Manual Chapter :
Ephemeral authentication workflow
Applies To:
Show Versions
BIG-IP APM
- 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0
Ephemeral authentication workflow
Here is an example of how ephemeral authentication works if you choose to
have the BIG-IP system authenticate users using RADIUS and/or LDAP with WebSSH.
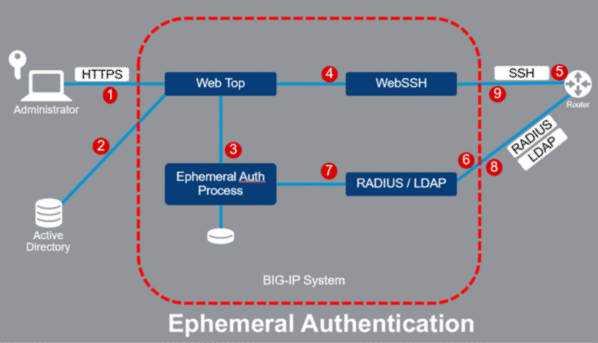
- User logs into the APM virtual server using a Smartcard or other credential. (The APM virtual server is the one that acts as the Ephemeral Authentication server on which the APM access profile/policy is configured.)
- The APM access policy checks provided credentials and retrieves AD/LDAP group membership information and returns a webtop showing backend resources.
- When the user clicks on a resource, APM generates an ephemeral password, and saves the username and password.
- Using SSO, APM signs the user on to the WebSSH virtual server with their ephemeral authentication credentials. At this point, portal access can be used instead.
- WebSSH makes an SSH connection (or HTTPS) to the router/server still using the ephemeral authentication credentials.
- The router sends an authentication request to the RADIUS or LDAP virtual server.
- The RADIUS or LDAP virtual server verifies the ephemeral password.
- The RADIUS or LDAP virtual server returns a Successful or Failure response.
- The SSH (or HTTPS) session is established or denied.





