Applies To:
Show Versions
BIG-IP AAM
- 12.1.1, 12.1.0
BIG-IP APM
- 12.1.1, 12.1.0
BIG-IP Link Controller
- 12.1.1, 12.1.0
BIG-IP Analytics
- 12.1.1, 12.1.0
BIG-IP LTM
- 12.1.1, 12.1.0
BIG-IP PEM
- 12.1.1, 12.1.0
BIG-IP AFM
- 12.1.1, 12.1.0
BIG-IP DNS
- 12.1.1, 12.1.0
BIG-IP ASM
- 12.1.1, 12.1.0
Setting Up Secure Remote Logging
Introduction to secure logging configuration
The BIG-IP® system can securely log messages using Transport Layer Security (TLS) encryption to a secure syslog server that resides on a shared, external network. This implementation describes a sample configuration consisting of two BIG-IP systems, in a Device Service Clustering (DSC®) Sync-Only or Sync-Failover device group, that encrypt log messages using a local virtual server before sending the messages on to the remote secure syslog server.
In the example, the BIG-IP systems (bigip1.syslog.secure.com and bigip2.syslog.secure.com) and the secure syslog server (server.syslog.secure.com) mutually authenticate each other using X.509 certificates and keys on their TLS connections. This certificate validation requires a dedicated certificate for each BIG-IP system's logging interface (the self IP address on the logging VLAN for that BIG-IP system) and a certificate for the secure syslog server. In this sample configuration, all three certificates are signed by the same Certificate Authority (CA) and each have the same CA certificate bundle installed, to be used for X.509 certificate validation. The configuration is based on the assumption that you have configured an external Domain Name System (DNS) server with forward and reverse DNS entries for the names and IP addresses used in the X.509 certificate authentication.
In most configurations, the shared, external network should be deployed as a dedicated VLAN connecting only the BIG-IP systems and secure syslog server, due to the potential for high-bandwidth logging from the High Speed Logging (HSL) subsystem.
Sample secure logging configuration
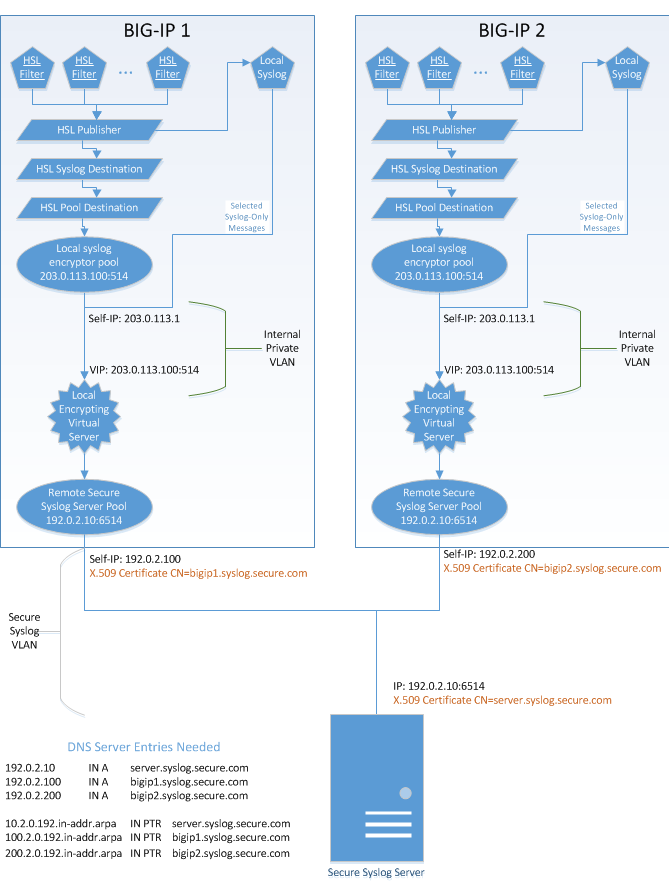
This illustration shows an example of the entire secure logging configuration. The logging traffic proceeds from top to bottom in the illustration.
High-level secure logging configuration
In the example:
- Each BIG-IP® system has one or more HSL filters directing certain kinds of log messages to an HSL destination. The HSL destination forwards the messages to both the local syslog server (for local log retention, in case the external syslog server is unreachable), and an HSL syslog destination, whose purpose is to add the timestamp and other information expected by RFC5424-compliant syslog servers. The HSL syslog destination then sends the decorated log messages to an HSL pool destination, which directs them to the local syslog encryptor pool containing the IP address of a local encrypting virtual server.
- The two BIG-IP systems include identically-configured local syslog encrypting virtual servers. The virtual servers are configured using a non-floating IP address on a private VLAN that is internal to each BIG-IP system, with no external interfaces attached. This VLAN exists solely to provide a private communications link between the local syslog encryptor pool, the local syslog server, and the local encrypting virtual server. For messages that are not currently processed by the HSL subsystem, the local syslog server uses this VLAN to send selected messages directly to the local encrypting virtual server, to be encrypted and sent on to the remote secure syslog server.
- The local encrypting virtual server is configured with a Server SSL profile for the purpose of sending the BIG-IP system's client certificate to the server for X.509 validation, as well as for validating the server's X.509 certificate using a locally-installed CA certificate bundle. Once authenticated and connected to the server listed in the remote secure syslog server pool, the local syslog encrypting virtual server sends the outbound encrypted syslog messages to the remote syslog server. The outbound TCP sessions are retained for subsequent syslog messages until the TCP timeout on the virtual server expires; then the next syslog message initiates a new TCP session.
The result is that when the high speed logging subsystem or the standard syslog service of either BIG-IP system sends TCP syslog traffic, the messages are forwarded to the remote syslog server over an authenticated and encrypted, secure channel.
Prerequisite tasks
Before configuring secure logging, you must perform these tasks on the BIG-IP® systems in the configuration.
| Task | Description |
|---|---|
| Create a device group. | The Device Service Clustering (DSC®) device group must contain the BIG-IP® systems as members. You perform this task on only one device in the device group. |
| Enable Automatic Sync on the device group. | Enabling automatic sync for the device group ensures that every change you make to a BIG-IP system is internally propagated to all device group members. In most cases, this eliminates the need to manually sync configuration changes to the peer device. You perform this task on only one device in the device group, and the change is propagated to the other device. |
| Assign fully-qualified domain names (FQDNs). | Each BIG-IP system in the device group, and the remote, secure syslog server, must have a unique fully-qualified domain name (FQDN). In our example, these FQDNs are: bigip1.syslog.secure.com, bigip2.syslog.secure.com, and server.syslog.secure.com. |
| Specify the DNS name server. | You must specify an external Domain Name System (DNS) server with forward and reverse DNS entries for the names and IP addresses used in the X.509 certificate authentication. Once configured, the DNS server resolves the FQDN used in the X.509 certificate for each device's secure logging configuration to the IP address on the logging VLAN for that device. You must perform this task on each BIG-IP device in the device group. |
About X.509 certificates for secure logging
One of the required elements of the secure logging configuration is the mutual validation of the X.509 certificate for each device in the configuration (that is, each BIG-IP® device, as well as the secure logging server). Each device must have a valid X.509 certificate and key assigned, where the Common Name attribute of the certificate resolves to the Fully Qualified Domain Name (FQDN) of that device's IP address on the shared secure logging VLAN. For the certificate on each of the two BIG-IP systems, this IP address is a self IP address. For the certificate of the secure, remote syslog server, this IP address is the IP address of that server.
For either BIG-IP system to successfully validate the certificate of the other device, all X.509 certificates must be signed by a parent certificate authority (CA) whose certificate chain is included in the certificate bundle referenced in the SSL profile of each of the BIG-IP encrypting virtual servers. The CA's certificate chain must also be included in the certificate bundle of the secure syslog server's configuration.
Task summary
You must perform several tasks to create a BIG-IP® system configuration that performs secure logging to a remote syslog server. Each of the tasks in this document is based on the sample configuration shown in Figure 1.
Task List
Importing an X.509 certificate, key, and CA bundle
To ensure that secure logging operates successfully, you must import the required certificate, key, and CA bundle to the local BIG-IP® device.
Creating a pool containing the syslog server
On either of the BIG-IP® systems in the device group, use the Traffic Management Shell (tmsh) to create a pool containing the IP address and TCP port number of the logging network interface on the remote syslog server.
Configuring system BIG-IP 1
The main goal of this task is to create a virtual server and associated objects on one of the two BIG-IP® systems (in the example, a system named bigip1.syslog.secure.com) that encrypts server-side traffic destined for the remote syslog server. This encrypting virtual server is on an internal, private VLAN and is associated with a non-floating virtual address, using the local BIG-IP system’s key and certificate. You also use this task to create a shared, external VLAN and an associated self IP address. This is the VLAN with which the remote syslog server is associated.
The encrypting virtual server that you create has the same destination address and port as the encrypting virtual server that you create on the peer system (in the example, bigip2.syslog.secure.com). Also, the virtual server targets the same pool as the peer system (the pool containing the remote syslog server).
Configuring system BIG-IP 2
The main goal of this task is to create a virtual server and associated objects on one of the two BIG-IP® systems (in the example, a system named bigip2.syslog.secure.com) that encrypts server-side traffic destined for the remote syslog server. This encrypting virtual server is on an internal, private VLAN and is associated with a non-floating virtual address, using the local BIG-IP system’s key and certificate. You also use this task to create a shared, external VLAN and an associated self IP address. This is the VLAN with which the remote syslog server is associated.
The encrypting virtual server has the same destination address and port as the encrypting virtual server that you create on the peer system (in the example, bigip1.syslog.secure.com). Also, the virtual server targets the same pool as the peer system (the pool containing the remote syslog server).
Modifying the local syslog server
Because some of the older audit log messages do not use the high-speed logging (HSL) system, you must modify the BIG-IP® system’s local syslog server to send audit data to one of the encrypting virtual servers.
modify sys syslog {
include "
destination d_to_secure_syslog { tcp( 203.0.113.100 port(514)); };
log { source(s_syslog_pipe); filter(f_audit); destination(d_to_secure_syslog); };
log { source(s_syslog_pipe); filter(f_authpriv); destination(d_to_secure_syslog); };
log { source(s_syslog_pipe); filter(f_apm); destination(d_to_secure_syslog); };
log { source(s_syslog_pipe); filter(f_sso); destination(d_to_secure_syslog); };
"
}
Creating a pool for the local encrypting virtual server
For the High-Speed Logging (HSL) system, you must create a pool containing the IP address and TCP port of the encrypting virtual servers. This pool becomes the target pool for the HSL pool destination.
Creating an HSL destination targeting the encrypting pool
You must create a remote high-speed log destination that targets the local encrypting syslog pool. This pool contains a single pool member, which is the destination IP address and port of the encrypting virtual server on each BIG-IP® system.
create sys log-config destination remote-high-speed-log hsldest_to_encryptor {
pool-name pool_syslog_encryptor
}
Creating an RFC 5424 (syslog) HSL destination
To ensure that the syslog timestamp and other identifying information is included with each log message, you must create a formatted remote-syslog destination that targets the remote high-speed log destination.
create sys log-config destination remote-syslog hsldest_syslog {
format rfc5424
remote-high-speed-log hsldest_to_encryptor
}
Creating an HSL publisher
You must create a high-speed logging (HSL) publisher, which sends the selected audit logging messages to both the local syslog server (for local logging) and the formatted remote-syslog destination.
create sys log-config publisher hslpub_secure_remote_syslog {
destinations replace-all-with {
hsldest_syslog
local-syslog
}
}
Creating HSL filters for log messages
You must create high-speed-logging (HSL) filters to select log messages and send the messages through the chain to the secure remote syslog server. Types of filters you can create are packet, SSL, tamd, and tmsh.
Configuring APM logging (APM systems only)
If you are testing a system on which you have provisioned BIG-IP® Access Policy Manager® (APM®), (also known as ADC-AP), you must enable APM syslog logging and create additional high-speed logging (HSL) filters.
Saving the secure logging configuration
After performing all tasks to configure secure logging on the BIG-IP® system, you must save the full secure logging configuration.





