Applies To:
Show Versions
BIG-IP AFM
- 14.0.1, 14.0.0
Configuring IP Address Intelligence in the Network Firewall
About IP intelligence in the Network Firewall
In the BIG-IP Network Firewall, you can configure policies to validate traffic against an IP intelligence database. Such traffic can be handled automatically if it originates from known-bad or questionable IP addresses. To use existing lists of known bad IPs, you can configure policies to automatically query feed lists that specify blacklist and whitelist IP address entries, and assign default classes and blacklist or whitelist behaviors to those feed lists. In addition, you can manually add an IP address to a blacklist category, or remove an IP address from a blacklist category.
You can control the actions for each blacklist category by specifying such actions in a policy, and you can configure default action and default logging for each policy. Furthermore, you can configure logging and actions per category. You can apply IP Intelligence policies at the global context, to a virtual server, or on a route domain.
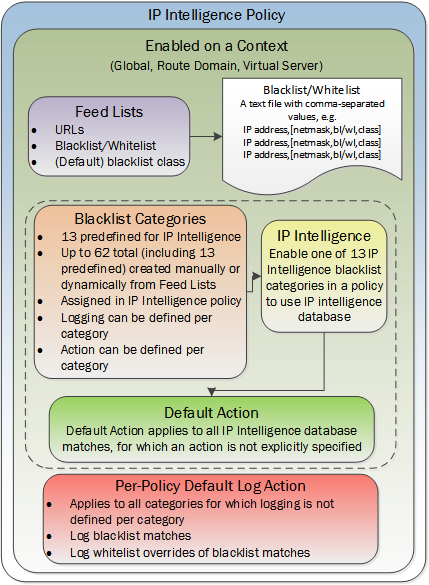
IP Intelligence Policy container and included elements
Downloading the IP intelligence database
- The system must have an IP Intelligence license.
- The system must have an Internet connection either directly or through an HTTP proxy server.
- The system must have DNS configured (go to ).
Blacklist categories
Along with the IP address, the IP intelligence database stores the category that explains the reason that the IP address is considered untrustworthy.
| Category Name | Description |
|---|---|
| additional | IP addresses that are added from additional categories not more explicitly defined. |
| appiq_badactors | IP addresses gathered from AppIQ central management. |
| application_denial_of_service | IP addresses involved in application DoS Attacks, or anomalous traffic detection. |
| attacked_ips | Destination IP addresses under attack. |
| botnets | IP addresses of computers that are infected with malicious software (Botnet Command and Control channels, and infected zombie machines) and are controlled as a group by a Bot master, and are now part of a botnet. Hackers can exploit botnets to send spam messages, launch various attacks, or cause target systems to behave in other unpredictable ways. |
| cloud_provider_networks | IP addresses and networks that belong to cloud providers, which offer services hosted on their servers via the Internet. |
| denial_of_service | IP addresses that have launched denial-of-service (DoS) attacks, distributed denial-of-service (DDoS) attacks, anomalous SYN flood attacks, or anomalous traffic detection. These attacks are usually requests for legitimate services, but occur at such a fast rate that targeted systems cannot respond quickly enough and become bogged down or unable to service legitimate clients. |
| infected_sources | Active IP addresses that issue HTTP requests with a low reputation index score, or that are known malicious web sites offering or distributing malware, shell code, rootkits, worms, or viruses. |
| mobile_threats | IP addresses of malicious and unwanted mobile applications. |
| phishing | IP addresses that host phishing sites, and other kinds of fraud activities, such as ad click fraud or gaming fraud. |
| proxy | IP addresses that are associated with web proxies that shield the originator's IP address (such as proxy and anonymization services). This category also includes TOR anonymizer addresses in versions prior to 13.1.0. |
| scanners | IP addresses that are involved in reconnaissance, such as probes, host scan, domain scan, and password brute force, typically to identify vulnerabilities for later exploits. |
| spam_sources | IP addresses tunneling spam messages through proxy, anomalous SMTP activities and forum spam activities. |
| tor_proxy | IP addresses acting as exit nodes for the Tor Network. Exit nodes are the last point along the proxy chain and make a direct connection to the originator’s intended destination. |
| web_attacks | IP addresses involved in cross site scripting, iFrame injection, SQL injection, cross domain injection, or domain password brute force. |
| windows_exploits | Active IP addresses that have exercised various exploits against Windows resources by offering or distributing malware, shell code, rootkits, worms, or viruses using browsers, programs, downloaded files, scripts, or operating system vulnerabilities. |
About IP intelligence blacklist categories
Blacklist categories are categories you can use to differentiate between types of blacklisted URLs. You can specify up to 62 blacklist categories, including those that are predefined on the system. A blacklist category definition consists only of a name and description. You can specify actions and logging options for each blacklist category you create, and for predefined categories, in an IP Intelligence policy. The predefined blacklist categories are automatically available for selection in an IP Intelligence policy.
Creating a blacklist category
Blacklisting an individual IP address
Removing an individual IP address from a blacklist
About IP intelligence feed lists
A feed list retrieves blacklists and whitelists from specified URLs. You can use a feed list to dynamically update blacklists and whitelists.
A feed list can retrieve multiple feeds from FTP, HTTP, or HTTPS addresses. You can specify whether a feed is a blacklist or whitelist, and the default category for the feed list. You can also configure a polling interval.
After a blacklist or whitelist is defined in a feed list, you add the feed list to an IP Intelligence policy. The list is then used by the policy to retrieve feeds and dynamically adjust the blacklist and whitelist policy.
Feed list settings
Feed lists dynamically define IP addresses that have been blacklisted or whitelisted. The IP Intelligence policy uses feed lists to dynamically filter traffic.
A feed list defines the feeds that dynamically update the IP address intelligence database for your system.
| Feed list setting | Description |
|---|---|
| URL | Select FTP, HTTP, or HTTPS, then specify the URL for the feed. Feeds are typically text files. An example for a local file might be http://172.10.1.23/feed.txt . |
| List Type | Whitelist or Blacklist. Specifies the default classification for all URLs in the feed for which a category is not specified. |
| Blacklist Category | Specifies a default category for the list. This is the default blacklist category for all blacklist URLs in the feed for which a category is not specified. On the BIG-IP system, you can specify a total of 62 categories; however, 9 categories are used by the IP Intelligence database. |
| Poll Interval | Specifies how often the feed URL is polled for new feeds. |
| Username | The user name to access the feed list file, if required. |
| Password | The password to access the feed list file, if required. |
| Feed URLs | In this area you can add, replace, or delete feed URLs from the feed list. |
A feed is a simple comma-separated value (CSV) file. The file contains four comma-separated values per line.
| Position | Value | Definition |
|---|---|---|
| 1 | IP Address | The IP address to be blacklisted or whitelisted. This is the only field that is required in each entry in the file. All other entries are optional. Important: If you append a route domain with a percentage sign and the route domain number, the route domain is not used.
|
| 2 | Network Mask | (Optional) The network mask for the IP address as a CIDR (such as, 24 for 255.255.255.0). This field is optional. Note: When IP 0.0.0.0 is mentioned in feed list without netmask, it is considered as a wild card IP and traffic from all the sources is blocked. If traffic from source IP 0.0.0.0 must be blocked, then add network mask of 32 as part of the blacklist entry.
|
| 3 | Whitelist/Blacklist | (Optional) Identifies whether the IP address is a whitelist or blacklist address. You can type wl, bl, whitelist, or blacklist, with any capitalization. Leave this field blank to retain the default specified for the feed. |
| 4 | Category | (Optional) Type the category name for the entry. Leave this field blank to retain the default specified for the feed. |
In this feed list file example, only the first entry specifies a value for every field. The third and fourth entries, 10.10.0.12 and 10.0.0.12, will be set to blacklist or whitelist entries depending on the setting for the feed. 10.10.0.12 is specified with a category of botnets; however, if the default setting for the feed is a whitelist, this is ignored. When an IP address has both a blacklist and a whitelist entry from the configuration, the whitelist entry takes precedence. The more specific entry takes precedence, so if an entry in the feed list file specifies a setting, that setting overrules the default setting for the feed list or category.
10.0.0.2,32,bl,spam_sources 10.0.0.3,,wl, 10.10.0.12,,botnets 10.0.0.12,,, 10.0.0.13,,bl,
Creating a feed list
Configuring and assigning IP intelligence policies
An IP intelligence policy combines combines feed lists, default actions, logging settings, and actions for blacklist categories into a container that you can apply to a virtual server or route domain.





