Manual Chapter :
Access Reporting and Statistics
Applies To:
Show Versions
BIG-IQ Centralized Management
- 6.0.0
Access Reporting and Statistics
About Access and SWG reports
Access reports focus on session and logging data from Access devices (managed devices with
APM licensed and provisioned).
F5 Secure Web Gateway Services reports focus on user requests (for URLs or
applications, for example) from Access devices with Secure Web Gateway Services provisioned.
BIG-IQ® Centralized Management Access also supports high availability.
Thus, users can view both Access and SWG reports on a secondary BIG-IQ system.
Access reports and SWG reports provide the following features.
- Reports on any combination of discovered devices, Access groups, and clusters
- Graphs for typical areas of concern and interest, such as cross-geographical comparisons or top 10 issues
- Tabular data to support the graphs
- Ability in some screens to drill down from summarized data to details
- Ability to save data to CSV files
Setup requirements for Access and SWG reports
Before you can produce Access reports and SWG reports, you must ensure that these tasks are
already complete.
- Set up the BIG-IQ® Centralized Management data collection devices.
- Add the BIG-IP® devices to BIG-IQ inventory.
- Discover the devices. (Devices with the Access service configuration are what you need.)
- Run the data collection device configuration setup on the devices from the Access Reporting screen.
Create flexible reports using the Access summary dashboard
For Access Policy Manager ® (APM) to have monitoring data for your device, you must add the BIG-IP device to the BIG-IQ Centralized Management system. The system must then discover the device, and a user must run the Access remote logging configuration on the device. You may use the Access Summary dashboard to view aggregated data from APM policies managed by this BIG-IQ environment. Data you may view includes authentication, connectivity, user, session, and license information. To do so, on the Main tab, navigate to .
Widget Title | Description |
|---|---|
ACCESS GROUP/DEVICE | Select Managed Devices or select one or more of these options:
|
TIMEFRAME | Adjust the time frame to reflect the period for which you would like to view data. You may do this by either: selecting the interval from the TIMEFRAME drop down menu, or by dragging the date selector from the horizontal widget below it. You may also select a timeframe between two specific dates or before or after a selected date by selecting Between ,Before , or After and then selecting a date or date range from the calendar widget.Once you have selected the time frame or date range you are interested in, the data on this dashboard will change to reflect the new time period. |
All Active Users | From this dashlet, you may view all unique users with an active session using this device or devices. You may drill down on this information and obtain more data about: top 10 client IP addresses, top 10 countries, top 10 users, top 10 Access profiles, top 10 virtual servers, top 10 client profiles, and top 10 Access policies associated with this metric. |
Sessions Created
| From this widget, you may view all new sessions initiated during the timeframe currently displayed at the top of the page. Select this widget to drill down and obtain more data about: top 10 client IP addresses, top 10 countries, top 10 users, top 10 Access profiles, top 10 virtual servers, top 10 client profiles, and top 10 Access policies associated with this metric.
|
Unique Users
| View the number of unique users during the timeframe specified at the top of the page. Select this widget to drill down and obtain more data about: top 10 client IP addresses, top 10 countries, top 10 users, top 10 Access profiles, top 10 virtual servers, top 10 client profiles, and top 10 Access policies associated with this metric.
|
Sign-In Denied
| From this widget, you can view the number of sessions that have been denied. Select this widget to drill down and obtain more data about: top 10 client IP addresses, top 10 countries, top 10 users, top 10 Access profiles, top 10 virtual servers, top 10 client profiles, and top 10 Access policies associated with this metric.
|
Active Sessions Over Time
| You may track the Average Established number of sessions in an interval of time, the Average Attempted number of sessions in one interval of time, the Maximum Established number of sessions in an interval of time, and the Maximum Attempted number of sessions in an interval of time. You may remove any of these components from the graph to focus your report by selecting the name of the component in the ledger at the top right corner of the chart. The time intervals with the horizontal axis will adjust depending on the length of time you select in the Timeframe widget at the top of the page. For example, longer time frames will yield larger intervals for data collection and shorter time frames will yield shorter intervals for data collection. Average and Maximum refer to the aggregated data in a single unit of time on the horizontal axis. You can check what units of time the graph is using in the top left corner of the chart. |
Denied Sessions / Auth Failures Over Time
| This widget allows you to track denied sessions and Authentication failures against each other. You may remove either denies sessions or Authentication failures from the data set by selecting either of these components in the legend at the top right corner of the chart.
|
Top 3 Devices by License Usage
| You may view devices by license usage in one of three categories: Access Sessions, Connectivity Sessions, and Secure Web Gateway (SWG) Sessions. Click on any of these categories to view the license usage for each, including the threshold and usage limit of each of the top three devices. By hovering over the bar graph for a device, you may view how many users are licensed for this device (displayed as the Limit ) and how many are currently using it (displayed as Usage .
|
Session Count Distribution Across Countries
| Use this widget to select a geographic location to view from the map to view more information about session logon locations in another dashboard. You may also view more data about sessions originating from unknown location by clicking on Unknown Locations at the bottom of the dashlet. To zoom in or out on the map widget, use the + and - icons.
|
Top Users by Session Count
| You may view the top 10 users with the most sessions for this device or set of devices. To learn more about the activity of each user, select the name to navigate to a summary dashboard displaying usage data for this user only.
|
What data goes into Access reports for the All Devices option?
The
All Devices
option for Access reports includes data from the devices
that are currently managed (discovered) in the BIG-IQ® system. This is in
addition to data from devices that were managed at some point during the report timeframe, but
that are not currently managed. With All Devices
selected, if data from
unmanaged devices exists, it displays in reports. An unmanaged device might be unmanaged temporarily or permanently. Any time a configuration
management change causes APM® to be undiscovered, the device and its data
are moved to
All Devices
until APM is re-discovered on the device. You cannot generate a report for an unmanaged device. However, you can generate a report for
the timeframe when the device was managed, and then search the report for the unmanaged device
name. In the Summary report, All Active Sessions includes the number of sessions that were active
on the device when it became unmanaged. Those sessions stay in the Summary and in the Active
sessions reports
until the next
session status update, which occurs every 15 minutes.
About upgrades affecting reports
When you upgrade a
BIG-IQ® Centralized Management system without taking a snapshot, it deletes all
reporting data, including both Access and SWG reports. After upgrading, users cannot obtain these
reports from the
BIG-IP® devices. To prevent the lost of reports, users should take an
Elasticsearch snapshot before upgrading, and restore the snapshot after upgrading. For more
information on elasticsnapshots, refer to
F5 BIG-IQ Centralized Management: Upgrading
Logging Nodes to Version
x.x.About the application dashboard
The Application Summary dashboard is your starting point to view and download general reports
for BIG-IQ Access.
View the Application Summary
dashboard
The
BIG-IQ Centralized Management Application Summary dashboard
displays information regarding the applications linked to the system.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .
The Application Summary screen opens,
showing detailed information and charts for specific applications.
About user visibility
You can monitor your user base by viewing the BIG-IQ® Centralized
Management Access user dashboard for data on specific users. The system displays which users
created the most sessions, were denied the most sessions, and had the longest total session
duration. The administrator can enter a specific user name to get the following details for the
user:
- The user login locations on a world map
- The total sessions, denied sessions, and session duration
- The Access denied sessions.
- The top authentication failures, including AD Auth and LDAP only
- The device type users used to log into the system
- The reason the system terminated the session
- The login history showing the success and failures over time
- The most accessed applications
- The most accessed URLs
- The login failure attempts over time, sorted by the reason
- The client session duration over time
- The Access denied reason over time
About application visibility
You can monitor your applications by viewing the BIG-IQ® Centralized
Management Access user dashboard for data on which applications are linked to the BIG-IQ Access
component. The system displays the top applications used and the application usage time.
Administrators can expand the GUI for a specific application and view the following
information:
- The application access history
- The users who use the application the most
- The access history
- The world map, showing where the user is access the application
About denied sessions
You can monitor the sessions that
BIG-IQ® Centralized Management denies. By using the Access Monitoring option,
you can view the following information:
- The history of denied sessions
- The reasons why sessions were denied
- The top denied users, sorted by session count
- The top authentication failures
- The top denied policies
- The top denied sessions by country of origin
- The top denied session by the virtual server
- The denied sessions, sorted by the client platform
Viewing denied sessions
You can use the BIG-IQ Centralized Management Access reporting features to see which sessions
were denied by the system, as well to create a report.
- Log in to the BIG-IQ system with your user name and password.
- Click .
- From theACCESS GROUP/DEVICElist at upper left, selectManaged Devicesor select one or more of these options:
- <- Select to include all devices in the Access group.Access group name>
- <- Select to include the devices in the cluster.Cluster display name>
- <- Select to include the device. You can select any device fromDevice name>Managed Devices,<, orAccess group name><.Cluster display name>
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
From here, you can view details
regarding denied sessions and create a report.
Managing a specific user in Access
reporting
You can use the
BIG-IQ Centralized Management Access reporting tools to view the
user dashboard for data on a specific user.
- Log in to the BIG-IQ system with your user name and password.
- Click .The User Summary screen displays, showing detailed information for specific users.
Running Access reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
You can create Access reports for
any device with the APM service configuration on it that has been
discovered on the BIG-IQ system, whether or not the device is a member of an Access
group. To create a report, you can select any combination of Access groups, clusters,
and devices.
- At the top of the screen, clickMonitoring.
- On the left, select .A Summary report (for all devices and a default timeframe) starts to generate and display.
- From the left, select any report that you want to run.
- At the top left of the screen, from theACCESS GROUP/DEVICESlist, either select one of the first two options (All DevicesandAll Managed Devices) or, select one or more of the other options (<,Access group name><, andCluster display name><).Device name>
- All DevicesIncludes Access devices that are currently managed, and Access devices that were managed at one time but are not managed now. (A managed device is one that has been discovered with the APM service configuration.)
- All Managed DevicesIncludes all Access devices that are currently discovered.
- <- Select to include all devices in the Access group.Access group name>
- <- Select to include the devices in the cluster.Cluster display name>
- <- Select to include the device. You can select any device fromDevice name>Managed Devices,<, orAccess group name><.Cluster display name>
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Getting the details that underlie an Access report
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
From the Summary report, and from most session reports, the initial display
includes graphs that summarize the report data. You can get successively more detailed
information by clicking a bar or a point on a graph or clicking a link if one is
displayed on the screen.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .The Summary report is an example of the type of report that presents high-level data, and provides access to underlying data.A Summary report (for all devices and a default timeframe) starts to generate and display.
- Click anywhere in a summary to get more information.Top left portion of the Summary report display
 Additional graphs display, and supporting data displays in a table at the bottom of the screen.
Additional graphs display, and supporting data displays in a table at the bottom of the screen. - If more details are available, click the bars in the graphs to display more details.
- Scroll down to the table to view the supporting data.
- If the table includes aSession IDfield, click the link in that field to open the session details.Session details popup screen (with addresses and host names blurred)
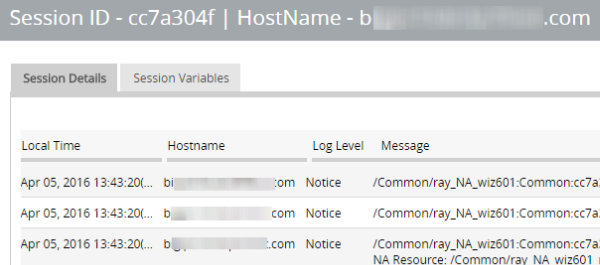
- To change which records display on this screen, select a log level from theLOG LEVELlist at the top of the screen.
About the maximum number records for Access and SWG reports
When you run an Access report or an SWG report, Access can get up to 10,000 records to display
to you. After you scroll to the end of those 10,000 records, Access displays a message. At that
point, all you can do is select fewer devices or select a shorter timeframe.
Setting the timeframe for your Access or SWG report
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Use the
TIMEFRAME
list at the top of any Access or SWG
report to change the report time period.- Log in to BIG-IQ Centralized Management with your admin user name and password.
- At the top of the screen, clickMonitoring.
- To set a predefined timeframe, select one of these from theTIMEFRAMElist:Last hour,Last day,Last week,Last 30 days,Last 3 months.
- To set a custom timeframe, select one of these from theTIMEFRAMElist:
- Between: Click each of the additional fields that display to select dates and times. The report displays the records between those dates and times.
- Before: Click the additional fields that display to select a date and a time. The report displays the records before that date and time.
- After: Click the additional fields that display to select a date and a time. The report displays the records after that date and time.
Access report problems: causes and resolutions
Problem | Resolution |
|---|---|
A session is over, but it continues to display in the Active sessions report. | If a session starts when logging nodes are up and working, but terminates during a
period when logging modes are unavailable, the session remains in the Active sessions report
for 15 minutes. After 15 minutes, the session status is updated and the session is dropped
from the report. |
Active sessions are included in the Summary and Active sessions reports for a device that is no longer managed. | Sessions were active on a device when it was removed from an Access group and became
unmanaged. Sessions that were active when the device became unmanaged remain counted in All
Active Sessions on the Summary screen and stay in the Active sessions report until the next
session status update, which occurs every 15 minutes. |
A session is over, but Session Termination and
Session Duration are blank in a session report. | If a session starts when logging nodes are up and working but terminates during a
period when logging nodes are unavailable, the session termination is not recorded and the
session duration cannot be calculated. |
What can cause logging nodes to become unavailable?
Logging nodes are highly available, but it is still possible for them to become unavailable.
This could occur, for example, if all logging nodes are on devices in the same rack in a lab, and
the power to the lab shuts down.
Sessions
Running Session reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
You can create Session reports for
any device with the APM service configuration on it that has been
discovered on the BIG-IQ system, whether or not the device is a member of an Access
group. To create a report, you can select any combination of Access groups, clusters,
and devices.
- At the top of the screen, clickMonitoring.
- On the left, select .A Summary report (for all devices and a default timeframe) starts to generate and display.
- From the left, select any report that you want to run.
- At the top left of the screen, from theACCESS GROUP/DEVICESlist, either select one of the first two options (All DevicesandAll Managed Devices) or select one or more of the other options (<,Access group name><, andCluster display name><).Device name>
- All DevicesIncludes Access devices that are currently managed, and Access devices that were managed at one time but are not managed now. (A managed device is one that has been discovered with the APM service configuration.)
- All Managed DevicesIncludes all Access devices that are currently discovered.
- <- Select to include all devices in the Access group.Access group name>
- <- Select to include the devices in the cluster.Cluster display name>
- <- Select to include the device. You can select any device fromDevice name>Managed Devices,<, orAccess group name><.Cluster display name>
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Stopping sessions on BIG-IP devices from Access
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
You can stop currently active sessions on BIG-IP devices,
using the Active sessions report on the BIG-IQ system.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .A Summary report (for all devices and a default timeframe) starts to generate and display.
- On the left, fromSessions, selectActive.The screen displays a list of active sessions for all devices.
- To display sessions for particular devices, groups, or clusters only, select them from theACCESS GROUP/DEVICElist at upper left.The screen displays the active sessions for the selected devices.
- To stop specific sessions only, select the sessions that you want to end and clickKill Selected Sessions.
- To stop all sessions, clickKill All Sessions.
Running Secure Web Gateway reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Only a device with SWG provisioned on it can provide data for Secure Web Gateway
reports. You can create SWG reports for Access groups, clusters (in Access groups), or
devices that you select from the Access groups and clusters (in Access groups) on the
BIG-IQ system.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .A Summary report (for all devices and a default timeframe) starts to generate and display.
- From the left, select any report that you want to run.
- From theACCESS GROUP/DEVICElist at upper left, selectManaged Devicesor select one or more of these options:
- <- Select to include all devices in the Access group.Access group name>
- <- Select to include the devices in the cluster.Cluster display name>
- <- Select to include the device. You can select any device fromDevice name>Managed Devices,<, orAccess group name><.Cluster display name>
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Getting the details that underlie an SWG report
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Only a device with SWG provisioned on it can provide data for SWG reports.From the Summary report, the initial display includes graphs that summarize the
report data. You can get more detailed information by clicking a bar or a point on a
graph to see additional graphs and tables with supporting entries.
- Log in to BIG-IQ Centralized Management with your admin user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .The Summary starts to generate and display. A timeline and some summaries display across the top of the screen. Graphs display under the summaries. Each graph provide different views of the data.
- Click any bar in a graph on the display to get more information.Additional graphs provide different views of the data, and supporting data displays in a table at the bottom of the screen.
- If more details are available, click the bars in the graphs to display them.
- Scroll down to the table to view the supporting data.
About VDI reports
You can monitor your virtual desktop infrastructure (VDI) by viewing the
BIG-IQ® Centralized Management Access user dashboard for VDI applications, and
creating a VDI report. The system displays the top VDI applications used and the application
usage time. Administrators can expand the UI for a specific application, and view the following
information:
- The top 10 VDI applications
- The top users for the VDI applications
- The application usage history
Managing federation reports
Running OAuth reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Only a device with OAuth provisioned on it can provide data for OAuth reports. You can create OAuth reports for
Access groups, clusters (in Access groups), or devices that you select from the Access
groups and clusters (in Access groups) on the BIG-IQ Centralized
Management system.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .
- SelectAuthorization Server,Client, orResource.A Summary report (for all devices and a default timeframe) starts to generate and display.
- From the left, select any report that you want to run.
- From theACCESS GROUP/DEVICElist at upper left, selectManaged Devicesor select one or more of these options:
- <- Select to include all devices in the Access group.Access group name>
- <- Select to include the devices in the cluster.Cluster display name>
- <- Select to include the device. You can select any device fromDevice name>Managed Devices,<, orAccess group name><.Cluster display name>
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Monitoring the OAuth server
performance
The Authentication Server Summary screen shows several charts that you can use to
track the health of your authorization server role. Data appears when you configure
statistics collection. Controls on this screen work together so you can fine-tune
the statistics display.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .The Authorization Server Peformance screen opens.
- From theACCESS GROUP/DEVICElist at upper left, selectAll Managed Devicesor or one of the session-specific options.
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- From theAUTHORIZATION SERVERlist, select an OAuth authorization server.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Monitoring the OAuth token summary
The Token Summary screen shows several charts that you can use to track the health of
your OAuth tokens. Data appears when you configure statistics collection. Controls
on this screen work together so you can fine-tune the statistics display.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .The Authorization Server Peformance screen opens.
- From theACCESS GROUP/DEVICElist at upper left, selectAll Managed Devicesor or one of the session-specific options.
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- From theAUTHORIZATION SERVERlist, select an OAuth authorization server.
- From theGRANT TYPElist, select an OAuth2 grant type.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Running SAML reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Only a device with SAML provisioned on it can provide data for SAML reports. You can create SAML reports for
Access groups, clusters (in Access groups), or devices that you select from the Access
groups and clusters (in Access groups) on the BIG-IQ Centralized
Management system.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .
- SelectSP SummaryorIdP Summary.A Summary report (for all devices and a default timeframe) opens, displaying chart data for assertions over time, the top SPs or IdPs with successful assertions, the top client IP addresses, the top subject values with successful assertions, and the top SP or IdPs with failed assertions.
- From theACCESS GROUP/DEVICElist at upper left, selectAll Managed Devicesor or one of the session-specific options.
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- From theSPlist, select a service provider.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
- To view the successful SP assertions, clickAssertions Success.The Successful Assertions screen opens, displaying data and statistics for the top 10 client IP's, platform distribution, geolocation distribution, subject values and SPs with successful assertions.
- To view the failed SP assertions, clickAssertions Failed.The Failed Assertions screen opens, displaying data and statistics for the top 10 client IP's, platform distribution, geolocation distribution, subject values and SPs with failed assertions.
Running SP assertion reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Only a device with SAML provisioned on it can provide data for SAML reports. The SP Assertions screen shows several charts that you can use to track the health of
your SAML SP assertions. Data appears when you configure statistics collection.
Controls on this screen work together so you can fine-tune the statistics
display.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .
- Select .The SP Assertions screen opens, displaying a table with assertion information.
- From theACCESS GROUP/DEVICElist at upper left, selectAll Managed Devicesor or one of the session-specific options.
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- From theSPlist, select a service provider.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Running SP error reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Only a device with SAML provisioned on it can provide data for SAML reports. The SP Errors screen shows several charts that you can use to track the health of
your SAML SP errors. Data appears when you configure statistics collection. Controls
on this screen work together so you can fine-tune the statistics display.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .
- Select .The SP Errors screen opens, displaying a table with error reports.
- From theACCESS GROUP/DEVICElist at upper left, selectAll Managed Devicesor or one of the session-specific options.
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- From theSPlist, select a service provider.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Running IdP assertion reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Only a device with SAML provisioned on it can provide data for SAML reports. The IdP Assertions screen shows several charts that you can use to track the health
of your SAML IdPs assertions. Data appears when you configure statistics collection.
Controls on this screen work together so you can fine-tune the statistics
display.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .
- Select .The IdP Assertions screen opens, displaying a table with assertion information.
- From theACCESS GROUP/DEVICElist at upper left, selectAll Managed Devicesor or one of the session-specific options.
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- From theIdPlist, select an identity provider.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Running IdP error reports
For Access
to have report data for a device, the device must have been added to the BIG-IQ Centralized Management system, discovered, and had the
Access remote logging configuration run for
it.
Only a device with SAML provisioned on it can provide data for SAML reports. The IdP Errors screen shows several charts that you can use to track the health of
your SAML IdP errors. Data appears when you configure statistics collection.
Controls on this screen work together so you can fine-tune the statistics
display.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, clickMonitoring.
- On the left, select .
- Select .The IdPs Errors screen opens, displaying a table with error reports.
- From theACCESS GROUP/DEVICElist at upper left, selectAll Managed Devicesor or one of the session-specific options.
- From theTIMEFRAMElist, specify a time frame:
- Select a predefined time period - These range fromLast hourtoLast 3 months.
- Set a custom time period - SelectBetween,After, orBefore, and click the additional fields that display the set dates and times that support your selection.
- From theIdPlist, select an identity provider.
- To save report data in a comma-separated values file, click theCSV Reportbutton.A CSV file downloads.
Configure remote
high-speed BIG-IQ and SWG event logging
You can configure the BIG-IQ®
system to log information about BIG-IQ and Secure Web Gateway events and send the log
messages to remote high-speed log servers.
When configuring remote high-speed logging of events, it is helpful to
understand the objects you need to create and why, as described here:
Object | Reason |
|---|---|
Pool of remote log servers | Create a pool of remote log servers to which the BIG-IP system can send log
messages. |
Destination (unformatted) | Create a log destination of Remote High-Speed Log type that specifies a pool of remote
log servers. |
Destination (formatted) | If your remote log servers are the ArcSight,
Splunk, or Remote Syslog type, create an additional log destination to
format the logs in the required format and forward the logs to a remote
high-speed log destination. |
Publisher | Create a log publisher to send logs to a set of specified log destinations. |
Log Setting | Add event logging for the APM system and configure log levels for it or add logging
for URL filter events, or both. Settings include the specification of up to two log
publishers: one for access system logging and one for URL request logging. |
Access profile | Add log settings to the access profile. The
log settings for the access profile control logging for the traffic that
comes through the virtual server to which the access profile is
assigned. |
Task
summary
Perform these tasks to configure remote high-speed BIG-IQ and SWG
event logging on the BIG-IQ system. Enabling remote
high-speed logging impacts BIG-IQ system performance.
Task
list
Creating a pool of remote logging servers
Before creating a pool of log servers, gather the IP addresses of the servers that
you want to include in the pool. Ensure that the remote log servers are configured to
listen to and receive log messages from the BIG-IP
system.
Create a pool of remote log servers to which the BIG-IP system can send log
messages.
- On the Main tab, click .The Pool List screen opens.
- ClickCreate.The New Pool screen opens.
- In theNamefield, type a unique name for the pool.
- Using theNew Memberssetting, add the IP address for each remote logging server that you want to include in the pool:
- Type an IP address in theAddressfield, or select a node address from theNode List.
- Type a service number in theService Portfield, or select a service name from the list.Typical remote logging servers require port514.
- ClickAdd.
- ClickFinished.
Create a new log destination
Before you can create a new log destination, you must have configured a remote log
server to send the logs to.
Use this screen to create a new log destination for a managed device.
Create a log destination to specify that log messages are sent to a remote log
server.
- At the top of the screen, clickConfiguration, then, on the left, click .The Log Destinations screen displays a list of the log destinations that are defined on this device.
- To create a new log destination, clickCreate.The New Log destination screen opens so you can define the settings you want for this destination.
- In theNamefield, type in a name for the log destination you are creating.
- ForType, select the kind of destination you are creating.Depending on the selection you make, additional controls are displayed.
- Specify the additional settings needed to suit the requirements for this log destination. The fields required to create a new log destination depend on the type you choose. BIG-IQ denotes required fields using an amber box. You can also determine whether you have completed all of the required fields by noting whether theSave & Closebutton is enabled.Except for the Devices and Device Specific settings, the parameters on this screen perform the same function as they do when you configure a log destination on a BIG-IP device. For details about the purpose or function of a particular setting, refer to the BIG-IP reference information onsupport.f5.com. From the BIG-IP Knowledge Center, select the BIG-IP LTM module and the software version you have installed; then select the appropriate guide. For example, information about the log destination parameters for BIG-IP version 13.0 is provided in the External Monitoring of BIG-IP Systems: Implementations, Version 13.0 guide.
- When you create a Log Destination and select a type ofIPFIXorRemote High-Speed Log, you need to specify which devices to associate this destination with. When you create a Log Destination and select a type ofManagement Portyou can specify device specific settings or, if no device specific settings are defined, the base configuration settings are used for any device associated with this log destination.For additional detail on device-specific log destination types, refer toWhat is a device specific log destination?in theF5 BIG-IQ Centralized Management: Local Traffic & Network Implementationsguide onsupport.f5.com.
- If you have a lot of devices that you need to associate with this log destination and want to automate the process:
- Use the steps below to specify one device and then clickSave.
- Associate this log destination with the log publishers that are pinned to your managed devices.
- Come back and edit this log destination. AFind Relevant Devicesbutton displays. You can use this button to let BIG-IQ assemble a list of devices. BIG-IQ finds the BIG-IP devices that this destination can be deployed to. You can use the list to create a device-specific instance of this destination for each BIG-IP.
- ClickSaveto add the listed devices to the Device Specific list.
- To specify the devices for this log destination manually:
- Select the device you want this destination to use
- If you are creating anIPFIXorRemote High-Speed Logdestination log, select the pool that you want each device to use.
- Use the
 button
to add additional devices to the list.
button
to add additional devices to the list. - Use the
 button
to remove a device from the list.
button
to remove a device from the list. - ClickSaveto add the listed devices to the Device Specific list.
Devices you select for this log destination are added to the Device Specific list.Click on a device name in the Device Specific list to edit settings for that device. Bear in mind though that changes you make to one device do not change the settings for other devices, or for the base configuration for the log destination. - ClickSave & Close.The system creates the new log destination with the settings you specified.
Create a new log publisher
Before you can create a new log
publisher, configure a log destination with a pool of remote log servers so you can
assign it to your publisher as you create it.
Log publishers specify log destinations that BIG-IP devices can send their log
messages to.
- At the top of the screen, clickConfiguration, then, on the left, click .The Log Publishers screen displays a list of the log publishers that are defined on this device.
- To create a new log publisher, clickCreate.The New Log Publisher screen opens so you can define the settings you want for this publisher.
- In theNamefield, type in a name for the log publisher you are creating.
- Select the Log Destinations for this publisher.
- Select a destination type from the Available list.The list of destinations displays only the type you selected.
- Select one or more destinations from the Available list.
- Move the selected destinations to the Selected list.If you are using a formatted destination, select the destination that matches your log servers, such as Remote Syslog, Splunk, or ArcSight.
- Specify the additional settings needed to suit the requirements for this log publisher.The parameters on this screen are optional and perform the same function as they do when you configure a log publisher on a BIG-IP device.For details about the purpose or function of a particular setting, refer to the BIG-IP reference information on support.f5.com. From the BIG-IP Knowledge Center, select the BIG-IP LTM module and the software version you have installed; then select the appropriate guide. For example, information about the log publisher parameters for BIG-IP version 13.0 is provided in theExternal Monitoring of BIG-IP Systems: Implementationsguide.
- ClickSave & Close.The system creates the new log publisher with the settings you specified.
Configure log
settings for access system and URL request events
Create log settings to enable event logging for
access system events or URL filtering events or both. Log settings specify how to
process event logs for the traffic that passes through a virtual server with a
particular access profile.
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, selectConfiguration, then on the left side of the screen, click.
- Click the name of the Access group that interests you.A new screen displays the group's properties.
- Click .
- Type a name for the name for the log setting.
- In theSSO Configuration Descriptionfield, type a descriptive text for the configuration.
- ForAccess System Logs, click the check box to specify a publisher for Access system logs and log levels.
- ForAccess Logs Publisher, select a log publisher.
- For the system log types, beginning withAccess Policyand ending withADFS Proxy, from the dropdown lists, select a log level. The default isNotice.
- ForURL Request Logs, click the check box to select a publisher for the logs and specifies the URL requests to log based on whether the request was blocked or allowed.
- ForURL Request Logs Publisher, select a log publisher.
- ForLog Allowed Events, click the check box to log request data when a user tries to access a URL that the URL filter allows.
- ForLog Blocked Events, click the check box to log request data when a user tries to access a URL that the URL filter blocks.
- ForLog Confirmed Events, click the check box to log request data when a user confirms a request for access to a URL for which the URL filter requires confirmation.
- ClickSave & Close.





