Manual Chapter :
One-Time Password Authentication
Applies To:
Show Versions
BIG-IP APM
- 21.0.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0
One-Time Password Authentication
Overview: Providing a one-time password using email
Access Policy Manager supplies an OTP Generate access policy item that
generates a one-time time-sensitive password and an OTP Verify item that verifies that a user
entered the correct password before that password expired. Between the two actions, you must
configure an action that delivers the one-time password to the user. To send the password in an
email message, use the Email access policy item. You must have an external SMTP server and you
must create an SMTP server configuration for it on the BIG-IP system.
Related access policy macro
A macro template to configure OTP over email is available for use in an access policy. Look at
the macro, AD auth query OTP by email and resources, from the visual policy editor to determine
whether to use it to help you configure the access policy more quickly.
Creating an SMTP server configuration
You specify the SMTP server configuration so that you can send emails through an
SMTP server.
- On the Main tab, click .
- Click theCreatebutton.The New SMTP Configuration screen opens.
- In theNamefield, type a name for the SMTP server that you are creating.
- In theSMTP Server Host Namefield, type the fully qualified domain name for the SMTP server host.
- In theSMTP Server Port Numberfield, type a port number.
- In theLocal Host Namefield, type the host name used in the SMTP headers in the form of a fully qualified domain name.This host name is not the same as the BIG-IP system's host name.
- In theFrom Addressfield, type the email address that you want displayed as the reply-to address for the email.
- From theEncrypted Connectionlist, select the encryption level required for the SMTP server.
- To require that the SMTP server validates users before allowing them to send email, select theUse Authenticationcheck box, and type the user name and password required to validate the user.
- Click theFinishbutton.
You can now configure the system to
use this SMTP server to send emails. For the SMTP mailer to work, you must make sure the
SMTP server is on the DNS lookup server list, and configure the DNS server on the BIG-IP system.
Creating an access policy to send an OTP using email
Before you start this task, configure an access profile.
Create an access policy like this when you need to generate and send a one-time
password over email.
Look at the macro, AD query auth OTP by email and
resources, to determine whether to use it to configure an access policy similar to
this one.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Add actions to authenticate the user and find an email address and a mobile phone number.
- Click the(+)icon anywhere in your access profile to add a new action item.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- On the Authentication tab, selectAD Authand clickAdd Item.A popup properties screen displays.
- From theServerlist, select a server and clickSave.The properties screen closes.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- On the Authentication tab, selectAD Queryand clickAdd Item.An AD Query is only one way to find the email address for a user. If users normally log on to your system with an email address as their username, you can get the email address using a Logon Page action.A popup properties screen displays.
- From theServerlist, select a server.
- ClickAdd new entry.An empty entry displays under Required Attributes (optional).
- Typemobileinto theRequired Attributes (optional)fieldAfter the query, the session.ad.last.attr.mobile variable holds the value.
- ClickAdd new entry.An empty entry displays under Required Attributes (optional).
- Typemailinto theRequired Attributes (optional)fieldAfter the query, the session.ad.last.attr.mail variable holds the value.
- ClickSave.The properties screen closes.
- Generate a one-time password.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- On the Authentication tab, selectOTP Generateand clickAdd Item.
- ClickSave.The properties screen closes and the policy displays.
- Send the OTP to the user through the Email agent.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- On the General Purpose tab, selectEmailand clickAdd Item.
- From theSMTP Configurationlist, select a configuration.The configuration specifies an external SMTP server to send the email.
- In theFromfield, type an email address on the system.
- In theTofield, type an email address, a session variable, or a session variable and a string.For example, type%{session.ad.last.attr.mobile}where providerservice.com is supplied by a mobile phone provider.@providerservice.com
- Type a subject in theSubjectfield.
- In theMessagefield, type the one-time password and anything else the user should know.One Time Passcode: %{session.otp.assigned.val} Expires after use or in %{session.otp.assigned.ttl} seconds
- ClickSave.The properties screen closes and the policy displays.
- Add a Logon Page action that requests the one-time password only.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- On the Logon tab, selectLogon Pageand click theAdd Itembutton.The Logon Page Agent properties screen opens.
- From the Logon Page Agent area, on line 1 selectnonefrom the Type column to remove the user name input field from the logon page; do not change line 2 (password).
- From the Customization area inLogon Page Input Field # 2, type a prompt for the field.For example, type One-Time Passcode.
- ClickSave.The properties screen closes and the policy displays.
- Verify the one-time password.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- On the Authentication tab, selectOTP Verifyand clickAdd Item.
- ClickSave.The properties screen closes and the policy displays.
- Add any other branches and actions that you need to complete the policy.
- Change the Successful rule branch fromDenytoAllow, and then click theSavebutton.
- At the top of the window, click theApply Access Policylink to apply and activate your changes to this access policy.
- Click theClosebutton to close the visual policy editor.
You have an access policy that provides a user with a one-time time-based password
over SMTP.
To
apply this access policy to network traffic, add the access profile to a virtual
server.
To ensure
that logging is configured to meet your requirements, verify the log settings for
the access profile.
Verify log settings for the access profile
Confirm that the correct log settings are selected
for the access profile to ensure that events are logged as you intend.
Log settings are configured in the area of the product. They enable and disable logging for access
system and URL request filtering events. Log settings also specify log publishers
that send log messages to specified destinations.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- Click the name of the access profile that you want to edit.The properties screen opens.
- On the menu bar, clickLogs.The access profile log settings display.
- Move log settings between theAvailableandSelectedlists.You can assign up to three log settings that enable access system logging to an access profile. You can assign additional log settings to an access profile provided that they enable logging for URl request logging only.Logging is disabled when theSelectedlist is empty.
- ClickUpdate.
An access profile is in effect when it is assigned to a virtual server.
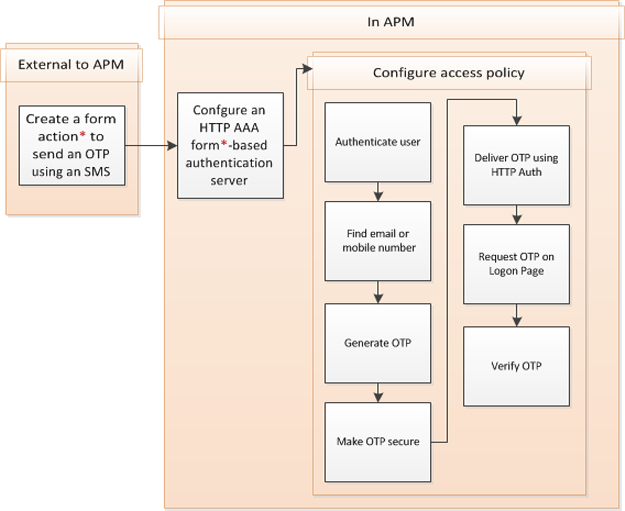
Overview: Providing a one-time password using an external SMS
Access Policy Manager supplies an OTP Generate action that generates a
one-time time-sensitive password and an OTP Verify action that verifies that a user entered
the correct password before it expired. In between the two actions, you must configure an
action that delivers the one-time password to the user. To send the password in a text
message, you can use a form-based HTTP authentication agent (if you do not want to use an
Email agent). You pass the one-time password in hidden parameters to a form action. You must
create a form action that sends the OTP using an external SMS.
Configuration process
Creating a configuration to send an OTP over SMS using HTTP
authentication
Related access policy macro
A macro template to configure an OTP and use the HTTP Auth agent to deliver it is available for
use in an access policy. Look at the macro, AD query auth OTP by HTTP and resources, from the
visual policy editor to determine whether to use it to help you configure the access policy more
quickly.
Configuring HTTP
form-based authentication to deliver a one-time password
Configure an AAA HTTP server to use a form action that you configured previously to send a
one-time password through an external SMS.
- On the Main tab, click .The HTTP servers screen opens.
- ClickCreate.The New Server properties screen opens.
- In theNamefield, type a unique name for the authentication server.
- From the Configuration area, selectForm Basedfor theAuthentication Type.
- Let theForm Methodremain at the default setting,POST.
- In theForm Actionfield, type the complete destination URL to process the form.Specify a URL for a form action that you created to send a user a one-time password using an SMS.
- In theHidden Form Parameters/Valuesfield, type parameters and values for the one-time password, the phone number, and any other values that the form action requires.Here is an example.otp_http_mobile "%{session.ad.last.attr.mobile}" otp_http_email "%{session.ad.last.attr.mail}" otp_http_body "One Time Passcode: %{session.otp.assigned.val} Expires after use or in %{session.otp.assigned.ttl} seconds"
- From theSuccessful Logon Detection Match Typelist, select the method that the authenticating server uses.
- In theSuccessful Logon Detection Match Valuefield, type the value that denotes successful logon.Type a cookie name, a URL, or a string, depending on the successful logon detection match type you selected.
- ClickFinished.The new server displays on the list.
An
HTTP server for form-based authentication with a one-time password is ready for use.
Creating an access policy to send an OTP using an SMS
Before you start this task, configure an access profile and configure a form action
that uses an external SMS to send the one-time password.
Create an access policy like this when you need to generate and send a one-time
password as a text message and you do not want to send it using email.
The macro, AD auth query OTP by HTTP and resources, is available from the visual
policy editor and might be useful to configure an access policy similar to this
one.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Add actions to authenticate the user and find a mobile phone number.
- Click the(+)icon anywhere in your access profile to add a new action item.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- From the Authentication tab, selectAD Authand clickAdd Item.A pop-up properties screen displays.
- From theServerlist, select a server and clickSave.The properties screen closes.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- On the Authentication tab, selectAD Queryand clickAdd Item.A pop-up properties screen displays.
- From theServerlist, select a server.
- ClickAdd new entry.An empty entry displays under Required Attributes (optional).
- Typemobileinto theRequired Attributes (optional)field
- ClickSave.The properties screen closes.
- Generate a one-time password.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- From the Authentication tab, selectOTP Generateand clickAdd Item.
- ClickSave.The properties screen closes and the policy displays.
- Make the OTP secure.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- From the Assignment tab, selectVariable Assignand clickAdd Item.A properties screen opens.
- ClickAdd new entry.AnEmptyentry displays.
- Click thechangelink in the new entry.A popup screen opens.
- From theUnsecurelist, selectSecure.
- In the Custom Variable text box, typesession.user.otp.pwd.
- In the Custom Expression text box, typeexpr { [mcget {session.user.otp.pw}]}.
- ClickFinished.The popup screen closes.
- Send the OTP through the HTTP Auth agent.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- From the Authentication tab, selectHTTP Authand clickAdd Item.
- From the AAA server list, select the HTTP form-based server that you configured previously.
- ClickSave.The properties screen closes and the policy displays.
- Add a Logon Page action that requests only the one-time password.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- From the Logon Page tab, selectLogon Pageand clickAdd Item.A pop-up properties screen displays.
- From the Logon Page Agent area, on line 1 selectpasswordfrom the Type column and change the post and session variable names.The variable name password is acceptable.
- From the Customization area inLogon Page Input Field # 1, type a prompt for the field.For example, type One-Time Passcode.
- ClickSave.The properties screen closes and the policy displays.
- Verify the one-time password.
- On the Successful branch after the previous action, click the(+)icon.An Add Item screen opens, listing predefined actions that are grouped on tabs such as General Purpose, Authentication, and so on.
- From the Authentication tab, selectOTP Verifyand clickAdd Item.
- ClickSave.The properties screen closes and the policy displays.
- Add any other branches and actions that you need to complete the policy.
- Change the Successful rule branch fromDenytoAllow, and then click theSavebutton.
- At the top of the window, click theApply Access Policylink to apply and activate your changes to this access policy.
- Click theClosebutton to close the visual policy editor.
You have an access policy that uses HTTP authentication to provide a user with a
one-time time-based password over SMS.
To
apply this access policy to network traffic, add the access profile to a virtual
server.
To ensure
that logging is configured to meet your requirements, verify the log settings for
the access profile.
Verify log settings for the access profile
Confirm that the correct log settings are selected
for the access profile to ensure that events are logged as you intend.
Log settings are configured in the area of the product. They enable and disable logging for access
system and URL request filtering events. Log settings also specify log publishers
that send log messages to specified destinations.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- Click the name of the access profile that you want to edit.The properties screen opens.
- On the menu bar, clickLogs.The access profile log settings display.
- Move log settings between theAvailableandSelectedlists.You can assign up to three log settings that enable access system logging to an access profile. You can assign additional log settings to an access profile provided that they enable logging for URl request logging only.Logging is disabled when theSelectedlist is empty.
- ClickUpdate.
An access profile is in effect when it is assigned to a virtual server.





