Manual Chapter :
Protecting APIs with Access Policy Manager
Applies To:
Show Versions
BIG-IP APM
- 16.0.0
Protecting APIs with Access Policy Manager
Overview: Protecting
APIs with Access Policy Manager
If you want to manually configure API protection, this section describes the
tasks required. For a simpler automated setup procedure, you can instead follow the steps in the
API Protection template using . You can still customize the components when you use Guided Configuration.
The manual procedure for implementing API protection includes the following
tasks:
- Creating an API protection profile
- Adding servers, paths, and responses to the API protection profile
- Optionally, add a single sign-on configuration and log settings
- Optionally, configure rate limiting (seeRate Limiting API Requests)
- Associate the API protection profile with a virtual server
- If needed, edit the per-request policy automatically created for API protection
Creating an API protection profile using an OpenAPI Spec file
Before you set up API protection, make sure that
basic system configuration is complete including configuring network interfaces, routes,
VLANs, self IPs, DNS, and NTP. For this task, you need to have an OpenAPI 2.0 spec file
that describes the API.
An
API protection profile
specifies
the URI paths, servers, and default properties of the API. You can easily create it
using an OpenAPI spec file. You can develop custom responses to API calls, use a
relevant single sign-on configuration, and specify log settings. - On the Main tab, click .
- ClickCreate.
- ForName, type a name for the API protection profile.
- ForOpenAPI File, browse to select the file.
- If using HTTPS, select the name ofSSL Profile.
- ForDNS Resolver Mode, select whether to query DNS nameservers usingIPv4,IPv6, orIPv6 Prefer(both).
- ForDNS Resolver, select the name of the DNS resolver to use for converting web links.If you need to create a DNS resolver, click .
- If you are protecting a pool of API servers, selectIgnore Default Server.If you use this option, the default server is not used.
- ForAuthorization, you can add one or both of the following:
- HTTP Basic: Validates user logins that use HTTP or HTTPS protocol.
- OAuth 2.0:Validates user logins using OAuth 2.0 to issue tokens to the client after successfully authenticating the resource owner.
- ClickSave.Access Policy Manager creates an API protection profile and opens new tabs. The profile includes paths, servers, properties, and responses using the details specified in the OpenAPI spec file.
The API protection profile is created. In addition,
Access Policy Manager automatically develops a per-request policy that is associated
with the protection profile.
You can adjust the policy as needed using the
visual policy editor to access all of the features per-request policies provide. For
example, you can
- Add or delete paths
- Modify path information, such as changing the server
- Add or modify servers
- Add or modify responses
- Add or modify log settings
- Add or modify SSO configuration
If the API changes, you can manually make changes to the API
profile.
Creating an API protection profile without an OpenAPI Spec
file
Before you set up API protection, make sure that
basic system configuration is complete including configuring network interfaces, routes,
VLANs, self IPs, DNS, and NTP.
An
API protection profile
specifies the URI paths, servers, and default properties of the API. You can create it
manually by adding the necessary paths and servers. You can also develop custom
responses to API calls, use a relevant single sign-on configuration, and specify log
settings. - On the Main tab, click .
- ClickCreate.
- ForName, type a name for the API protection profile.
- If you are protecting a pool of API servers, selectIgnore Default Server.If selected, the default server is not used.
- ForAuthorization, you can add none, one, or both of the following:
- HTTP Basic: Validates user logins that use HTTP or HTTPS protocol. For HTTP Basic mode, the credential must be checked using an APMAAA server. You can use different AAA servers depending on any request criteria, geolocation, time, path, source IP, and so on.
- OAuth 2.0:Validates user logins using OAuth 2.0 to issue tokens to the client after successfully authenticating the resource owner. For OAuth mode, token validation (introspection) can be performed internally if JWKs are available and Java Web tokens used, OR externally against an externalOAuth AS.
When either option is selected, the per-request policy creates a macro namedOAuth Scope Check AuthZto handle the authentication. Despite the name, this subsession macro is usually used for handling both HTTP Basic and OAuth. - ClickSave.
Access Policy Manager creates an API protection
profile and opens new tabs where you can manually add paths, servers, and responses. In
addition, Access Policy Manager automatically develops a per-request policy that is
associated with the protection profile. You can adjust the policy as needed using the
visual policy editor to access all of the features per-request policies
provide.
You can manually develop the policy as needed. For
example, you can
- Add paths
- Add servers
- Create responses
- Specify log settings
- Add SSO configurations
If the API changes, locate the API profile in the list, then
click
Edit
to edit the associated per-request
policy.Adding servers to an API protection profile
You add servers to an API protection profile so you
need to have created a profile. Also, if the URL is HTTPS, you need to have a server SSL
profile (or use the default
serverssl
profile). Create SSL
profiles using .You create paths to define different endpoints to
access services provided by the API. If you used an OpenAPI Spec file, a server is
automatically created and listed on the Paths tab. If creating the protection profile
manually, you need to add the necessary API servers.
- On the Main tab, click .
- Click the name of the API protection profile to which you want to add servers.
- On the Paths tab, in the Servers section, clickCreate.The Server Properties section opens where you define the servers.
- ForName, type a name for the API server.
- ForURL, type the full path to the server. For example,https://store.order.io/v1.
- From theSSL Profilelist, select an SSL profile for initiating secure connections to the server, or use one of the defaults provided.
- From theServerlist, select the name of the API server.The server must be listed in the Servers section below.
- ClickActiveto make this path available.
- ClickAddto add the path to the profile.
- Add as many servers as are needed.
- In the Properties section, from theDefault Serverlist, select the name of the API server to use by default.
- FromDNS Resolver Mode, select whether the DNS resolver usesIPv4,IPv6, orIPv6 Prefer(both).
- FromDNS Resolver, select the DNS resolver the server uses to resolve addresses.
- ClickSave.
The servers are listed on the Paths tab of the API
protection profile.
Adding paths to an API protection profile
You add paths to an API protection profile so you
need to have created a profile. You also need to have specified one or more API servers
on the Paths tab.
You create paths to define different endpoints to
access services provided by the API. If you used an OpenAPI Spec file, the paths are
automatically imported and listed on the Paths tab. If creating the protection profile
manually, you need to add the paths to each of the API services. In either case, you can
adjust the paths as needed.
- On the Main tab, click .
- Click the name of the API protection profile to which you want to add paths.
- On the Paths tab, in the Paths section, clickCreate.The Path Properties section opens where you define the paths for the APIs being protected.
- ForURI, type the URI for the path you are creating starting with/. For example,/user/login.The URI pattern can use asterisk * wildcards to represent a segment of an API path; wildcards do not go beyond the path segment boundaries, and are not regular expressions. For example,/f5/util/*.
- From theMethodlist, select the method allowed for this API operation.The server must be listed in the Servers section below.
- From theServerlist, select the name of the API server for this type of request.The server must be listed in the Servers section below.
- ClickActiveto make this path available.
- ClickAddto add the path to the profile.
- Add as many paths as are required to support the API.
- ClickSave.
The paths are listed on the Paths tab of the API
protection profile. Note that deleting a path on the Paths tab does not delete the path
from the profile in the visual policy editor. So it is recommended that you edit the
paths in the editor.
Creating API responses
You create responses in an API protection profile so
you need to have created a profile.
You can create responses that indicate the results
of processing an API request. If you used an OpenAPI Spec file that includes responses
when creating the API protection profile, the responses are automatically imported and
listed on the Responses tab. If developing the protection profile manually, you need to
create the responses that you want to use. In either case, you can add, delete, or edit
the responses as needed.
- On the Main tab, click .
- Click the name of the API protection profile to which you want to add responses.
- On the Responses tab, clickCreate.The API Response Properties section opens where you define the responses for the APIs being protected.
- ForName, type a name for the response.
- ForStatus Code, type the 3-digit HTTP status code resulting from the attempt to satisfy the API request. For example,404or%{perflow.oauth.scope.status_code}.
- ForStatus, type a short textual description of the status code. For example,Invalid inputor%{perflow.oauth.scope.status_string}.
- If specifying headers for the response, forHeaders, click +, then type the name-value pairs for the header that appears in the API response.You can specify multiple response headers, if needed, to allow the server to provide additional information about the response.
- To add text for the response, type it inBody.The message in the body may include a file or resource.
- ClickAddto add the response to the profile.
- Add as many responses as are required to support the APIs.
- In the Properties section, forDefault Response, select the response to use by default.
- ClickSave.
The responses are listed on the Responses tab of the
API protection profile.
Specifying access control for API protection
You can specify access control including an
existing SSO configuration and log settings in an API protection profile. In addition,
you can edit the per request policy the system creates for API protection.
- On the Main tab, click .
- Click the name of the API protection profile you want to work on.
- Click theAccess Controltab.
- FromSSO Configuration, select the SSO configuration to use for API Protection.If using Single Sign-On with API protection, you can use only the following SSO authentication methods:
- HTTP Basic
- Kerberos
- OAuth Bearer
To add an SSO Configuration, go to . SeeAccess Policy Manager: Single Sign-On Concepts and Configuration. - FromLog Settings, select the format to use for logs, or use the default-log-setting.To configure custom log settings, refer toLogging and Reportingin theAccess Policy Manager: Network Access Guide.
- ClickSave.
- To see the per-request policy that was developed for API protection, clickEdit.The visual policy editor opens in a new tab and shows the policy contents. You can edit the policy as needed to customize it for API protection. SeeAccess Policy Manager: Visual Policy Editor.
The specified SSO configuration and log
settings are associated with the API protection profile.
Creating a virtual server for API protection
You create a virtual server to act as the
traffic destination address. Then you associate an API protection profile so that the
system can apply API protection to incoming API requests. The virtual server can have
only one protection profile assigned to it.
If you have already
created a virtual server, simply assign the API protection profile to it. No other
access policy can be associated with that virtual server.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- For theDestination Address/Masksetting, confirm that theHostbutton is selected, and type the IP address in CIDR format.The supported format is address/prefix, where the prefix length is in bits. For example, an IPv4 address/prefix is10.0.0.1or10.0.0.0/24, and an IPv6 address/prefix isffe1::0020/64or2001:ed8:77b5:2:10:10:100:42/64. When you use an IPv4 address without specifying a prefix, the BIG-IP system automatically uses a/32prefix.The IP address you type must be available and not in the loopback network.
- In theService Portfield, type80(for HTTP) or443(for HTTPS), or selectHTTPorHTTPSfrom the list.
- From theHTTP Profilelist, selecthttp.
- In the API protection area, from theAPI Protection Profilelist, select the protection profile that you configured earlier.
- Optional: Customize other settings as needed.
- ClickFinished.
The virtual server is created and the API
protection profile is associated with it. API requests directed through the virtual
server are protected by the profile.
Editing an API protection per-request policy
When you create an API protection profile, the
system automatically develops a per-request policy based on the settings you provided.
You can edit the per-request policy later to add or remove servers, paths, responses, or
to otherwise customize the policy for your networking environment.
- On the Main tab, click .
- ClickEditin the Per-Request Policy column for the API protection profile.The visual policy editor opens in a new tab and shows the policy contents. You can edit the policy as needed to customize it for API protection.
- To see how requests are classified using the paths and methods added in the API protection profile, locateClassify API Request (RCA), the Request Classification Agent. For example:
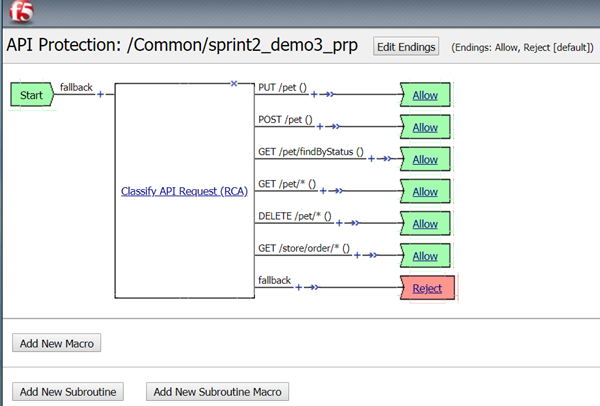
- ClickClassify API Request (RCA)to display the properties.
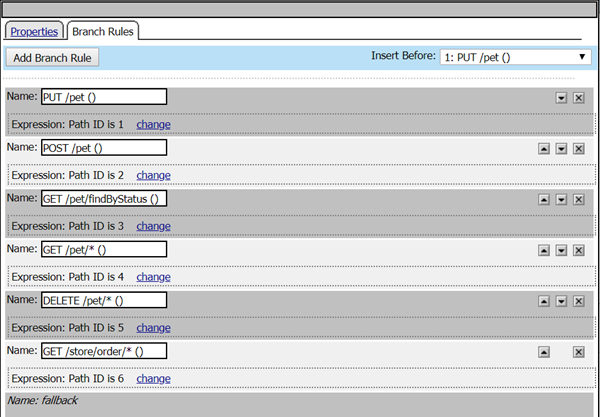 You can edit the paths here.Adding or modifying paths in the API protection profile adds them to the Classify API Request (RCA) in the visual policy editor. But deleting or modifying paths in the profile on the Paths tab does not delete or modify the path in the editor. So we recommend modifying or deleting paths in the editor.The Classify API Request object reads connection data and can steer the request to a specific policy branch. The branch can contain any logic you like, and generally it terminates in an Allow or Reject ending.
You can edit the paths here.Adding or modifying paths in the API protection profile adds them to the Classify API Request (RCA) in the visual policy editor. But deleting or modifying paths in the profile on the Paths tab does not delete or modify the path in the editor. So we recommend modifying or deleting paths in the editor.The Classify API Request object reads connection data and can steer the request to a specific policy branch. The branch can contain any logic you like, and generally it terminates in an Allow or Reject ending. - Click any other object to view and edit properties. Click the + between objects to see which options are available to add to the policy.
See
Access Policy
Manager: Visual Policy Editor
for details on editing policies.




