Applies To:
Show Versions
BIG-IP LTM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
Using NAT64 to Map IPv6 Addresses to IPv4 Destinations
About NAT64
For the BIG-IP® system CGNAT module, NAT64 is the NAT type that maps IPv6 subscriber private addresses to IPv4 Internet public addresses. NAT64 translates subscriber IPv6 addresses to public Internet IPv4 addresses and allows Internet traffic from an IPv6 client to reach a public IPv4 server. The CGNAT module processes NAT64 traffic, as defined in RFC 6146 for TCP and UDP addresses.
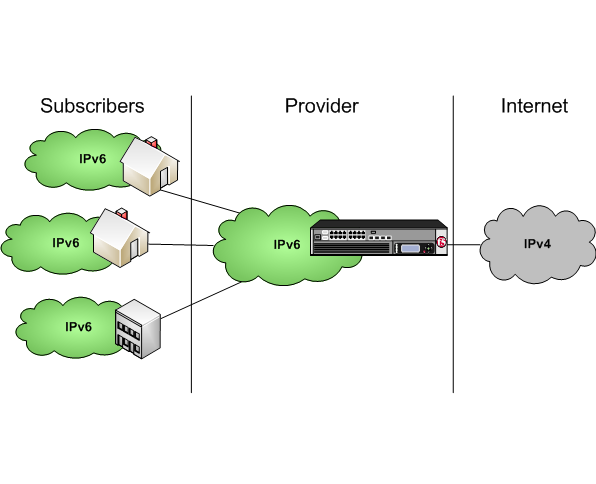
Diagram of a NAT64 network





