Applies To:
Show Versions
BIG-IP APM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
Overview: Configuring SWG explicit forward proxy
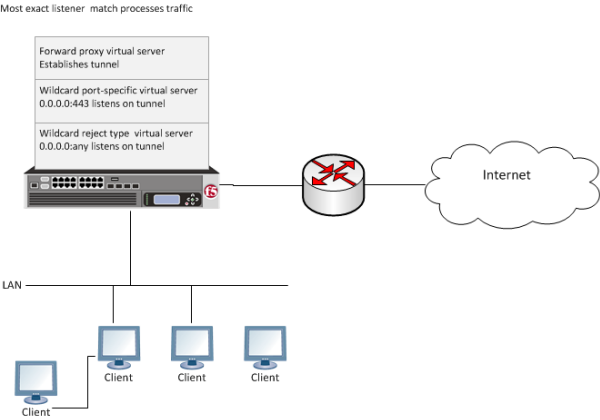
A Secure Web Gateway (SWG) explicit forward proxy deployment provides an easy way to handle web requests from users. For explicit forward proxy, you configure client browsers to point to a forward proxy server. A forward proxy server establishes a tunnel for SSL traffic. Other virtual servers (wildcard SSL and wildcard forwarding IP virtual servers) listen on the tunnel. The listener that best matches the web traffic directed to the forward proxy server handles the traffic.
 Explicit forward proxy configuration
Explicit forward proxy configuration
In any deployment of explicit forward proxy, you must consider how best to configure browsers on client systems to point to the proxy server and how to configure your firewall to prevent users from bypassing the proxy. This implementation does not explain how to do these tasks. However, here are some best practices to consider.
| Configuration | Recommendation |
|---|---|
| Client browser | Consider using a group policy that points to a Proxy Auto-Configuration (PAC) file to distribute the configuration to clients and periodically update it. |
| Firewall | A best practice might be to configure the firewall to trust outbound connections from Secure Web Gateway only. Note that possibly not all applications will work with a firewall configured this way. (Secure Web Gateway uses ports 80 and 443.) |
Before you begin
To use SWG, you must configure URL categorization. You might need to configure additional items depending on the other features that you decide to use.
- URL categorization
- To get a working SWG configuration, you must first download URL categories, configure URL filters, and configure schemes.
- Transparent user identification
- If you plan to identify users transparently, you must first download, install, and configure the F5® DC Agent.
- Authentication
- F5 recommends that you use NTLM or Kerberos authentication. If you plan to use
authentication, ensure that you have what you need configured.
- For NTLM, you need an NTLM Auth Configuration in Access Policy Manager® (APM®).
- For Kerberos, you need a domain-joined Kerberos user account and a Kerberos AAA server configured in APM.
- SSL intercept
- To intercept SSL connections that are passing through the proxy, ensure that you have imported a valid subordinate CA certificate and key that is trusted by the endpoints behind the proxy.
Task summary
About the iApp for Secure Web Gateway configuration
When deployed as an application service, the Secure Web Gateway iApps® template can set up either an explicit or a transparent forward proxy configuration. You can download the template from the F5® DevCentral™ iApp Codeshare wiki at (http://devcentral.f5.com/wiki/iapp.Codeshare.ashx).
About ACLs and SWG explicit forward proxy
Only L7 ACLs (or L4 ACLs that match L7 traffic, like hostname or IP-address only ACLs) work with Secure Web Gateway (SWG) explicit forward proxy.
Creating a DNS resolver
Adding forward zones to a DNS resolver
Before you begin, gather the IP addresses of the nameservers that you want to associate with a forward zone.
Creating a tunnel for SSL forward proxy traffic
Creating a custom HTTP profile for explicit forward proxy
Creating a custom Client SSL forward proxy profile
Creating a Client SSL forward proxy profile makes it possible for client and server authentication, while still allowing the BIG-IP® system to perform data optimization, such as decryption and encryption. This profile applies to client-side SSL forward proxy traffic only.





