Applies To:
Show Versions
BIG-IP APM
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
Overview: Policy branching based on Windows Registry values
You can create access policy branches using the values of Windows Registry keys on the client. You can use the GET operator in the Windows Registry action to fetch values from the client. To ensure client security, you must first configure the Windows registry on each client to allow trusted BIG-IP® systems to fetch specific Windows Registry values. Without client configuration, the GET operator fails.
Task summary
Registry screenshot: Allowed keys for a trusted server

Registry Allowed keys for a trusted server
Example: Allowed registry key value fetched
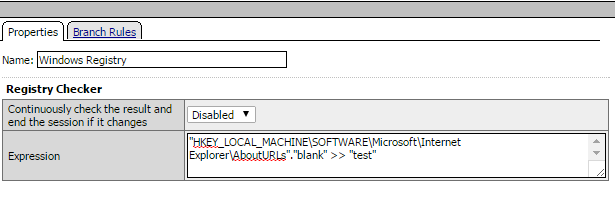
Windows Registry expression in the visual policy editor
The expression uses the GET (>>) operator to fetch the value of the registry key, HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\AboutURLs"."blank", into the user-defined session variable test.





