Manual Chapter :
Local User Account Management
Applies To:
Show Versions
BIG-IP AAM
- 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP APM
- 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP Analytics
- 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP Link Controller
- 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP LTM
- 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP PEM
- 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP AFM
- 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP DNS
- 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP ASM
- 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
Local User Account Management
About local user
accounts
Managing local user accounts refers to the tasks of creating, viewing,
modifying, and deleting user accounts that reside on the
BIG-IP system.
The BIG-IP system stores local user accounts (including user names,
passwords, and user roles) in a local user-account database. When a user logs into the BIG-IP
system using one of these locally-stored accounts, the BIG-IP system checks the account to
determine the user role assigned to that user account for each partition to which the user has
access.
For example, suppose you grant local user
jsmith
access to partitions A
and B
, and in the process, assign her a role of
Manager for partition A
and a role of
Operator for partition B
. This means
that user jsmith
can create, modify,
and delete several types of local traffic objects that reside in partition A
, but in partition B
, she is restricted to enabling and disabling
nodes, pool members, virtual servers, and virtual addresses.For user
rjones
,
you can grant him access to the same partitions A
and B
, but assign him
the roles of Certificate Manager and Guest, respectively. For user rjones
, this means that with respect to partition
A
, he can fully manage digital
certificates that reside in that partition, but he has no permission to manage other types of
objects in the partition. For objects in partition B
, he has read access only.Displaying a list of local user accounts
Before performing this task, ensure that you have a role of Administrator or that you have a role of User Manager for the relevant partition.
Using the BIG-IP Configuration utility, you can display a list of existing
local user accounts. If the user role assigned to your account is Administrator, you
can view any user account on the BIG-IP system, in any
partition. If the user role assigned to your account is User Manager, you can view
any user account in any partition to which you have access on the BIG-IP system.
- On the Main tab, click .
- From thePartitionlist in the upper-left corner of the screen, set the current partition to the partition in which the relevant user accounts reside.
- View the list of user accounts.
Creating a local user account
To perform this task, you must have the Administrator or User Manager user role assigned to your user account. Note that if the user role assigned to your account is User Manager, you can only create a user account in the partitions to which you have access.
You perform this task to create a local user account for BIG-IP
administrative users.
User accounts on the BIG-IP system are case-sensitive.
Thus, the system treats user accounts such as
JONES
and
Jones
as two separate user accounts. Note, however, that certain user
names, such as admin
, are reserved, and are therefore exempt from
case-sensitivity. For example, you cannot create a user account named
Admin
, aDmin
, or
ADMIN
.- Access the BIG-IP Configuration utility.
- On the Main tab, click .The BIG-IP system displays the list of user accounts that reside in the current partition and in partitionCommon. Note that all users except those with a user role of No Access have at least read access to partitionCommon.
- From thePartitionlist in the upper-left corner of the screen, set the current partition to the partition in which you want the user account to reside.The partition you select in this step is not the partition to which you want the user account to have access.
- Click theCreatebutton.If theCreatebutton is unavailable, you do not have permission to create a local user account. You must have the Administrator or User Manager role assigned to your user account in order to create a local user account.
- For thePasswordsetting:
- In theNewfield, type a password for the user account.
- In theConfirmfield, type the password again.If the two passwords match, the BIG-IP system assigns the password to the user account. The user can log in to the system later and change this password.
- For thePartition Accesssetting:
- From theRolelist to select a user role.
- From thePartitionlist, select a partition name.
- Click theAddbutton.A user role pertaining to a partition now appears in the box.
- Repeat these steps for each partition to which you want to assign a role for this user.
Granting partition access to a BIG-IP user account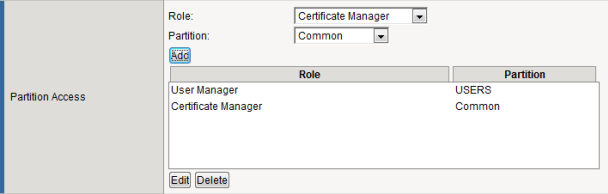 After you configure this setting, one or more role-partition combinations are specified for assignment to this user account.
After you configure this setting, one or more role-partition combinations are specified for assignment to this user account. - If you want to allow user access to the command line interface, then from theTerminal Accesslist, select a level of access.The advanced shell is only available for accounts with the Administrator or Resource Administrator user role.
- Click theFinishedbutton.
After you perform this task, a user account exists on the BIG-IP system that assigns
one or more roles, each corresponding to a partition on the system. The task also grants
some level of terminal access, either
tmsh
or Bash shell
access.Viewing the properties of a local user account
Before performing this task, ensure that you have a user role of Administrator or
that you have a role of User Manager for the relevant partition.
Using the BIG-IP Configuration utility, you can view the
properties of an individual account.
- On the Main tab, click .
- From thePartitionlist in the upper-left corner of the screen, set the current partition to the partition in which the relevant user accounts reside.
- In the user-account list, find the user account you want to view and click the account name. This displays the properties of that user account.
Modifying the properties of a local user account
Before performing this task, ensure that you have a user role of Administrator or
that you have a role of User Manager for the relevant partition.
Using the BIG-IP Configuration utility, you can modify the
properties of an existing local user account, other than the
root
account.If you change a role
on a user account while the user is logged into the system through the Traffic
Management Shell (
tmsh
), the BIG-IP system terminates the
user's tmsh
session when the user subsequently issues another
tmsh
command.- On the Main tab, click .
- From thePartitionlist in the upper-left corner of the screen, set the current partition to the partition in which the relevant user accounts reside.
- In the user account list, find the user account you want to view and click the account name. This displays the properties of that user account.
- To change the user's password, locate thePasswordsetting and replace the existing password in theNewandConfirmfields with the new password.
- To modify a user's role and partition access, do any of the following:
- To add a role for a partition, from theRolelist select a role, and from thePartitionlist, select a partition. Then click theAddbutton.The new role-partition entry appears in thePartitian Accessbox.
- To modify a role or partition, in thePartition Accessbox, select the role-partition entry you want to modify, and click theEditbutton. Then from theRoleorPartitionlist, select a new role or partition. Then click theAddbutton.
- To delete a role-partition entry, in thePartition Accessbox, select the role-partition entry you want to delete, and click theDeletebutton.
You can add, modify, or delete only those role-partition entries that you are authorized to manage based on your own user role and partition access. - If you want to change the user's access to the command line interface, then from theTerminal Accesslist, select a level of access.The advanced shell is only available for accounts with the Administrator or Resource Administrator user role.
- Click theUpdatebutton.
Deleting a local user account
Before performing this task, ensure that you have a user role of Administrator or
that you have a role of User Manager for the relevant partition.
When you delete a local user account, you remove it permanently from the local
user-account database on the BIG-IP system. If the account you are using has the
Administrator or User Manager user role, you can delete other local user accounts. A
user with the Administrator role can delete any user account on the BIG-IP system in any partition. A user with the User Manager role can
delete user accounts on the BIG-IP system in only those partitions to which she has
access.
You cannot delete the
admin
user account, nor
can you delete the user account with which you are logged in.The Administrator user role provides access to the BIG-IP system
prompt. If another user with the Administrator user role is currently logged in to
the system and you delete the user account, the user can still run commands at the
BIG-IP system command prompt until he or she logs off of the system.
- On the Main tab, click .
- In the user-account list, locate the name of the account you want to delete and select the check box to the left of the account name.
- Click theDeletebutton.
- ClickDeleteagain.
Properties of a local BIG-IP system user account
This table lists and describes the properties that define a local BIG-IP user
account.
Property |
Description |
Default Value |
|---|---|---|
User Name |
Specifies the name of the user account. The BIG-IP system is case-sensitive,
which means that names such as JONES and Jones are treated as separate user
accounts. |
No default value |
Partition |
When viewing the properties of an existing user account, displays the name of the
partition in which the user account object resides. All partitionable BIG-IP system
objects (including user account objects) have the Partition
property. Note that you cannot edit the value of this setting. |
No default value |
Password |
Specifies a password that the user will use to log in to the BIG-IP
system. |
No default value |
Partition Access |
Specifies a user role for each partition to which the user has access when logged on to the BIG-IP
system. When you assign the user role of Administrator, Resource Administrator, or Auditor, the list of partitions to choose from becomes unavailable.
(Accounts with these roles always have universal
partition access, that is, access to all partitions.) |
All |
Terminal Access |
Specifies the level of access to the BIG-IP system command line interface.
Possible values are: Disabled and Advanced
shell . Users with the Administrator or
Resource Administrator role assigned to their accounts can
have advanced shell access, that is, permission to use all BIG-IP system command line
utilities, as well as any Linux commands. |
Disabled |
About secure password policy configuration
The BIG-IP system includes
a
security policy for creating passwords for local BIG-IP system user accounts. A secure password
policy ensures that BIG-IP system users who have local user accounts create and maintain
passwords that are as secure as possible.
The secure password policy feature includes two distinct types of password restrictions:
- Enforcement restrictions
- These are, specifically, character restrictions that you can enable or disable. They consist of the minimum password length and the required character types (numeric, uppercase, lowercase, and other kinds of characters).
- Policy restrictions
- These restrictions represent the minimum and maximum lengths of time that passwords can be in effect. Also included in this type of policy restriction are the number of days prior to password expiration that users are warned, and the number of previous passwords that the BIG-IP system should store, to prevent users from re-using former passwords. These restrictions are always enabled, although using the default values provides a minimal amount of restriction.
Passwords for remotely-stored user accounts are not subject to this password policy, but might
be subject to a separate password policy defined on the remote system.
About secure password policy enforcement
In versions of BIG-IP prior to 14.0.0, Secure Password Policy is available but
not enabled. Beginning with BIG-IP version 14.0.0, Secure Password Policy is enabled by
default. This means that on new installations, the passwords for root and admin
accounts are expired and must be changed upon initial login. This only applies to new
installations and does not apply to upgrades or UCS load. Password policy settings from
the UCS file are imported, so if you load a UCS from an 13.1 (or earlier) onto version
14.0 and the password policy was set to disabled in that UCS, then the password policy
will be disabled on version 14.0.
When you login to either the admin or root account, you will be
prompted to change the password. Whichever account password you change first will also
set the password for the other account. For example, if on a new installation you change
the admin password for the first time, the root password will also be changed. This is a
one-time event; meaning that future changes to the root password will not affect the
password for the admin user ID.
During an upgrade, the password policy settings from the previous version are rolled
forward. This means that you will not encounter the secure password policy enforcement
settings if you are upgrading; only on new installations or on a reset to factory
default.
The new password must be more than 6 characters long and must pass
basic pam_cracklib checks including:
- cannot be a dictionary word
- cannot be a palindrome of the old password
- cannot be a case change only of an older password
- cannot be a rotated version of the old password
- cannot be too similar to the old password
- cannot be too simple
Configuration settings for a secure password policy
This table lists and describes the settings for a password policy. These settings apply to all local user accounts on the BIG-IP system.
Setting | Description | Default value |
|---|---|---|
Secure Password Enforcements | Enables or disables character restrictions, that is, a policy for minimum
password length and required characters. When you enable this setting, the BIG-IP
Configuration utility displays the Minimum Length and
Required Characters settings. | Enabled |
Minimum Length | Specifies the minimum number of characters required for a
password, and the allowed range of values is 6 to 255 . | 6 |
Required Characters | Specifies the number of numeric, uppercase, lowercase, and
other characters required for a password. The allowed range of values is 0 to 127 . | 0 |
Password Memory | Specifies, for each user account, the number of former passwords that the BIG-IP
system retains to prevent the user from re-using a recent password. The range of
allowed values is 0 to 127 . | 0 |
Minimum Duration | Specifies the minimum number of days before a user can change a password. The
range of allowed values is 0 to 255 . | 0 |
Maximum Duration | Specifies the maximum number of days that a user's password can be valid. The
range of allowed values is 1 to 99999 . | 99999 |
Expiration Warning | Specifies the number of days prior to password expiration that the system sends a
warning message to a user. The range of allowed values is 1 to
255 . | 7 |
Maximum Login Failures | Denies access to a user after the specified number of failed authentication
attempts. The administrator can then reset the lock to re-enable access for the
user. | 0 |
Required Lowercase | Specifies the minimum number of lowercase characters required for a
password. | 0 |
Required Numeric | Specifies the minimum number of numeric characters required for a
password. | 0 |
Required Special | Specifies the minimum number of special characters required for a
password. | 0 |
Required Uppercase | Specifies the minimum number of uppercase characters required for a
password. | 0 |
Configuring a
password policy for administrative users
Use this procedure to require BIG-IP system users to create
strong passwords and to specify the maximum number of BIG-IP login failures that the
system allows before the user is denied access.
You must have the user role of Administrator assigned to your
account to configure this feature.
- On the Main tab, click .
- On the menu bar, clickAuthentication.
- From theSecure Password Enforcementlist, selectEnabled.Additional settings appear on the screen.
- For theMinimum LengthandRequired Characterssettings, configure the default values, according to your organization's internal security requirements.
- In thePassword Memoryfield, type the number of passwords that the user cannot re-use. The valid range is from0to127.
- In theMinimum Durationfield, type the minimum number of days before which users cannot change their passwords. The valid range is from0to255.
- In theMaximum Durationfield, type the maximum number of days that a password is valid. Users must change their passwords before the maximum duration is reached.The value of this setting determines when users receive warning messages to change their passwords. If you change the value of this setting, any subsequent warning messages that users receive indicate the previous maximum duration value, rather than the new value. Once a user changes the password, however, subsequent reminder messages show the new value.
- In theExpiration Warningfield, type the number of days before the password expires that the user receives a password expiration warning. The valid range is from1to255.
- In theMaximum Login Failuresfield, specify a number.If the user fails to log in the specified number of times, the user is locked out of the system. Therefore, F5 Networks recommends that you specify a value that allows for a reasonable number of login failures before user lockout.
- ClickUpdate.
User authentication lockout
When you configure the password policy restrictions for user accounts, you can configure the
number of failed authentication attempts that a user can perform before the user is locked out of
the system. If a user becomes locked out, you can remove the lock to re-enable access for the
user.
Unlocking a user account
Before performing this task, you must have an Administrator user role or have a User Manager role with access to the partition containing the locked user account.
If a user exceeds the number of failed login attempts that the password policy allows,
the BIG-IP system locks the user account. You can perform this
task to unlock the account.
- Access the BIG-IP Configuration utility.
- On the Main tab, click .The BIG-IP system displays the list of user accounts that reside in the current partition and in partitionCommon. Note that all users except those with a user role of No Access have at least read access to partitionCommon.
- In the upper-left corner of the screen, from thePartitionlist, select the partition in which the user account that you want to unlock resides.
- In the user account list, locate the name of the account you want to unlock and select the check box to the left of the account name.
- Click theUnlockbutton.
After you perform this task, the user can attempt to log in to the BIG-IP system.





