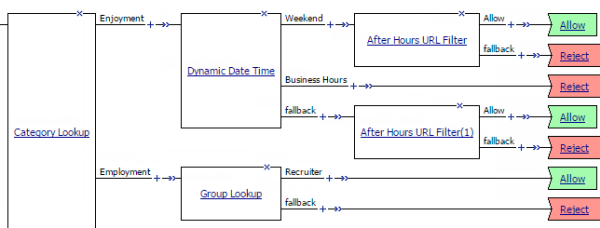
Example policy: User-defined
category-specific access control
In this example per-request policy, only recruiters can access URLs in the
user-defined category Employment. The policy also restricts access to entertaining videos
during business hours.
Category-specific access restrictions
(using user-defined categories)
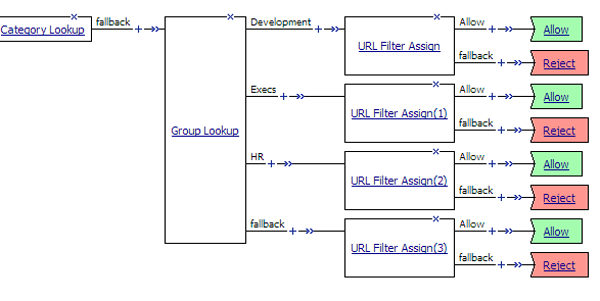
Example policy: URL filter per user
group
Each URL Filter Assign item in this per-request policy example needs to
specify a filter that applies to the user group.
URL filter based on group membership
Creating a per-request policy
You can create a per-request policy to ensure
greater security on your system.
- On the Main tab, click .The Per-Request Policies screen opens.
- ClickCreate.The General Properties screen opens.
- In theNamefield, type a name for the policy.A per-request policy name must be unique among all per-request policy and access profile names.
- LeavePolicy Typeset toAll.
- For most cases, leaveIncomplete Actionset toDeny.
- In theLanguagessetting, select the accepted languages.
- ClickFinished.The policy name appears on the Per-Request Policies screen.
Applying user-defined URL categories and
filters in a per-request policy
This task is for
use on a BIG-IP system without an SWG subscription.
Look up the category for a URL
request and assign a URL filter that blocks or allows access to control access to the
web, based on the category of the URL request.
This task provides the
steps for adding items to control web traffic based on the URL category. It does not
specify a complete per-request policy.
- On the Main tab, click .The Per-Request Policies screen opens.
- In theNamefield, locate the policy that you want to update, then in thePer-Request Policyfield, click theEditlink.The visual policy editor opens in another tab.
- On the General Purpose tab, selectCategory Lookupitem and clickAdd Item.A popup Properties screen opens.
- ForCategorization Input, select an option based on the type of traffic to process:
- For HTTP traffic, selectUse HTTP URI (cannot be used for SSL Bypass decisions). If selected, theSafeSearch Modefield displays set toEnabled.
- For SSL-encrypted traffic, selectUse SNI in Client Hello (if SNI is not available, use Subject.CN)orUse Subject.CN in Server Cert.
- For connections that are passing through an upstream proxy, selectUse HTTP Connect Hostname. It uses information from the HTTP Connect header and matches only the hostname. The Category Lookup agent functions only on the transparent HTTP virtual servers and fails if the policy is attached to explicit HTTP virtual servers.
Early in the per-request policy, you can insert a Protocol Lookup agent to provide separate branches for HTTPS and HTTP traffic. - ForCategory Lookup Type, you can only retain the default valueProcess custom categories only.Category Lookup looks through the user-defined categories to compile a list of categories for the URL.
- ClickSave.The properties screen closes. The visual policy editor displays.
- On a branch after a Category Lookup item, add aURL Filter Assignagent and, in its properties, select a URL filter.
A per-request policy goes into
effect when you add it to a virtual server. Depending on the forward proxy
configuration, you might need to add the per-request policy to more than one virtual
server.
Adding a
per-request policy to the virtual server
To add per-request processing to a configuration, associate the
per-request policy with the virtual server.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server.
- In the Access Policy area, from thePer-Request Policylist, select the policy that you configured earlier.
- ClickUpdate.
The per-request policy is now associated with the virtual server.
Virtual server Access Policy settings for
forward proxy
F5 recommends multiple virtual servers for configurations where Access
Policy Manager (APM) acts as an explicit or transparent forward
proxy. This table lists forward proxy configurations, the virtual servers recommended for each,
and whether an access profile and per-request policy should be specified on the virtual
server.
Forward proxy | Recommended virtual servers (by purpose) | Specify access profile? | Specify per-request policy? |
|---|---|---|---|
Explicit | Process HTTP traffic | Yes | Yes |
Process HTTPS traffic | Yes | Yes | |
Reject traffic other than HTTP and HTTPS | N/A | N/A | |
Transparent Inline | Process HTTP traffic | Yes | Yes |
Process HTTPS traffic | Only when a captive portal is also included in the configuration | Only when a captive portal is also included in the configuration | |
Forward traffic other than HTTP and HTTPS | N/A | N/A | |
Captive portal | Yes | No | |
Transparent | Process HTTP traffic | Yes | Yes |
Process HTTPS traffic | Only when a captive portal is also included in the configuration | Only when a captive portal is also included in the configuration | |
Captive portal | Yes | No |





