Applies To:
Show Versions
BIG-IP APM
- 11.5.1
About CRLDP configuration
Access Policy Manager supports retrieving Certificate Revocation Lists (CRLs) from network locations (distribution points). A Certificate Revocation List Distribution Point (CRLDP) AAA server defines how to access a CRL file from a distribution point. A distribution point is either an LDAP Uniform Resource Identifier (URI), a directory path that identifies the location where the CRLs are published, or a fully qualified HTTP URL.
About AAA high availability
Using AAA high availability with Access Policy Manager (APM), you can configure multiple authentication servers to process requests, so that if one authentication server goes down or loses connectivity, the others can resume authentication requests, and new sessions can be established, as usual.
APM supports the following AAA servers for high availability: RADIUS, Active Directory, LDAP, CRLDP, and TACACS+. APM supports high availability by providing the option to create a pool of server connections when you configure the supported type of AAA server.
Task summary for CRLDP configuration
This task list includes all steps required to set up this configuration. If you are adding CRLDP items to an existing access policy, you do not need to create another access profile.
Task list
Configuring an AAA server for CRLDP
Creating an access profile
Configuring an access policy that uses CRLDP authentication
Configuring a client SSL profile for CRLDP
Adding client-side SSL and access profiles to a virtual server
You associate the client SSL and access profiles with the virtual server so that the BIG-IP system handles client-side SSL traffic as specified, and so that Access Policy Managercan apply the access profile to incoming traffic.
Testing AAA high availability for supported authentication servers
- Begin a tcpdump on the Access Policy Manager, using a protocol analyzer, and scanning for packets destined for the specific port for your authentication server.
- Log in to the virtual server with both servers active.
- Using the tcpdump records, verify that the requests are being sent to the higher priority server.
- Log out of the virtual server.
- Disable the higher-priority server.
- Log in to the virtual server again.
- Verify that the request is being sent to the other server.
- Log out again, re-enabling the server, and try one more time to verify that the new requests are being sent to the high priority server.
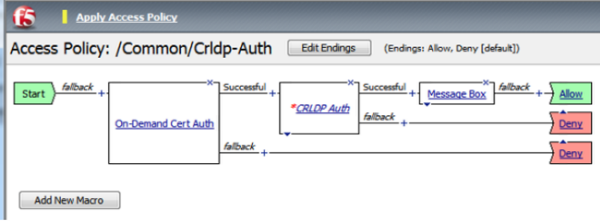
Example access policy for CRLDP authentication
This is an example of an access policy with all the associated elements needed to retrieve CRLs using CRLDP. Notice that you must add either the Client Cert Inspection agent or On-Demand Cert Auth agent before the CRLDP object in your access policy. One of those agents is required in order to receive the X.509 certificate from the user. This is also important because both agents store the user information, as well as the issuer certificates, in the session variables. This allows the CRDLP Auth agent to check the revocation status of the user's certificate.
 How CRLDP works
How CRLDP worksCRLDP session variables
When the CRLDP Auth access policy item runs, it populates session variables which are then available for use in access policy rules. The table lists the session variables for the CRLDP access policy item and for the certificate item used in the access policy.
Session variables for CRLDP
| Session Variable | Description |
|---|---|
| session.ssl.cert.whole | Provides the client certificate received from the user in PAM format. |
| session.ssl.cert.certissuer | Provides the issuer certificate of the client certificate in PAM format. |
| session.crldp.last.result | Sets the result of the CRLDP authentication. The available values are:
|
| session.crldp.last.status | Sets the status of the authentication to Failed. |
CRLDP authentication troubleshooting tips
You might run into problems with CRLDP authentication in some instances. Follow these tips to try to resolve any issues you might encounter.
CRLDP auth and query troubleshooting
| Possible error messages | Possible explanations and corrective actions |
|---|---|
| No AAA server associated with the agent | Make sure that a valid CRLDP responder configuration is assigned to the CRLDP agent in the access policy. |
| User/Issuer certificate not found for the session | The user/issuer certificate session variables are missing. Make sure that either the Client Cert Inspection agent or On-Demand Cert Auth agent is configured in the access policy (or use a variable assignment agent to create them). |
| Failure to connect to CRLDP server | Make sure that the CRLDP server is up and running and reachable from the BIG-IP system. |
| No LDAP URL found in the DP list | Indicates that no valid CRL DP is configured on the LDAP server. Make sure that the LDAP server used in the CRLDP server configuration has valid CRL DPs configured. |
| CRLDP response - Cert with serial number 'x' has been revoked | Indicates that the status of the user certificate is revoked. |





