Manual Chapter :
Creating a Device Template for an AWS Cloud
Applies To:
Show Versions
BIG-IQ Centralized Management
- 8.4.0, 8.3.0, 8.2.0, 8.1.0, 8.0.0, 7.1.0
Creating a Device Template for an AWS Cloud
What details are needed in a device template for AWS?
There isn't much you need to configure for an AWS device template. Just
identify the correct port and NTP server to use,
and then specify the admin credentials and you are
all set.
Before you create a device template for a service scaling group
This is a list of things you'll need to set up your device template for auto-scaling BIG-IP VE devices.
Before you create your device template, you might want to gather some, or all, of the following information specific to creating the BIG-IP VE devices that deploy to the service scaling group (SSG):
- If you want to specify the port for communication between BIG-IQ and the BIG-IP VE devices, determine what you want to use.
- The NTP server and timezone you want the BIG-IP VE devices to use.
- The admin user credentials required to access the devices in the SSG.If you're using local authentication with a password enforcement policy, you'll have to meet the criteria it specifies for the admin account you created for accessing BIG-IP VE devices.
Create a new device template for AWS
Before you start creating your template, it's a good idea to gather any details you might need for the template property objects.
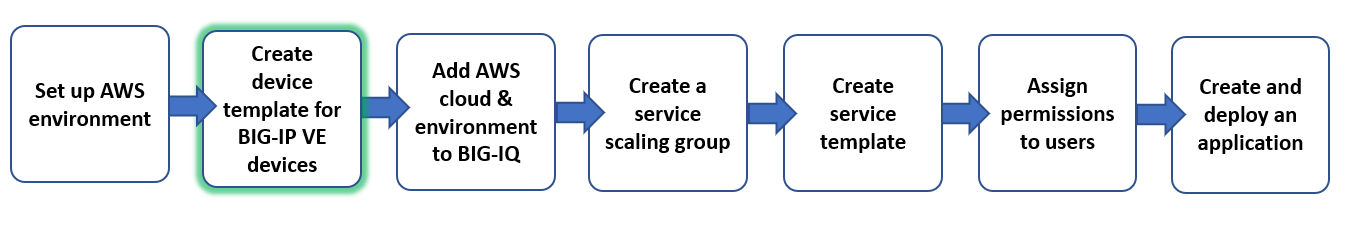
You create a new device template to specify settings AWS applies to devices in the service scaling group (SSG).
- At the top of the screen, clickDevicesthen, on the left, clickDEVICE TEMPLATES.
- Click theCreatebutton.
- Select theProviderfor which you are creating this template.The screen updates to display the configuration objects required for the selected provider type. A yellow circle displays next to each object to let you know that you need to provide an initial value.
- Click each object needed for the device template you need to create so you can specify the values appropriate for the devices in your SSG.The table lists the object types you can configure along with details about how the SSG uses those details.ObjectThis is where you specify:NotesConfigurationYou can specify a management port for communication between BIG-IQ and the BIG-IP VE devices in the SSG.By default, port 8443 is used, but you can configure a different port if needed.DNS & NTPDetails about the lookup and NTP server settings and time zone.You must specify an NTP server so all of the devices in the SSG have the same time reference. This must be a server that has the same time as the managing BIG-IQ system.User accountsThe username you specify for devices in a service scaling group must beadmin.In addition to alphanumeric input, you can use all punctuation characters for the password.Or, if you are using local authentication and have created a password enforcement policy, the password must meet the criteria specified in the password enforcement policy.
When you finish defining your new template, you can use it to create a new application that deploys to your BIG-IP devices.





