Applies To:
Show Versions
BIG-IP APM
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
Overview: Protecting internal resources on a per-request basis
You can use a per-request policy to protect your internal resources and to be more selective about who accesses them and when. After a user starts a session, a per-request policy makes it possible to apply additional criteria for access any time the user makes a request. These steps are for use in a reverse proxy configuration; that is, with APM® and LTM® set up for web access management.
Note: You cannot use subroutines in macros within per-request policies.
Task summary
Creating a per-request policy
Configuring policies to branch by local database user group
Categorizing URLs using custom categories in a per-request policy
Configuring a per-request policy to control access to applications
Configuring a per-request policy to branch by group or class
Adding a per-request policy to the virtual server
To add per-request processing to a configuration, associate the per-request policy with the virtual server.
Example policy: URL filter per user group
Each URL Filter Assign item in this per-request policy example should specify a filter that is applicable to the user group.
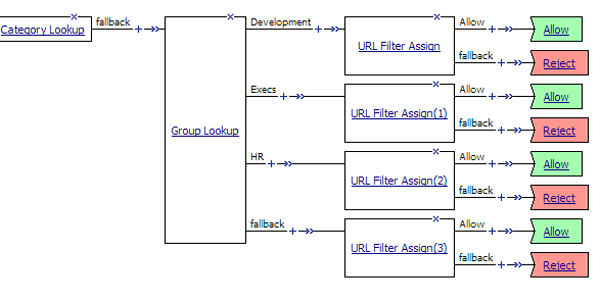
URL filter based on group membership
Example policy: Access control by date, time, and user group
This per-request policy example applies specific URL filters for weekends and weeknights, and restricts access during work hours based on user group.

Deny or allow access based on date and time and group membership
Example policy: User-defined category-specific access control
In this per-request policy example, only recruiters are allowed to access URLs in the user-defined category Employment. The policy also restricts access to entertaining videos during business hours.
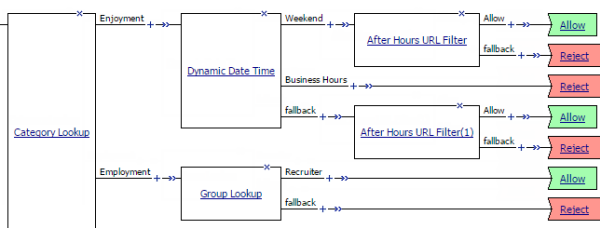
Category-specific access restrictions (using user-defined categories)
Example policy: Application lookup and filter
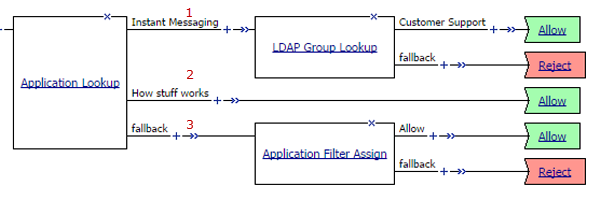
Application access control by application family, application name, and application filter
| 1 | A user-defined branch for the instant messaging application family. |
| 2 | A user-defined branch for a specific application. |
| 3 | The default fallback branch, on which an application filter is applied. Application Filter Assign needs the information provided by Application Lookup. |





