Applies To:
Show Versions
BIG-IP APM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
Overview: BIG-IP APM Secure Web Gateway
BIG-IP® Access Policy Manager® Secure Web Gateway (SWG) implements a secure web gateway by adding access control, based on URL categorization, to forward proxy. The access profile supports both transparent and explicit forward proxy modes. The access policy includes support for using a captive portal to collect credentials for transparent forward proxy mode and HTTP 407-based credential capture for explicit forward proxy mode. In addition to user identification by credentials, SWG provides the option to identify users transparently, providing access based on best effort identification. SWG also supports SSL traffic inspection.
The benefits that SWG provides include:
- URL filtering capability for outbound web traffic.
- Identifying malicious content and providing the means to block it.
- Applying web application controls for application types, such as social networking and Internet communication in corporate environments.
- Monitoring and gating outbound traffic to maximize productivity and meet business needs.
- User identification or authentication (or both) tied to monitoring, and access control compliance and accountability.
- Visibility into SSL traffic.
BIG-IP APM Secure Web Gateway terminology
Here are some common terms as defined within the context of BIG-IP®APM Secure Web Gateway (SWG).
| Term | Definition |
|---|---|
| application templates | An application template is a collection of parameters (in the form of F5® iApps® templates) that an administrator defines to create a configuration, such as configuration objects for explicit or transparent forward proxy or for communication between the BIG-IP® system and the F5 DC Agent. |
| explicit forward proxy | Traffic goes directly from the client browser to the forward proxy server. The forward proxy configuration takes place in the client browser, either manually or using a Proxy Auto-Configuration (PAC) file. |
| F5 DC Agent | The F5® DC Agent is an optional program that runs on a Windows-based server in your network. As users log on to Windows domains, the agent makes a best effort to map IP addresses to user names and send them to Secure Web Gateway (SWG). |
| IF-MAP server | When you configure the BIG-IP system to communicate with the F5 DC Agent, IP address and user name pairs are stored on the BIG-IP system in an IF-MAP server. |
| transparent forward proxy | The administrator can place the BIG-IP system right in the path of traffic (inline) as the next hop after the gateway, or can use policy-based routing or Web Cache Communication Protocol (WCCP) to send traffic for ports 80 and 443 to Secure Web Gateway. |
| transparent user identification | The Transparent Identity Import access policy item obtains the IP-address-to-username-mapping from the IF-MAP server. Alone or by pairing this item with another query to look up the user or validate user information, you can allow access through the proxy without requesting credentials. Transparent user identification is not authentication; use it only when you are comfortable accepting a best effort at identifying a user. |
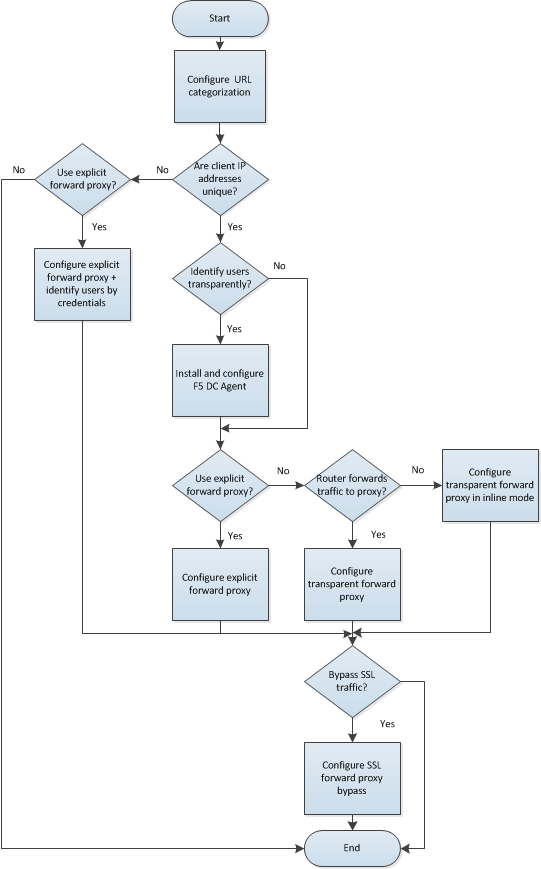
Flowchart for Secure Web Gateway configuration
How you proceed with configuring Secure Web Gateway (SWG) depends on answers to questions such as:
- Are IP addresses unique and trusted in your network? F5® recommends that they should be if you plan to identify users by IP address.
- Do you want to use transparent user identification? It identifies users by a best effort at login.
- Can you and do you want to use policy-based routing or Web Cache Communication Protocol (WCCP) to forward traffic to the proxy?
 Configuring SWG
Configuring SWG
Additional resources and documentation for BIG-IP Access Policy Manager
You can access all of the following BIG-IP® system documentation from the AskF5™ Knowledge Base located at http://support.f5.com/.
| Document | Description |
|---|---|
| BIG-IP® Access Policy Manager®: Secure Web Gateway Implementations | This guide contains information to help an administrator configure Secure Web Gateway (SWG) explicit or transparent forward proxy and apply URL categorization and filtering to Internet traffic from your enterprise. |
| BIG-IP® Access Policy Manager®: Third-Party Integration Implementations | This guide contains information about integrating third-party products with Access Policy Manager (APM®). It includes implementations for integration with VMware Horizon View, Oracle Access Manager, Citrix Web Interface site, and so on. |
| BIG-IP® Access Policy Manager®: Authentication and Single-Sign On | This guide contains information to help an administrator configure APM for single sign-on and for various types of authentication, such as AAA server, SAML, certificate inspection, local user database, and so on. |
| BIG-IP® Access Policy Manager®: Visual Policy Editor | This guide contains information about how to use the visual policy editor to configure access policies. |
| BIG-IP® Access Policy Manager®: Implementations | This guide contains implementations for synchronizing access policies across BIG-IP systems, hosting content on a BIG-IP system, maintaining OPSWAT libraries, configuring dynamic ACLs, web access management, and configuring an access policy for routing. |
| BIG-IP® Access Policy Manager®: Portal Access | This guide contains information about how to configure APM portal access. In portal access, APM communicates with back-end servers, rewrites links in application web pages, and directs additional requests from clients back to APM. |
| BIG-IP® Access Policy Manager®: Edge Client and Application Configuration | This guide contains information for an administrator to configure the BIG-IP
system for these clients:
|
| BIG-IP® Access Policy Manager®: Application Access | This guide contains information for an administrator to configure application tunnels for secure, application-level TCP/IP connections from the client to the network. |
| BIG-IP® Access Policy Manager®: Network Access | This guide contains information for an administrator to configure APM network access to provide secure access to corporate applications and data using a standard web browser. |
| BIG-IP® Access Policy Manager®: Customization | This guide provides information about using the APM customization tool to provide users with a personalized experience for access policy screens, and errors. An administrator can apply your organization's brand images and colors, change messages and errors for local languages, and change the layout of user pages and screens. |
| Release notes | Release notes contain information about the current software release, including a list of associated documentation, a summary of new features, enhancements, fixes, known issues, and available workarounds. |
| Solutions and Tech Notes | Solutions are responses and resolutions to known issues. Tech Notes provide additional configuration instructions and how-to information. |





