Applies To:
Show Versions
BIG-IP APM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
About Network Access
What is network access?
The BIG-IP® Access Policy Manager® network access feature provides secure access to corporate applications and data using a standard web browser, or the BIG-IP Edge Client®. Using network access, employees, partners, and customers can have access to corporate resources securely, from any location.
The network access feature provides users with the functionality of a traditional IPsec VPN client. Unlike IPsec, however, network access does not require any pre-installed software or configuration on the remote user's computer. It is also more robust than IPsec VPN against router and firewall incompatibilities.
Network access features
Network access provides connections with the following features.
- Full access from any client
- Provides Windows®, Macintosh®, Linux®, and mobile apps users with access to the complete set of IP-based applications, network resources, and intranet files available, as if they were physically working on the office network.
- Split tunneling of traffic
- Provides control over exactly what traffic is sent over the network access connection to the internal network, and what is not. This feature provides better client application performance by allowing connections to the public Internet to go directly to their destinations, rather than being routed over the tunnel and then out to the public Internet.
- Client checking
- Detects operating system and browser versions, antivirus and firewall software, registry settings, and processes, and checks files during the login process to insure that the client configuration meets the organization's security policy for remote access.
- Compression of transferred data
- Compresses traffic with GZIP before it is encrypted, reducing the number of bytes transferred between the Access Policy Manager® and the client system and improving performance.
- Routing table monitoring
- Monitors changes made in the client's IP routing table during a network access connection. You can configure this feature to stop the connection if the routing table changes, helping prevent possible information leaks. This feature applies to Windows clients only.
- Session inactivity detection
- Closes network access connections after a period below an inactivity threshold that you can configure. This feature helps prevent security breaches.
- Automatic application start
- Starts a client application automatically after establishing the network access connection. This feature simplifies user access to specific applications or sites.
- Automatic drive mapping
- Connects the user to a specific drive on the intranet. This feature simplifies user access
to files. Note: This feature is available only for Windows-based clients.
- Connection-based ACLs
- Filters network traffic by controlling whether packets are allowed, discarded, or rejected, based on specific criteria. For example, connections can be filtered by Layer 4 properties like source and destination IP address and port, protocol (TCP or UDP), and Layer 7 properties like scheme, host name, and paths. ACLs also support auditing capabilities with logging. ACLs allow groups of users or access policy users to have access to full client-server application support without opening up the entire network to each user.
- Dynamic IP address assignment
- Assigns client endpoint IP addresses dynamically from a configured pool of addresses. IP addresses can also be assigned with an external AAA server attribute.
- Traffic classification, prioritization, and marking
- Provides the ability to classify and prioritize traffic to ensure levels of service to users with defined characteristics.
About network access traffic
Network access implements a point-to-point network connection over SSL, which provides a secure solution that works well with firewalls and proxy servers.
Network access settings specify IP address pools, which the Access Policy Manager® then uses to assign IP addresses to a client computer's virtual network adapter. When an end user opens the address of the Access Policy Manager in a web browser, the browser starts an SSL connection to the Access Policy Manager. The user can then log in to the Access Policy Manager.
Network access connection diagram
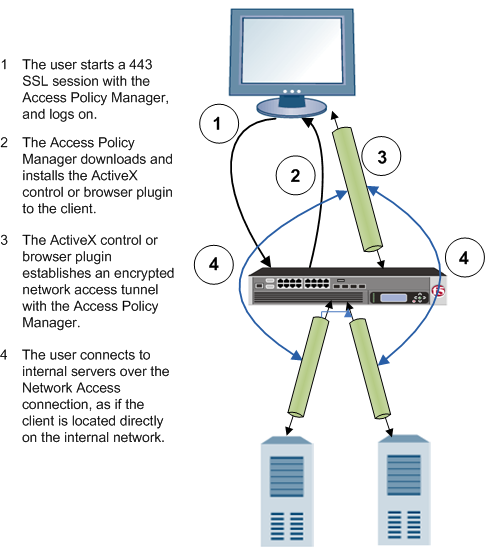
The process flow of a network access connection is depicted in this diagram.
Network access configuration elements
A network access configuration requires:
- A network access resource
- An access profile, with an access policy that assigns:
- A network access resource
- A network access or full webtop
- A lease pool that provides internal network addresses for tunnel clients
- A connectivity profile
- A virtual server that assigns the access profile
Network access elements are summarized in the following diagram.

Network access elements
Additional resources and documentation for BIG-IP Access Policy Manager
You can access all of the following BIG-IP® system documentation from the AskF5™ Knowledge Base located at http://support.f5.com/.
| Document | Description |
|---|---|
| BIG-IP® Access Policy Manager®: Application Access | This guide contains information for an administrator to configure application tunnels for secure, application-level TCP/IP connections from the client to the network. |
| BIG-IP® Access Policy Manager®: Authentication and Single-Sign On | This guide contains information to help an administrator configure APM for single sign-on and for various types of authentication, such as AAA server, SAML, certificate inspection, local user database, and so on. |
| BIG-IP® Access Policy Manager®: Customization | This guide provides information about using the APM customization tool to provide users with a personalized experience for access policy screens, and errors. An administrator can apply your organization's brand images and colors, change messages and errors for local languages, and change the layout of user pages and screens. |
| BIG-IP® Access Policy Manager®: Edge Client and Application Configuration | This guide contains information for an administrator to configure the BIG-IP® system for browser-based access with the web client as well as for access using BIG-IP Edge Client® and BIG-IP Edge Apps. It also includes information about how to configure or obtain client packages and install them for BIG-IP Edge Client for Windows, Mac, and Linux, and Edge Client command-line interface for Linux. |
| BIG-IP® Access Policy Manager®: Implementations | This guide contains implementations for synchronizing access policies across BIG-IP systems, hosting content on a BIG-IP system, maintaining OPSWAT libraries, configuring dynamic ACLs, web access management, and configuring an access policy for routing. |
| BIG-IP® Access Policy Manager®: Network Access | This guide contains information for an administrator to configure APM Network Access to provide secure access to corporate applications and data using a standard web browser. |
| BIG-IP® Access Policy Manager®: Portal Access | This guide contains information about how to configure APM Portal Access. In Portal Access, APM communicates with back-end servers, rewrites links in application web pages, and directs additional requests from clients back to APM. |
| BIG-IP® Access Policy Manager®: Secure Web Gateway | This guide contains information to help an administrator configure Secure Web Gateway (SWG) explicit or transparent forward proxy and apply URL categorization and filtering to Internet traffic from your enterprise. |
| BIG-IP® Access Policy Manager®: Third-Party Integration | This guide contains information about integrating third-party products with Access Policy Manager (APM®). It includes implementations for integration with VMware Horizon View, Oracle Access Manager, Citrix Web Interface site, and so on. |
| BIG-IP® Access Policy Manager®: Visual Policy Editor | This guide contains information about how to use the visual policy editor to configure access policies. |
| Release notes | Release notes contain information about the current software release, including a list of associated documentation, a summary of new features, enhancements, fixes, known issues, and available workarounds. |
| Solutions and Tech Notes | Solutions are responses and resolutions to known issues. Tech Notes provide additional configuration instructions and how-to information. |





