Applies To:
Show Versions
BIG-IP APM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
Overview: What is portal access?
Portal access allows end users access to internal web applications with a web browser from outside the network. With portal access, the BIG-IP Access Policy Manager communicates with back-end servers, and rewrites links in application web pages so that further requests from the client browser are directed back to the Access Policy Manager server. With portal access, the client computer requires no specialized client software other than a web browser.
Portal access provides clients with secure access to internal web servers, such as Microsoft OutlookWeb Access (OWA), Microsoft SharePoint, and IBM Domino Web Access. Using portal access functionality, you can also provide access to most web-based applications and internal web servers.
Portal access differs from network access, which provides direct access from the client to the internal network. Network access does not manipulate or analyze the content being passed between the client and the internal network. The portal access configuration gives the administrator both refined control over the applications that a user can access through Access Policy Manager, and content inspection for the application data. The other advantage of portal access is security. Even if a workstation might not meet requirements for security for full network access, such a workstation can be passed by the access policy to certain required web applications, without allowing full network access. In a portal access policy, the client computer itself never communicates directly with the end-point application. That means that all communication is inspected at a very high level, and any attacks originating on the client computer fail because the attack cannot navigate through the links that have been rewritten by the portal access engine.
About portal access configuration elements
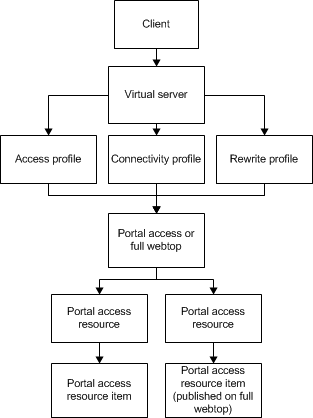
A portal access configuration requires several elements:
- A portal access resource including one or more portal access resource items
- An access profile
- An access policy that assigns both:
- A portal access resource
- A portal access or full webtop
- A rewrite profile (you can use the default rewrite profile)
- A connectivity profile
- A virtual server that assigns the access profile and a rewrite profile
Portal access elements are summarized in this diagram.
Understanding portal access patching
Portal access patches, or rewrites, links in web content. Portal access rewrites links in complex Java, JavaScript, Flash, CSS, and HTML content. In full patching mode, Access Policy Manager retrieves content from back-end servers and rewrites links in that content so it can be presented to a web browser, as if the content originated from the Access Policy Manager. Portal access rewrites content to make intranet targets resolvable, no matter what the intranet host is.
Understanding full patching mode
In full patching mode, you can select one or more of the following content types in which portal access rewrites links.
| Patching content type | Description |
|---|---|
| HTML patching | Rewrites links in HTML content to redirect to the Access Policy Manager. |
| JavaScript patching | Rewrites link content in JavaScript code to redirect requests to the Access Policy Manager. |
| CSS patching | Rewrites links to CSS files, and within CSS content, to redirect to the Access Policy Manager. |
| Flash patching | Rewrites links in Flash movies and objects to redirect requests to the Access Policy Manager. |
| Java patching | Rewrites link content in Java code to redirect requests to the Access Policy Manager. Access Policy Manager can also relay and handle any socket connections required by a patched Java applet. |
Understanding minimal patching mode
In minimal patching mode, portal access allows only minimum rewriting of web application content. Minimal patching mode is useful for troubleshooting, or when full portal access patching fails with a file or site.
In minimal patching mode, only HTML and CSS content is patched.
To use minimal patching, the following conditions must be met:
- You must create a local traffic pool for the application server or servers, and select it as the default pool in the virtual server definition.
- You must add a portal access resource item to the portal access resource, and configure it with host *, and port 0 (or any). In addition, the path /* must be specified in the resource item.
- You must configure the scheme any, not http or https.
- Minimal patching does not use a webtop, and will fail if one is assigned. For this reason, you must disable the Publish on webtop option, and you can not assign a webtop to the minimal patching access policy branch.
| Patching mode | Description |
|---|---|
| Scheme patching | Specifies a method of patching that replaces all HTTP scheme addresses with HTTPS scheme addresses. |
| Host Patching | Specifies a method of patching where one or multiple hosts (typically the actual application server host name) are replaced with another host, the Access Policy Manager virtual server. You can specify multiple hosts separated with spaces for host search strings. The host replace string must be the Access Policy Manager virtual server IP address or fully qualified domain name (FQDN). |