Manual Chapter :
Evaluating Behavioral DoS protection
Applies To:
Show Versions
BIG-IQ Centralized Management
- 7.1.0
Evaluating Behavioral DoS protection
When reviewing traffic, it is important to note that this
protection method applies system settings to detect attacks as they occur. Once
the system detects an attack, it immediately begins mitigation to protect from
server overload. You can see an example of this in the image, which shows the
virtual server's report of server stress over time following two separate
attacks. By evaluating signatures of attacks, you can manage your settings to
whitelist or blacklist traffic based on detected signature outcomes. 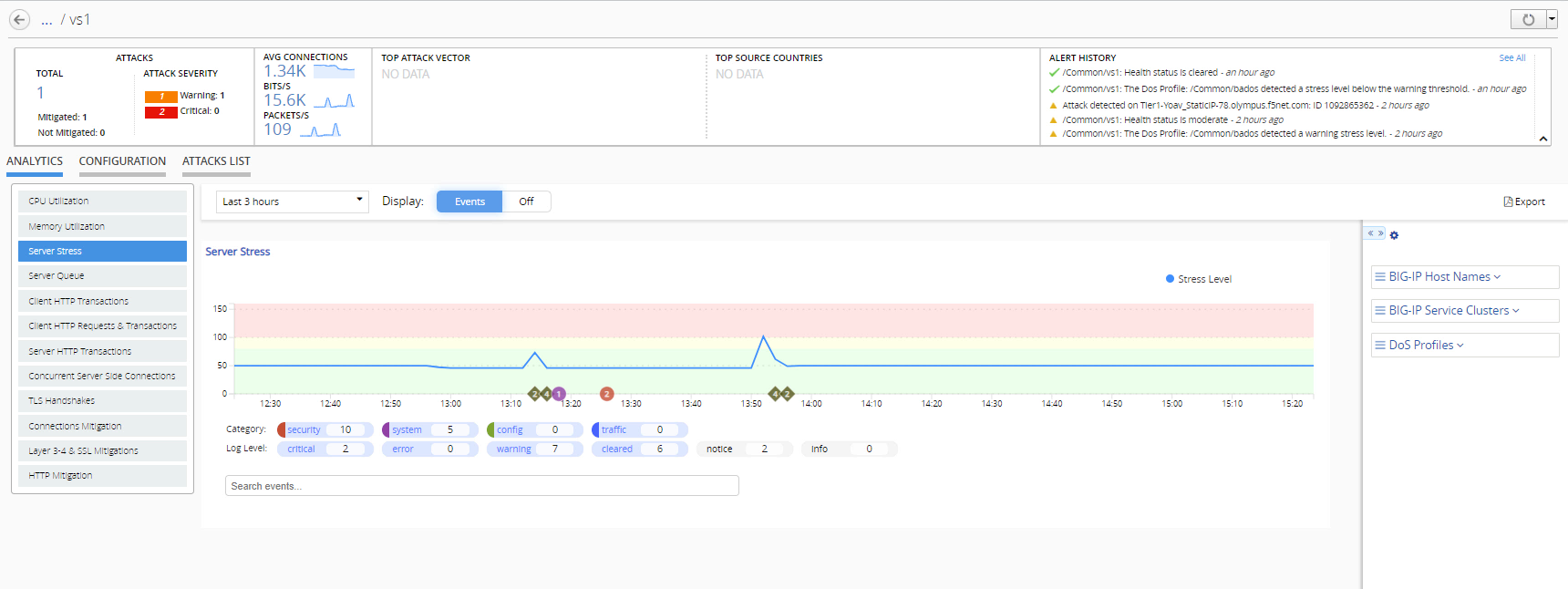
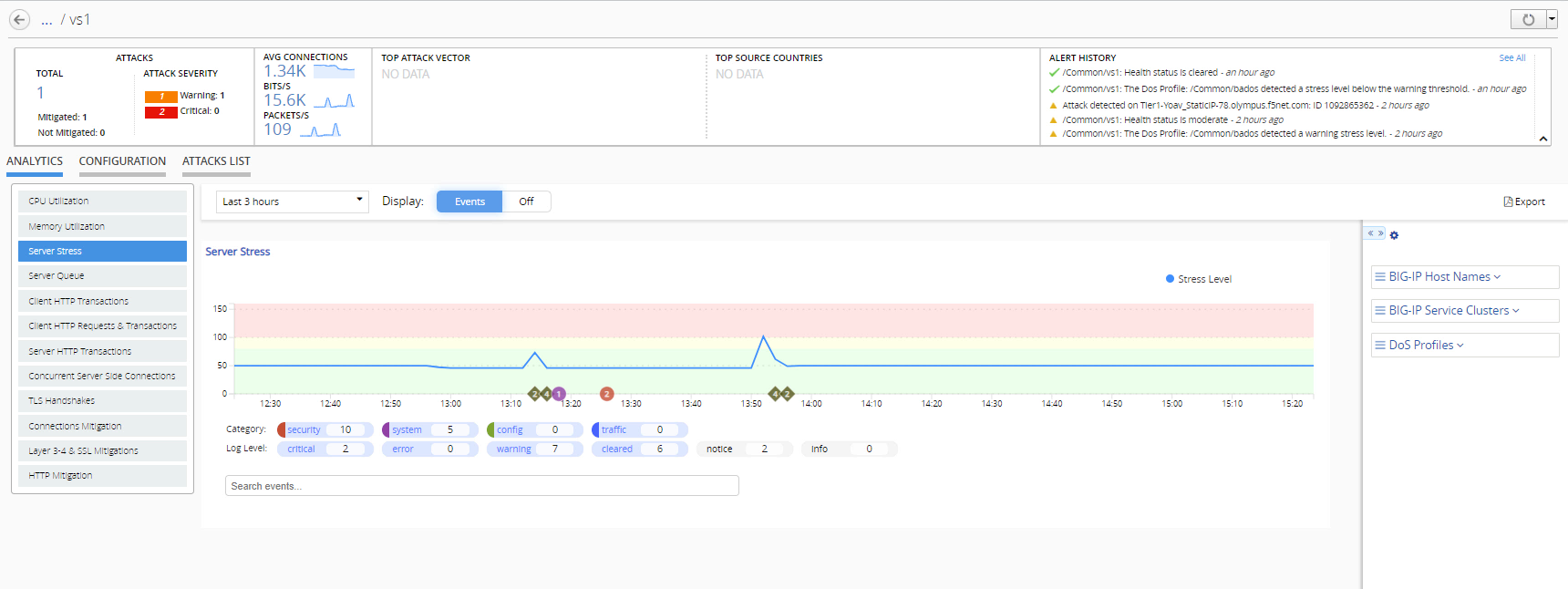
Behavioral DoS protection occurs when a protected object uses traffic
thresholds to detect whether and application server (pool member) is under stress.
Pool member health issues can indicate issues with the application's performance.
By monitoring virtual servers and pool member status events, you can evaluate
whether mitigation action is required.
In addition, you can monitor the detected attacks over time, and evaluate whether a
dynamic behavioral signature is repeatedly attacking your application.





