Manual Chapter :
TACACS+ Authentication and Accounting
Applies To:
Show Versions
BIG-IP APM
- 21.0.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0
TACACS+ Authentication and Accounting
About TACACS+ authentication and accounting
Access Policy Manager (APM®) supports
authenticating and authorizing the client against Terminal Access Controller Access Control
System (TACACS+) servers.
TACACS+
is a mechanism used to encrypt the entire body of
the authentication packet. If you use TACACS+ authentication, user credentials are authenticated
on a remote TACACS+ server. If you use the TACACS+ Accounting feature, the accounting service
sends start
and stop
accounting records
to the remote server.APM supports TACACS+ authentication with the TACACS+ Auth access policy item and supports
TACACS+ accounting with the TACACS+ Acct access policy item.
APM must include a TACACS+ server configuration for every TACACS+ server
that exists.
About AAA high availability
Using AAA high availability with Access Policy Manager (APM), you can configure multiple authentication servers to process requests, so that if one authentication server goes down or loses connectivity, the others can resume authentication requests, and new sessions can be established, as usual.
Although new authentications fail if the BIG-IP system loses connectivity to the server, existing sessions are unaffected provided that they do not attempt to re-authenticate.
APM supports the following AAA servers for high availability: RADIUS, Active Directory, LDAP, CRLDP, and TACACS+. APM supports high availability by providing the option to create a pool of server connections when you configure the supported type of AAA server.
If you use AAA with pools, such as RADIUS pools or Active
Directory pools, APM assigns each pool member with a different number for the pool
member's priority group value. APM must define each pool member with a different
priority group because AAA load balancing is not used. The priority group number
increases automatically with each created pool member. Alternative AAA pool
configurations can be defined manually using the full flexibility of Local Traffic
Manager (LTM) if high availability is desired.
Task summary for TACACS+ authentication and accounting
This task list includes all steps required to set up this configuration. If you are adding
TACACS+ authentication or accounting to an existing access policy, you do not need to create
another access profile and the access policy might already include a logon page.
Configuring a TACACS+
AAA server for authentication and authorization
- On the Main tab, click .The TACACS+ Servers list screen opens.
- ClickCreate.The New Server properties screen opens.
- In theNamefield, type a unique name for the authentication server.
- For theServer Connectionsetting, select one of these options:
- SelectUse Poolto set up high availability for the AAA server.
- SelectDirectto set up the AAA server for standalone functionality.
- If you selectedUse Pool, type a name in theServer Pool Namefield.You create a pool of servers on this screen.
- Provide the addresses required for your server connection:
- If you selectedDirect, type an IP address in theServer Addressfield.
- If you selectedUse Pool, for each pool member you want to add, type an IP address in theServer Addressesfield and clickAdd.When you configure a pool, you have the option to type the server address in route domain format:.IPAddress%RouteDomain
- If you selectedUse Pool, you have the option to select aServer Pool Monitorto track the health of the server pool.
- In theService Portfield, type a TACACS+ service port or select one from the list. The default is49.
- In theSecretfield, type a secret key to use to encrypt and decrypt packets sent or received from the server, and then re-type the secret key in theConfirm Secretfield.
- For theServicesetting, select the name of the service for the user who is being authenticated to use.Identifying the service enables the TACACS+ server to behave differently for different types of authentication requests.
- ClickFinished.The new server displays on the list.
Using TACACS+ authentication in an access policy
You configure an access policy with a TACACS+ Auth action to provide TACACS+
authentication as an authentication option for users trying to gain access.
- In the Per-Session Policy column, click theEditlink for the access profile you want to configure.The visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- On the Logon tab, selectLogon Pageand click theAdd Itembutton.The Logon Page Agent properties screen opens.
- Make any changes that you require to the logon page properties and clickSave.The properties screen closes and the policy displays.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- SelectTACACS+ Auth, and clickAdd item.A properties popup screen opens.
- From theAAA Serverlist, select the TACACS+ server to use for authentication.
- Add any other branches and actions that you need to complete the policy.
- ClickSave.The properties screen closes and the policy displays.
- ClickApply Access Policyto save your configuration.
This creates an access policy that presents a user with a logon page, and then uses the
input credentials to authenticate the user with an external TACACS+ server specified in the
TACACS+ AAA server that you select.
To
apply this access policy to network traffic, add the access profile to a virtual
server.
To ensure
that logging is configured to meet your requirements, verify the log settings for
the access profile.
Verify log settings for the access profile
Confirm that the correct log settings are selected
for the access profile to ensure that events are logged as you intend.
Log settings are configured in the area of the product. They enable and disable logging for access
system and URL request filtering events. Log settings also specify log publishers
that send log messages to specified destinations.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- Click the name of the access profile that you want to edit.The properties screen opens.
- On the menu bar, clickLogs.The access profile log settings display.
- Move log settings between theAvailableandSelectedlists.You can assign up to three log settings that enable access system logging to an access profile. You can assign additional log settings to an access profile provided that they enable logging for URl request logging only.Logging is disabled when theSelectedlist is empty.
- ClickUpdate.
An access profile is in effect when it is assigned to a virtual server.
Test AAA high availability for supported authentication servers
To effectively test that high availability works for your authentication servers, you should have two servers that are accessible, where you can remove one of them from the network.
High availability is supported for these authentication server types only: RADIUS, Active Directory, LDAP, CRLDP, and TACACS+.
If you configured a supported authentication server type to use a pool of connection servers, you can test the configuration using these steps.
- Begin atcpdumpon the Access Policy Manager, using a protocol analyzer, and scanning for packets destined for the specific port for your authentication server.
- Log in to the virtual server with both servers active.
- Using thetcpdumprecords, verify that the requests are being sent to the higher priority server.
- Log out of the virtual server.
- Disable the higher-priority server.
- Log in to the virtual server again.
- Verify that the request is being sent to the other server.
- Log out again, re-enabling the server, and try one more time to verify that the new requests are being sent to the high priority server.
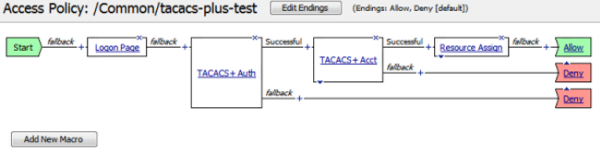
Example access policy for TACACS+ authentication and accounting
This is an example of an access policy with all the associated elements needed to authenticate
and authorize users with TACACS+ authentication. Note that the server used for authentication can
be different from the server used for TACACS+ accounting service.
How TACACS Plus works
TACACS+ session variables for access policy rules
When the TACACS+ Auth (or TACACS+ Acct) access policy item runs, it populates session
variables which are then available for use in access policy rules. The tables list the session
variables for the TACACS+ access policy items and for a logon access policy item.
Session variables for TACACS+
Session Variable |
Description |
|---|---|
session.tacasplus.last.acct.start_date;
session.tacasplus.last.acct.start_time
|
Provides TACACS+ accounting start time and date set by the accounting agent. |
session.tacacsplus.last.acctresult
|
Allows the accounting agent to set the available values to either of the following
values:
|
session.tacacsplus.last.errmsgs
|
Contains the error message string when the TACACS+ authentication or accounting
fails. |
session.tacacsplus.last.result
|
Sets to 1 when authentication succeeds, or 0 when it fails. |
Common session variables
Session Variable |
Description |
|---|---|
session.logon.last.username
|
Provides user credentials. The username string is stored after
encrypting, using the system's client key. |
session.logon.last.password
|
Provides user credentials. The password string is stored after
encrypting, using the system's client key. |
TACACS+ authentication troubleshooting tips
You might run into problems with TACACS+ authentication in some instances. Follow these
tips to try to resolve any issues you might encounter.
TACACS+ auth and query troubleshooting
Possible error messages |
Possible explanations and corrective actions |
|---|---|
No AAA server associated with the agent
|
Make sure that a valid TACACS+ server configuration is assigned to the agent
(TACACS+ Auth or TACACS+ Acct) used in the access policy. |
Failure to connect to TACACS+ server |
Make sure that the TACACS+ server is up and running and reachable from the BIG-IP system. |
Login incorrect |
Supplied user credentials are not valid. |
Invalid reply content, incorrect key |
Make sure that the shared encryption key configured on the TACACS+ server
configuration matches with the key on the remote TACACS+ server. |
Invalid AUTHEN/START packet from server
|
Indicates either the wrong keys or that the authentication action (LOGIN) is not
supported on the server. |
Unacceptable authen method |
Indicates that the TACACS+ server does not support the authentication. Check the
settings on the server. |
Unexpected failure return/legal status value from authentication
function/Permission error |
Caused by internal errors on the remote TACACS+ server. Check the logs on the
remote TACACS+ server and also the configuration. |





