Manual Chapter :
Configuring a Custom Cipher String for SSL
Negotiation
Applies To:
Show Versions
BIG-IP AAM
- 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP APM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP Link Controller
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP Analytics
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP LTM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP PEM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP AFM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP DNS
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP ASM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
Configuring a Custom Cipher String for SSL
Negotiation
Overview: Configuring a custom cipher string
for SSL negotiation
Before the BIG-IP system can process SSL traffic, you need to define the
cipher string that the system will use to negotiate security settings with a client or
server system.
Typing a raw cipher string on the system can be tedious and contain typos. It can also
be unsecure, since the cipher string could inadvertently cause the system to negotiate in a way
that you didn't intend.
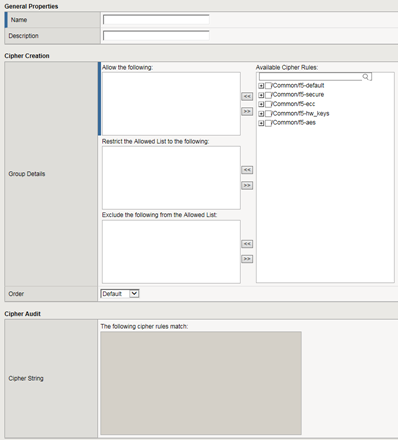
To avoid these problems, you can use cipher rules and cipher groups. With cipher rules and
groups, you instruct the BIG-IP system which cipher suites to include and exclude, and the system
will build the cipher string for you. This illustration shows the main screen for creating a
cipher group.
Use of cipher groups and cipher rules is optional.
About BIG-IP cipher
support
The BIG-IP system includes a default cipher string named DEFAULT, which contains a subset of the cipher suites that the BIG-IP system supports.
The full set of cipher suites that the BIG-IP system supports are contained in the NATIVE cipher string. The cipher suites contained in both the DEFAULT and NATIVE cipher string are eligible for hardware acceleration.
The BIG-IP system supports a large set of cryptographic parameters that you can use to modify how the BIG-IP manages SSL/TLS connections.
For TLS 1.2 and TLS 1.3, you can configure all or some of the cryptographic
parameters:
- Ciphersuites.
- Key exchange algorithms, for example RSA, DH, or ECDHE.
- Signature algorithms, for example RSA or ECDSA.
- Encryption primitives, for example AES128 or CAMELLIA.
- Hash algorithms, for example SHA256.
- Message authentication codes, for example HMAC-SHA256 or HMAC-SHA384.
What is a cipher rule?
A
cipher rule
is an object that contains
a list of cipher suites. After you create a cipher rule, you specify
it within a cipher group. A
cipher
group
is the object that builds the actual cipher string that the system will use during
SSL negotiation.You can use pre-defined cipher rules that the BIG-IP system provides, or you
can create your own.
An example of a cipher rule might be one that specifies only cipher suites
that use a particular bulk encryption algorithm and key exchange method.
DH Groups and Signature Algorithms allow modification of TLS
1.2 and 1.3 key agreements and signature algorithms respectively.
To create a custom SM2 cipher rule to use when creating a custom client SSL profile that
supports SM2, see the
Create a custom Client SSL profile that supports SM2
section for task details. What is a cipher group?
A
cipher group
contains a list of cipher
rules, and the instructions that the BIG-IP system
needs for building the cipher string it will use for security negotiation. The instructions tell
the system which cipher rules to include in the string, and how to apply them (allow, restrict,
or exclude, and in what order).Pre-built cipher groups
The BIG-IP system offers a few pre-built cipher groups that you can choose from to use as is
to build your final cipher string, However, it's common to create your own custom cipher group
instead.
Custom cipher
groups
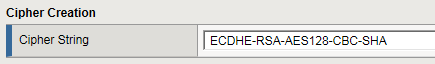
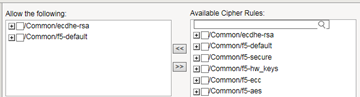
This illustration shows an example of a custom cipher group.
Using this cipher group, the BIG-IP system builds the final cipher string using a user-created
custom cipher rule named
/Common/my_ecdhe_rsa
and the pre-built cipher rule /Common/f5-default
.Notice that the system will exclude from the string any cipher suites defined in the pre-built
cipher rule
/Common/f5-hw_keys
.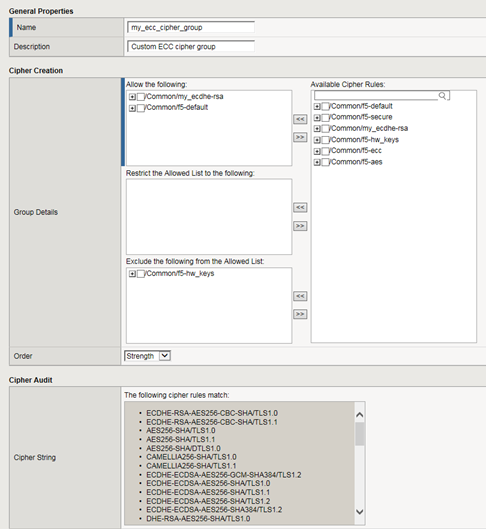
Also notice that the cipher group displays a preview of the final cipher
string after the instructions are applied.
To create a custom SM2 cipher group to use when
creating a custom client SSL profile that supports SM2, see the
Create a custom Client
SSL profile that supports SM2
section for task details. This section also provides
information on creating a custom SM2 cipher rule.Best practices for BIG-IP cipher
strings
For security and performance reasons, consider the following recommendations:
- When modifying cipher suites, F5 strongly recommends that you append cipher suite modifications to theDEFAULTcipher string.
- Include a cipher string that specifies the ECC key type. Due to their smaller size, ECC keys reduce computing costs while maintaining a similar level of security.
- Disable ADH ciphers but also include the keywordHIGH. To do this, just include both!ADHand:HIGHin your cipher string.
- For AES, DES, and RC4 encryption types, make sure you specify the DHE key exchange method. DHE usesperfect forward secracy, which creates an ephemeral private key for each new secure connection. This ensures the same private key is never used twice.
- When you use DHE, make sure that the SSL private key isn't being shared with a monitoring system or a security device like an intrusion detection or prevention system. And by the way, diagnostic tools likessldumpwon't work when you're using Forward Secrecy.
View all cipher suites supported by BIG-IP
system
Before you start this task, make sure
your user account gives you permission to access the BIG-IP
advanced shell.
You can use the BIG-IP advanced
shell to view all cipher suites that the BIG-IP system supports.
- Using a console access application such as PuTTY, log in to the advanced shell on the BIG-IP system.
- At the system prompt, type eithertmm --clientciphers allortmm --serverciphers all.The system lists all supported cipher suites for either client-side or server-side traffic.
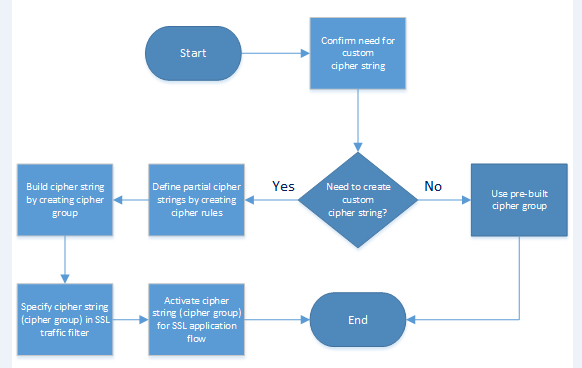
Task summary for configuring a custom cipher string
There are a few tasks you need to perform to use cipher rules and cipher groups to configure
the cipher string that the BIG-IP system will use for SSL negotiation.
This illustration shows the order that you need to perform these tasks in.
Confirm the
need for a custom cipher group
Before you create and deploy a custom cipher group
(that is, the final cipher string for SSL negotiation), you can
review the pre-built cipher groups on the BIG-IP system to see if
any of them already contains the cipher suites you need.
- On the Main tab, click .The screen displays a list of pre-built cipher groups.
- In the Name column, click the name of a cipher group.For example, click/Common/f5-ecc.The system displays the contents of the cipher group.
- In theAvailable Cipher Ruleslist, find the corresponding cipher rule and click the plus sign to view the cipher suites included in the rule.For example, this shows the pre-built cipher group/Common/f5-eccand the cipher suites included in it.
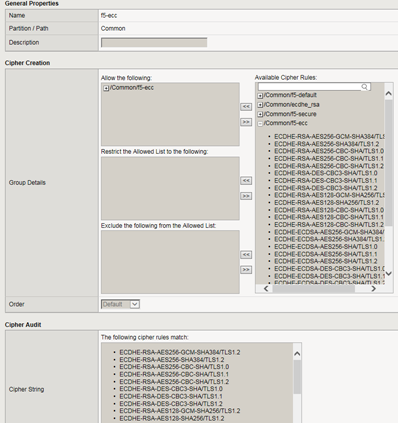 If the cipher suites in the corresponding cipher rule, as well as the single instructionAllow the following, are not sufficient for your cipher string, you'll need to create your own custom cipher group.
If the cipher suites in the corresponding cipher rule, as well as the single instructionAllow the following, are not sufficient for your cipher string, you'll need to create your own custom cipher group. - ClickCancel.
- As an option, you can repeat this task for any other pre-built cipher groups.
Create a custom cipher rule
When you create your own cipher rules for inclusion in a custom cipher group, the BIG-IP system builds a cipher string that includes or excludes the cipher suites and algorithms needed for negotiating SSL connections.
To create a custom SM2 cipher rule to use when creating a custom client SSL
profile that supports SM2, see the
Create a custom Client SSL profile that
supports SM2
section for task details.- On the Main tab, click .The screen displays a list of pre-built cipher rules.
- ClickCreate.
- In theNamefield, type a name for the cipher rule.Never include the prefixf5-in a cipher rule name. This prefix is reserved for pre-built cipher rules only.For example:
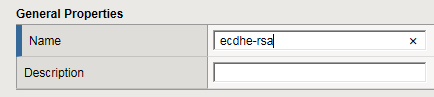
- In theCipher Suitesfield, type one or more cipher suites.For example:
- In theDH Groupsfield, type one or more Elliptic Curve Diffie-Hellman key exchange algorithms, separated by commas (:).The available named groups (formerly known ascurves) are:secp256r1,secp384r1, andX25519. You can also type a special keyword,DEFAULT, which represents the recommended set of named groups.For example, you can specifysecp256r1:X25519.
- In theSignature Algorithmsfield, type one or more signature algorithms, separated by commas (:), that you want to include in the cipher rule. You can also type a special keyword,DEFAULT, which represents the recommended set of signature algorithms.The available signature algorithms are:DSA-SHA1,DSA-SHA256,DSA-SHA384,DSA-SHA512,ECDSA-SHA1,ECDSA-SHA256,ECDSA-SHA384,ECDSA-SHA512,RSA-PKCS1-SHA1,RSA-PKCS1-SHA256,RSA-PKCS1-SHA384,RCS-PKCS1-SHA512,RSA-PSS-SHA256,RSA-PSS-SHA384, andRSA-PSS-SHA512.For example, you can specifyRSA_PKCS1_SHA256:ECDSA_P256_SHA256.
- ClickFinished.
The cipher rule now appears within any custom cipher group, in the list of available cipher rules.
Building a custom
Cipher Group
Before starting this task, make sure you've confirmed the need to create a custom
cipher string instead of using a pre-built cipher group.
You build a final, custom cipher string by creating a cipher
group. A
cipher group
contains the cipher rules
and instructions that the BIG-IP system needs for building the cipher string it will
use for security negotiation with a client or server system. To create a custom SM2 cipher group to use when creating a custom client SSL
profile that supports SM2, see the
Create a custom Client SSL profile that
supports SM2
section for task details. This section also provides
information on creating a custom SM2 cipher rule.- On the Main tab, click .The screen displays a list of pre-built cipher groups.
- ClickCreate.
- In theNamefield, type a name for the cipher group.Never include the prefixf5-in a cipher rule name. This prefix is reserved for pre-built cipher groups only.
- If you created any custom rules, then in the Cipher Creation area of the screen in theAvailable Cipher Ruleslist, verify that the custom rules appear in the list.
- For each cipher rule in theAvailable Cipher Ruleslist, click the plus sign to view the cipher suites included in the rule.For example, this shows the cipher suites included in the pre-built cipher rule named/Common/f5-ecc.
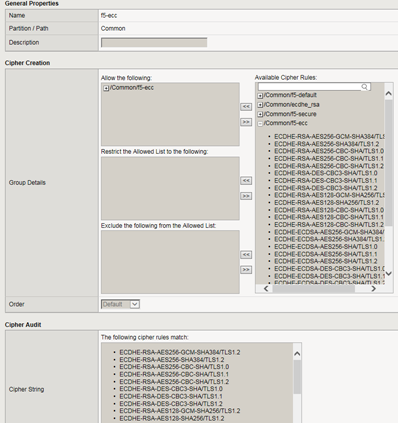
- In theAvailable Cipher Ruleslist, select the boxes for the cipher rules you want to allow for negotiating security for SSL connections.We strongly recommend that you select the cipher rule/Common/f5-default, and for added security, select other cipher rules, too.Here's an example of a list of available cipher rules that you might see within a cipher group. Notice that we've selected both a pre-built cipher rule and a custom cipher rule:
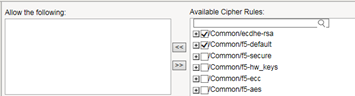
- In theGroup Detailssetting, move the selected cipher rules to theAllow the followingbox.Here we see that we're instructing the BIG-IP system to allow, during security negotiation, the cipher suites contained in the selected cipher rules:
- Again from theAvailable Cipher Ruleslist, select the boxes for the cipher rules you want to restrict the allowed cipher rules to when negotiating security for SSL connections.
- Move the selected cipher rules to theRestrict the Allowed list to the followingbox.
- If you want to exclude any cipher rules from the allowed list, then from theAvailable Cipher Ruleslist, select the boxes for the rules you want to exclude.
- Move the selected cipher rules to theExclude the following from the Allowed listbox.
- From theOrderlist, select the order that you want the BIG-IP system to use when negotiating SSL connections.The choices are:Default,Speed,Strength,FIPS, andHardware.
- In theCryptographic Parametersbox, view the cipher suites that the BIG-IP system will use to construct the final cipher string, based on the selections you made in the previous steps.
- ClickFinished.
After you complete this task, the BIG-IP system has a custom cipher group that the
BIG-IP system will use to build the final cipher string.
Specify the custom
cipher group within an SSL traffic filter
Before starting this task, make sure that the relevant traffic filter for managing SSL
traffic (either a Client SSL or Server SSL profile) exists on the BIG-IP system.
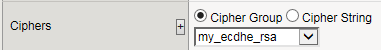
Specifying a custom cipher group within a particular Client SSL or
Server SSL profile tells the BIG-IP system which cipher string to use when
negotiating security settings.
- On the Main tab, click or .The Client SSL or Server SSL profile list screen opens.
- Click the name of a profile.
- From theConfigurationlist, selectAdvanced.
- On the right side of the screen, select theCustomcheck box.
- For theCipherssetting, clickCipher Groupand from the list, select a custom cipher group.This shows a custom cipher group selected for theCipherssetting:
- If you are using TLS 1.3, locate theOptions Listsetting and confirm that theNo TLSv1.3option does not appear in theEnabled Optionslist.
- ClickUpdate.
Activate a cipher
string for an application flow
Before starting this task, make sure that the
virtual server for the relevant SSL application flow exists on the BIG-IP
system.
You activate a cipher string for a specific
application flow by assigning a Client SSL or Server SSL profile (or both) to a virtual
server. This causes the BIG-IP system to use the cipher group specified in the profile
to build the cipher string for negotiating security settings for SSL
connections.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of a virtual server.
- From theConfigurationlist, selectAdvanced.
- For theSSL Profile (Client)and theSSL Profile (Server)settings, from theAvailablelist, select the name of the SSL profile you previously created, and move the name to theSelectedlist:
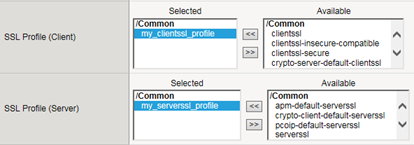 Using theSSL Profile (Server)setting is optional.
Using theSSL Profile (Server)setting is optional. - ClickUpdateto save the changes.
The BIG-IP system now uses the cipher group specified in an SSL profile to build a
cipher string to use when negotiating security for the relevant application
flow.





