Manual Chapter :
On-Demand Certificate Authentication
Applies To:
Show Versions
BIG-IP APM
- 21.0.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0
On-Demand Certificate Authentication
Overview: Requesting and validating an SSL certificate on demand
Typically, when a client makes an HTTPS request, an SSL handshake request occurs at the start of an SSL session. You can configure a client SSL profile to skip the initial SSL handshake and add the On-Demand certificate authentication agent to the access policy to re-negotiate the SSL connection later. Access Policy Manager can perform the certificate request and validation task that is normally performed by the target server, on demand.
Use the agent when you want to request and validate a certificate only after a user has already completed some other steps (logged on, gone through an authentication process, or anything else you require). Wherever you place the On-Demand authentication action in your access policy, it performs an SSL re-handshake.
You might want to use the On-Demand certificate authentication agent, for example, if all employees must gain access to the network before only a few employees can gain access to servers with sensitive information.
When configuring On-Demand certification authentication in a
per-request policy
, avoid having any other agent before the On-Demand Cert Auth agent if the client SSL profile on the virtual server has the Client Certificate
field set to ignore
. This configuration makes the per-request policy re-execute the subroutine when it reaches the On-Demand Cert Auth agent. This can cause the per-request policy to go to the unexpected branch on each agent located before On-Demand Cert Auth agent. Certificate validation in BIG-IP
Certificate validation in BIG-IP
This session provides the list of checks performed by BIG-IP to validate the certificates.
- Certificate depth should not be more than the configured valueBIG-IP validates the certificate chain (root and intermediate certificate) based on the value specified in theCertificate Chain Traversal Depthfield sent by the client or server. By default, the value is set to 9. If the certificate chain depth is more than the specified value, then certificate validation fails with the “certificate chain too long” error message
- Certificate trusted chainBIG-IP validates the certificate chain of trust with the respective issuer for each certificate in the chain.
- Certificate Revocation List (CRL)The CRL validates the certificates from the chain, statically or dynamically, based on the configurations.
- Certificate extensionsBIG-IP requires a CA certificate to haveBasic ConstrainsandCA: Trueattributes.
- Certificate duration validityThe date and time mentioned in theNot BeforeandNot Afterfields for a valid certificate must be based on the current time.
- Certificate’s common nameBIG-IP verifies the common name of the certificate with the DNSName attributes subject alternative names (subjectAltName).
If any one of the above checks fails, then the certificate is marked as invalid.
Exchanging SSL certificates
Before you can use On-Demand certificate authentication successfully, you must exchange certificates between clients and the BIG-IP system.
The client needs a valid certificate with which to respond to a certificate request. The BIG-IP system includes a self-signed certificate that you can export and install on the client. As an alternative to the self-signed certificate, you can import a certificate and corresponding key (issued by your organization CA) into the BIG-IP system and install that on the client.
The BIG-IP systems needs the client root certificate installed on it. Exporting and importing SSL certificates is done in the System File Management area of the product.
Create a custom Client SSL profile
You create a custom Client SSL profile when you
want the BIG-IP system to terminate client-side SSL traffic for the purpose
of decrypting client-side ingress traffic and encrypting client-side egress
traffic. By terminating client-side SSL traffic, the BIG-IP system offloads
these decryption/encryption functions from the destination server. When you
perform this task, you can specify multiple certificate key chains, one for
each key type (RSA, DSA, and ECDSA). This allows the BIG-IP system to
negotiate secure client connections using different cipher suites based on
the client's preference.
- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Client SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- From theParent Profilelist, selectclientssl.
- Select theCustomcheck box.The settings become available for change.
- From theConfigurationlist, selectAdvanced.
- For theModesetting, select theEnabledcheck box.
- For theCertificate Key Chainsetting, clickAdd.
- From theCertificatelist, select a certificate name.This is the name of a certificate that you installed on the BIG-IP system. If you have not generated a certificate request nor installed a certificate on the BIG-IP system, and the BIG-IP system is not part of a device service clustering (DSC) configuration, you can specify the name of the existing certificate nameddefault.If the BIG-IP system is part of a DSC Sync-Failover group, always select a non-default certificate name, and ensure that this same certificate name is specified in every instance of this SSL profile in the device group. Taking these actions helps to ensure that SSL handshakes are successful after a failover event.
- From theKeylist, select the name of the key associated with the certificate specified in the previous step.This is the name of a key that you installed on the BIG-IP system. If you have not installed a key on the BIG-IP system, and the BIG-IP system is not part of a device service clustering (DSC) configuration, you can specify the name of the existing key nameddefault.If the BIG-IP system is part of a DSC Sync-Failover group, always select a non-default key name, and ensure that this same key name is specified in every instance of this SSL profile in the device group. Taking these actions helps to ensure that SSL handshakes are successful after a failover event.
- From theChainlist, select the chain that you want to include in the certificate key chain.A certificate chain can contain either a series of public key certificates in Privacy Enhanced Mail (PEM) format or a series of one or more PEM files. A certificate chain can contain certificates for Intermediate certificate Authorities (CAs).The default self-signed certificate and the default CA bundle certificate are not appropriate for use as a certificate chain.
- For thePassphrasefield, type a string that enables access to SSL certificate/key pairs that are stored on the BIG-IP system with password protection.This setting is optional. For added security, the BIG-IP system automatically encrypts the pass phrase itself. This pass phrase encryption process is invisible to BIG-IP system administrative users.
- ClickAdd.
- In theCertificate Key Chainsetting, clickAddagain, and repeat the process for all certificate key chains that you want to specify.At a minimum, you must specify an RSA certificate key chain.The result is that all specified key chains appear in the text box.
- TheOCSP Staplingsetting allows you to select an SSL Online Certificate Status Protocol (OCSP) stapling profile which contains various OCSP stapling parameters. By default this setting is disabled. To enable OCSP stapling, select theOCSP Staplingcheck box.To enable OCSP stapling, you must first create an OCSP Stapling profile. SeeCreating an OCSP stapling profilefor detailed steps.
- If you want toNotify Certificate Status to Virtual Server, select the check box.This setting is used to communicate SSL certificate revocation status to the virtual server. This is typically implemented in conjunction with an OCSP stapling configuration.
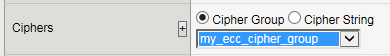
- TheCipherssetting is optional. By default, the Client SSL profile uses the DEFAULT cipher string. In most cases, the DEFAULT cipher string is appropriate, but you can customize it as necessary to meet the security and performance needs of your site. Specify a cipher group or cipher string by choosing one of these options.If you specified an ECDSA certificate key chain in theCertificate Key Chainsetting, you must include the cipher stringECDHE_ECDSAin the cipher group or cipher string that you specify in theCipherssetting. (At a minimum, you should specify a cipher group or string such asDEFAULT:ECDHE_ECDSA.) This is necessary to ensure successful cipher negotiation when the BIG-IP system is offered an ECDSA-based certificate only.OptionDescriptionCipher GroupSelect an existing cipher group from the list when you want to use a system-defined or custom cipher group to define the ciphers that the BIG-IP system uses for negotiating SSL connections. Here's an example of theCipherssetting where we've selected a custom cipher group that we created earlier.
 Cipher StringType a cipher string in the box if you want to manually specify a cipher string instead of selecting a cipher group. For security and performance reasons, consider following these recommendations:
Cipher StringType a cipher string in the box if you want to manually specify a cipher string instead of selecting a cipher group. For security and performance reasons, consider following these recommendations:- Always append ciphers to theDEFAULTcipher string.
- Type a cipher string that includes the ECC key type, because its shorter length speeds up encryption and decryption while still offering virtually the same level of security.
- Disable ADH ciphers but also include the keywordHIGH. To do this, just include both!ADHand:HIGHin your cipher string.
- For AES, DES, and RC4 encryption types, make sure you specify the DHE key exchange method. DHE usesForward Privacy, which creates a key that it throws away after each session so that the same session key never gets used twice. When you use DHE, make sure that the SSL private key isn't being shared with a monitoring system or a security device like an intrusion detection or prevention system. Also, diagnostic tools likessldumpwon't work when you're using Forward Secrecy.
- Disable EXPORT ciphers by including!EXPORTin the cipher string.
- If you can live with removing support for the SSLv3 protocol version, do it. This protocol version is not secure. Simply include:!SSLv3in any cipher string you type.
Here's an example of theCipherssetting where we have opted to manually type the cipher stringDEFAULT:ECDHE-RSA-AES-128-GCM-SHA256:!ADH:!EXPORT:HIGH: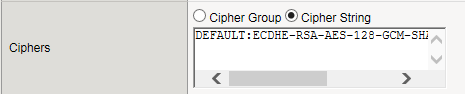
- When enabled, theOptionssetting, references the Options List setting, which are industry standard SSL options and workarounds use for handling SSL processing. The default setting is All Options Disabled. By default, TLSv1.3 is disabled in this configuration.
- TheOptions Listsetting provides selection from a set of industry standard SSL options and workarounds for handling SSL processing.
- TheData 0-RTTsetting when Enabled, specifies that you can initiate a server connection for early data so to receive the benefits of early data delivered to the server-side early. The default value is Disabled.
- When theProxy SSLsetting is enabled, the client can directly authenticate with the server, and the server can authenticate with the client, based on the client certificate presented. In a typical setup, with the BIG-IP system in the middle, the client and server cannot communicate directly to authenticate each other. The Proxy SSL setting requires both a Client SSL profile and a Server SSL profile, and you must enable the setting in both profiles. For information about the Proxy SSL setting, refer to the following resources:
- TheImplementing Proxy SSL on a Single BIG-IP systemchapter in this guide.
- TheProxy SSL Passthroughsetting allows Proxy SSL to pass traffic when the cipher suite negotiated between client and server is not supported. Disabled by default. If you enable it, you should enable this setting on the server SSL profile as well.
- TheModSSL Methodssetting enables or disables ModSSL method emulation. Disabled (cleared) by default. Enable this setting when OpenSSL methods are inadequate. For example, enable it when you want to use SSL compression over TLSv1. When you enable this setting, you can then write an iRule, using theHTTP::header insert_modssl_fieldscommand, which inserts some of the ModSSL options as headers into HTTP requests. SeeModSSL options for use with iRulessection of theAdditional SSL Profile Configuration Optionschapter in this guide.
- TheCache Sizesetting specifies the maximum number of SSL sessions allowed in the SSL session cache. The default value for Cache Size is 262144 sessions. A value of0disallows session caching.
- TheCache Timeoutsetting specifies the number of seconds that the system allows SSL sessions to remain in the SSL session cache before removing them. The default value for Cache Timeout is 3600 seconds. The range of values configurable for Cache Timeout is between 0 and 86400 seconds inclusive.Longer cache timeout periods can increase the risk of SSL session hijacking.
- TheAlert Timeoutsetting specifies the duration that the system tries to close an SSL connection by transmitting an alert or initiating an unclean shutdown before resetting the connection. Select Indefinite to specify that the connection should not be reset after transmitting an alert or initiating an unclean shutdown. The BIG-IP system sends an RST once the Alert Timeout value has been reached, forcefully aborting the connection early and reducing the amount of data transferred between the peer system and the BIG-IP system. The Immediate value makes the BIG-IP system reset both client and server side flows after 1/1000 seconds.
- TheHandshake Timeoutsetting specifies the number of seconds that the system tries to establish an SSL connection before terminating the operation. Selecting Indefinite specifies that the system continues trying to establish a connection for an unlimited time.
- Configure theRenegotiationsetting to control if the virtual server allows midstream session renegotiation. When enabled (default), Renegotiation allows the BIG-IP system to process midstream SSL renegotiation requests. When disabled, the system either terminates the connection or ignores the request, depending on system configuration. SeeAdditional SSL Profile Configuration Optionschapter in this guide for more details.
- TheRenegotiation Periodsetting indicates the amount of time before the system renegotiates the SSL session after the initial connection. If you set it to Indefinite (default), the system does not renegotiate the SSL session.
- TheRenegotiation Sizesetting indicates the amount of application data in megabytes the system must receive from the time of initial connection before it renegotiates the SSL session. If set to Indefinite (default), the system does not renegotiate the SSL session.
- TheRenogotiate Max Record Delaysetting indicates the number of SSL records allowed during the SSL renegotiation before the system terminates the connection. If set to Indefinite, the system allows an unlimited number.
- TheSecure Renegotiationsetting specifies the method of secure renegotiation for SSL connections. The default value for the Client SSL profile isRequire. The values for the Secure Renegotiation setting in the Client SSL profile are as follows:
- Request: Specifies that the system requests secure renegotiation of SSL connections.
- Require: Specifies that the system requires secure renegotiation of SSL connections. In this mode, the system permits initial SSL handshakes from clients but terminates renegotiations from clients that do not support secure renegotiation.
- Require Strict: Specifies that the system requires strict, secure renegotiation of SSL connections. In this mode, the system denies initial SSL handshakes from clients that do not support secure renegotiation.
- TheMax Renegotiationsetting specifies the maximum number of SSL renegotiation attempts per connection that the system can receive in one minute before renegotiating an SSL session. For example, one client with three connections may have a maximum number of SSL renegotiation attempts equal to three times the configured Max Renegotiation value. After the system receives this number of SSL renegotiation records, it closes the connection. This setting applies to client profiles only. The default value is 5.
- TheMax Aggregate Renegotiationsetting specifies the maximum number of aggregated SSL renegotiation records that the system can receive before renegotiating an SSL session. After the system receives this number of aggregated SSL renegotiation records, it closes the connection. This setting applies to client profiles only. The default value is Indefinite.
- TheServer Namesetting specifies the fully qualified DNS hostname of the server, or a wildcard string containing the asterisk (*) character to match multiple names, used in the TLS SNI connection. There is no default value for this setting. For information about configuring the TLS SNI feature on the BIG-IP system, see K13452: Configuring a virtual server to serve multiple HTTPS sites using TLS Server Name Indication feature.
- When enabled, theDefault SSL Profile for SNIsetting indicates that the system should use the profile as the default SSL profile when there is no match to the server name or when the client does not support TLS SNI extension. This setting is disabled by default. For information about configuring the TLS SNI feature on the BIG-IP system, see K13452: Configuring a virtual server to serve multiple HTTPS sites using TLS Server Name Indication feature.
- When enabled, theRequire Peer SNI Supportsetting requires that the client support the TLS SNI extension; otherwise, the BIG-IP system disconnects the client connection with a fatal alert. This setting is disabled by default.
- TheUnclean Shutdownsetting allows the BIG-IP system to perform an unclean shutdown of SSL connections by closing the underlying TCP connection without sending the SSL close notify alerts. By default, this setting is enabled (selected) and is useful for certain browsers that handle SSL shutdown alerts differently. For example, some versions of Internet Explorer require SSL shutdown alerts from the server while other versions do not, and the SSL profile cannot always detect this requirement. In the case where the browser expects a shutdown alert but the SSL profile has not exchanged one (the default setting), the browser displays an error message.
- TheStrict Resumesetting enables or disables the resumption of SSL sessions after an unclean shutdown.
- The BIG-IP SSL profiles support the stateless TLS session resumption mechanism as described in Internet Engineering Task Force (RFC 5077) . This mechanism allows the BIG-IP system to encapsulate the TLS session state as a ticket to the client and allows the client to subsequently resume a TLS session using the same ticket. Disabled (cleared) by default.
- TheSession Ticket Timeoutsetting specifies the timeout for the session ticket. The default is 0 seconds, which means the system uses the cache timeout.
- TheSession Mirroringsetting enables or disables the mirroring of SSL session ID data to a high-availability peer. The default setting is Disabled, preventing the system from mirroring SSL session ID data.
- When enabled (default), theGeneric Alertsetting causes the system to send all SSL alerts using a generic handshake failure message. When the setting is disabled, the system sends more specific SSL alert messages.
- TheNon SSL Connectionssetting enables or disables acceptance of non-SSL connections.
- TheAllow Dynamic Record Sizingsetting allows a TLS performance improvement preventing buffering and delay of TLS record fragment delivery. The BIG-IP system dynamically adjusts the size of TLS records based on the state of the connection. The disabled by default.
- TheMaximum Record Sizesetting specifies the profile's maximum record size. Set to enabled when you want to allow dynamic record sizing. The range is 128 - 16384. The default setting is 16384.
- TheSSL Sign Hashsetting specifies the hash algorithm that the BIG-IP system uses to sign server key exchanges with the Diffie-Hellman (DHE), including Elliptic Curve (ECDHE) ciphers, and for certificate verify messages. Possible choices are SHA1, SHA256, SHA384, or Any. When you select Any, you authorize the system to choose any one of the hash algorithms. The BIG-IP system respects the client signature_algorithms extension as defined in TLS 1.2. When possible, the BIG-IP system prefers SHA256 in the handshake signature based on the content of the signature_algorithms extension. The BIG-IP system further upgrades the hash algorithm to Hash SHA384 from SHA256 when P-384 is used. The BIG-IP system attempts to avoid the use of SHA1 in a TLS handshake, except in the case when signatures are used in X.509 certificates (these signatures are created by the X.509 Certificate Authority). The only time the BIG-IP system uses the SHA1 handshake signature is when an RSA key is used and the signature_algorithms extension is missing or - signature_algorithms is present and only lists SHA1.
- ThePeer No-renegotiate Timeoutsetting specifies the number of seconds the system waits before resetting the connection to peer systems that do not renegotiate SSL sessions. The default is 10.
- TheMax Active Handshakessetting limits the number of concurrent SSL handshakes. When the number of active SSL handshakes reaches the specified limit, the system terminates the most recent SSL handshake. The default setting is Indefinite, which means that there is no limit.
- For information about using the SSL Forward Proxy feature, refer to theImplementing SSL Forward Proxy on a Single BIG-IP systemchapter of the SSL Administration guide.
- In theClient Authenticationsection, theClient Certificatesetting enables and disables client certificate authentication. The possible options for this setting are:
- Ignore: The Ignore setting is the default setting. It disables Client Certificate Authentication. The BIG-IP system ignores any certificate presented and does not authenticate the client before establishing the SSL session.
- Request: The Request setting enables optional Client Certificate Authentication. The BIG-IP system requests a client certificate and attempts to verify it. However, an SSL session is established regardless of whether a trusted CA presents a valid client certificate. The Request setting is often used in conjunction with iRules to provide selective access depending on the certificate presented. For example, this option is useful if you want to allow clients who present a certificate from the configured trusted CA to gain access to the application, while redirecting clients who do not provide the required certificate to a page that details the access requirements. However, if you are not using iRules to enforce a different outcome, depending on the certificate details, there is no functional benefit to using the Request setting instead of the default Ignore setting.
- Require: The Require setting enforces Client Certificate Authentication. The BIG-IP system requests a client certificate and attempts to verify it. The system establishes an SSL session only if a trusted CA presents a valid client certificate. Use the Require setting to restrict access to only clients that present a valid certificate from a trusted CA.
- TheFrequencysetting specifies the frequency of client authentication for an SSL session. The default value for this setting is once.
- TheRetain Certificateis enabled by default. When this setting is disabled, the client certificate is not stored in an SSL session.
- TheCertificate Chain Traversal Depthsetting specifies the maximum number of certificates to be traversed in a client certificate chain. The default value is 9.
- TheTrusted Certificate Authoritiessetting specifies a client CA that the system trusts. The default is.None
- None: Specifies that no CA is trusted for client-side processing.
- ca-bundle: Uses the ca-bundle.crt file, which contains all well-known public certificate authority (CA) certificates, for client-side processing.
- default: Specifies that the trusted CA for client-side processing is the default certificate on the system.
- TheAdvertised Certificate Authoritiessetting specifies that the CAs that the system advertises to clients is being trusted by the profile. The default is None.
- None: Specifies that the system does not advertise any chain as being trusted.
- ca-bundle: Uses the ca-bundle.crt file, which contains all well-known public certificate authority (CA) certificates, for client-side processing.
- default: Specifies that the name of the certificate on the system is the default certificate name, which the system advertises as trusted.
- TheCRL Filesetting allows you to specify a CRL that the BIG-IP system should use to check revocation status of a certificate prior to authenticating a client. If you want to use a CRL, you must import it to the BIG-IP system.
- TheAllow Expired CRL Filesetting instructs the system to use the specified CRL file, even if it has expired. Disabled by default.
- TheClient Certificate Constrained Delegationsetting enables or disables the C3D feature. Using constrained delegation prevents users from having to provide credentials twice for certain authentication actions. For more information on this setting, refer to K72668381: Overview of the SSL Client Certificate Constrained Delegation feature article.
- TheClient Fallback Certificatesetting specifies the client SSL profile name of the certificate file that is used as the client certificate when the client does not send one during SSL handshake. You can click the + icon to open the create-new OCSP object screen.
- TheOCSPsetting specifies the SSL client certificate constrained delegation OCSP object that the BIG-IP system's SSL should use to connect to the OCSP responder and check the client certificate status. You can click the + icon to open the create-new SSL Certifcate screen.
- TheUnknown OCSP Response Controlsetting specifies the action the system takes when the OCSP object returns an unknown status. The default value is Drop, which causes the connection to be dropped. Selecting Ignore causes the connection to ignore the unknown status and continue.
- In theLoggingsection, theLog Publishersetting specifies the defined Log Publisher for the system to use for logging information.
- Select theLog SSL Handshake Eventssetting to log SSL Handshake events that are equal to or above the specified log level. Default is Warning. In descending order of urgency, the available options are Emergency, Alert, Critical, Error, Warning, Notice, Informational, and Debug.
- Select theLog SSL Client Authentication Eventssetting to log SSL Client Authentication events that are equal to or above the specified log level. Default is Warning. In descending order of urgency, the available options are Emergency, Alert, Critical, Error, Warning, Notice, Informational, and Debug.
- Select theLog SSL Forward Proxy Eventssetting to log SSL Forward Proxy events that are equal to or above the specified log level. Default is Warning. In descending order of urgency, the available options are Emergency, Alert, Critical, Error, Warning, Notice, Informational, and Debug.
- Select theLog SSL C3D Eventssetting to log SSL Client Certificate Constrained Delegation (C3D) events that are equal to or above the specified log level. Default is Warning. In descending order of urgency, the available options are Emergency, Alert, Critical, Error, Warning, Notice, Informational, and Debug.
- ClickFinished.
After performing this task, you can see the custom
Client SSL profile in the list of Client SSL profiles on the
system.
Create a custom Server SSL profile
Create a custom server SSL profile to support SSL forward proxy.
- On the Main tab, click .The Server SSL profile list screen opens.
- ClickCreate.The New Server SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- ForParent Profile, retain the default selection,serverssl.
- From theConfigurationlist, selectAdvanced.
- Select theCustomcheck box.The settings become available for change.
- From theSSL Forward Proxylist, selectEnabled.You can update this setting later, but only while the profile is not assigned to a virtual server.
- From theSSL Forward Proxy Bypasslist, selectEnabled(or retain the default valueDisabled).The values of theSSL Forward Proxy Bypasssettings in the server SSL and the client SSL profiles specified in a virtual server must match. You can update this setting later but only while the profile is not assigned to a virtual server.
- Scroll down to theSecure Renegotiationlist and selectRequest.
- For detailed information on the different settings of the SSL:Server page, refer to theSSL Traffic Managementchapter (Create a custom Server SSL profilesection) of the SSL Administration guide.
- ClickFinished.
Adding On-Demand
certificate authentication to an access policy
To successfully pass the On-Demand certificate authentication, the client browser must
have a valid SSL certificate for the BIG-IP system.
The client
browser might stop responding if the client fails to provide a certificate. We
strongly recommend that you add a Decision Box action in which you ask the user
whether a valid certificate is installed and provide an option to not proceed to the
On-Demand Cert Auth action when a valid certificate is not installed.
Add an On-Demand Cert Auth agent to an access
policy to request and validate an SSL certificate anywhere in the session.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- Select the Authentication tab.The tab displays a list of authentication actions.
- SelectOn-Demand Cert Authand clickAdd Item.A properties screen opens.
- From theAuth Modelist, select one of these:
- RequestThis is the default mode.
- RequiredFor an iPod or an iPhone, you must select this mode. (You can select this mode for other clients as well.)To pass a certificate check using Safari, you will be asked to select the certificate multiple times. This is expected behavior.
- ClickSave.The properties screen closes and the policy displays.
- Click theApply Access Policylink to apply and activate the changes to the policy.
The On-Demand Cert Auth action is included and applied to the access policy.
To
apply this access policy to network traffic, add the access profile to a virtual
server.
To ensure
that logging is configured to meet your requirements, verify the log settings for
the access profile.
Verify log settings for the access profile
Confirm that the correct log settings are selected
for the access profile to ensure that events are logged as you intend.
Log settings are configured in the area of the product. They enable and disable logging for access
system and URL request filtering events. Log settings also specify log publishers
that send log messages to specified destinations.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- Click the name of the access profile that you want to edit.The properties screen opens.
- On the menu bar, clickLogs.The access profile log settings display.
- Move log settings between theAvailableandSelectedlists.You can assign up to three log settings that enable access system logging to an access profile. You can assign additional log settings to an access profile provided that they enable logging for URl request logging only.Logging is disabled when theSelectedlist is empty.
- ClickUpdate.
An access profile is in effect when it is assigned to a virtual server.
Add client-side SSL and access profiles to a virtual server
You associate the client SSL and access profiles with the virtual
server so that the BIG-IP system handles client-side SSL
traffic as specified, and so that Access Policy Managercan
apply the access profile to incoming traffic.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- For theSSL Profile (Client)setting, from theAvailablelist, select the name of the Client SSL profile you previously created and move the name to theSelectedlist.
- In the Access Policy area, from theAccess Profilelist, select the access profile that you configured earlier.
- ClickUpdateto save the changes.
The access policy and client-side SSL profiles are now associated with the virtual
server.





