Manual Chapter :
Configuring the BIG-IP System for Passive Monitoring
Applies To:
Show Versions
BIG-IP AAM
- 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP APM
- 17.0.0, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP Analytics
- 17.0.0, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP Link Controller
- 17.0.0, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP LTM
- 17.0.0, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP PEM
- 17.0.0, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP AFM
- 17.0.0, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP DNS
- 17.0.0, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP ASM
- 17.0.0, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
Configuring the BIG-IP System for Passive Monitoring
Overview: Configuring the BIG-IP System for Passive Monitoring
You can configure a physical interface on a BIG-IP ®system to operate in
passive mode
. In this mode, the interface accepts mirrored traffic from another device to collect data for analysis and intrusion detection.Important
: - The following hardware platform series do not support passive monitoring: 2000,4000,i2000 and i4000
- Virtualized setup using vCMP (Virtual Clustered Multiprocessing) are not supported for passive monitoring
- High Availability (HA) setup is not supported for passive monitoring
Passive mode behavior
The BIG-IP system analyzes the mirrored traffic, drops it, and then sends the resulting analytics data and log messages to a remote analytics and logging server. The mirrored traffic never leaves the system, and the BIG-IP system never acts on the headers and payload.
Benefits of passive monitoring
You don't need to deploy the BIG-IP system in line with your BIG-IP application delivery controller (ADC), which means there's no need to make changes to your network infrastructure.
Sample configuration
This illustration shows a configuration that includes a BIG-IP passive monitoring system.
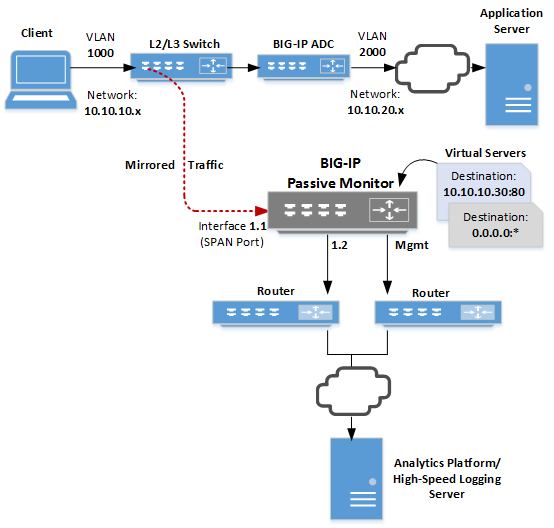
As we see in the illustration, a Layer 2/Layer 3 switch receives client traffic on the
10.10.10.x
network. The traffic comes into the switch, which mirrors it to a SPAN port on the BIG-IP system. A SPAN port
is an interface that can receive traffic mirrored to it from another device.After analyzing the traffic, the BIG-IP system forwards all analytics data and log messages through interface
1.2
to a remote analytics and logging server and then discards its copy of the application traffic.We've also configured two virtual servers to listen on the SPAN port. One virtual server listens for any mirrored HTTP traffic destined for a particular destination address on port 80, while the other listens for any traffic not caught by the HTTP virtual server.
Common use cases
Typical reasons for deploying a BIG-IP system as a passive monitoring device are:
- To collect HTTP analytics data
- To analyze mirrored traffic using a configured Application Security Manager (ASM) security policy. For more information, see the guide titledBIG-IP Application Security Manager: Implementationson the F5 websitehttp://support.f5.com.
- To collect application analytics data along with Subscriber-awareness made available by BIG-IP Policy Enforcement Manager™ (PEM™)
- To enable firewall services that report on possible infringements
- To detect denial-of-service attacks with signaling to some external entity for triggering actions
- To perform intrusion detection services
- To perform behavioral analysis
Prerequisite configuration
Before you set up a BIG-IP system as a passive monitoring system, make sure you have configured these things:
- A network device, such as a Layer 2/Layer 3 switch, configured to receive client application traffic and mirror it to the BIG-IP passive monitoring system.
- A user account with a user role that grants permission to perform all tasks (Administrator, Resource Administrator, or Manager).
- Provisioned the optional BIG-IP AVR module.
Other considerations
- A BIG-IP system operating in passive mode can accept mirrored traffic either raw or tunneled. In the case of tunneled traffic, the tunnel must be terminated on the BIG-IP system prior to the system analyzing the traffic.
- Global statistics do not differentiate between mirrored traffic and active traffic. However, statistics for an individual virtual server do differentiate between mirrored and active traffic because a virtual server applies to one type of traffic only.
- Passive mode is not available for interfaces on certain blade models.
- A trunk on which Link Aggregation Control Protocol (LACP) is enabled cannot operate as a passive monitoring interface.
- When you assign a passive monitoring interface to a BIG-IP VLAN, any self IP addresses associated with that VLAN will no longer respond to ARP requests.
Task summary for passive monitoring
To configure the system to do passive monitoring, you designate an interface on the BIG-IP passive monitoring system as a SPAN port and assign the interface to the ingress VLAN. Then, you configure a Fast L4 profile to disable SYN cookie support and Packet Velocity® Asic (PVA) acceleration. Finally, you set up whatever virtual servers you need to listen for mirrored traffic.
The result is that the system will analyze ingress traffic and send log messages and analytics data to a remote analytics and high-speed logging server.
Important
- The following hardware platform series do not support passive monitoring: 2000,4000,i2000 and i4000
- Virtualized setup using vCMP (Virtual Clustered Multiprocessing) are not supported for passive monitoring
- High Availability (HA) setup is not supported for passive monitoring
Configure an interface for passive monitoring
You can designate a physical interface on the BIG-IP ® system as a SPAN port. A
SPAN port
receives mirrored traffic for the purpose of doing passive monitoring of that traffic. Through passive monitoring, the system can collect data for the purpose of analytics or intrusion detection.
You can configure a trunk for passive monitoring. In this case, you must set the
Forwarding Mode
to Passive
separately on each link of the trunk.- On the Main tab, click .The Interface List screen displays the list of interfaces on the system.
- In the Name column, click an interface number.This displays the properties of the interface.
- For theStatesetting, verify that the interface is set toEnabled.
- From theForwarding Modelist, selectPassive.If you do not see thePassiveoption, your hardware platform does not support passive monitoring. The following hardware platform series do not support passive monitoring: 2000, 4000, i2000 and i4000.
- Click theUpdatebutton.
After you do this task, an interface on a passive monitoring system can receive mirrored traffic from another network device.
Be sure to assign the interface to a VLAN. Otherwise, the interface remains in an uninitialized state.
Create a BIG-IP VLAN to accept mirrored
traffic
Before performing this task, make sure that you have configured a VLAN with a tagged interface on
the upstream switch that will mirror ingress application traffic and send it to this
BIG-IP system.
For any BIG-IP interface that you've configured to receive mirrored application
traffic, you must create a VLAN and assign the interface to the VLAN.
- On the Main tab, click .The VLAN List screen opens.
- ClickCreate.
- In theNamefield, type a name for the VLAN.
- In theVLAN IDfield, type the same VLAN ID that you configured on the VLAN of the upstream switch that will send mirrored traffic to this BIG-IP system.
- For theInterfacessetting:
- From theInterfacelist, select the interface that you previously set toPassiveforwarding mode.
- From theTagginglist, selectTagged.This is the recommended configuration.
- ClickAdd.
- ClickFinished.
The BIG-IP system now has a VLAN
capable of receiving mirrored application traffic from an an upstream switch on the
network.
Configure a Fast L4 traffic filter for
passive monitoring
You create a Fast L4 profile to disable the Packet Velocity® ASIC
settings and disable the
SYN Challenge Handling
setting.- On the Main tab, click .The screen displays a list of Fast L4 profiles.
- ClickCreate.
- In theNamefield, type a name for the profile.An example of a profile name ismy_http_fastl4_profile.
- On the right side of the screen, select theCustomcheck box.
- From thePVA Accelerationlist, selectNone.
- Confirm that thePVA Flow Agingcheck box is cleared.
- Confirm that thePVA Flow Evictcheck box is cleared.
- For thePVA Offload Dynamicsetting, clear the check box.
- From theSYN Challenge Handlinglist, selectDisable Challenges.
- ClickFinished.
After completing these steps, the BIG-IP system has a Fast L4 profile for filtering mirrored traffic coming into the system through a SPAN port.
Create a virtual server for mirrored HTTP traffic
Before you create the virtual server, make sure that you have provisioned the BIG-IP AVR module.
You create an HTTP virtual server (also known as a listener) on a BIG-IP passive monitoring device to intercept specific mirrored HTTP traffic. This is traffic that you want to collect analytics and intrustion detection data on and then forward the data to a remote server.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- From theTypelist, selectPerformance (Layer 4).
- In theSource Addressfield, type0.0.0.0/0.
- In theDestination Address/Maskfield, type the destination address found in the destination IP address header of specific HTTP traffic that gets mirrored to the BIG-IP passive monitoring system.For example, if client traffic is destined for the IP address10.10.10.30, the BIG-IP passive monitoring system can listen for mirrored traffic with this destination address in its header in order to receive and analyze the mirrored traffic.
- In theService Portfield, type80, or selectHTTPfrom the list.
- From theConfigurationlist, selectAdvanced.
- From theProtocollist, selectTCP.
- From theProtocol Profile (Client)list, select the name of the Fast L4 profile you created earlier.
- From theHTTP Profile (Client)list, select the default HTTP profile namedhttp.If you'd rather assign a custom profile, create a new HTTP profile before you create this virtual server, and then select the profile from this list.
- From theHTTP Profile (Server)list, selectUse Client Profile.
- From theVLAN and Tunnel Trafficlist, retain the default selection,All VLANs and Tunnels.
- For theAddress Translationsetting, verify that the check box is cleared.
- For thePort Translationsetting, verify that the check box is cleared.
- For theSource Portsetting, verify thatPreserve Strictis selected.
- From theHTTP Analytics Profilelist, selectanalytics.
- From theTCP Analytics Profilelist, selecttcp-analytics.
- ClickFinished.
You now have a virtual server configured to accept specific HTTP traffic coming into the interface designated as a SPAN port.
Create a virtual server for non-specific mirrored traffic
Before you create the virtual server, make sure that you have provisioned the BIG-IP AVR module.
You can create a wildcard virtual server (also known as a listener) on the BIG-IP passive monitoring device. The purpose of a
wildcard virtual server
is to intercept any mirrored traffic that the other virtual servers on the BIG-IP passive monitoring device don't already intercept. Once the wildcard virtual server receives the traffic, it can monitor the traffic for analytics and intrusion detection.- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- From theTypelist, selectPerformance (Layer 4).
- In theSource Addressfield, type0.0.0.0/0.
- In theDestination Address/Maskfield, type0.0.0.0to accept any IPv4 traffic.
- In theService Portfield, type*or select* All Portsfrom the list.
- From theConfigurationlist, selectAdvanced.
- From theProtocollist, selectTCP.
- From theProtocol Profile (Client)list, select the name of the Fast L4 profile you created for filtering mirrored traffic.
- From theVLAN and Tunnel Trafficlist, retain the default selection,All VLANs and Tunnels.
- For theAddress Translationsetting, verify that the check box is cleared.
- For thePort Translationsetting, verify that the check box is cleared.
- For theSource Portsetting, verify thatPreserve Strictis selected.
- From theTCP Analytics Profilelist, selecttcp-analytics.
- ClickFinished.
You now have a virtual server configured to accept all traffic coming in through the interface designated as a SPAN port, except for traffic that specifically matches another virtual server on the system.
Create a pool of
remote logging servers
Before creating a pool of log servers, gather the IP addresses of the servers that you
want to include in the pool. Ensure that the remote log servers are configured to listen
to and receive log messages from the BIG-IP
system.
You create a pool of remote log servers to which
the BIG-IP system can send log messages.
- On the Main tab, click the applicable path.The Pool List screen opens.
- ClickCreate.The New Pool screen opens.
- In theNamefield, type a unique name for the pool.
- Using theNew Memberssetting, add the IP address for each remote logging server that you want to include in the pool:
- Type an IP address in theAddressfield, or select a node address from theNode List.
- Type a service number in theService Portfield, or select a service name from the list.Typical remote logging servers require port514.
- ClickAdd.
- ClickFinished.
Create a remote
high-speed log destination
Before creating a remote high-speed log destination, ensure that at least one pool of
remote log servers exists on the BIG-IP
system.
You create a log destination of the
Remote High-Speed Log
type to
specify that log messages are sent to a pool of remote log servers.- On the Main tab, click .The Log Destinations screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this destination.
- From theTypelist, selectRemote High-Speed Log.If you use log servers such as Remote Syslog, Splunk, or ArcSight, which require data be sent to the servers in a specific format, you must create an additional log destination of the required type, and associate it with a log destination of theRemote High-Speed Logtype. With this configuration, the BIG-IP system can send data to the servers in the required format.The BIG-IP system is configured to send an unformatted string of text to the log servers.
- From thePool Namelist, select the pool of remote log servers to which you want the BIG-IP system to send log messages.
- From theProtocollist, select the protocol used by the high-speed logging pool members.
- ClickFinished.
Create a formatted
remote high-speed log destination
Before you start this task, ensure that at least one remote high-speed log destination
exists on the BIG-IP system.
You create a formatted logging destination to specify that log
messages are sent to a pool of remote log servers, such as Remote Syslog, Splunk, or
ArcSight servers.
- On the Main tab, click .The Log Destinations screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this destination.
- From theTypelist, select a formatted logging destination, such asIPFIX,Remote Syslog,Splunk, orArcSight.ArcSight formatting is only available for logs coming from Advanced Firewall Manager (AFM), Application Security Manager (ASM), and the Secure Web Gateway component of Access Policy Manager (APM). IPFIX is not available for Secure Web Gateway. Remote Syslog formatting is the only type supported for logs coming from APM. The Splunk format is a predefined format of key value pairs.The BIG-IP system is configured to send a formatted string of text to the log servers.
- If you selectedRemote Syslog, then from theSyslog Formatlist select a format for the logs, and then from theHigh-Speed Log Destinationlist, select the destination that points to a pool of remote Syslog servers to which you want the BIG-IP system to send log messages.For logs coming from Access Policy Manager (APM), only the BSD Syslog format is supported.
- If you selectedSplunkorIPFIX, then from theForward Tolist, select the destination that points to a pool of high-speed log servers to which you want the BIG-IP system to send log messages.
- ClickFinished.
Create a publisher
Before you start this task, ensure that at least one destination associated with a pool
of remote log servers exists on the BIG-IP
system.
You can create a publisher to specify where the
BIG-IP system sends log messages for specific resources.
- On the Main tab, click .The Log Publishers screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this publisher.
- For theDestinationssetting, select a destination from theAvailablelist, and move the destination to theSelectedlist.If you are using a formatted destination, select the destination that matches your log servers, such as Remote Syslog, Splunk, or ArcSight.
- ClickFinished.
Create a logging
filter
Before you start this task, ensure that at least one log publisher is configured on the
BIG-IP system.
You create a custom log filter to specify the
system log messages that you want to publish to a particular log.
- On the Main tab, click .The Log Filters screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this filter.
- From theSeveritylist, select the level of alerts that you want the system to use for this filter.The severity level that you select includes all of the severity levels that display above your selection in the list. For example, if you selectEmergency, the system publishes only emergency messages to the log. If you selectCritical, the system publishes critical, alert, and emergency-level messages in the log.
- From theSourcelist, select the system processes from which messages will be sent to the log.
- In theMessage IDfield, type the first eight hex-digits of the specific message ID that you want the system to include in the log. Use this field when you want a log to contain only each instance of one specific log message.BIG-IP system log messages contain message ID strings in the format:xxxxxxxx:x:. For example, in this log message:Oct 31 11:06:27 olgavmmgmt notice mcpd[5641]: 01070410:5: Removed subscription with subscriber id lind, the message ID string is:01070410:5:. You enter only the first eight hex-digits:01070410.
- From theLog Publisherlist, select the publisher that includes the destinations to which you want to send log messages.
- ClickFinished.
Disable system
logging
When you no longer want the BIG-IP system to log information about its internal
systems, you can delete the log filter that you created. For example, when mitigating a
DoS attack, if you created a log filter that includes only one specific message in the
log, you can delete that log filter once you handle the attack.
- On the Main tab, click .The Log Filters screen opens.
- Select the check box next to the name of the log filter that you want to delete. ClickDelete, and then clickDeleteagain.





