Manual Chapter :
Configuring Remote High-Speed Logging of Network Firewall Events
Applies To:
Show Versions
BIG-IP APM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP Link Controller
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP Analytics
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP LTM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP PEM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP AFM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP DNS
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
BIG-IP ASM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0
Configuring Remote High-Speed Logging of Network Firewall Events
Overview: Configuring
remote high-speed Network Firewall event logging
You can configure the BIG-IP
system to log information about the BIG-IP system Network Firewall events and send the log
messages to remote high-speed log servers.
The
BIG-IP system Advanced Firewall Manager™ (AFM™) must be licensed and provisioned before you can configure Network
Firewall event logging.
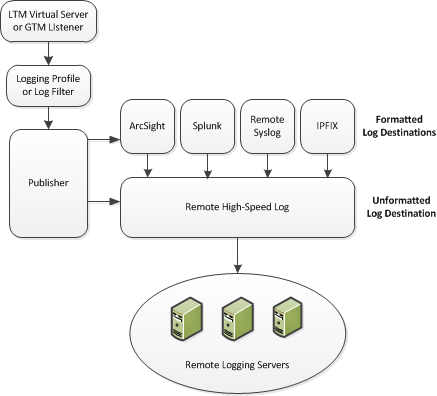
This illustration shows the association of the configuration objects for
remote high-speed logging.
Association of
remote high-speed logging configuration objects
About the configuration objects of remote high-speed Network Firewall event logging
When configuring remote high-speed logging of Network Firewall events, it is helpful to understand the
objects you need to create and why, as described here:
Object |
Reason |
Applies to |
|---|---|---|
Pool of remote log servers |
Create a pool of remote log servers to which the BIG-IP system
can send log messages. |
Creating a pool of remote logging servers. |
Destination (unformatted) |
Create a log destination of Remote High-Speed Log type that specifies a pool of remote log servers. |
Creating a remote high-speed log destination. |
Destination (formatted) |
If your remote log servers are the ArcSight, Splunk, IPFIX, or Remote Syslog type, create an additional log destination to format the logs in the required format and forward the logs to a remote high-speed log destination. |
Creating a formatted remote high-speed log destination. |
Publisher |
Create a log publisher to send logs to a set of specified log destinations. |
Creating a publisher. |
DNS Logging profile |
Create a custom DNS Logging profile to define the data you want the BIG-IP system to include in the DNS logs and associate a log publisher with the profile. |
Creating a custom Network Firewall Logging profile. |
LTM virtual server |
Associate a custom DNS profile with a virtual server to define how the BIG-IP system logs the DNS traffic that the virtual server processes. |
Creating a virtual server for Network Firewall evemt logging. |
Create a pool of remote logging servers
Before creating a pool of log servers, gather the IP addresses of the servers that you want to include in the pool. Ensure that the remote log servers are configured to listen to and receive log messages from the BIG-IP system.
Create a pool of remote log servers to which the BIG-IP system can send log messages.
- At the top of the screen, clickConfiguration.
- On the Main tab, click .The Pool List screen opens.
- ClickCreate.The New Pool screen opens.
- In theNamefield, type a unique name for the pool.
- Using theNew Memberssetting, add the IP address for each remote logging server that you want to include in the pool:
- Type an IP address in theAddressfield, or select a node address from theNode List.
- Type a service number in theService Portfield, or select a service name from the list.Typical remote logging servers require port514.
- ClickAdd.
- ClickFinished.
Create a remote high-speed log destination
Before creating a remote high-speed log destination, ensure that at least one pool
of remote log servers exists on the BIG-IP system.
Create a log destination of the
Remote High-Speed Log
type to
specify that log messages are sent to a pool of remote log servers.- On the Main tab, click .The Log Destinations screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this destination.
- From theTypelist, selectRemote High-Speed Log.If you use log servers such as Remote Syslog, Splunk, or ArcSight, which require data be sent to the servers in a specific format, you must create an additional log destination of the required type, and associate it with a log destination of theRemote High-Speed Logtype. With this configuration, the BIG-IP system can send data to the servers in the required format.The BIG-IP system is configured to send an unformatted string of text to the log servers.
- From thePool Namelist, select the pool of remote log servers to which you want the BIG-IP system to send log messages.
- From theProtocollist, select the protocol used by the high-speed logging pool members.
- ClickFinished.
Create a formatted remote high-speed log destination
Ensure that at least one remote high-speed log destination exists on the BIG-IP system.
Create a formatted logging destination to specify that log messages are sent to a
pool of remote log servers, such as Remote Syslog, Splunk, or IPFIX servers.
- On the Main tab, click .The Log Destinations screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this destination.
- From theTypelist, select a formatted logging destination, such asRemote Syslog,Splunk, orIPFIX.The Splunk format is a predefined format of key value pairs.The BIG-IP system is configured to send a formatted string of text to the log servers.
- If you selectedRemote Syslog, then from theSyslog Formatlist select a format for the logs, and then from theHigh-Speed Log Destinationlist, select the destination that points to a pool of remote Syslog servers to which you want the BIG-IP system to send log messages.For logs coming from Access Policy Manager (APM), only the BSD Syslog format is supported.
- If you selectedSplunkorIPFIX, then from theForward Tolist, select the destination that points to a pool of high-speed log servers to which you want the BIG-IP system to send log messages.
- ClickFinished.
Create a publisher
Ensure that at least one destination associated with a pool of remote log servers
exists on the BIG-IP system.
Create a publisher to specify where the BIG-IP system sends log messages for
specific resources.
- On the Main tab, click .The Log Publishers screen opens.
- ClickCreate.
- In theNamefield, type a unique, identifiable name for this publisher.
- For theDestinationssetting, select a destination from theAvailablelist, and click<<to move the destination to theSelectedlist.If you are using a formatted destination, select the destination that matches your log servers, such as Remote Syslog, Splunk, or ArcSight.
- ClickFinished.
Creating a custom Network Firewall Logging profile
Create a custom logging profile to log messages about Network Firewall events.
- On the Main tab, click .The Logging Profiles list screen opens.
- ClickCreate.The Create New Logging Profile screen opens.
- In theNamefield, type a unique name for the profile.
- Select theNetwork Firewallcheck box.
- In the Network Firewall area, from thePublisherlist, select the publisher the BIG-IP system uses to log Network Firewall events.
- Set anAggregate Rate Limitto define a rate limit for all combined network firewall log messages per second.Beyond this rate limit, log messages are not logged.Rate Limits are calculated per-second per TMM. Each TMM throttles as needed independently of other TMMs.
- For theLog Rule Matchessetting, select how the BIG-IP system logs packets that match ACL rules. You can select any or all of the options.OptionEnables or disables logging of packets that match ACL rules configured with:Acceptaction=AcceptDropaction=DropRejectaction=RejectWhen an option is selected, you can configure a rate limit for log messages of that type.
- Select theLog IP Errorscheck box, to enable logging of IP error packets.When this setting is enabled, you can configure a rate limit for log messages of this type.
- Select theLog TCP Errorscheck box, to enable logging of TCP error packets.When this is enabled, you can configure a rate limit for log messages of this type.
- Select theLog TCP Eventscheck box, to enable logging of open and close of TCP sessions.When this is enabled, you can configure a rate limit for log messages of this type.
- Enable theLog Translation Fieldssetting to log both the original IP address and the NAT-translated IP address for Network Firewall log events.
- Enable theLog Geolocation IP Addresssetting to specify that when a geolocation event causes a network firewall action, the associated IP address is logged.
- From theStorage Formatlist, select how the BIG-IP system formats the log.OptionDescriptionNoneSpecifies the default format type in which the BIG-IP system logs messages to a remote Syslog server, for example:"management_ip_address","bigip_hostname","context_type","context_name","src_ip","dest_ip","src_port","dest_port","vlan","protocol","route_domain","acl_rule_name","action","drop_reasonField-ListAllows you to:
- Select, from a list, the fields to be included in the log.
- Specify the order the fields display in the log.
- Specify the delimiter that separates the content in the log. The default delimiter is the comma character.
User-DefinedAllows you to:- Select, from a list, the fields to be included in the log.
- Cut and paste, in a string of text, the order the fields display in the log.
- In the IP Intelligence area, from thePublisherlist, select the publisher that the BIG-IP system uses to log source IP addresses, which are identified and configured for logging by an IP Intelligence policy.The IP Address Intelligence feature must be enabled and licensed.
- Set anAggregate Rate Limitto define a rate limit for all combined IP Intelligence log messages per second.Beyond this rate limit, log messages are not logged.Rate Limits are calculated per-second per TMM. Each TMM throttles as needed independently of other TMMs.
- Enable theLog Translation Fieldssetting to log both the original IP address and the NAT-translated IP address for IP Intelligence log events.
- In the Traffic Statistics area, from thePublisherlist, select the publisher that the BIG-IP system uses to log traffic statistics.
- For theLog Timer Eventssetting, enableActive Flowsto log the number of active flows each second.
- For theLog Timer Eventssetting, enableReaped Flowsto log the number of reaped flows, or connections that are not established because of system resource usage levels.
- For theLog Timer Eventssetting, enableMissed Flowsto log the number of packets that were dropped because of a flow table miss. A flow table miss occurs when a TCP non-SYN packet does not match an existing flow.
- For theLog Timer Eventssetting, enableSYN Cookie (Per Session Challenge)to log the number of SYN cookie challenges generated each second.
- For theLog Timer Eventssetting, enableSYN Cookie (White-listed Clients)to log the number of SYN cookie clients whitelisted each second.
- ClickFinished.
Assign this custom network firewall Logging profile to a virtual server.
Configuring a virtual server for event logging
Ensure that at least one log publisher exists on the AFM Network Firewall system.
Assign a custom network firewall logging profile to a virtual server when you want the system to log network firewall events on the traffic that the virtual server processes.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- On the menu bar, click .The screen displays policy settings for the virtual server.
- In theLog Profilesetting, selectEnabled. Then, select one or more profiles, and move them from theAvailablelist to theSelectedlist.If you do not have a custom profile configured, select the predefined logging profileglobal-networkto log Advanced Firewall Manager events. Note that to log global, self IP, and route domain contexts, you must enable a Publisher in theglobal-networkprofile.
- ClickUpdateto save the changes.
Disabling logging
Disable event logging when you need to suspend logging for a period of time or you no
longer want the BIG-IP system to log specific events.
Logging is
enabled by adding log settings to the access profile.
- To clear log settings from access profiles, on the Main tab, click .
- Click the name of the access profile.Access profile properties display.
- On the menu bar, clickLogs.
- Move log settings from theSelectedlist to theAvailablelist.
- ClickUpdate.
Logging is disabled for the access profile.





