Manual Chapter :
Windows Registry Reference
Applies To:
Show Versions
BIG-IP APM
- 16.0.1, 16.0.0
Windows Registry Reference
Overview: Policy branching based on Windows Registry values
You can create access policy branches using the values of Windows Registry keys on the client.
You can use the GET operator in the Windows Registry action to fetch values from the client. To
ensure client security, you must first configure the Windows registry on each client to allow
trusted BIG-IP systems to fetch specific Windows Registry values. Without
client configuration, the GET operator fails.
Task summary
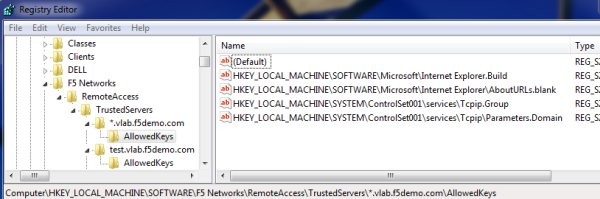
Registry screenshot: Allowed keys for a trusted server
Registry Allowed keys for a trusted server
Example: Allowed registry key value fetched
Windows Registry expression in the visual
policy editor
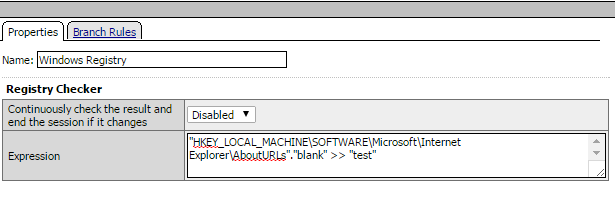
The expression uses the GET (>>) operator to fetch the value of the registry key,
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet
Explorer\AboutURLs"."blank"
, into the user-defined session variable
test
.Configuring clients
for Windows Registry GET operation
To ensure that only Access Policy Manager (APM)
can fetch a value from the Windows Registry on a client, you must create registry
entries on the client. The entries must specify the BIG-IP systems that are trusted
servers and the specific registry key values that each server is allowed to fetch.
Use
Microsoft Group Policy or any other client desktop management system to populate the
entries.
- For the trusted servers, create this registry location:HKEY_LOCAL_MACHINE\Software\F5 Networks\RemoteAccess\TrustedServers.
- Add subkeys that specify the trusted server locations.A subkey name can be a fixed server location, such aswww.siterequest.com, or a regular expression that begins with a wildcard, such as*.siterequest.com. The asterisk (*) is the only supported wildcard.When server names are defined with wildcards, the Windows Registry action selects the most specific server name. For example, for a client configured with these trusted servers: computer.subd.domain.com, *.subd.domain.com, and *.domain.com, Windows Registry prefers: computer.subd.domain.com over *.subd.domain.com and *.domain.comHere is an example subkey for a trusted server location:HKEY_LOCAL_MACHINE\Software\F5 Networks\RemoteAccess\TrustedServers\*.site1.com.Here is another example subkey:HKEY_LOCAL_MACHINE\Software\F5 Networks\RemoteAccess\TrustedServers\www.site2.com.
- For each trusted server location, add this subkey:AllowedKeys.Here is an example:HKEY_LOCAL_MACHINE\Software\F5 Networks\RemoteAccess\TrustedServers\*site1.com\AllowedKeysHere is another example:HKEY_LOCAL_MACHINE\Software\F5 Networks\RemoteAccess\TrustedServers\www.site2.com\AllowedKeys
- Add values to each AllowedKeys subkey; populate each value with a specific registry key value that the server is allowed to fetch.The format for the value isregistry path.value.When specifying values, bear in mind that the Windows Registry action supports fetching only these Windows Registry data types: REG_DWORD, REG_SZ, and REG_MULTI_SZ.Here are two example values:HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Tcpip\Parameters.DomainIf the example values exist for theHKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Tcpip.GroupHKEY_LOCAL_MACHINE\Software\F5 Networks\RemoteAccess\TrustedServers\*.site1.com\AllowedKeyskey, it implies that any server that matches *.site1.com can fetch the valueDomain, from this registry locationHKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Tcpip\Parameters.Domainand can fetch the valueGroupfrom this registry locationHKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Tcpip.Group.
Viewing trusted server registry keys and subkeys on a client
You can verify the trusted servers and allowed key values on a client by running a
diagnostic report using BIG-IP
Edge Client. If present on the client, the
HKEY_LOCAL_MACHINE\SOFTWARE\F5
Networks\RemoteAccess\TrustedServers
Windows Registry key and its subkeys
are included in the report.As an alternative, you can use the Client
Troubleshooting Utility to verify trusted server and allowed key values.
- Open the BIG-IP Edge Client user interface.On a client with aStartbutton, you can typeBIG-IPin the search field and, in the results, clickBIG-IP Edge Client.
- Click theView Detailsbutton.The Details popup screen displays.
- Click theDiagnostics Reportbutton.A Save As popup screen opens.
- Select a location, specify a file name, and clickSave.A Collecting data popup screen remains open until the report completes.
- Navigate to the location with the downloaded file, extract the files to a folder, and click the HTML file in the folder.The F5 Report displays in a browser screen.
- Scroll down to theMS Remote Access Diagnosticsection of the table of contents.
- Look for a link that includes the wordTrustedServers.If you do not find such a link, then trusted servers and allowed keys are not configured on the client.The link in the table of contents should include this path:HKLM\Software\F5 Networks\RemoteAccess\TrustedServers.
- If the link exists, click it to view the subkeys and values configured on the client.
Fetching the value of a Windows Registry key from a client
Before this access policy can run successfully, clients must be configured to allow
trusted BIG-IP systems to fetch specific Windows Registry key
values.
You can use a Windows Registry action to fetch values from the Windows Registry on
the client.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen opens.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- On a policy branch, click the(+)icon to add an item to the policy.A popup screen displays actions on tabs, such as General Purpose and Authentication, and provides a search field.
- Click the Endpoint Security (Client-Side) tab.
- SelectWindows Registryand clickAdd Item.A popup properties screen opens.
- In theExpressionfield, type an expression that includes these items: the name of a Windows Registry key value, the >> operator, and a name for use as a variable.The Windows Registry key value used in the expression must match a registry key value that the client allows a trusted server to fetch.Here is an example expression:"HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Tcpip\Parameters"."Domain" >> "variable_name"whereHKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Tcpip\Parametersis the registry key,Domainis the name of the value to fetch and>>is the GET operator. If GET is successful, thenvariable_nameis used to store the value in a session variable formatted like this:session.windows_check_registry.last.data.variable_name.
- ClickFinished.The popup screen closes.
- ClickSave.The properties screen closes and the policy displays.
You added an action to fetch a registry key value from the Windows Registry on the
client. This is not a complete access policy.
Click the
Apply Access
Policy
link to apply and activate your changes to this access policy.
To ensure that logging is configured to meet your requirements, verify the log settings for the access profile.





