Manual Chapter :
Visual Policy Editor
Concepts
Applies To:
Show Versions
BIG-IP APM
- 16.0.1, 16.0.0
Visual Policy Editor
Concepts
About the visual policy editor
The visual policy editor is a screen on which to configure a per-session policy (also known
as an access policy) or a per-request policy using visual elements.
Visual policy editor conventions
This table provides a visual dictionary for the visual policy editor.
Visual element | Element type | Description |
|---|---|---|
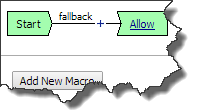 | Initial access policy and initial per-request policy | When an access profile is created, usually an initial access policy is also
created. A per-request policy starts with similar initial elements. |
 | Start | Every access policy and per-request policy contains a start. |
 | Branch | A branch connects an action to another action or to an ending. |
 | Add an action | Clicking this icon causes a screen to open with available actions for selection. |
 | Action | Clicking the name of an action, such as Logon Page , opens
a screen with properties and rules for the action. Clicking the
x deletes the action from the access policy. |
 | Action that requires some configuration | The red asterisk indicates that some properties must be configured. Clicking the
name opens a screen with properties for the action. |
 | Ending | Each branch has an ending. An access policy includes Allow
or Deny endings. A per-request policy includes
Allow or Reject endings. |
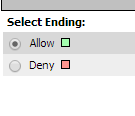
| Configure ending | Clicking the name of an ending opens a popup screen. |
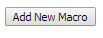 | Add a macro for use in the access policy | Opens a screen for macro template selection. After addition, the macro is
available for configuration and for use as an action item. |
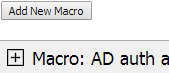 | Macro added for use | Added macros display under the access policy. Clicking the plus ( + ) sign expands
the macro for configuration of the actions in it. |
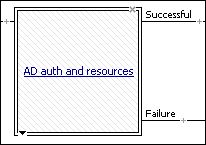 | Macrocall in an access policy | Clicking the macrocall name expands the macro in the area below the access
policy. |
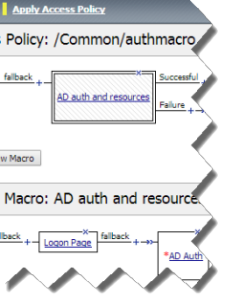 | Apply Access Policy | Clicking it commits changes. The visual policy editor displays this link when any
changes remain uncommitted. |
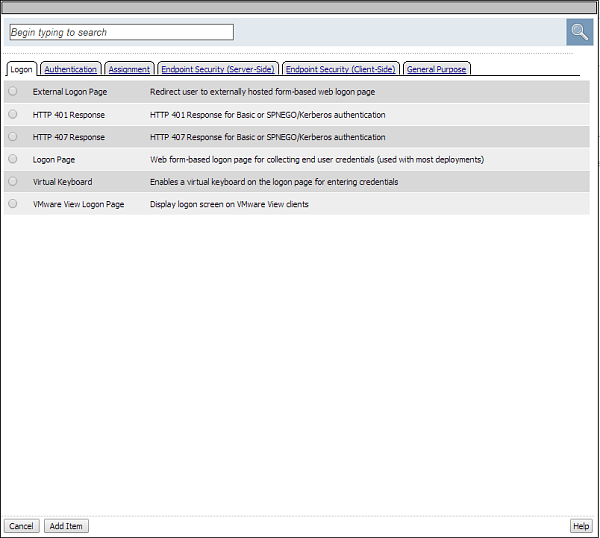
About actions on
the add item screen
The actions that are available on any given tab of the add item
screen depend on the access profile type, such as LTM-APM (for web access) or
SSL-VPN (for remote access), and so on. Only actions that are appropriate for the
access profile type will display.
Add action item screen
About macros and
macrocalls
A
macro
is a collection of access
policy actions that provide common access policy functions. For example, AD auth and resources
is a preconfigured macro template. It supplies a logon page, an Active Directory
authentication action, and a resource assignment action. The properties and rules for the
actions are configurable. After a macro is configured, it can be placed into the access policy by
adding a macrocall. A
macrocall
is an action that performs
the functions defined in a macro.A macro contains actions and terminals and can include macrocalls.
You cannot use subroutines in macros within per-request policies.
- Access policy actions
- Any available action or series of actions.
- Macrocalls
- Calls to other macros (nested macros).
- Terminals
- An endpoint in a macro. Default terminals areSuccessfulandFailure. Terminals are configurable and can be added and deleted.
Terminals defined in the macro display as the branches that follow the
macrocall after it has been added to the access policy.
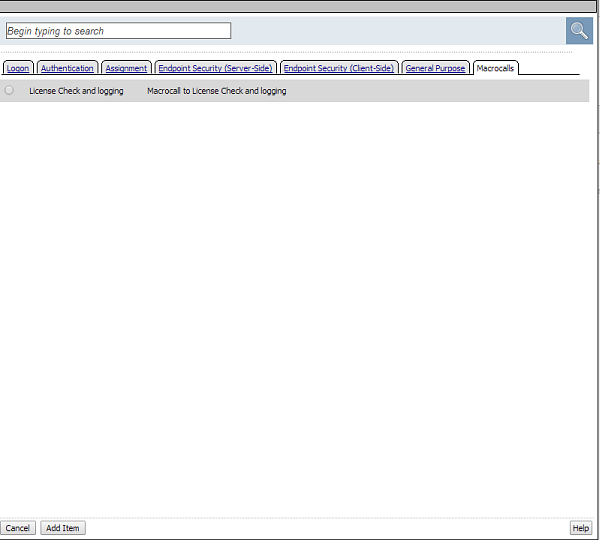
About macrocalls
on the add item screen
The Macrocalls tab displays when one or more macros has been added
for use in the access policy. When adding an access policy item to a macro, the
Macrocalls tab displays unless adding a macrocall would create a misconfiguration,
such as causing a macro loop or causing a series of macrocalls to exceed a depth
of three.
Macrocalls can be added to any access policy. Macrocalls cannot be shared across
access policies.
Macrocalls tab on the add item screen
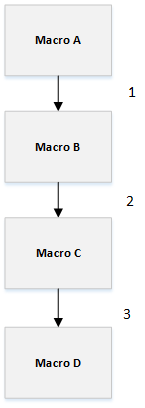
About maximum depth
for nested macros in an access policy
In an access policy, a macro can make a macrocall to another macro until
up to three macros have been called in series.
The maximum
depth of macrocalls
About access policy endings
An ending provides a result for an access policy branch. An ending for an access policy branch can be one
of three types.
- Allow
- Starts the SSL VPN session and loads assigned resources and a webtop, if assigned, for the user. Typically, you assign this when the user passes specific checks.
- Deny
- Disallows the SSL VPN session and shows the user an access denied web page. Typically, you assign this when the user does not have access to resources, or fails authentication. Alternatively after a session starts, shows a URL filter denied web page after a per-request policy rejects a request for a URL.
- Redirect
- Redirects the client to the URL specified in the ending configuration. You can define a redirect URL for each redirect ending. Typically, you can assign a redirect when the user requires remediation or a separate resource. For example, a user who fails the antivirus check because virus definitions are out of date can be redirected to the software manufacturer's site to get an antivirus update.
About maximum
expression size for visual policy editor
The maximum size for an expression in the visual policy editor is 64 KB. The
visual policy editor cannot save an expression that exceeds this limit.
About per-session and
per-request policies
Access Policy Manager (APM) provides two types of policies.
- Per-session policy
- The per-session policy runs when a client initiates a session. (A per-session policy is also known as an access policy.) Depending on the actions you include in the access policy, it can authenticate the user and perform other actions that populate session variables with data for use throughout the session.
- Per-request policy
- After a session starts, aper-request policyruns each time the client makes an HTTP or HTTPS request. Because of this behavior, a per-request policy is particularly useful in the context of a Zero Trust scenario, where the client requires re-verification on every request. A per-request policy can include a subroutine, which starts a subsession. Multiple subsessions can exist at one time.You cannot use subroutines in macros within per-request policies.
You can associate one access policy and one per-request policy with a virtual
server.
About per-request policies and the Apply Access Policy link
The Apply Access Policy link has no effect on a per-request policy. Conversely, updates made to
a per-request policy do not affect the state of the Apply Access Policy link.
About per-request policies and nested macros
Access Policy Manager® (APM®) supports calling a
macro from a per-request policy and calling a subroutine macro from a per-request policy
subroutine. However, APM does not support calling any type of macro from a per-request policy
macro or from a per-request policy subroutine macro.
About per-request policy subroutines
A per-request policy
subroutine
is a
collection of actions. What distinguishes a subroutine from other collections of actions (such as
macros), is that a subroutine starts a subsession that, for its duration, controls user access to
specified resources. If a subroutine has an established subsession, subroutine execution is
skipped. A subroutine is therefore useful for cases that require user interaction (such as a
confirmation dialog or a step-up authentication), since it allows skipping that interaction in a
subsequent access.You cannot use subroutines in macros within per-request policies.
Subroutine properties specify subsession timeout values, maximum macro loop
count, and gating criteria. You can reauthenticate, check for changes on the client, or take
other actions based on timeouts or gating criteria.
About subsessions
A
subsession
starts when a subroutine runs
and continues until reaching the maximum lifetime specified in the subroutine properties,
or until the session terminates. A subsession populates subsession variables that are
available for the duration of the subsession. Subsession variables and events that occur
during a subsession are logged. Multiple subsessions can exist at the same time. The maximum number of subsessions allowed
varies across platforms. The total number of subsessions is limited by the session limits
in APM (128 * max sessions). Creating a subsession does not count against the license
limit.
Additional resources and documentation for BIG-IP Access Policy Manager
You can access all of the BIG-IP system documentation from
the AskF5 Knowledge Base located at
https://support.f5.com/
.Document |
Description |
|---|---|
BIG-IP
Access Policy Manager: Application Access |
This guide contains information for an administrator to configure application
tunnels for secure, application-level TCP/IP connections from the client to the
network. |
BIG-IP Access Policy Manager:
Authentication Essentials |
This guide contains information to help an administrator understand authentication concepts, such as AAA server, SSL certificate, local user database, and so on. |
BIG-IP Access Policy Manager:
Authentication Methods |
This guide contains information describes different types of authentication, including Active Directory, LDAP and LDAPS, RSA SecurID, RADIUS, OCSP, CRLDP, Certificate, TACACS+, and so on. |
BIG-IP Access Policy Manager:
OAuth Concepts and Configuration |
This guide describes OAuth concepts and explains how to configure the system to use OAuth authorization servers, resource servers, and other examples. |
BIG-IP Access Policy Manager:
SAML Configuration |
This guide introduces SAML concepts and provides several examples using APM as a SAML IdP, as a SAML service provider, and others. |
BIG-IP Access Policy Manager:
Single Sign-On Concepts and Configuration |
This guide describes how to configure different types of single sign-on methods, such as HTTP basic, HTTP forms-based, NTLMV1, NTLMV2, Kerberos, OAuth Bearer. |
BIG-IP
Access Policy Manager: Customization |
This guide provides information about using the APM customization tool to provide
users with a personalized experience for access policy screens, and errors. An
administrator can apply your organization's brand images and colors, change messages
and errors for local languages, and change the layout of user pages and screens.
|
BIG-IP
Access Policy Manager: Edge Client and Application
Configuration |
This guide contains information for an administrator to
configure the BIG-IP system for browser-based access with the web client as well as
for access using BIG-IP Edge Client and F5 Access Apps. It also includes information
about how to configure or obtain client packages and install them for BIG-IP Edge
Client for Windows, Mac, and Linux, and Edge Client command-line interface for Linux. |
BIG-IP
Access Policy Manager: Implementations |
This guide contains implementations for synchronizing access policies across
BIG-IP systems, hosting content on a BIG-IP system, maintaining OPSWAT libraries,
configuring dynamic ACLs, web access management, and configuring an access policy for
routing. |
BIG-IP
Access Policy Manager: Network Access |
This guide contains information for an administrator to configure APM Network
Access to provide secure access to corporate applications and data using a standard
web browser. |
BIG-IP
Access Policy Manager: Portal Access |
This guide contains information about how to configure APM Portal Access. In
Portal Access, APM communicates with back-end servers, rewrites links in application
web pages, and directs additional requests from clients back to APM. |
BIG-IP
Access Policy Manager: Secure Web Gateway |
This guide contains information to help an administrator configure Secure Web
Gateway (SWG) explicit or transparent forward proxy and apply URL categorization and
filtering to Internet traffic from your enterprise. |
BIG-IP
Access Policy Manager: Third-Party Integration |
This guide contains information about integrating third-party products with
Access Policy Manager (APM). It includes implementations for
integration with VMware Horizon View, Oracle Access Manager, Citrix Web Interface
site, and so on. |
BIG-IP
Access Policy Manager: Visual Policy Editor |
This guide contains information about how to use the visual policy editor to
configure access policies. |
Release notes |
Release notes contain information about the current software release, including a
list of associated documentation, a summary of new features, enhancements, fixes,
known issues, and available workarounds. |
KB articles |
Knowledge base articles are responses and resolutions to known issues, additional configuration instructions, and how-to information. |





