Manual Chapter :
Integrating Portal Access and Secure Web Gateway
Applies To:
Show Versions
BIG-IP APM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0
Integrating Portal Access and Secure Web Gateway
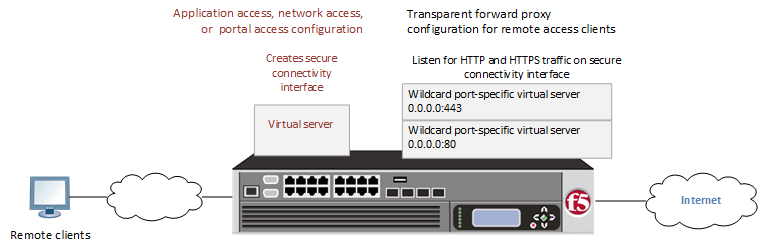
Overview: Configuring transparent forward
proxy for remote access
Access Policy Manager® (APM®) can be configured to
act as a transparent forward proxy to support remote clients that connect using application
access, network access, or portal access.
Using a distinct APM
transparent forward proxy configuration to process traffic from remote clients separately from
a forward proxy configuration used for processing traffic from internal clients provides an
important measure of network security.
Transparent forward proxy for remote
access
Prerequisites for APM
transparent forward proxy for remote access
Before you start to create an Access Policy Manager (APM®) transparent forward proxy
configuration to support remote access clients, you must have completed these tasks.
- You must have a working Network Access, Portal Access, or Application Access configuration.
- You need a per-request policy configured for forward proxy.
- On a BIG-IP system with an SWG subscription, you must ensure that the URL database is downloaded. You can also configure any URL filters that you want to use in addition to, or instead of, the default URL filters.
- On a BIG-IP system without an SWG subscription, if you want to designate only a few URLs for specific handling, you probably do not need to configure user-defined URL categories and filters. However, if you need to control access to many URLs, for better performance and ease-of-use you should configure user-defined URL categories and filters.
Configuration outline for APM transparent
forward proxy for remote access
Tasks for integrating an Access Policy Manager (APM®) remote access configuration with a transparent forward proxy configuration for APM
follow this order.
- First, update the existing application access, network access, or portal access configuration to add a secure connectivity profile to the virtual server if one is not already specified.
- Next, create a transparent forward proxy configuration for APM. The per-request policy is part of this configuration.
- Finally, update the access policy in the existing application access, network access, or portal access configuration if needed. If the per-request policy uses group or class lookup items, add queries to the access policy to populate the session variables on which the lookup items rely.
Creating a connectivity profile
You create a connectivity profile to configure client connections.
- On the Main tab, click .A list of connectivity profiles displays.
- ClickAdd.The Create New Connectivity Profile popup screen opens and displays General Settings.
- Type aProfile Namefor the connectivity profile.
- Select aParent Profilefrom the list.APM provides a default profile,/Common/connectivity.
- ClickOK.The popup screen closes, and the Connectivity Profile List displays.
The connectivity profile displays in the list.
Add a connectivity profile to a virtual server
Update a virtual server that is part of an Access
Policy Manager application access, network access, or portal access
configuration to enable a secure connectivity interface for traffic
from the client.
- On the Main tab, click .The Virtual Server List screen opens.
- Click the name of the virtual server you want to modify.
- Scroll down to the Access Policy area.
- From theConnectivity Profilelist, select the connectivity profile.
- ClickUpdateto save the changes.
Creating an access profile for transparent forward
proxy
You create an access profile to
provide the access policy configuration for a virtual server that
establishes a secured session.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- ClickCreate.The New Profile screen displays.
- In theNamefield, type a name for the access profile.An access profile name should be unique among all per-session profile and per-request policy names.
- From theProfile Typelist, selectSWG-Transparent. Additional settings display.
- From theProfile Scopelist, select the required profile criteria. Default is Profile.
- Profile: Gives an user access only to resources that are behind the same access profile. This is the default value.
- Virtual Server: Gives an user access only to resources that are behind the same virtual server.
- Global: Gives an user access to resources behind any access profile that has global scope.
- Named: Gives an SSL Orchestrator user access to resources behind any access profile that has global scope.
- From theCustomization Typelist, select the required page style for an access profile. Default is Modern. Available options are Modern and Standard. You can also use Standard but Modern customization is simpler and provides better compatibility for modern cross-platform and cross-device applications.
- In theSettingsarea, click theCustomcheckbox to enable the options. Configure the available options as applicable.
- In theConfigurationsarea, configure the following parameters:
- When SWG-Transparent profile type is selected, theUser Identification Methodoption is selected as IP address and remains unchanged.
- IP Address: Use this option only in an environment where a client IP address is unique and can be trusted, typically, in an internal network. This option is not for use with internal NAT or shared systems. In the case of a shared machine, an IP address might already be associated with a user or a session. Using Kerberos or NTLM authentication ensures that the system can associate the IP address with the correct session (new or existing) or with a new user each time a user logs on to a shared machine. Selecting this option ignores the existing cookies.When IP address is selected, the default authentication type is set as None and the NTLM auth configuration and Kerberos auth configuration are optional.
- From theAuthentication typelist, select the required authentication type from the list. Available options are NTLM Only, Kerberos Only, Both, and None.
- From theNTLM Auth Configurationlist, select the required NTLM auth configuration object from the list. Default is None.
- From theKerberos Auth Configurationlist, select the required Kerbreos auth configuration object from the list. Default is None.
- To use NTLM authentication before a session starts, from theNTLM Auth Configurationlist select a configuration.For NTLM authentication to work, you must also enable theCaptive Portalssetting and specify an IP address in thePrimary Authentication URIfield for the virtual server that you configure for the captive portal.In the case of a shared machine, an IP address might already be associated with a user or a session. Using NTLM authentication ensures that the system can associate the IP address with the correct session (new or existing) or with a new user each time a user logs on to the shared machine.
- To direct users to a captive portal, forCaptive PortalselectEnabledand, in thePrimary Authentication URIfield, type the URI.You might specify the URI of your primary authentication server if you use single sign-on across multiple domains. Users can then access multiple back-end applications from multiple domains and hosts without needing to re-enter their credentials, because the user session is stored on the primary domain.For example, you might typehttps://logon.siterequest.comin the field.
- In the Language Settings area, add and remove accepted languages, and set the default language.If any browser language does not match with the accepted languages list, the browser uses the default language.
- ClickFinished.The Access Profiles list screen displays.
The access
profile displays in the Access Profiles List. Default-log-setting is assigned to the
access profile.
You do not need to add any actions or
make any changes to the access policy.
Create a wildcard virtual server for HTTP traffic on the connectivity interface
Before you begin, you need to know
the name of the connectivity profile specified in the virtual server for the remote
access configuration that you want Access Policy Manager (APM) to protect.
You configure a virtual server to process web traffic on the secure connectivity
interface for a remote access client.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- In theDestination Address/Maskfield, type0.0.0.0to accept any IPv4 traffic.
- In theService Portfield, type80, or selectHTTPfrom the list.
- From theConfigurationlist, selectAdvanced.
- From theHTTP Profile (Client)list, select a previously-created HTTP/2 profile for client-side traffic.
- Scroll down to theVLAN and Tunnel Trafficsetting and selectEnabled on.
- For theVLANs and Tunnelssetting, move the secure connectivity interface to theSelectedlist.
- From theSource Address Translationlist, selectAuto Map.
- Scroll down to thePort Translationsetting and clear theEnabledcheck box.
- In the Access Policy area, from theAccess Profilelist, select the access profile that you configured earlier.
- In the Access Policy area, from thePer-Request Policylist, select the policy that you configured earlier.
- ClickFinished.
Create a custom Client SSL forward proxy profile
You perform this task to create a Client SSL forward proxy profile that makes it
possible for client and server authentication while still allowing the BIG-IP system to perform data optimization, such as decryption
and encryption. This profile applies to client-side SSL forward proxy traffic
only.
- On the Main tab, click .The Client SSL profile list screen opens.
- ClickCreate.The New Client SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- From theParent Profilelist, selectclientssl.
- From theSSL Forward Proxylist, selectAdvanced.
- Select theCustomcheck box for the SSL Forward Proxy area.
- Modify the SSL Forward Proxy settings.
- From theSSL Forward Proxylist, selectEnabled.
- From theCA Certificatelist, select a certificate.If the BIG-IP system is part of a DSC Sync-Failover group, always select a non-default certificate name, and ensure that this same certificate name is specified in every instance of this SSL profile in the device group. Taking these actions helps to ensure that SSL handshakes are successful after a failover event.
- From theCA Keylist, select a key.If the BIG-IP system is part of a DSC Sync-Failover group, always select a non-default key name, and ensure that this same key name is specified in every instance of this SSL profile in the device group. Taking these actions helps to ensure that SSL handshakes are successful after a failover event.
- In theCA Passphrasefield, type a passphrase.
- In theConfirm CA Passphrasefield, type the passphrase again.
- In theCertificate Lifespanfield, type a lifespan for the SSL forward proxy certificate in days.
- From theCertificate Extensionslist, selectExtensions List.
- For theCertificate Extensions Listsetting, select the extensions that you want in theAvailable extensionsfield, and move them to theEnabled Extensionsfield using theEnablebutton.
- Select theCache Certificate by Addr-Portcheck box if you want to cache certificates by IP address and port number.
- From theSSL Forward Proxy Bypasslist, selectEnabled.Additional settings display.
- From theBypass Default Actionlist, selectInterceptorBypass.The default action applies to addresses and hostnames that do not match any entry specified in the lists that you specify. The system matches traffic first against destination IP address lists, then source IP address lists, and lastly, hostname lists. Within these, the default action also specifies whether to search the intercept list or the bypass list first.If you selectBypassand do not specify any additional settings, you introduce a security risk to your system.
- For detailed information on the different settings of the SSL:Client page, refer to theSSL Traffic Managementchapter (Create a custom Client SSL profilesection) of the SSL Administration guide.
- ClickFinished.
Create a custom Server SSL profile
Create a custom server SSL profile to support SSL forward proxy.
- On the Main tab, click .The Server SSL profile list screen opens.
- ClickCreate.The New Server SSL Profile screen opens.
- In theNamefield, type a unique name for the profile.
- ForParent Profile, retain the default selection,serverssl.
- From theConfigurationlist, selectAdvanced.
- Select theCustomcheck box.The settings become available for change.
- From theSSL Forward Proxylist, selectEnabled.You can update this setting later, but only while the profile is not assigned to a virtual server.
- From theSSL Forward Proxy Bypasslist, selectEnabled(or retain the default valueDisabled).The values of theSSL Forward Proxy Bypasssettings in the server SSL and the client SSL profiles specified in a virtual server must match. You can update this setting later but only while the profile is not assigned to a virtual server.
- Scroll down to theSecure Renegotiationlist and selectRequest.
- For detailed information on the different settings of the SSL:Server page, refer to theSSL Traffic Managementchapter (Create a custom Server SSL profilesection) of the SSL Administration guide.
- ClickFinished.
Create a wildcard virtual server for SSL traffic on the connectivity interface
Before you begin, you need to know the name of the connectivity profile specified in
the virtual server for the remote access configuration that you want Secure Web Gateway
(SWG) to protect. Also, if you do not have existing client SSL and server SSL profiles
that you want to use, configure them before you start.
You configure a virtual server to process SSL web traffic coming in on the secure
connectivity interface for a remote access client.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- In theDestination Address/Maskfield, type0.0.0.0to accept any IPv4 traffic.
- In theService Portfield, type443or selectHTTPSfrom the list.
- From theConfigurationlist, selectAdvanced.
- From theHTTP Profile (Client)list, select a previously-created HTTP/2 profile for client-side traffic.
- For theSSL Profile (Client)setting, from theAvailablelist, select the name of the Client SSL forward proxy profile you previously created, and using the Move button, move the name to theSelectedlist.To enable SSL forward proxy functionality, you can either:
- Disassociate existing Client SSL and Server SSL profiles from a virtual server and configure the SSL Forward Proxy settings.
- Create new Client SSL and Server SSL profiles and configure the SSL Forward Proxy settings.
Then with either option, select the Client SSL and Server SSL profiles on a virtual server. You cannot modify existing Client SSL and Server SSL profiles while they are selected on a virtual server to enable SSL forward proxy functionality. - For theSSL Profile (Server)setting, from theAvailablelist, select the name of the Server SSL forward proxy profile you previously created, and using the Move button, move the name to theSelectedlist.To enable SSL forward proxy functionality, you can either:
- Disassociate existing Client SSL and Server SSL profiles from a virtual server and configure the SSL Forward Proxy settings.
- Create new Client SSL and Server SSL profiles and configure the SSL Forward Proxy settings.
Then with either option, select the Client SSL and Server SSL profiles on a virtual server. You cannot modify existing Client SSL and Server SSL profiles while they are selected on a virtual server to enable SSL forward proxy functionality. - Scroll down to theVLAN and Tunnel Trafficsetting and selectEnabled on.
- For theVLANs and Tunnelssetting, move the secure connectivity interface to theSelectedlist.
- From theSource Address Translationlist, selectAuto Map.
- Scroll down to thePort Translationsetting and clear theEnabledcheck box.
- For theAddress Translationsetting, clear theEnabledcheck box.
- In the Access Policy area, from theAccess Profilelist, select the access profile that you configured earlier.
- In the Access Policy area, from thePer-Request Policylist, select the policy that you configured earlier.
- ClickFinished.
Update the access policy in the remote access configuration
Add queries to the access policy to populate any session variables that are required
for successful execution of the per-request policy.
Class lookup or group lookup items in a per-request policy rely on
session variables that can only be populated in this access policy.
- On the Main tab, click .The Access Profiles (Per-Session Policies) screen displays.
- Click the name of the access profile that you want to edit.The properties screen opens.
- In the General Properties area, click theEdit Access Policy for Profilelink.profile_nameThe visual policy editor opens the access policy in a separate screen.
- Click the(+)icon anywhere in the access policy to add a new item.Only an applicable subset of access policy items is available for selection in the visual policy editor for any access profile type.A popup screen opens, listing predefined actions on tabs such as General Purpose, Authentication, and so on.
- To supply LDAP group information for use in the per-request policy, add an LDAP Query item anywhere in the policy and configure its properties:
- From theServerlist, select an AAA LDAP server.An LDAP Query uses SSL connections when you select an LDAP AAA server that is configured for LDAPS.
- Specify theSearchDN, andSearchFiltersettings.SearchDN is the base DN from which the search is done.
- ClickSave.
This item populates thesession.ldap.last.attr.memberOfsession variable. - To supply Active Directory groups for use in the per-request policy, add an AD Query item anywhere in the policy and configure its properties:
- From theServerlist, select an AAA AD server.
- Select theFetch Primary Groupcheck box.The value of the primary user group populates thesession.ad.last.attr.primaryGroupIDsession variable.
- ClickSave.
- To supply RADIUS class attributes for use in the per-request policy, add a RADIUS Auth item anywhere in the policy and configure its properties:
- From theServerlist, select an AAA RADIUS server.
- ClickSave.
This item populates thesession.radius.last.attr.classsession variable. - To supply local database groups for use in the per-request policy, add a Local Database item anywhere in the policy and configure its properties:
- From theLocalDB Instancelist, select a local user database.
- In theUser Namefield, retain the default session variable.
- ClickAdd new entryA new line is added to the list of entries with the Action set toReadand other default settings.
- In the Destination columnSession Variablefield, typesession.localdb.groups.If you type a name other thansession.localdb.groups, note it. You will need it when you configure the per-request access policy.
- In the Source column from theDB Propertylist, selectgroups.
- ClickSave.
This item populates thesession.localdb.groupssession variable.
The access policy is configured to support the per-request policy.
Click the
Apply Access
Policy
link to apply and activate your changes to this access policy.
To ensure that logging is configured to meet your requirements, verify the log settings for the access profile.
About configuration
elements for transparent forward proxy (remote access)
When you configure the BIG-IP system so that Access Policy Manager (APM) can act as a transparent forward proxy for use by
remote access clients, you might want to understand how these objects fit into the overall
configuration.
- Secure connectivity interface
- In a remote access configuration, a connectivity profile is required on the virtual server to specify a secure connectivity interface for traffic from the client. In the APM configuration, wildcard virtual servers must listen on the secure connectivity interface for traffic from remote access clients.
- Per-request policy
- In any APM forward proxy configuration, the determination of whether a user can access a URL must be made in a per-request access policy. A per-request access policy determines whether to block or allow access to a request based on time or date or group membership or other criteria that you configure.
- Access policies
- The access policy in the remote access configuration continues to authenticate users, assign resources, and evaluate ACLs, if any. In addition, this access policy must populate any session variables used in the per-request policy. An access profile of theSWG-Transparenttype is required; however, it is not necessary to include any items in the access policy.
Per-request policy items that read session variables
This table lists some of the many per-request policy items that read session variables.
Per-request policy item | Session variable | Access policy item |
|---|---|---|
AD Group Lookup | session.ad.last.attr.primaryGroupID | AD Query |
LDAP Group Lookup | session.ldap.last.attr.memberOf | LDAP Query |
LocalDB Group Lookup | session.localdb.groups This session variable is a default in the expression for LocalDB
Group Lookup; any session variable in the expression must match the session variable
used in the Local Database action in the access policy. | Local Database |
RADIUS Class Lookup | session.radius.last.attr.class | RADIUS Auth |





