Applies To:
Show Versions
BIG-IP AAM
- 13.0.1, 13.0.0
BIG-IP APM
- 13.0.1, 13.0.0
BIG-IP Link Controller
- 13.0.1, 13.0.0
BIG-IP Analytics
- 13.0.1, 13.0.0
BIG-IP LTM
- 13.0.1, 13.0.0
BIG-IP AFM
- 13.0.1, 13.0.0
BIG-IP PEM
- 13.0.1, 13.0.0
BIG-IP DNS
- 13.0.1, 13.0.0
BIG-IP ASM
- 13.0.1, 13.0.0
Overview: Configuring authentication for a remote system based on APM
As an administrator in a large computing environment, you might prefer to store user accounts remotely, on a dedicated authentication server. When you want to use a remote server to authenticate traffic that manages a BIG-IP® system, you can store BIG-IP system administrative accounts on an AAA server. BIG-IP APM® supports AAA servers such as HTTP, LDAP, RADIUS, Active Directory, and TACACS+. To complete the authentication process, you must add the newly configured AAA action to an access policy. You can find more information about AAA authentication and access policies in BIG-IP Access Policy Manager: Authentication and Single Sign-On and BIG-IP Access Policy Manager: Visual Policy Editor.
Creating a user authentication based on APM
- Verify that the BIG-IP® system user accounts have been created on the remote authentication server.
- Verify that the appropriate user groups, if any, are defined on the remote authentication server.
You can configure the BIG-IP® system to use an APM® server for authenticating BIG-IP® system user accounts, that is, traffic that passes through the management interface (MGMT).
You can now authenticate administrative traffic for user accounts that are stored on a remote APM server. If you have no need to configure group-based user authorization, your configuration tasks are complete.
Example access policy using APM LDAP authentication
This is an example of an access policy with all the associated elements that are needed to authenticate and authorize your users with LDAP authentication.
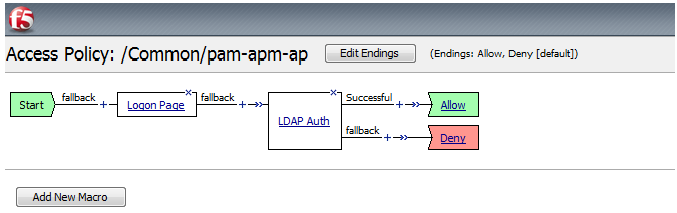
Example of an access policy for LDAP Auth





