Manual Chapter :
Azure Setup for a Service Scaling Group
Applies To:
Show Versions
BIG-IQ Centralized Management
- 8.4.0, 8.3.0, 8.2.0, 8.1.0, 8.0.0, 7.1.0
Azure Setup for a Service Scaling Group
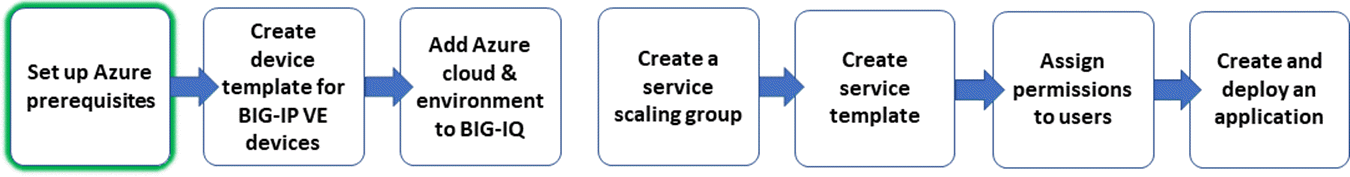
Overview of the Azure setup process
There are four primary configuration tasks to complete in your Azure
portal before you can create an Azure service scaling group (SSG) on your BIG-IQ.
- Register the F5 enterprise application.
- Create an Azure virtual network (VNet) in the region in which you want to deploy the SSG.
- Specify the credentials BIG-IQ uses to authenticate on the Azure portal. You need the following Azure credentials:
- Enterprise Application ID
- Azure Active Directory ID
- Service Principal Secret
- Set up the F5 device images for automated deployment.
These Azure essentials are needed whether you house the BIG-IQ system
and data collection devices (DCDs) in the Azure cloud, or in a private cloud or on-premises
environment.
- If you use the Azure cloud for all of your resources, you install the BIG-IQ devices and DCDs that manage the SSG in the Azure VNet. When you use Azure for your BIG-IQ and DCDs, you most likely have already created an Azure VNet and installed the BIG-IQ VE. If this is the case, be sure to review the Azure requirements here to ensure proper support for your SSG.
- If you install your BIG-IQ devices and DCDs in a private cloud or on-premises environment, after you create the Azure environment, configure a VPN to support the required communication between the Azure VNet and the management components.
Because the SSG resides in a VNet, the public or private cloud
accommodations you make for that VNet must also be made for each region in which you
operate an SSG.
Register the F5 enterprise application on your Azure portal
You create and register an
enterprise application, and make sure it has access control, so you can manage BIG-IP VE devices in an Azure cloud.
- Access your Azure Subscription, and use your admin privileges to register a new enterprise application.Make sure the application definition includes this information:FieldContent to enterNameThe name of the application you want to create.Application TypeWeb app/API.Sign-on URLThe URL of the web address you plan to advertise.
- Add additional application owners, if needed.
- Grant access control to your application.
- Access your Azure account, and navigate to .
- Click the name of the subscription that you plan to use to host your BIG-IP VE devices.
- SelectAccess control IAMand click+.
- ForRole, selectContributor.
- In theSelectbox, type the name of the application you specified when you registered the application for your BIG-IP VE devices.
- ClickSaveto assign access control to your application.
Create an Azure virtual network
You need to set up the Azure virtual network (VNet) that hosts your BIG-IP VE devices. If you use the public cloud option, this VNet hosts your BIG-IQ, as well.
- Access your Azure Subscription, and create a VNet.For the most current instructions for creating a virtual network in Azure, refer to the Microsoft Quick Start web site, quick-create-portal.
- As you configure the VNet, make sure it is in the location you want to work in and contains this information:
- A matching address space and address range with netmask size of 24
- Resource Group Name
- A management subnet, with a name that indicates what it is and includes a prefix and a body (for example:<prefix>-mgmt-subnet)
- Basic DDos protection
- Service endpoints and Firewall disabled
Locate the credentials for BIG-IQ authentication
You need to gather the credentials required to configure the Azure provider in the BIG-IQ user interface.
- In Azure Active Directory under App registrations, create a key and note the value.The key is used as the Service Principal Secret on the New Cloud Provider screen in the BIG-IQ user interface.
- To find the Subscription ID: Open the Azure portal, navigate toSubscriptionsand make a note of the ID for your subscription.
- To find the Tenant ID: Open the Azure Active Directory, navigate toPropertiesand make a note of the Directory ID.
- Find the Client ID: Open the Azure Active Directory, navigate toApp registrationsand make a note of Application ID.
Set Up Azure Marketplace images for automated
deployment
When the BIG-IQ needs to
deploy a BIG-IP instance to meet the needs of an
application on your BIG-IP VE device, the image
that Azure uses to deploy that instance must be
set up for automated deployment. To set this up,
you enable programmatic deployment in the Azure
environment for the required image types.
- Access your Azure account, and navigate to .
- In theFilterbox, typeF5 BIG-IP, and pressEnter.The screen lists all of the BIG-IP products currently published in Azure.
- Set up each BIG-IP product that is required by the applications you plan to deploy BIG-IP VE devices:
- Click the name of the BIG-IP product.A new panel opens on the Azure user interface and displays details about the selected BIG-IP product.
- At the very bottom of the details panel for the selected BIG-IP product, click the link that says:Want to deploy programmatically? Get started.
- On the Configure Programmatic Deployment page, clickEnableand then clickSave.
Requirements for a public BIG-IQ cluster
If you are using Azure cloud to house your BIG-IQ cluster, you most
likely have already created an Azure environment and installed the BIG-IQ VE and data
collection devices. If this is the case, be sure to review the Azure requirements here to
ensure proper support for your BIG-IP VE devices.
If you have configured an Azure portal network, but have not yet
deployed BIG-IQ virtual edition and data collection devices in it, refer to the
BIG-IQ Centralized Management and Microsoft Azure: Setup
guide on support.f5.com
for the
step-by-step process for deploying a BIG-IQ system and data collection device cluster in
Azure. As you follow that process, make sure that the parameters you specify conform to the
standards detailed here.For these Azure VE parameters |
Make these entries |
|---|---|
VNet Resource Group |
Use the resource group you associated with the Azure
VNet for the virtual machines that manage your BIG-IP VE devices. |
Virtual Machine name |
Specify the name of the BIG-IQ virtual machine that
manage your BIG-IP VE devices. |
Instance Size |
You need at least 8 CPUs and 32 GB of RAM. |
Public Inbound Ports |
Allow HTTPS(443) and SSH(22) as selected inbound
ports. |
User Name & Password |
|
OS Disk Type |
Specify Premium Select SSD. |
Virtual Network |
Use the VNet you created for the virtual machines
that manage your BIG-IP VE devices. |
Management Subnet |
Use the management subnet that you created when you
created the VNet for the virtual machines that manage your SSGs. |
Requirements for a private BIG-IQ cluster
When you manage BIG-IP VE devices in Azure and use a BIG-IQ
and data collection devices that are housed in a private cloud or
on-premises, you need a VPN to facilitate communication. Without a VPN,
the devices cannot send the analytic information you need to manage your
applications. Also, if you use the bring your own license (BYOL) option,
when new devices are created, they need the VPN so that they can contact
the BIQ-IQ acting as a license server.
Configuration
requirements for an Azure VPN
The VPN you use to facilitate communication between the
devices in your BIG-IP VE devices and the BIQ-IQ that manages them, and acts as the license
server, must meet the requirements defined in this table.
Requirement | For more information |
|---|---|
Both ends of the VPN require a gateway. That
is, you need a gateway between your BIG-IQ/data collection device
cluster and the VPN; and, you need a virtual private gateway between the
VPN and the Azure environment. | Refer to the vendor documentation for the gateway that you use
locally. For details on the Azure end, refer to Create a Site-to-Site connection in the Azure
portal on docs.microsoft.com . |
You must use a VPN supported by Azure. | For details on the VPN types that Azure
supports, refer to About VPN devices and
IPsec/IKE parameters for Site-to-Site VPN Gateway connections
on docs.microsoft.com . |
Subnets on your local network must use a
different subnet than the subnet used by the VNet you create in the
Azure environment. There can be no overlap. | For example, if the BIG-IQ and data collection devices in your local
cloud use a subnet such as 172.16.0.0/16 , you could use a subnet such as
10.1.0.0/16 on your Azure VNet. |
There must be a route from your BIG-IQ/data
collection device cluster to the Azure environment through your
gateway. | Create this route by logging in to the BIG-IQ and DCD in your local
cloud and running a set of tmsh commands. For
example, if your setup used the subnets listed in the previous example
(Azure network is 10.1.0.0/16 and your gateway address is 172.16.0.9 ), you
could run the following sequence of commands:
|





