Manual Chapter :
Configuring Dynamic ACLs
Applies To:
Show Versions
BIG-IP APM
- 21.1.0 , 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0
Configuring Dynamic ACLs
Overview: Applying
ACLs from session variables
You can apply ACLs by using the dynamic ACL action in an APM access
policy. Sources of dynamic ACL entries are session variables that can contain data from
external servers, such as Active Directory, RADIUS, or LDAP, or internal sources.
After you configure ACLs in a supported format, you can configure a
dynamic ACL action to extract and use the ACLs.
About Dynamic ACLs
A
dynamic ACL
is an ACL whose ACL entries are defined during access policy
execution time, and the entries are stored and enforced for that particular Access session.
The source of ACL entries is a session variable having content that can be sourced from
external sources such as ActiveDirectory, LDAP, RADIUS, or internal sources such as iRules,
data groups, or any combination of the above.Access Policy Manager supports dynamic ACLs in F5 ACL
format, and in a subset of the Cisco ACL format.
A dynamic ACL action includes these configuration elements and
options:
- Source
- Specifies a type of session variable (CustomorCiscoAV-PairVSA) and the source session variable from which the dynamic ACL is derived. ForCustomdynamic ACL entries, this is any session variable that is populated with an F5 format ACL. ForCiscoAV-PairVSAdynamic ACL entries, this is predefined assession.radius.last.attr.vendor-specific.1.9.1.
- ACL
- Specifies the dynamic ACL container configured on the BIG-IP system. Dynamic ACL objects are empty container ACLs that you define on the system.
- Format
- Specifies the format (F5 or Cisco) used to define the ACL.
To succeed, a dynamic ACL action must follow actions
that populate the session variables with ACLs.
Configuring a
dynamic ACL container
A dynamic ACL container provides an
unconfigured ACL that you select when you specify a dynamic ACL action in an access
policy.
- On the Main tab, click .The ACLs screen opens.
- ClickCreate.The New ACL screen opens.
- In theNamefield, type a name for the access control list.
- From theTypelist, selectDynamic.
- In theDescriptionfield, add a description of the access control list.
- From theACL Orderlist, specify the order in which to add the new ACL relative to other ACLs:
- SelectAfterto add the ACL after a specific ACL and select the ACL from the list.
- SelectSpecifyto type the specific number of the ACL in the field.
- SelectLastto add the ACL at the last position in the list.
- From theMatch Case for Pathslist, selectYesto match case for paths, orNoto ignore path case.This setting specifies whether alphabetic case is considered when matching paths in an access control entry.
- Click theCreatebutton.The ACL Properties screen opens; it displays the newly configured dynamic ACL container.
Adding a dynamic ACL to an access policy
Before you start this task, configure an access profile and a dynamic ACL container.
Add an authentication action to the access policy before the dynamic ACL action so that
Access Policy Manager can first capture authentication variables that contain the
dynamic ACL specification.
Configure a dynamic ACL action to extract and
apply an ACL from an AAA server (Active Directory, LDAP, or RADIUS).
Because a
dynamic ACL is associated with a user directory, you can use one to assign ACLs
specifically per the user session.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
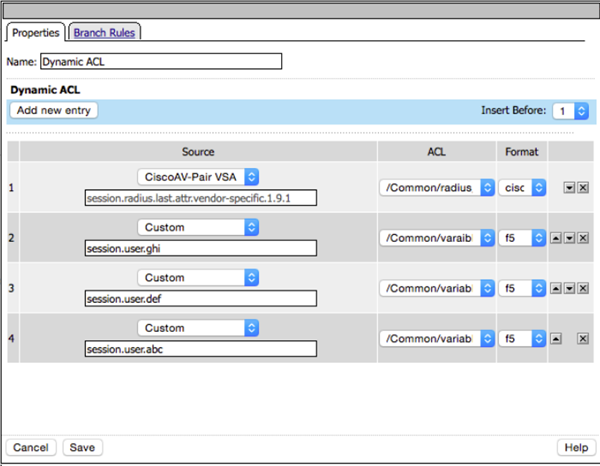
- From the Assignment tab, selectDynamic ACL, and clickAdd Item.A properties screen opens.
- To add an ACL, click theAdd new entrybutton.A new row opens in the table.
- Select one of these from the list:
- CustomSelect to use a custom ACL. The ACL source can be an attribute from an AD, RADIUS, or LDAP directory, or any properly formatted session variable.
- Cisco AV-Pair VSASelect to use a Cisco AV-Pair ACL from a RADIUS directory.
- In theSourcefield, type the attribute from which the Dynamic ACL action extracts ACLs.If you are using Cisco AV-Pair VSA from a RADIUS server, the field is prepopulated withsession.radius.last.attr.vendor-specific.1.9.1.
- From theACLlist, select the dynamic ACL container that you configured previously.
- From theFormatlist, select the format in which the ACL is specified.
- To configure another ACL, click theAdd new entrybutton and repeat the configuration steps.
- SelectSaveto save any changes and return to the policy.
- Complete the policy:
- Add any additional policy items you require.
- Change the ending fromDenytoAllowon any access policy branch on which you want to grant access.
- Click theApply Access Policylink to apply and activate the changes to the policy.
The access policy is configured to extract an ACL from an AAA server and apply it when
processing occurs on the access policy branch.
To
apply this access policy to network traffic, add the access profile to a virtual
server.
To ensure
that logging is configured to meet your requirements, verify the log settings for
the access profile.
Using dynamic ACLs with multiple dynamic ACL objects
In an access policy, you can use the Variable
Assign agent before a Dynamic ACL agent having multiple dynamic ACL objects. This allows
you to combine multiple objects in a dynamic ACL. Here an example shows the general
steps to do this. The policy you are working with needs to have a Variable Assign
agent.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
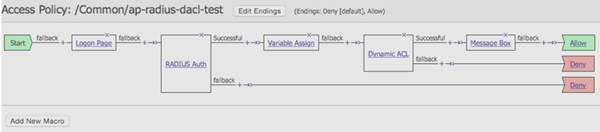
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
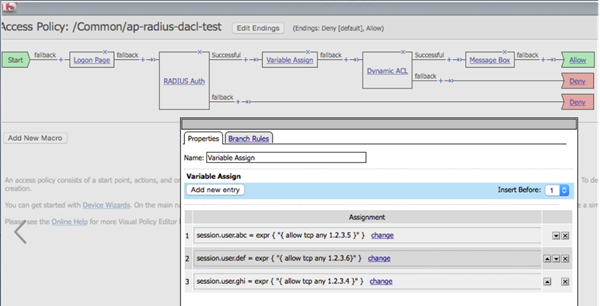
- In the visual policy editor, create entries for session variables with the required ACL values in the Variable Assign agent. For example:
- On the Main tab, click .
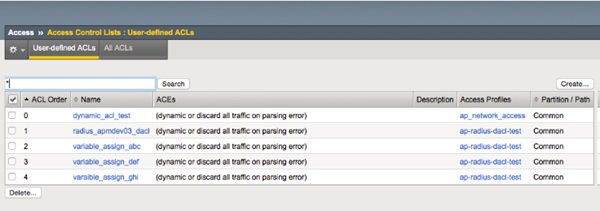
- Create the corresponding dynamic ACL objects in Access Control Lists. For example:
- In the visual policy editor, add the assigned session variable dynamic ACL values to the Dynamic ACL agent selecting the corresponding ACL in the appropriate format (Cisco or F5). For example:
- Add the ACL entries to the RADIUS server (here namedapm03) for the corresponding user to be applied as shown in the example.In this example, for the host to be allowed, you need to specify the virtual server IP address and not the pool IP address, and the log indicates the logging for the corresponding log message to appear in/var/log/pktfilter:test Cleartext-Password := "click123" Service-Type = Framed-User, Framed-Protocol = PPP, Framed-Filter-Id = "std.ppp", Framed-MTU = 1500, Framed-Compression = Van-Jacobsen-TCP-IP, Cisco-AVPair = "ip:inacl#1=permit tcp any host 10.192.152.109 log", Cisco-AVPair += "ip:inacl#2=deny tcp any any log"
- Access the virtual IP address (for example,http://10.192.152.109) and upon entering the credentialstest/click123, a message box displayingDynamic ACL is assignedappears.
- On the BIG-IP system 10.192.34.121 command line, typingsessiondump –allkeysshows the following values forsession.assigned.dacls:cdc9d4e5.session.assigned.dacl./Common/radius_apm03_dacl 65 { allow log tcp any 10.192.152.109 } { discard log tcp any any } cdc9d4e5.session.assigned.dacl./Common/variable_assign_ghi 26 { allow tcp any 1.2.3.4 } cdc9d4e5.session.assigned.dacl./Common/variable_assign_abc 26 { allow tcp any 1.2.3.5 } cdc9d4e5.session.assigned.dacl./Common/variable_assign_def 26 { allow tcp any 1.2.3.6 } cdc9d4e5.session.assigned.dacls 112 /Common/radius_apm03_dacl /Common/variable_assign_ghi /Common/variable_assign_abc /Common/variable_assign_def cdc9d4e5.session.radius. /Common/ap-radius-dacl-test_act_radius_auth_ag.attr. vendor-specific.1.9.1 83 ip:inacl#1=permit tcp any host 10.192.152.109 log | ip:inacl#2=deny tcp any any log
- When you clickContinuein theDynamic ACL is assignedmessage box, the pool IP address (10.192.254.11:80) with the test php page opens. The following log entry in/var/log/pktfiltershows the allowed ACL:Nov 9 10:17:40 bigip4002mgmt notice tmm[32697]: 01580005:5: /Common/ap-radius-dacl-test:Common:cdc9d4e5: allow ACL: /Common/radius_apmdev03_dacl@cdc9d4e5:0 packet:http://10.192.152.109/ tcp 192.168.85.53:59888 -> 10.192.152.109:80
F5 ACL format
Specifies F5 ACL syntax and provides examples. This syntax
applies to both static and dynamic ACLs.
Specify an F5 ACL using this syntax.
comment { action [logging_options] context } comment { action [logging_options]
context }...
The syntax allows multiple ACLs in a single string along with comments.
comment
Any characters before an open curly brace ({) or after a closed curly brace (}) are treated
as comments. Comments are optional. They have no effect on the ACLs. These examples show
identical ACLs with different comments; APM interprets them as being
the same.
String comments
This is my HTTP server ACL { allow tcp any 1.2.3.4:80 } This is my default ACL {
reject ip any any }
A space as a comment
{ allow tcp any 1.2.3.4:80 } { reject ip any any }
Newline comments
{ allow tcp any 1.2.3.4:80 }\n
{ reject ip any any }\n
Vertical bar comments
| { allow tcp any 1.2.3.4:80 } | { reject ip any any } |
action
This is an action that the ACL takes on traffic that matches the ACL
context.
allow |
Allows the specified traffic. |
reject |
Rejects the specified traffic and sends a TCP RST code
to the initiator. |
discard |
Silently drops the packets. |
continue |
Skips checking against the remaining access control entries in
this ACL, and continues evaluation at the next ACL. |
logging_options
Specifying a logging option is optional.
log |
Enables default logging for the ACL |
log-packet |
Writes packet-level logs to the packet filter log file |
log-verbose |
Writes verbose logs |
log-summary |
Writes summary logs |
log-config |
Writes configuration logs to the configuration log file |
context
Context specifies a protocol followed by addresses, networks, and ports
for the ACL action.
http |
HTTP protocol traffic. Requires that you specify an HTTP or
HTTPS URL in the ACL definition |
udp |
UDP traffic only |
tcp |
TCP traffic only |
ip |
IP protocol traffic |
F5 ACL format treats IP protocol number zero (0) as a wildcard, meaning that
it applies to all IPv4 and IPv6 traffic.
For example,
{ reject ip 0 any any }
is the equivalent of { reject
ip any any }
.Address, network, and port specification
Specify addresses in a pair separated by a space. The first address in the pair should
match the host, and the second address in the pair should match the destination. This
syntax:
any[/mask][:port]
matches any host or IP address with an optional subnet mask or a port. For example,
{ allow tcp any 1.2.3.4 }
allows TCP traffic between any host and the destination IP address 1.2.3.4.
{ allow tcp any/8 1.2.3.4 }
allows TCP traffic between any host within the subnet 255.0.0.0 and the destination IP
address 1.2.3.4.
{ allow tcp any/8:8000 1.2.3.4 }
allows TCP traffic between any host within the subnet 255.0.0.0 on port 8000 and the
destination IP address 1.2.3.4.
This syntax:
IP address[/mask][:port]
matches a specific IP address with an optional subnet mask or a port. For example,
{ allow tcp 1.1.1.1 1.2.3.4 }
allows TCP traffic between the host IP address 1.1.1.1 and the destination IP address
1.2.3.4.
{ allow tcp 1.1.1.1:22 1.2.3.4 }
allows TCP traffic between the host IP address 1.1.1.1 on port 22 and the destination IP
address 1.2.3.4.
F5 ACL with the IP protocol
ip
.
{ allow ip 51 any 1.2.3.4 }
F5 ACL with the TCP or UDP protocol
tcp
or udp)
.
{ allow tcp any 1.2.3.4 } { allow udp any 1.2.3.4 }
F5 ACL with the HTTP protocol
http
. The URL specification supports wildcards with glob
matching.
{ allow http any 1.2.3.4 https://www.siterequest.com/* } { allow http any 1.2.3.0/24 http://*.siterequest.com/* } { allow http any 1.2.3.0/24 http://*.siterequest.???/* }
Cisco ACL format
Specifies the subset of Cisco ACL syntax that Access Policy
Manager supports and provides examples.
Usage
On a RADIUS server, Access Policy Manager supports dynamic ACLs
that use the subset of the Cisco ACL format described here.Prefix
You must specify a prefix. For IPv4, use
ip:inacl#
where X
=X
is an integer used as a rule identifier. For IPv6, use
ipv6:inacl#
. X
=Keywords
These keywords are mapped with the F5 log-packet format:
log
and log-input
. These keywords are not
supported:
tos
, established
, time-range
, dynamic
,
and precedence
.Supported specification for Cisco ACL for IP protocol
{ip|ipv6}:inacl#X={deny|permit} {ip|ipv6}sourcesource-wildcarddestinationdestination-wildcard[log|log-input]
For example:
ipv6:inacl#10=permit
ipv6 any any log
Supported specification for Cisco ACL for TCP protocol
{ip|ipv6}:inacl#X={deny|permit}tcpsourcesource-wildcard[operator [port]]destinationdestination-wildcard[operator [port]][log|log-input]
For example:
ip:inacl#10=permit tcp any host 10.168.12.100 log
Supported specification for Cisco ACL for UDP protocol
{ip|ipv6}:inacl#X={deny|permit}udpsourcesource-wildcard[operator [port]]destinationdestination-wildcard[operator [port]][log|log-input]
For example:
ip:inacl#2=deny udp any any log





