Manual Chapter :
Monitoring Web Application Security Activity
Applies To:
Show Versions
BIG-IQ Centralized Management
- 8.4.0, 8.3.0, 8.2.0, 8.1.0
Monitoring Web Application Security Activity
Monitoring Web Application Security
When Analytics is enabled on BIG-IQ, and AVR is provisioned on managed BIG-IP
devices, you can view detailed insights about the traffic that violated your layer 7
security policies. Data can indicate the need for changes to the application service's
Web Application Security (ASM) protection.
Policy management indicators can include, but are not limited to:
- Policy enforcement settings: A security policy may be deployed inTransparentorBlockingenforcement modes. Depending on your environment you may want to change these settings following the application service's deployment.
- Increased bad traffic: Drill down into traffic details, such as geolocation or malicious requests, or targeted URLs to identify sources of an attack. Based on these results, the security admin can enable strict enforcement for specific objects.
- False Positives: Application service alerts of increased false positives may indicate that enforcement settings are too strict and need adjustment.
Configuring Statistics Collection
in BIG-IQ: Monitoring and Reports
at support.f5.com
. If you are running BIG-IP
v13.0.8, or later, you are able to view the dynamic Web Application Security
dashboards found on . For more information about the information you can see in these
dashboards, see
Monitoring Web Application Security
Activity
.- A BIG-IQ data collection device configured for the BIG-IQ device
- The BIG-IP device located in your network and running a compatible software version
- Statistics collection enabled for managed BIG-IP devices
- AVR provisioned on your BIG-IP devices
Web Application Security Charts
The charts that reflect Web Application Security data allow
you to analyze current trends in traffic to applications with Web Application Security. The
parameters found in the charts described display the detected layer 7 security threats, out
of all HTTP traffic. Security information is available to AS3, Legacy, and Service Catalog
application services.
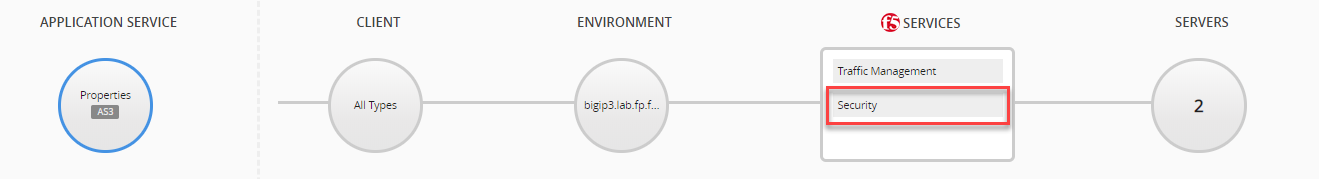
To view data for a single application
service, go to and select an application service. Once you select an application
service, data for security can be found in charts when the Security icon is
selected, as indicated in the image of an application service. To view Web
Application Security data for all applications, go to .
For general information about navigating the security charts
and application services, see
Monitoring and Managing Applications Using
BIG-IQ
on support.f5.com
. - Illegal Transactions Rate (TPS)
- The average number of illegal transactions per second that were identified by the Web Application Security profile. These transactions were detected based on the violation rating and your Web Application Security policy's action settings. Increases in illegal traffic over time can indicate an increase in attacks to your applications, or it can indicate an overly-strict protection policy. The current protection mode is indicated by Blocked or transparent transactions. You can use theViolation Ratingdimension to filter violations above a certain threat level. This will allow you to identify specific violations types that were detected.A single illegal transaction can include multiple violations. Therefore, comparing the number of illegal transactions vs the number of violations may not accurately reflect your system's status. It is recommended to primarily evaluate the number of illegal transactions.
- Transactions Rate by Violation Rating (TPS)
- The average number of transactions per second by the detected threat level assigned by your Web Application Security policy. The threat level of the traffic is shown in ascending order; fromLegaltoMalicious.
- Top 6 Violations (Violations/s)
- The six types of violations most commonly detected (per second). Violation information can be useful in adjusting your Web Application Security policy for optimized protection against the most common attacks.
Web Application
Security Dimensions and Metrics
The metrics and dimensions listed are provide data regarding
the transaction volume and traffic violations detected by your Web Application Security policy.
The information provided is found in the dimensions pane tables with the screens that display
Web Application Security data. You use this information to filter the on-screen data by specific
dimension objects. For example, if you would like to view data that pertains to specific virtual
servers, you can select specific virtual servers to filter only their data results. It is
important note that all metric data is displayed as a unit over the time period selected for the
screen.
Web Application Security Dimensions
The following defines the dimensions that provide traffic analytics for
objects protected by a Web Application Security profile.
Some
dimensions may not have listed objects, as information may not be available. For example,
if your policy is in Transparent mode, or there are no reported attacks, there will be no
data listed under the
Actions
dimension.- BIG-IP Host Names
- The name of each BIG-IP system that processed the monitored transactions.
- BIG-IP Blade Numbers
- The individual blades (by number) for all monitored BIG-IP devices.
- Applications
- The name of each application reporting HTTP traffic data.
- Application Services
- The name of each HTTP application service reporting transaction data.
- Virtual Servers
- The name of each virtual server that processes monitored transactions.
- ASM Policy Names
- The names of the Web Application Security (ASM) policies that protect the virtual servers currently processing application traffic.
- Actions
- The enforcement applied to a detected attack signature. These actions include:
- Learn
- Alarm
- Block
- Violation Ratings
- The rating assigned to traffic by the Web Application Security policy. The assigned ratings include:
- Legal, normal traffic that does not contain any threat indicators.
- Legal (Staging), traffic that is tentatively detected as legal during the policy builder process. The relevant settings in the security policy are in staging.
- Likely F.P., traffic may present a security threat, but is likely a false positive.
- Illegal, traffic that contains known violations, or abnormalities, that pose a threat to the application's performance.
- Malicious, traffic that contains known threat actors.
- Network Protocols
- The network protocol (HTTP, HTTPS) in the transaction.
- Client IPs
- The client IP address that initiated the HTTP request that was processed by the BIG-IP system.
- Attack Types
- The general category of application-layer attack, as identified by the Web Application Security policy.
- Violations
- The types of traffic violations, as detected by your Web Application Security policy.
- Virus Names
- The names of known viruses detected.
- Client Device IDs
- The unique identifier of the client’s device, derived from a JavaScript injection from BIG-IP to the client device.
- IP Reputation
- The IP categories configured for IP Intelligence. This dimension is relevant to users who have configured an ASM policy with IP Intelligence.
- Countries
- The country listed in the HTTP request that was processed by the BIG-IP system.
- User Name
- The client login name, based on information submitted from a login page. This information is available when Web Application Service is paired with Access service.
- Session ID
- The unique identifier of an HTTP session between the client and the application. This information is stored along with other client data, such as device ID.
- URLs
- The URL that initiated the HTTP request that was processed by the BIG-IP system.
- Response Code Families
- The class of the HTTP response result received by the BIG-IP system.
- Methods
- The HTTP method included in the HTTP request received by the BIG-IP system.
Web Application Security Metrics
HTTP metrics reflect the quantity, volume and speed of the HTTP traffic
processed by your managed BIG-IP systems. Metric sets categorize the metric data according
to an aspect of the traffic's progress throughout the transaction process. The table below
defines the metric set and the kind of metric data collected.
Metric Set | Metric Set Definition | Metric | Metric Definition |
|---|---|---|---|
Transactions | Each initiated request between the client
and BIG-IP system, regardless of the outcome. Depending on your configuration of Web Application Security, not all legal transactions are included in the transaction totals. | Avg/s | Average number of transactions per second that were
processed by the BIG-IP system. |
Total | Total number of transactions processed by the BIG-IP
system. | ||
Violations | The number of violations detected by the
Web Application Security policy. | Avg/s | The average number of violations detected per
second. |
Total | The total number of violations detected over the
selected period of time |





