Manual Chapter :
Creating an Access Policy for Network Access
Applies To:
Show Versions
BIG-IP APM
- 16.0.1, 16.0.0
Creating an Access Policy for Network Access
About access
profiles
In the BIG-IP Access Policy Manager, an access profile is
the profile that you select in a virtual server definition to establish a secured
session. You can also configure an access profile to provide access control and security
features to a local traffic virtual server hosting web applications.
The access profile contains:
- Access policy timeout and concurrent user settings
- Accepted language and default language settings
- Single Sign-On information and domain cookie information for the session
- Customization settings for the access profile
- The access policy for the profile
About access policies
for network access
Define an access policy for network access in order to provide access
control conditions that you want users to satisfy, before they can connect to internal resources.
For a network access policy, you need to configure a minimum of a resource assign action that
assigns a network access resource.
Creating an access profile
You create an access profile to provide the access policy configuration for a
virtual server that establishes a secured session.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- ClickCreate.The New Profile screen opens.
- In theNamefield, type a unique name for the access profile.
- From theProfile Typelist, selectSSL-VPN.Additional settings display.
- From theProfile Scopelist, retain the default value or select another.
- Profile: Gives a user access only to resources that are behind the same access profile. This is the default value.
- Virtual Server: Gives a user access only to resources that are behind the same virtual server.
- Global: Gives a user access to resources behind any access profile that has global scope.
- Named: Gives an SSL Orchestrator user access to resources behind any access profile that has global scope.
- ForCustomization Type, selectModern.You can also useStandardbutModerncustomization is simpler and provides better compatibility for modern cross-platform and cross-device applications.
- To configure timeout and session settings, select theCustomcheck box.
- In theInactivity Timeoutfield, type the number of seconds that should pass before the access policy times out. Type0to set no timeout.If there is no activity (defined by theSession Update ThresholdandSession Update Windowsettings in the Network Access configuration) between the client and server within the specified threshold time, the system closes the current session.
- In theAccess Policy Timeoutfield, type the number of seconds that should pass before the access profile times out because of inactivity.Type0to set no timeout.
- In theMaximum Session Timeoutfield, type the maximum number of seconds the session can exist.Type0to set no timeout.
- In theMax Concurrent Usersfield, type the maximum number of users that can use this access profile at the same time.Type0to set no maximum.
- In theMax Sessions Per Userfield, type the maximum number of concurrent sessions that one user can start.Type0to set no maximum.Only a user in the administrator, application editor, manager, or resource administrator role has access to this field.
- In theMax In Progress Sessions Per Client IPfield, type the maximum number of concurrent sessions that can be in progress for a client IP address.When setting this value, take into account whether users will come from a NAT-ed or proxied client address and, if so, consider increasing the value accordingly. The default value is 128.Only a user in the administrator, application editor, manager, or resource administrator role has access to this field.F5 does not recommend setting this value to0(unlimited).
- Select theRestrict to Single Client IPcheck box to restrict the current session to a single IP address.This setting associates the session ID with the IP address.Only a user in the administrator, application editor, manager, or resource administrator role has access to this field.Upon a request to the session, if the IP address has changed the request is redirected to a logout page, the session ID is deleted, and a log entry is written to indicate that a session hijacking attempt was detected. If such a redirect is not possible, the request is denied and the same events occur.
- To redirect users attempting to access the root URI in a validated session with a webtop, selectRedirect client to webtop on root URI access.Users are redirected to the webtop in this case. Otherwise, requests are forwarded.
- To configure logout URIs, in the Configurations area, type each logout URI in theURIfield, and then clickAdd.
- In theLogout URI Timeoutfield, type the delay in seconds before logout occurs for the customized logout URIs defined in theLogout URI Includelist.
- To configure SSO:
- For users to log in to multiple domains using one SSO configuration, skip the settings in the SSO Across Authentication Domains (Single Domain mode) area. You can configure SSO for multiple domains only after you finish the initial access profile configuration.
- For users to log in to a single domain using an SSO configuration, configure settings in the SSO Across Authentication Domains (Single Domain mode) area, or you can configure SSO settings after you finish the initial access profile configuration.
- In theDomain Cookiefield, specify a domain cookie, if the application access control connection uses a cookie.
- In theCookie Optionssetting, specify whether to use a secure cookie.
- If the policy requires a secure cookie, select theSecurecheck box to add thesecurekeyword to the session cookie.
- If you are configuring an LTM access scenario that uses an HTTPS virtual server to authenticate the user and then sends the user to an existing HTTP virtual server to use applications, clear this check box.
- If the access policy requires a persistent cookie, in theCookie Optionssetting, select thePersistentcheck box.This sets cookies if the session does not have a webtop. When the session is first established, session cookies are not marked as persistent; but when the first response is sent to the client after the access policy completes successfully, the cookies are marked persistent. Persistent cookies are updated for the expiration timeout every 60 seconds. The timeout is equal to session inactivity timeout. If the session inactivity timeout is overwritten in the access policy, the overwritten value will be used to set the persistent cookie expiration.
- From theSSO Configurationlist, select an SSO configuration.
- In the Language Settings area, add and remove accepted languages, and set the default language.If no browser language matches one in the accepted languages list, the browser uses the default language.
- ClickFinished.
The access
profile displays in the Access Profiles List. Default-log-setting is assigned to the
access profile.
To add an SSO configuration for multiple domains, click
SSO / Auth
Domains
on the menu bar. To provide functionality with an access
profile, you must configure the access policy. The default access policy for a profile
denies all traffic and contains no actions. Click Edit
in the
Access Policy
column to edit the access policy. Access profile settings
You can configure the following settings in an access profile.
Setting | Value | Description and defaults |
|---|---|---|
Name | Text | Specifies the name of the access profile. |
Inactivity Timeout | Number of seconds, or 0 | Specifies the inactivity timeout for the connection. If there is no activity between
the client and server within the specified threshold time, the system closes the current
session. By default, the threshold is 0 , which specifies that as long as
a connection is established, the inactivity timeout is inactive. However, if an inactivity
timeout value is set, when server traffic exceeds the specified threshold, the inactivity
timeout is reset. |
Access Policy Timeout | Number of seconds, or 0 | Designed to keep malicious users from creating a denial-of-service (DoS) attack on
your server. The timeout requires that a user, who has followed through on a redirect, must
reach the webtop before the timeout expires. The default value is 300
seconds. |
Maximum Session Timeout | Number of seconds, or 0 | The maximum lifetime is from the time a session is created, to when the session
terminates. By default, it is set to 0 , which means no limit. When you
configure a maximum session timeout setting other than 0 , there is no
way to extend the session lifetime, and the user must log out and then log back in to the
server when the session expires. |
Max Concurrent Users | Number of users, or 0 | The number of sessions allowed at one time for this access profile. The default value
is 0 which specifies unlimited sessions. |
Max Sessions Per User | Number between 1 and 1000 , or
0 | Specifies the number of sessions for one user that can be active concurrently. The
default value is 0 , which specifies unlimited sessions. You can set a
limit from 1 -1000 . Values higher than
1000 cause the access profile to fail. Only users in the administrator,
application editor, manager, or resource administrator roles have access to this field.
|
Max In Progress Sessions Per Client IP | Number greater than 0 | Specifies the maximum number of sessions that can be in progress for a client IP
address. When setting this value, take into account whether users will come from a NAT-ed or
proxied client address and, if so, consider increasing the value accordingly. The default value
is 128 . Only users in the administrator, application editor, manager, or resource administrator
roles have access to this field. F5® does not recommend setting this value to
0 (unlimited). |
Restrict to Single Client IP | Selected or cleared | When selected, limits a session to a single IP address. Only users in the administrator,
application editor, manager, or resource administrator roles have access to this field.
|
Logout URI Include | One or more URIs | Specifies a list of URIs to include in the access profile to initiate session
logout. |
Logout URI Timeout | Logout delay URI in seconds | Specifies the time delay before the logout occurs, using the logout URIs defined in
the logout URI include list. |
SSO Authentication Across Domains (Single Domain mode) or SSO / Auth Domains:
Domain Cookie | A domain cookie | If you specify a domain cookie, then the line
domain= is added to the
specified_domain MRHsession cookie. |
SSO / Auth Domains: Domain Mode | Single Domain or Multiple
Domains | Select Single Domain to apply your SSO configuration to a
single domain. Select Multiple Domain to apply your SSO configuration
across multiple domains. This is useful in cases where you want to allow your users a single
Access Policy Manager (APM) login session and
apply it across multiple Local Traffic Manager or APM virtual servers,
front-ending different domains. All virtual servers must be on one
single BIG-IP system in order to apply SSO configurations across
multiple domains. |
SSO / Auth Domains: Primary Authentication URI | URI | The URI of your primary authentication server, for example
https://logon.siterequest.com . This is required if you use SSO across
multiple domains. You provide this URI so your users can access multiple back-end applications
from multiple domains and hosts without requiring them to re-enter their credentials, because
the user session is stored on the primary domain. |
Cookie Options: Secure | Enable or disable check box | Enabled, this setting specifies to add the secure keyword to
the session cookie. If you are configuring an application access control scenario where you are
using an HTTPS virtual server to authenticate the user, and then sending the user to an
existing HTTP virtual server to use applications, clear this check box. |
Cookie Options: Persistent | Enable or disable check box | Enabled, this setting specifies to set cookies if the session does not have a webtop.
When the session is first established, session cookies are not marked as persistent, but when
the first response is sent to the client after the access policy completes successfully, the
cookies are marked persistent. Persistent cookies are updated for the
expiration timeout every 60 seconds. The timeout is equal to the session inactivity timeout.
If the session inactivity timeout is overwritten in the access policy, the overwritten value
is used to set the persistent cookie expiration. |
Cookie Options: HTTP only | HttpOnly is an additional flag included in a Set-Cookie HTTP response header. Use the
HttpOnly flag when generating a cookie to help mitigate the risk of a client-side script
accessing the protected cookie, if the browser supports HttpOnly. When this option is enabled, only the web access management type of access (an LTM virtual
server with an access policy) is supported. | |
SSO Authentication Across Domains (Single Domain mode) or SSO / Auth Domains
SSO Configuration | Predefined SSO configuration | SSO configurations contain settings to configure single sign-on with an access
profile. Select the SSO configuration from the list that you want applied to your domain.
|
SSO / Auth Domains: Authentication Domains | Multiple | If you specify multiple domains, populate this area with hosts or domains. Each host
or domain can have a separate SSO config, and you can set persistent or secure cookies. Click
Add to add each host you configure. |
Accepted Languages | Language strings | Adds a built-in or customized language to the list of accepted languages. Accepted
languages can be customized separately and can present customized messages and screens to
users, if the user's default browser language is one of the accepted languages. Select a
language from the Factory Builtin Languages list and click the Move
button (<< ) to add it to the Accepted
Languages list. Select a language from the Additional
Languages list and click Add to add it to the
Accepted Languages list. |
Factory Builtin Languages | Languages in a predefined list | Lists the predefined languages on the Access Policy Manager system, which can be added
to the Accepted Languages list. Predefined languages include customized
messages and fields for common appearance items, as opposed to Additional
Languages , which must be separately customized. |
Additional Languages | Languages in a predefined list | Lists additional languages that can be added to the Accepted
Languages list, and customized on the Access Policy Manager system. These
languages are populated with English messages and fields and must be individually customized
using the Customization menu, as opposed to Factory Builtin Languages ,
which are already customized. |
Verify log settings for the access profile
Confirm that the correct log settings are selected
for the access profile to ensure that events are logged as you intend.
Log settings are configured in the area of the product. They enable and disable logging for access
system and URL request filtering events. Log settings also specify log publishers
that send log messages to specified destinations.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- Click the name of the access profile that you want to edit.The properties screen opens.
- On the menu bar, clickLogs.The access profile log settings display.
- Move log settings between theAvailableandSelectedlists.You can assign up to three log settings that enable access system logging to an access profile. You can assign additional log settings to an access profile provided that they enable logging for URl request logging only.Logging is disabled when theSelectedlist is empty.
- ClickUpdate.
An access profile is in effect when it is assigned to a virtual server.
Adding network
access to an access policy
Before you assign a network access resource to an access policy, you must:
- Create a network access resource.
- Create an access profile.
- Define a network access webtop or a full webtop.
When you assign a network access resource to an
access policy branch, a user who successfully completed the branch rule (which includes
that access policy item) starts a network access tunnel.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- Click the name of the access profile for which you want to edit the access policy.The properties screen opens for the profile you want to edit.
- On the menu bar, clickAccess Policy.
- In the General Properties area, click theEdit Access Policy for Profilelink.profile_nameThe visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- Select one of the following resource assignment actions and clickAdd.Resource AssignSelect theResource Assignaction to add a network access resource only.Resource Assigndoes not allow you to add a webtop or ACLs. If you want to add ACLs, a webtop, or webtop links after you add a Resource Assign action, you can add them with the individual actionsACL AssignandWebtop, Links and Sections Assign.Webtop sections are for use with a full webtop only.Advanced Resource AssignSelect theAdvanced Resource Assignaction to add network access resources, and optionally add a webtop, webtop links, webtop sections, and one or more ACLs.
- Select the resource or resources to add.
- If you added anAdvanced Resource Assignaction, on the Resource Assignment screen, clickAdd New Entry, then clickAdd/Delete, and select and add resources from the tabs, then clickUpdate.
- If you added aResource Assignaction, next to Network Access Resources, clickAdd/Delete.
If you add a full webtop and multiple network access resources, Auto launch can be enabled for only one network access resource. (With Auto launch enabled, a network access resource starts automatically when the user reaches the webtop.) - ClickSave.
- ClickApply Access Policyto save your configuration.
A network access tunnel is assigned to the access policy. You may also assign a network
access or full webtop. On the full webtop, users can click the link for a network access
resource to start the network access tunnel, or a network access tunnel (that is
configured with Auto launch enabled) can start automatically.
After you complete the access policy, you must
define a connectivity profile. In the virtual server definition, you must select the
access policy and connectivity profile.
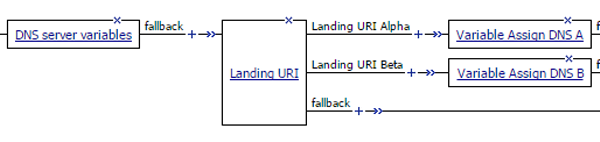
Overview: Assigning a DNS server dynamically for network access
When you configure DNS servers for a network access resource, you must specify IP addresses.
You do not have the option to enter a session variable instead. You can still assign a DNS server
dynamically to a network access tunnel if you do so from the access policy using the Variable
Assign agent.
About maximum
expression size for visual policy editor
The maximum size for an expression in the visual policy editor is 64 KB. The
visual policy editor cannot save an expression that exceeds this limit.
Assigning DNS servers dynamically to a network access
tunnel
Before you begin, you need to have a network
access configuration, including an access policy. Open the access policy for editing.
You require that DNS name servers be assigned
dynamically to a network access tunnel. (For example, you might want to assign DNS name
servers based on the landing URI.)
- On a policy branch, click the(+)icon to add an item to the policy.A popup screen displays actions on tabs, such as General Purpose and Authentication, and provides a search field.
- Typevarin the search field, selectVariable Assignfrom the results list, and then clickAdd Item.The Variable Assign properties screen opens.
- Assign the addresses of the DNS name servers to custom variables so that they are available for assignment later in the policy.You can create custom variables for multiple DNS name servers.
- ClickAdd new entry.Anemptyentry appears in the Assignment table.
- Click thechangelink next to the empty entry.A dialog box opens, where you can enter a variable and an expression.
- From the left-side list, retainCustom Variable(the default), and type a variable name.For example, typesession.custom.tunnel-dns-server.A
- From the right-side list, selectText, and type the IP address for the DNS name server.
- ClickFinished.The popup screen closes.
- To assign custom variables for additional DNS name servers, repeat the previous substeps.
- ClickSave.The properties screen closes. The policy displays.
- Insert an additional Variable Assign action into the access policy at the point where the policy logic dictates the assignment of a particular DNS name server to a network access tunnel.After you insert the Variable Assign action, a popup properties screen displays.
- On the popup properties screen, create an entry to assign DNS name servers (stored in a previously created custom session variables) for the Network Access tunnel resource.
- ClickAdd new entry.Anemptyentry appears in the Assignment table.
- Click thechangelink next to the empty entry.A dialog box opens, where you can enter a variable and an expression.
- From the left-side list, retainCustom Variable(the default), and type this variable name:config.connectivity_resource_network_access.na1.dnsYou must replacena1with the name of the network access resource that you have assigned to the access policy.
- From the right-side list, retainCustom Expression(the default), and type this expression:expr{ "<dns_primary>[mcgetsession.custom.tunnel-dns-serverA]</dns_primary><dns_secondary>[mcgetsession.custom.tunnel-dns-serverB]</dns_secondary>" }You must replacesession.custom.tunnel-dns-serverAandsession.custom.tunnel-dns-serverBwith the names you used for the custom variables that you created previously.Using the <dns> tag to enclose <dns_primary> and <dns_secondary> tags is optional and remains syntactically valid :{ "<dns><dns_primary>...</dns_secondary></dns>" }.
- ClickFinished.The popup screen closes.
- ClickSave.The properties screen closes and the policy displays.
You added Variable Assign items to specify DNS
name servers and to assign them dynamically.