Applies To:
Show Versions
BIG-IP AAM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
Overview: Configuring Global Network Acceleration for Web Application
Operating symmetrically, the BIG-IP acceleration functionality, using Web Application functionality, caches objects from origin web servers (less than approximately 100MB) and delivers them directly to clients. The BIG-IP device handles both static content and dynamic content, by processing HTTP responses, including objects referenced in the response, and then sending the included objects as a single object to the browser. This form of caching reduces server TCP and application processing, improves web page loading time, and reduces the need to regularly expand the number of web servers required to service an application.
Configuring BIG-IP acceleration across a WAN involves creation of a Sync-Only device group for two or more devices across the WAN, creation of a parent folder for acceleration objects under /Common on each device, configuration of one or more central BIG-IP devices, configuration of one or more remote BIG-IP devices, and synchronization of all devices in the Sync-Only device group.
Deployment of BIG-IP Devices for Acceleration
Global network symmetric deployment with an application configured symmetrically
A configuration for a site with multiple BIG-IP devices that are distributed across a large geography comprises a symmetric deployment. A symmetric deployment of multiple BIG-IP devices consists of central and remote BIG-IP devices that have synchronized configurations. With this configuration, users can transparently utilize the functionality of a BIG-IP device on another network across town, or across the world, from both sides of the transaction.
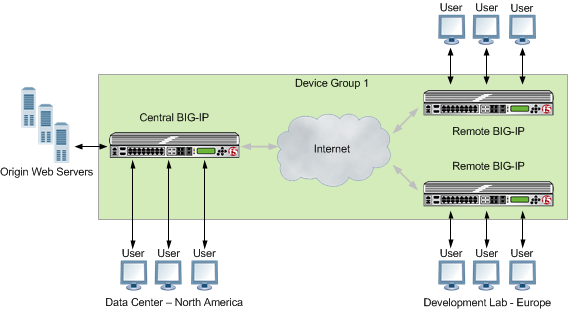 A global symmetric deployment with an application configured symmetrically
A global symmetric deployment with an application configured symmetrically
In a symmetric deployment, the central BIG-IP device is located closest to the application it is accelerating. The central BIG-IP device is accessed by local clients as well as clients from a remote BIG-IP device located in a separate geographic location, which can be around the world or across the country.
For example, a BIG-IP device might be located at a corporate office in North America that is accelerating a web mail server application that employees in a satellite office in Europe use. For this symmetric deployment, the central BIG-IP device is located at the corporate office, closest to the web mail application, and the remote BIG-IP device is located in Europe.
Once the remote BIG-IP device in Europe receives the response from the central BIG-IP device in North America, it caches that response and then sends it to the employee. As long as the content is still valid, the remote BIG-IP device in Europe can then respond to the future requests for the same content from local clients.
About symmetric request and response headers
In a global network that includes a symmetric deployment of remote and central BIG-IP devices across a WAN, the remote BIG-IP device receives a request and includes an X-Client-WA header, which distinguishes the request to the central BIG-IP device, enabling the central BIG-IP device to process the request, as necessary. When the central BIG-IP device receives a response for the origin web servers, it includes an X-WA-Surrogate header in the response, which distinguishes the response to the remote BIG-IP device, which processes the response as necessary and removes the X-WA-Surrogate header before sending the response to the client.
Working with Sync-Only device groups
One of the types of device groups that you can create is a Sync-Only device group. A Sync-Only device group contains devices that synchronize configuration data with one another, but their configuration data does not fail over to other members of the device group. A maximum of 32 devices is supported in a Sync-Only device group.
A device in a trust domain can be a member of more than one Sync-Only device group. A device can also be a member of both a Sync-Failover group and a Sync-Only group.
A typical use of a Sync-Only device group is one in which you configure a device to synchronize the contents of a specific folder to a different device group than to the device group to which the other folders are synchronized.
What is device trust?
Before any BIG-IP devices on a local network can synchronize configuration data or fail over to one another, they must establish a trust relationship known as device trust. Device trust between any two BIG-IP devices on the network is based on mutual authentication through the signing and exchange of x509 certificates.
Devices on a local network that trust one another constitute a trust domain. A trust domain is a collection of BIG-IP devices that trust one another and can therefore synchronize and possibly fail over their BIG-IP configuration data, as well as exchange status and failover messages on a regular basis. A local trust domain is a trust domain that includes the local device, that is, the device you are currently logged in to. You can synchronize a device's configuration data with either all of the devices in the local trust domain, or to a subset of devices in the local trust domain.
Illustration of Sync-Only device group configuration
You can use a Sync-Only device group to synchronize policy data in a specific folder across a local trust domain.
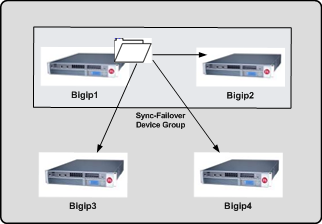 Sync-Only Device Group
Sync-Only Device Group
Device identity
The devices in a BIG-IP device group use x509 certificates for mutual authentication. Each device in a device group has an x509 certificate installed on it that the device uses to authenticate itself to the other devices in the group.
Device identity is a set of information that uniquely identifies that device in the device group, for the purpose of authentication. Device identity consists of the x509 certificate, plus this information:
- Device name
- Host name
- Platform serial number
- Platform MAC address
- Certificate name
- Subjects
- Expiration
- Certificate serial number
- Signature status
Task summary
Perform these tasks to create a Sync-Only device group.
Task list
Defining an NTP server
Adding a device to the local trust domain
- On the Main tab, click , and then either Peer List or Subordinate List.
- In the Peer Authority Devices or the Subordinate Non-Authority Devices area of the screen, click Add.
-
Type a device IP address, administrator user name, and administrator password
for the remote BIG-IP device with which you want to
establish trust. The IP address you specify depends on the type of BIG-IP
device:
- If the BIG-IP device is a non-VIPRION device, type the management IP address for the device.
- If the BIG-IP device is a VIPRION device that is not licensed and provisioned for vCMP, type the primary cluster management IP address for the cluster.
- If the BIG-IP device is a VIPRION device that is licensed and provisioned for vCMP, type the cluster management IP address for the guest.
- If the BIG-IP device is an Amazon Web Services EC2 device, type one of the Private IP addresses created for this EC2 instance.
- Click Retrieve Device Information.
- Verify that the displayed information is correct.
- Click Finished.
Creating a Sync-Only device group
Syncing the BIG-IP configuration to the device group
Task summary for accelerating HTTP traffic with a Central BIG-IP Device
Perform these tasks to accelerate HTTP traffic with a symmetric BIG-IP device.
Task list
Defining an NTP server
Creating a new folder for synchronized acceleration applications
- On the Main tab, click .
- Click Create.
- In the Folder Name field, type a name for the folder.
- From the Device Group list, select a Sync-Only device group.
- Optional: In the Description field, type a description.
- Click Save.
Creating a user-defined acceleration policy from a predefined acceleration policy
Creating an application profile for a symmetric deployment
Enabling acceleration with the Web Acceleration profile
Creating a pool on a central BIG-IP device to process synchronized HTTP traffic
Task summary for accelerating HTTP traffic with a Remote BIG-IP Device
Perform these tasks to accelerate HTTP traffic with a symmetric BIG-IP device.





