Applies To:
Show Versions
BIG-IP AFM
- 14.0.1, 14.0.0
Deploying the BIG-IP Network Firewall in Firewall Mode
About Firewall mode in the Network Firewall
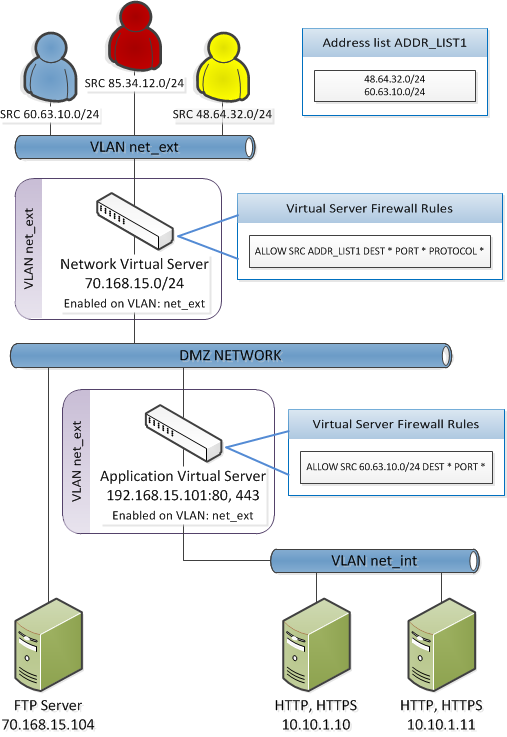
The BIG-IP Advanced Firewall Manager (AFM) provides policy-based access control to and from address and port pairs, inside and outside of your network. In this scenario, the network firewall is configured in Firewall mode, a default deny configuration, in which all traffic is blocked through the firewall, and any traffic you want to allow must be explicitly specified.
To understand this firewall scenario, imagine that your prerequisite system load-balances all traffic from the Internet to several internal servers. The internal servers are:
| Device and location | IP address | Traffic type |
|---|---|---|
| Server on DMZ network | 70.168.15.104 | FTP |
| Server on internal network | 10.10.1.10 | HTTP, HTTPS |
| Server on internal network | 10.10.1.11 | HTTP, HTTPS |
In order for traffic from the internal application virtual server to reach the external network virtual server, you must create a VLAN and enable both internal and external virtual servers on it. In this scenario, these VLANs are specified:
| VLAN | Configuration |
|---|---|
| net_ext | Enabled on 70.168.15.0/24, 192.168.15.101 |
| net_int | Includes pool members 10.10.1.10, 10.10.1.11 |
In addition, in this firewall configuration, there are three external networks that must be firewalled:
| Network | Policy |
|---|---|
| 60.63.10.0/24 | Allow all access |
| 85.34.12.0/24 | Deny all access |
| 48.64.32.0/24 | Allow FTP, deny HTTP and HTTPS |
Firewall configuration scenario