Manual Chapter :
Configuring BIG-IP DNS on a Network with Multiple Route Domains
Applies To:
Show Versions
BIG-IP LTM
- 21.0.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0
BIG-IP DNS
- 21.0.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0
Configuring BIG-IP DNS on a Network with Multiple Route Domains
Overview: How do I
deploy BIG-IP DNS on a network with multiple route domains?
You can deploy DNS (formerly GTM) on a network where BIG-IP Local Traffic
Manager (LTM) systems are configured with
multiple route domains and overlapping IP addresses.
On a BIG-IP system that includes both Local Traffic Manager LTM) and Global Traffic
Manager (now BIG-IP DNS), all IP addresses that BIG-IP DNS
references (virtual IP addresses, link addresses, and so on) must be associated with route domain
0
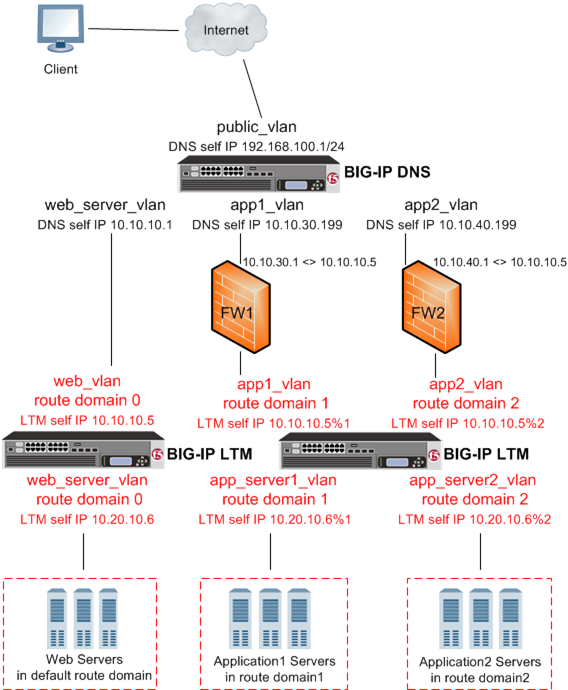
.The following figure shows BIG-IP DNS deployed in a network with multiple
BIG-IP LTM systems, one configured with the default route domain (zero), and
one configured with two additional route domains. BIG-IP DNS can monitor the Application1 and
Application2 servers that have overlapping IP addresses and reside in different route domains.
The firewalls perform the required address translation between the BIG-IP DNS and BIG-IP LTM
addresses; you must configure the firewalls to segment traffic and avoid improperly routing
packets between route domain 1 and route domain 2.
BIG-IP DNS deployed
on a network with multiple route domains
Before BIG-IP DNS can gather
status and statistics for the virtual servers hosted on BIG-IP LTM systems that are configured with route domains, you must configure
the following on each BIG-IP LTM that handles traffic for route domains:
- VLANs through which traffic for your route domains passes
- Route domains that represent each network segment
- Self IP addresses that represent the address spaces of the route domains
Additionally, configure a BIG-IP DNS server object on BIG-IP DNS to
represent each LTM system device.
Creating VLANs for a route domain on BIG-IP LTM
Create two VLANs on BIG-IP LTM through which
traffic can pass to a route domain.
- On the Main tab, click .The VLAN List screen opens.
- ClickCreate.The New VLAN screen opens.
- In theNamefield, typeexternal.
- In theTagfield, type a numeric tag, between 1-4094, for the VLAN, or leave the field blank if you want the BIG-IP system to automatically assign a VLAN tag.The VLAN tag identifies the traffic from hosts in the associated VLAN.
- If you want to use Q-in-Q (double) tagging, use theCustomer Tagsetting to perform the following two steps. If you do not see theCustomer Tagsetting, your hardware platform does not support Q-in-Q tagging and you can skip this step.
- From theCustomer Taglist, selectSpecify.
- Type a numeric tag, from 1-4094, for the VLAN.
The customer tag specifies the inner tag of any frame passing through the VLAN. - For theInterfacessetting:
- From theInterfacelist, select an interface number or trunk name.
- From theTagginglist, selectTaggedorUntagged.SelectTaggedwhen you want traffic for that interface to be tagged with a VLAN ID.
- If you specified a numeric value for theCustomer Tagsetting and from theTagginglist you selectedTagged, then from theTag Modelist, select a value.
- ClickAdd.
- Repeat these steps for each interface or trunk that you want to assign to the VLAN.
- If you want the system to verify that the return route to an initial packet is the same VLAN from which the packet originated, select theSource Checkcheck box.
- For theHardware SYN Cookiesetting, select or clear the check box.When you enable this setting, the BIG-IP system triggers hardware SYN cookie protection for this VLAN.Enabling this setting causes additional settings to appear. These settings appear on specific BIG-IP platforms only.
- For theSyncache Thresholdsetting, retain the default value or change it to suit your needs.TheSyncache Thresholdvalue represents the number of outstanding SYN flood packets on the VLAN that will trigger the hardware SYN cookie protection feature.When theHardware SYN Cookiesetting is enabled, the BIG-IP system triggers SYN cookie protection in either of these cases, whichever occurs first:
- The number of TCP half-open connections defined in the LTM settingGlobal SYN Check Thresholdis reached.
- The number of SYN flood packets defined in thisSyncache Thresholdsetting is reached.
- For theSYN Flood Rate Limitsetting, retain the default value or change it to suit your needs.TheSYN Flood Rate Limitvalue represents the maximum number of SYN flood packets per second received on this VLAN before the BIG-IP system triggers hardware SYN cookie protection for the VLAN.
- ClickFinished.The screen refreshes, and it displays the new VLAN in the list.
Repeat this procedure, but in Step 3, name the VLAN
internal
.Creating a route domain on BIG-IP LTM
Ensure that VLANs exist on BIG-IP
LTM, before you create a route domain.
You can create a route domain on a BIG-IP system to segment (isolate)
network traffic on your network.
- On the Main tab, click .The Route Domain List screen opens.
- ClickCreate.The New Route Domain screen opens.
- In theIDfield, type an ID number for the route domain.This ID must be unique on the BIG-IP system; that is, no other route domain on the system can have this ID.An example of a route domain ID is1.
- In theDescriptionfield, type a description of the route domain.For example:This route domain applies to application traffic for Customer A.
- For theStrict Isolationsetting, select theEnabledcheck box to restrict traffic in this route domain from crossing into another route domain.
- For theParent Namesetting, retain the default value.
- For theVLANssetting, move theexternalandinternalVLANs from theAvailablelist, to theMemberslist.Configuring this setting ensures that the BIG-IP system immediately associates any self IP addresses pertaining to the selected VLANs with this route domain.
- ClickFinished.The system displays a list of route domains on the BIG-IP system.
Create additional route domains based on your network configuration.
Creating a self IP address for a route domain on BIG-IP LTM
Ensure that VLANs exist on BIG-IPLTM,
before you begin creating a self IP address for a route domain.
Create a self IP address on the BIG-IP system that resides in the address space of
the route domain.
- On the Main tab, click .
- ClickCreate.The New Self IP screen opens.
- In theNamefield, type a unique name for the self IP address.
- In theIP Addressfield, type an IP address.This IP address must represent a self IP address in a route domain. Use the formatx.x.x.x%n, wherenis the route domain ID, for example, 10.1.1.1%1.The system accepts IPv4 and IPv6 addresses.
- In theNetmaskfield, type the network mask for the specified IP address.For example, you can type255.255.255.0.
- From theVLAN/Tunnellist, select the VLAN that you assigned to the route domain that contains this self IP address.
- From thePort Lockdownlist, selectAllow Default.
- ClickFinished.The screen refreshes, and displays the new self IP address.
Create additional self IP addresses based on your network configuration.
Defining a server for a route domain on BIG-IP DNS
Ensure that at least one data center exists in the configuration.
On a BIG-IP
DNS system, define a server that represents the route domain.
- On the Main tab, click .The Server List screen opens.
- ClickCreate.The New Server screen opens.
- In theNamefield, type a name for the server.Server names are limited to 63 characters.
- From theProductlist, selectBIG-IP System.
- From theData Centerlist, select the data center where the server resides.
- From theProber Preferencelist, select the preferred type of prober(s).Inherit From Data CenterBy default, a server inherits the prober preference selection assigned to the data center in which the server resides.Inside Data CenterA server selects the probers from inside the data center where the server resides.Outside Data CenterA server selects the probers from outside the data center where the server resides.Specific Prober PoolSelect one of the Prober pools from the drop-down list. When assigning the Prober pool at the server level.Note:Prober pools are not used by the bigip monitor.
- From theProber Fallbacklist, select the type of prober(s) to be used if insufficient numbers of the preferred type are available.Inherit From Data CenterBy default, a server inherits the prober fallback selection assigned to the data center in which the server resides.Any AvailableFor selecting any available prober.Inside Data CenterA server selects probers from inside the data center where the server resides.Outside Data CenterA server selects probers from outside the data center where the server resides.NoneNo fallback probers are selected. Prober fallback is disabled.Specific Prober PoolSelect one of the probers from the list When you want to assign a prober pool at the server level.
- In the BIG-IP System devices area, add the self IP address that you assigned to the VLAN that you assigned to the route domain.Do not include the route domain ID in this IP address. Use the format x.x.x.x, for example, 10.10.10.1.
- In theHealth Monitorssetting, assign thebigipmonitor to the server by moving it from theAvailablelist to theSelectedlist.
- From theAvailability Requirementslist, select an option and enter any required values.All Health MonitorsBy default, specifies that all of the selected health monitors must be successful before the server is considered up (available).At LeastThe minimum number of selected health monitors that must be successful before the server is considered up.RequireThe minimum number of successful probes required from the total number of probers requested.
- From theVirtual Server Discoverylist, select how you want virtual servers to be added to the system.Virtual server discovery is supported when you have only one route domain.DisabledUse this option when you plan to manually add virtual servers to the system, or if your network uses multiple route domains. This is the default value.EnabledThe system automatically adds virtual servers using the discovery feature.Enabled (No Delete)The system uses the discovery feature and does not delete any virtual servers that already exist.
- ClickFinished.The Server List screen opens displaying the new server in the list.
Running the big3d_install script
Determine the self IP addresses of the BIG-IP systems that you want
to upgrade with the latest
big3d
agent. Ensure that port
22
is open on these systems.Run the
big3d_install
script on the DNS system
you are adding to your network. This upgrades the big3d
agents on the other BIG-IP
systems on your network. It also instructs these systems to authenticate with the other BIG-IP
systems through the exchange of SSL certificates. For additional information about running the
script, see K13312 on AskF5.com (www.askf5.com
).You must perform this task from the command-line
interface.
All target BIG-IP systems
must be running the same or an older version of BIG-IP software.
- Log in asrootto the BIG-IP DNS system you are adding to your network.
- Run this command to accesstmsh:tmsh
- Run this command to run thebig3d_installscript:run gtm big3d_install<IP_addresses_of_target BIG-IP_systems>The script instructs BIG-IP DNS to connect to each specified BIG-IP system.
- If prompted, enter therootpassword for each system.
The SSL certificates are exchanged, authorizing communications between the systems. The
big3d
agent on each system is upgraded to the same version as is installed on
the BIG-IP DNS system from which you ran the script.Running the bigip_add script
You must determine the self IP addresses of
the LTM systems that you want to communicate with BIG-IP DNS before you start this task.
You run the
bigip_add
script on the BIG-IP DNS
system you are installing on a network that includes other BIG-IP systems
of the same version. This script exchanges SSL certificates so that each system is authorized to
communicate with the other. For additional information about running the script, see K13312 on
AskF5.com (www.askf5.com
).The BIG-IP DNS and BIG-IP LTM systems must have
TCP port
22
open for the script to work. You must perform this task from
the command-line interface.- Log in asrootto the BIG-IP DNS system you are installing on your network.
- Run this command to accesstmsh.tmsh
- Run this command to run thebigip_addutility:run gtm bigip_add<IP_addresses_of_BIG-IP_LTM_systems>The utility exchanges SSL certificates so that each system is authorized to communicate with the other.
Implementation result
You now have an implementation in which BIG-IP DNS monitors BIG-IP LTM virtual servers on
the various route domains in your network.





