Manual Chapter :
Evaluating and Deploying Changes
Applies To:
Show Versions
BIG-IQ Centralized Management
- 8.4.0, 8.3.0, 8.2.0, 8.1.0, 8.0.0, 7.1.0
Evaluating and Deploying Changes
How do I evaluate changes made to managed objects?
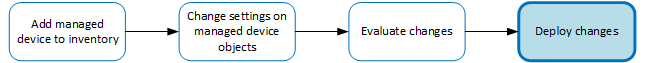
To change the object settings on a managed device, there are four tasks to
perform.
This figure illustrates the workflow for managing the objects on
BIG-IP devices. Evaluating the changes you have made is the third step in
this process.
Overview of evaluating changes made to
managed objects

If you need to make an urgent change, you can skip the evaluation
step. However, we highly recommend evaluation in all but emergency situations. See
Making
an urgent deployment
for details.How do I deploy changes made to managed objects?
Deploying changes
applies the revisions that you have made on the
BIG-IQ Centralized Management system to the managed BIG-IP devices. This figure illustrates the workflow for managing the objects on
BIG-IP devices. Deploying the settings is the last step in this process.
Change managed object workflow
How does deployment to devices in a cluster work?
When you created a cluster in BIG-IQ inventory, you chose a deployment option for the devices in that cluster.
If you chose to initiate BIG-IP DSC sync, and the Sync-Failover group on the BIG-IP system is configured for manual sync, after deployment to either device in the HA pair, Access kicks off manual sync to the other device. If manual sync succeeds, the deployment is successful. Otherwise, the deployment status shows an error.
If you chose to initiate BIG-IP DSC sync and the Sync-Failover group on the BIG-IP system is configured for automatic sync, after deploying to either device in the HA pair, automatic sync propagates the configuration to the other device. If automatic sync succeeds, the deployment is successful. Otherwise, the deployment status shows an error.
If you chose to ignore BIG-IP DSC sync, you must deploy the configuration from BIG-IQ to both devices in the cluster.
It is possible that after this, conflicts in DSC sync for these devices will occur.
Evaluate APM
configuration changes
Evaluating your changes gives you a chance to
spot critical errors and review your revisions one more time before deploying
them.
- At the top of the screen, clickDeployment.
- At the left, underEVALUATE & DEPLOY, clickAccess.The screen opens a list of Access evaluations and deployments that have been created on this device.
- Under Evaluations, clickCreate.The New Evaluation screen opens.
- Type aNameand an optionalDescriptionfor the evaluation task you are creating.
- Type a briefDescriptionfor the evaluation task you are creating.
- For theSource, select what you want to evaluate.
- When you want to compare the object settings currently on the managed device with the object settings in the pending version, selectCurrent Changes.
- When you want to compare the object settings currently on the managed device with the object settings in a stored snapshot, selectExisting Snapshot, then choose the snapshot you want to use.
- For theUnused Objectssetting, specify whether you want the system to delete unused objects from the BIG-IP devices that you are deploying changes to.If you do not want the system to delete unused objects:selectKeep Unused Objects.If you want the system to delete objects not referenced (directly or indirectly) by an object:leaveRemove Unused Objects(the default) selected.To understand what an unused object is, consider the following example:There are two address lists on the BIG-IP device to which you are about to deploy changes (AddressList-aandAddressList-b).
- AddressList-ais referenced by a policy that in turn is referenced by a firewall context.
- AddressList-bis not referenced (directly or indirectly) by any objects.
If you leaveRemove Unused Objects(the default) selected, then when you deploy changes to the BIG-IP device,AddressList-bis deleted. If you don’t want it deleted, selectKeep Unused Objects. - To deploy an Access configuration with associated LTM objects, forSupporting Objects, selectInclude associated LTM Objects.
- In theTargetsettings, from theGrouplist, select the Access group that you want to evaluate.Devices in the group display in the field.
- Move the devices that you want to evaluate to the Selected list.
- If you are evaluating a device that is a member of a cluster that is set to initiate BIG-IP DSC sync at deployment, you can select either member of the HA pair.
- If you are evaluating a device that is a member of a cluster that is set to ignore BIG-IP DSC sync, you should select both devices in the cluster.
- If you want to apply access policies on each BIG-IP device after deployment, selectAutomatically apply policies after deployment.
- Review the evaluation to determine whether you are going to deploy it.
- If there are critical errors, you cannot deploy these changes. In the Critical Errors column, click each error to see what it is, and then go back to where you made the change to fix it.After resolving any critical errors, you can come back and repeat the evaluation.
- If there are verification warnings, you can still deploy your changes, but you will probably want to resolve the warnings first. In the Verification Warnings column, click each warning to see what it is, and then go back to where you made the change to fix it.After resolving any verification warnings, you can come back and repeat the evaluation.
- If there are no critical errors or verification warnings, review the changes by clicking theviewlink.Each change is listed. You can review each one by clicking the name.When you create an evaluation to deploy an ASM or AFM object that is referenced by a Local Traffic & Network object, it can trigger a verification error. This occurs for a few related object types that require manual intervention before you can deploy objects that reference them. To deploy these objects, you must deploy the related object and the object that references it using the Local Traffic & Network user interface. In some cases, before you deploy, you need to pin the related object to a pinning policy that establishes the relationship between a device and that object.
- If you get a verification error that requires a Local Traffic & Network deployment, use the partial deployment option to deploy the Local Traffic & Network object. After you complete the partial deployment, you can complete the deployment that triggered the error.
- If you get a verification error with aPin Objectbutton that requires a Local Traffic & Network deployment, click the button to associate the two objects, and then use the partial deployment option to deploy the Local Traffic & Network object. After you complete the partial deployment, you can complete the deployment that triggered the error.
Managing Object PinninginF5 BIG-IQ Centralized Management: Securityonsupport.f5.com. - When you finish reviewing the differences, clickCancel.
- If the evaluation shows that you must evaluate and deploy Local Traffic configurations, do that before you deploy this evaluation.
Before BIG-IQ applies these just-evaluated object
changes to the managed device, you must deploy them. Refer to
Deploy configuration changes
for instructions.Deploy the Access configuration
To apply the Access configuration on the BIG-IQ system to your managed devices, deploy the configuration.
You must log in as an Administrator, Access Manager, or Access Deployer user to perform this task.
- Click theDeploymenttab.
- UnderEVALUATE & DEPLOY, selectAccess.The screen displays a list of Access evaluations and deployments defined on this device.
- Click the name of the evaluation that you want to deploy.The View Evaluation screen opens.
- Scroll down to Deployment, and then use the Schedule controls to specify whether you want to deploy the changes immediately or schedule deployment for later.
- To deploy this change immediately:
- SelectDeploy Now.
- ClickDeployto confirm.
- To deploy this change later:
- Select theSchedule for latercheck box.
- Select the date and time.
- ClickSchedule Deployment.
The process of deploying changes can take some time, especially if there are a large number of changes. During this time, you can clickCancelto stop the deployment process.If you cancel a deployment, some of the changes might have already deployed.Canceldoes not roll back these changes.
The evaluation you chose is added to the list
of deployments on the bottom half of the screen.
- If you chose to deploy immediately, the changes begin to deploy and the Status column updates as it proceeds.
- If you choose to delay deployment, the Status column displays the scheduled date and time.
Access deployment errors and warnings: causes and resolutions
Troubleshoot common issues with access deployment.
Access profile type mismatch
- Description
- The deployment process imports an access profile from a device to the other devices in the Access group. If an access profile of the same name exists on a device, the access profile types must match. If it does not, a critical error occurs and deployment fails.
- Resolution
- On the BIG-IP device, delete the access profile. Then, redeploy on the BIG-IQ system.
Sandbox object outside of the /Common partition
/Common
partition- Description
- If partitions exist on the device in addition to the/Commonpartition, they contain sandbox objects by default. When the deployment process tries to create the sandbox objects, if the same partitions do not exist on the device, a critical error occurs and deployment fails.
- Resolution
- On each BIG-IP device, create the same partitions. Then, redeploy on the BIG-IQ system.
Pools, pool members, self IPs, route domains
- Description
- Access objects refer to pools, pool members, self IP addresses, and route domains, all of which are managed in ADC. If any of these objects is not present on the device, evaluation provides a warning that LTM must be deployed before Access can be deployed. If the warning is ignored, Access deployment fails.
- Resolution
- Deploy LTM. Then re-discover LTM before trying to deploy Access.





