Applies To:
Show Versions
BIG-IP AAM
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
BIG-IP APM
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
BIG-IP LTM
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
BIG-IP AFM
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
BIG-IP DNS
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
BIG-IP ASM
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
About setting up embedded FIPS platforms in a device group
You can configure a device group using two platforms from the same series with a FIPS hardware security module (HSM) installed in each unit. When setting up an embedded FIPS solution on a device group, you install the two systems and can connect to a serial console to remotely manage the systems. In the event that network access is impaired or not yet configured, the serial console might be the only way to access your system.
After you have set up and configured the systems, you can create the FIPS security domain by initializing the HSM and creating a security officer (SO) password. You must configure the same security domain name on all HSMs in the group.
About embedded HSM initialization and synchronization
After you have set up and configured your BIG-IP® systems, you create a FIPS security domain by initializing the embedded HSM and then synchronizing all applicable HSMs.
Initializing the HSM in 5000/7000/10200 platforms
Initializing the HSM in 10350 platforms
Initializing the HSM in i5000/i7000 Series platforms
Viewing HSM information using tmsh
Before you synchronize the HSMs
Before you can synchronize the FIPS hardware security modules (HSMs), you must ensure that the target HSM:
- Is already initialized
- Has an identical security domain name
- Does not contain existing keys
- Is the same hardware model
- Contains the same firmware version
Before you run the fips-card-sync command, ensure that you have this information:
- The SO password for the source F5® device
- The SO password for the target F5 device
- The root password for the target F5 device
The target device must also be reachable using SSH from the source device.
Synchronizing the HSMs using tmsh
About FIPS multi-tenancy for vCMP guests
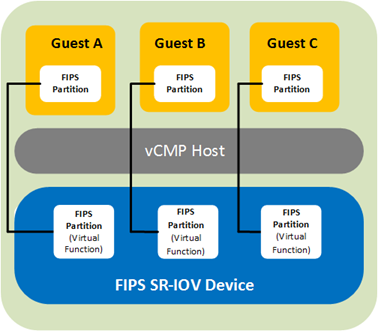
The BIG-IP® 10350v-FIPS platform model contains a FIPS-verified hardware security module (HSM) that supports Single Root I/O Virtualization (SR-IOV) mode on Virtual Clustered Multiprocessing (vCMP®)-enabled systems.
Benefit
The benefit of SR-IOV mode is that for a BIG-IP system on a 10350v-FIPS platform provisioned for Virtual Clustered Multiprocessing (vCMP®), you can create a virtual HSM (known as a FIPS partition) for each guest on the system. A FIPS partition is a portion of cores and private key slots on the HSM that a host administrator can dedicate to a guest for cryptographic functions.
This illustration shows a BIG-IP system where three guests each have their own FIPS partition for FIPS hardware-based processing.
About core allocation
You can create up to 32 FIPS partitions on the HSM, with some number of cores allocated to each partition. The number of cores you allocate to a FIPS partition depends on the processing needs of the guest you assign the partition to. The only limit is that the combined number of cores for all partitions cannot exceed 63, the total number of cores that the HSM supports.
To determine how you want to deploy FIPS partitioning for your vCMP guests, you should:
- Identify the guests that need dedicated cores.
- Decide how many cores and private key slots you want to allocate to each guest's partition.
For example, to decide how many cores to dedicate to each guest, suppose guests A and B have equal core requirements, but guest C has twice the needs of both A and B. In this case, you could allocate 12 cores each to A and B, and 24 cores to C. This would mean a total core allocation of 48 HSM cores, leaving 15 cores unallocated and available for future guest needs.
About FIPS private keys
Once you have assigned a FIPS partition to a guest, the guest administrator can log in to the guest to create, convert, or import FIPS private SSL keys, which are stored on the HSM. The FIPS partition assigned to the guest dictates the amount of storage available for FIPS keys on the HSM for the guest.
Host administration tasks
Before vCMP® guest administrators can create and manage FIPS keys in their own secure partitions on the FIPS hardware security module (HSM), a host administrator must initialize the FIPS HSM, resize the default partition to free up cores for other FIPS partitions, and create those other partitions on the HSM. As host administrator, you'll create one unique partition for each guest.
Prerequisite tasks for managing FIPS partitions
Before you set up FIPS partitions for your Virtual Clustered Multiprocessing (vCMP®) guests, confirm that the vCMP host prerequisites have been met, on each device that hosts vCMP guests in your high availability configuration. Confirm all prerequisites by logging into the BIG-IP system using the management IP address of the vCMP host.
| Prerequisites | Verification tool | Verification instructions |
|---|---|---|
| The BIG-IP system is provisioned for Virtual Clustered Multiprocessing (vCMP). | BIG-IP Configuration utility | On the Main tab, click . In the Module column, locate Virtual CMP (vCMP) and then view the Provisioning column. |
| You have created vCMP guests on the system. | BIG-IP Configuration utility | On the Main tab, click . View the list of vCMP guests. |
| You have permission to use the TMSH (TMOS® Shell) command-line interface. | BIG-IP Configuration utility | On the Main tab, click . Then click your account name and view the Terminal Access list. This setting must be set to either tmsh or Advanced shell. |
| The license type is 10350v-FIPS. | An SSH application such as PuTTY | At the tmsh prompt, type show sys hardware and under Platform, look for a Name property of 10350F. |
| The hardware security module (HSM) is initialized and the security label matches the label on all other devices hosting BIG-IP device group members (that is, vCMP guests). | An SSH application such as PuTTY | At the tmsh prompt, type fips-util -v info. |
| The HSMs on the appliances hosting the vCMP guests in the BIG-IP device group are synchronized. | An SSH application such as PuTTY | At the tmsh prompt, type run util fips-card-sync hostname . |
| You know the Security Officer password for managing the FIPS HSM. | Not applicable. | If you do not know the Security Officer password, see your security administrator. |
| The device has a Master Symmetric key. | An SSH application such as PuTTY | At the tmsh prompt, type show sys crypto master-key. |
| The BIG-IP configurations on all members of the BIG-IP device group (that is, vCMP guests) are synchronized. | BIG-IP Configuration utility | On the Main tab, click . Then verify that all device group members have a status of In Sync. |
For more information, see the guide BIG-IP Device Service Clustering: Administration, on the F5 support site support.f5.com.
About resizing FIPS partitions
After all vCMP® guests are deployed with FIPS partitions assigned to them, you might decide later that you need to increase or decrease the number of cores for a specific guest.
When you resize a guest's partition, you use the TMSH (TMOS® Shell) command-line interface, and it's helpful to understand the output that TMSH displays during the resizing process. For example, suppose you initially resized PARTITION_1 and created three other partitions, with these core allocations:
- PARTITION_1: 32 cores
- PARTITION_2: 8 cores
- PARTITION_3: 10 cores
- PARTITION_4: 4 cores
This shows that we have a total of 54 of the 63 cores on the HSM allocated, leaving 9 cores still unallocated.
Now suppose you decide to adjust the number of cores allocated to PARTITION_2, from 8 cores to 6. In this case, you'll need to use the fips-util ptnresize command within tmsh. For example, if you type:
tmsh /util fips-util ptnresize
The system prompts you for a password and the relevant partition name and displays other fields showing their currently-configured values:
Enter Security Officer password:
SO_password
Enter partition name:
PARTITION_2
Enter max keys (1-82160, current 5000):
4000
Enter max accel devs (0 to 25, current 8):
In the Enter max accel devs field, the system shows that there are 0 to 25 cores available to PARTITION_2 for resizing, with 8 cores currently allocated. The system calculates this 0 to 25 value using this formula:
(Total cores on the HSM - The sum of cores for the three other partitions) + (cores currently assigned to PARTITION_2)
which translates to:
63 - (32 + 10 + 4) + 8 = 25
For Enter mac accel devs, once you specify a new value of 6, the number of unallocated cores on the HSM increases from 9 to 11.
Enabling vCMP after a BIG-IP software upgrade
If your BIG-IP® system was provisioned for vCMP® prior to upgrading to this BIG-IP version, you must enable a BigDB variable, kernel.iommu.
Resizing the default FIPS partition
Whenever you initialize the FIPS hardware security module (HSM) on a vCMP® host, the process creates a FIPS partition named PARTITION_1 that you can assign to one of your vCMP guests. By default, PARTITION_1 contains all available FIPS cores on the HSM (63).
To free up cores for other guests, you'll need to reduce the number of cores assigned to PARTITION_1. You can then allocate those freed-up cores to other FIPS partitions that you create.
Creating FIPS partitions on the HSM
You can create a virtual hardware security module (HSM) for each vCMP® guest on the system that processes FIPS-related traffic. After creating FIPS partitions on the HSM, you can provide each guest with its own dedicated FIPS hardware resource to use for cryptographic functions.
Disabling a vCMP guest
Before you assign a FIPS partition to a guest, you must set the guest to the Configured state.
Assigning a FIPS partition to a vCMP guest
For BIG-IP® systems containing a FIPS hardware security module (HSM) on which you have created FIPS partitions, you can assign a separate FIPS partition to each vCMP® guest on the system. This provides each guest with its own virtual FIPS HSM to use for cryptographic functions when processing FIPS-related traffic.
It’s worth noting that in addition to using FIPS partitions for FIPS-related traffic, you can configure the SSL Mode setting for non-FIPS related traffic. This controls the non-FIPS hardware SSL resources on the system.
Displaying the list of FIPS partitions on the HSM
When the FIPS hardware security module (HSM) in your BIG-IP® system contains FIPS partitions for multi-tenancy, you can display a list of the partitions at any time.
Deleting FIPS partitions on the HSM
When the FIPS hardware security module (HSM) in your BIG-IP® system contains FIPS partitions for multi-tenancy, you can delete one or more of those partitions from the HSM if for some reason you no longer need them.
Guest administration tasks
When a vCMP® guest has a FIPS partition assigned to it, the guest administrator can store private SSL keys on the FIPS hardware security module (HSM). Specifically, a guest administrator can use the BIG-IP® Configuration utility to:
- Create and store FIPS keys in the HSM.
- Import non-FIPS keys (.exp files) or FIPS keys to the HSM. Importing FIPS keys requires the BIG-IP system to use the same Master Symmetric key that was previously used to export the FIPS keys.
- Convert non-FIPS keys to FIPS keys, which are then stored in the HSM.
For information about managing your FIPS keys, see the Key Management section of this guide.
Before you log in to a vCMP guest and manage private SSL keys, confirm that you have met these prerequisites:
- You have a user role that allows you to log in to the system as a vCMP guest administrator.
- You have permission to use the TMSH (TMOS Shell) command-line interface.
- You have permission to manage private SSL keys.
For more information, see the BIG-IP Digital Certificates: Administration guide at support.f5.com.
About managing keys on embedded FIPS systems
You can use one of two tools to manage keys on your embedded FIPS system: the BIG-IP® Configuration utility or the F5® TMOS® Shell (tmsh).
About managing FIPS keys using the BIG-IP Configuration utility
You can use the BIG-IP® Configuration utility to create FIPS keys, import existing FIPS keys into a hardware security module (HSM), and convert existing keys into FIPS keys.
Existing FIPS keys (.exp files) can only be imported into an HSM that possesses the same Master Symmetric key used when the FIPS keys were exported. The Symmetric Master Key is used to encrypt SSL private keys as they are exported from an HSM. Therefore, only the same Master Symmetric key can be used to decrypt the SSL private keys as they are imported into the HSM.
Creating FIPS keys using the BIG-IP Configuration utility
Importing keys using the BIG-IP Configuration utility
Converting a key to FIPS using the BIG-IP Configuration utility
About managing FIPS keys using tmsh
You can use the TMOS Shell (tmsh) to create FIPS keys, import existing keys into an F5® system, and convert existing keys to FIPS keys.
Creating FIPS keys using tmsh
Importing FIPS keys using tmsh
Converting a key to FIPS using tmsh
Listing FIPS keys in the HSM using tmsh
Listing FIPS keys in the F5 software configuration using tmsh
Deleting a key from the F5 software configuration and HSM using tmsh
Supported FIPS key sizes
These are the supported key sizes for F5® FIPS platforms.
| FIPS platform | Supported key sizes (bits) |
|---|---|
| 5000 | 1024, 2048, 4096 |
| 7000 | 1024/2048, 4096 |
| 10200 | 1024, 2048, 4096 |
| 10350 | 2048 |
Additional FIPS platform management tmsh commands
This table lists additional tmsh commands that you can use to manage your FIPS platform.
| Command | Description |
|---|---|
| show sys crypto fips key | Lists information about FIPS keys stored in the FIPS hardware security module (HSM), including FIPS key ID, length, type, and key objects. |
| list sys crypto key | Lists keys in the F5® software configuration. |
| delete sys crypto fips key <key-id> | Deletes a FIPS key from the FIPS HSM only. |
About recovery options
You can use one of these options for recovering your embedded FIPS system.
- Configure an additional unit for recovery
- Save the keys on a disk
- Configure a device group
FIPS system recovery options
This table describes configuration options for FIPS system recovery.
| Option | Description |
|---|---|
| Configure a device group | Configure the F5® devices in a device group with the FIPS HSMs synchronized. In the event of a system failure, the standby unit becomes active and handles incoming traffic. Contact F5 to arrange a Return Material Authorization (RMA) for the failed F5 device and then follow the steps for implementing a replacement unit to recover the failed device. |
| Configure an additional unit for recovery | Fully configure a third unit, add it to the security domain, and synchronize the configurations. Remove the unit from the network and store it in a secure location. If the F5 system in production is damaged or destroyed, you can use the backup unit to reconstitute the security domain. |
| Save the keys on a disk | Generate the private keys outside of the FIPS HSM. Copy the non-FIPS protected keys to a secure external location as a backup. Then convert the non-FIPS into FIPS keys on the F5 system. The keys on the F5 system are now protected by the FIPS HSM. If there is a catastrophic system failure, use the non-FIPS protected backup keys to repopulate the FIPS HSM. CAUTION:
This method for backup is not FIPS-compliant.
|





